Category Archives: Science
EMF Meters for TI Use
Radio Frequencies and Electromatic Fields can be weaponized for use against ANYONE. With the advent of 5G and the Internet of (smart) Things, almost EVERYONE should worry about RF/EMF effects. THIS MEANS YOU!
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
Dateline, Oct 30, 2020, from an undisclosed location not too far from wrong. copyright © 2020, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.
Hard rocks and harder places…
This is an extremely broad topic which cannot be well discussed here, beyond some basic advice. The problem for TIs is uniquely different from common uses of Technical Security Countermeasures (TSCM) equipment and services. So one problem right off the bat is obtaining useful help (good luck with that). This leads to a do-it-yourself (DIY) alternative by use of low-cost EMF meters, and possibly shielding or other tactical solutions. As result, most pros are ex mil-intel types, which creates a trust barrier with most of the TI community.

Not that it matters: a TI simply cannot afford the cost of their services. Professional TSCM equipment is extremely expensive (a pro might have a million dollars invested) and extremely complex, and requires a lot of experience and the kind of training offered in the military and intelligence communities. So, between trust and cost, and unique needs, a TIs find themselves between a proverbial rock, and hard place, a DIY nightmare. That’s not all.
That help issue trickles down the food chain to the makers and sellers of lower cost solutions, such as EMF meters, which are little brothers to more sophisticated and costly signal analyzers used by pros. Such firms do not and will not support DIY use of their products for TI related needs, and indeed, many pros will not offer their services, either because they fear running afoul with some government operation — or they don’t believe in the whole targeting notion and presume the client mentally ill.
It is possible to hire a PI or some individual who’s gone into business using low cost gear to do ‘mini’ TSCM sweeps, some of whom are aware of and will cater to TI needs, but many of these are charlatans, especially true in those who specialize in select TI issues, such as ‘finding implants.’ Be wary of anyone charging for implant detection using small EMF meters, esp. if charging by the implant found: with many meters, it is possible to cause a false read by simply moving a finger of the hand holding the device toward the front of the meter… for another $50 ‘find.’ “Would you like me to continue searching?”
It would therefore be better for the TI to do their own searches, though even with a decent EMF meter, the odds of finding an implant are extremely nil. EMF meters detect Radio Frequency (RF) and Electro-Magnetic Fields (EMF), which are radiated energy/field readings not given off by implants, as a rule. Most implants receive such signals, and those that transmit them tend to do so by remote command. Even then, it is very briefly, rather than being ‘on’ all the time — defying meter detection.
While there may be exceptions, the type of signal they use is likely to be lost amid the ambient signals present already (i.e., wifi, broadcast radio/TV, cellular, AC wiring, power
lines, amplifiers, etc.). An EMF meter displays the sum total of all such data, and can only identify a source by virtue of increasing in signal strength as it nears the signal source. An implant signal is rather weak. But, implants aside, there are other valuable uses for such a meter, if you have a decent one.
Choosing an EMF meter
First, know that cell phone apps that offer EMF readings are not reading the right kind of EMF. They are not reading any signal which is involved with targeting, but instead, the Earth’s own magnetic field, using sensors in the phone designed for game play to know changes in the phones relative position to prior positions (i.e., steering a car in a driving/racing game). For like cause, avoid ‘Natural’ EMF meters or EMF meters that do not include RF measurement, as they are also reading the Earth, only.
So what you really want is an actual RF/EMF meter. And not just any such meter, but one which is directional in nature when reading RF, and not omnidirectional. AC Magnetic Field readings will be omnidirectional, in virtually any meter, but if the RF sensing is directional, that will not impede usefulness of omnidirectional EMF readings. RF, on the other hand, is barely useful if only omnidirectional. That said, some omnidirectional meters will allow you to install and optional directional antenna… for added cost. One way or another, you want directional.

The type of antenna system described by the maker in specifications or manuals won’t necessarily tell you if it is omnidirectional or directional, they prefer a technical description of the physical antenna design (engineer speak). Omnidirectional (least useful for a TI) are typically described as ISOTROPIC or TRIAXIAL (3–AXIS), and are often visually discernible by a large ball or spherical object at their top. Sometimes it is internal and, therefore, smaller and unseen. That limits the sensitivity, compared to an external. Directional RF meters might have no antenna, a rod antenna (like old brick cell phones), a ‘wand’ at the end of a cable, or a triangular antenna (very useful with distant sources). So, any other technical description other than Isotropic or Triaxial, is good.
My base-line low-cost meter of choice is the TriField TF-2, which I actually used to sell with some value-added features for TI use. That included a user manuals I wrote for such use for the Trifield, and the Micro Alert audible meter (a good companion product). These manuals, along with a copy of this post and many others, are part of my TI Helps Kit available on request to proparanoidgroup at gmail com. I used to charge $10 for the manuals, but the Kit is free, though I do encourage a donation to the Free Will Society to aid severely impacted stalking victims (freewillsociety.wordpress.com) via PayPal to the above email addy.
I compare all other meters to the TriField before considering them desirable, or worth the price for TI needs. It is a directional RF with omnidirectional EMF readings in a simple to use and reliable product at a low cost. You can buy direct (trifleld.com) or find it online from many resellers. Experts in the meter reseller and RF/EMF consulting field also use it as a standard for comparisons, and that is telling. In fact, currently, one such pro who advocates for the TriField is EMF Academy, a valuable resource for information to anyone interested in issues revolving around the topic.
More importantly, they have a newsletter you can subscribe to, and associated with that, is a monthly drawing for one of three TriField meters. If you just visit their site and poke around looking at articles on things like EMF paint and shielded clothing, a popup will offer you the ability to subscribe and enter to win one of the meters. Some of their more expensive and exotic solutions I am currently testing, and will likely write an update report within a month: be sure to FOLLOW my blog so you get a notice. While you do that, also click the LIKE button and leave a comment, if you wish — all at that bottom of each blog post.
There are other features to look for in a meter which could be handy to a TI. An audible tone option, for working in the dark or allowing you to focus on what you are scanning (TF-2). Peak reading indicator and Avg signal strength (TF-2) instead of just a needle or light bar reading that is bouncing around enough to make such things difficult. It would be nice to have the ability to add a special antenna, such as (specifically) a dipole. This may be a round tube, or a flat, triangular antenna for very precise targeted distance source location (useful for DEW sources, typically hundreds to thousands of feet, or even miles away). Some offer a pistol grip or a protective case. These things are nice to have, but not usually critical, if you are willing to walk a bit more to effect the same results.
But the important feature is antenna, and frequency range. Most meters are intended only for cellular and wi-fi operating ranges, which stop (well before 5G) at below 3.5 GHz. One insidious risk of 5G compared to 4G and the current wifi standards, is that it operates at such a high frequency, citizens won’t be able to afford meters designed to check for safety. They may operate at up to 6 GHz. As it happens, DEW weapons are likely operating in similar ‘beyond hope’ ranges. My $12K meter setup can still only see to 12GHz, and some DEW will be above 50 or 60 GHz.
And, it is true that EEG entrainment (mood, sleep control, thought interference), which many TIs call remote neural monitoring (a misnomer), operates at frequencies well below any low-cost meter on the market, unless you are looking at something like my $12K rig… which is exactly why I have it. We are talking human brain operating frequencies, at and below 30Hz. Your ears cannot hear below 30Hz, because if they could, it would confuse your brain, and therefore, that’s also why audio equipment tends to stop at that low end, as well.
Proper use…
Hold the meter level, flat in your hand, so you are looking down to see the reading. If you aim it upward, you are going to flood the meter with radio waves reflecting off the ionosphere, and will always get incorrectly high readings. You wouldn’t even be able to sense a satellite signal, that way; such meters are not designed for anything but environment readings or very near or high-outpt sources. Also, many meters without external antenna will give similar false readings if your hand is touching the ‘head’ or ‘business end’ of the meter, so hold it by the rear half, only. When taking a reading, your purpose may vary, but generally, you are looking for a ‘hot’ or higher-than-average reading among the ambient collective.
Before actually taking readings, consider perp strategies. They likely have excellent surveillance and will know when you are using a meter. It is very likely that they would therefore simply shut down, making any sweeps pointless. This is why a pro TSCM sweep is typically conducted unannounced, anonymously, and with a degree of stealth and cunning. Ideally, it would be best if you arranged for a companion to do the sweeps with as little fanfare or obvious effort, as possible.
This brings in additional problematic factors, such as trust and willingness to help in what is a lengthy and complex set of tedious steps. Or, you might get lucky and find the enemy’s gear is simply left running while they take a nap. For most TI’s, though, it can mean many attempts before being able to acquire useful information from the meter. Failure to find clues of targeting does not mean they never target, does not mean the meter is defective, does not mean you are doing something wrong… it just means that was not likely the right opportunity.
And yet, of course, the other possibilities may yet be true, in the end. While a negative is not necessarily proof of a negative, a positive is its own proof. Even so… you will want multiple positives over time if to have useful evidence. That will also require good documentation, such as video and verbal announcements of what you are doing and seeing, and where the meter is pointing. Have a witness, too. More to follow.
Taking readings…
Slowly sweep back and forth, left to right, looking for possible reading jumps or dangerously high readings (hot spots). When you first start, you won’t likely know what is dangerous, or not. There are good online resources to help with that, but they can sometimes seem way too technical, and measurement increments of your meter may not match the measurement increments of a given site. That can result in confusion or misinterpretation, and force some math you might wish to avoid. Here are several sites you can review and compare against your meter, hopefully finding one more directly useful, without involving conversion factors. There are many others out there, and what constitutes unsafe levels is kind of a moving target in constant redefinition, and there is a difference in European, American, and Asian standards, the U.S. being the most lax (natch) of the three.
https://www.home-biology.com/electromagnetic-field-radiation-meters/safe-exposure-limits
https://healthybuildingscience.com/2013/02/18/emf-and-emr-conversion-formulas/
If you find a hot spot, stop and watch for several seconds to see if it holds relatively steady or was just a random spike. Generally, you will want to repeat scans in each of the meter’s modes of operation (i.e., the TriField has three: AC Magnetic, AC Electric, and RF/Microwave). If you are logging results for legal or comparative purposes, give it at least five seconds and note the reading(s), avg, and peak. If you’ve made an entry, be sure to note the values for each meter setting at that same position/angle. That added information could prove useful at some point.
Hot spots may show up either as a gradual rise and fall as you sweep, or a sudden spike. It may be brief, or hold steady. Brief spikes are not typically useful, but one which holds or is above safe limits is very useful. Note if gradual or sudden, and especially note if it was synchronous with any impact on you or your environment. You will also want to get a compass heading (there are cell phone apps for that, relying on natural EMF, as it happens).
If outside, and you are in something like a depression or valley, or a where there are tall buildings, you may wish to then tip the meter a bit to scan lower and higher in angle, such that you avoid looking directly into the sky (stay below the visual horizon, where rooftops may so redefine it), looking for further increases which may help identify a specific source location of the signal (a cell phone ‘bubble level’ app with off-level degree readouts might help with your notes, as well). If it is a building you are aiming at, try to estimate the floor, and note that. You may want a strong pair of binoculars, a rifle scope, or other strong lens to try to see what is at the suspect location. And it is suspect, only. A hot spot, even if very hot, is not alone a proof of a targeting source… but only reveals a possible suspect location.
If we are talking about finding a surveillance or other targeting device planted somewhere within your location with the meter, there is a similar concern, should you find something. Depending on the device purpose (which you may not be able to discern), and tactical matters dictated by your targeting situation (which may not be obvious), it may be to your advantage to leave it in place. You may wish to contact me (I am interested) via public library computer.
Or, use your best judgment, if worried it might should be removed immediately. Video document its removal and take it directly to a bank and get a safety deposit box to put it in… or take it to a local professional for analysis, per the advice in the next paragraph. Send me still images, in place, and after removal, if removed. Safety first, if it involves AC electrical power, and if it is in a large sealed box, don’t try to open it… such are often booby-trapped to destroy the evidence; very scary fireworks which may require the Fire Department, as it once did in a case I was investigating.
Now, about suspects, we need a warning: If you do establish a suspect, DO NOT confront individuals which you might be able to identify. Instead, try to learn as much about them or the property as possible, and add it to your notes. You should then contact me, or an appropriate professional, such as a private investigator, lawyer, or Agency. I don’t recommend Police, but if you have good readings and symptoms verified by a Doctor as not due a health issue, you might want to contact the FCC or your State’s Environmental Protection Agency, or perhaps your local County Extension Office Agent. Some larger cities may have bio-home or bio-environmental engineers or similar, who could be very good resources, if available. If there is any significant find or action taking, I would like to hear from you, and may be able to suggest ‘next step(s)’ to consider.
Specific uses
To find a surveillance or targeting device in a structure (the TI’s ‘space’) requires comparing readings well away from a suspect source to readings within an inch of it, looking for a large increase (signal strength falls off at the square of the distance). Scan low, scan high, and all around. You will want to be as physically close to surfaces as you can get, without touching, preferably (no harm, no foul, if you do). Every object and surface should be treated as a potential suspect to be tested.
One should establish ‘normal’ levels in a non TI environment (a test control space) similar to the TI’s space, and compare by taking readings at room center or well away from major RF sources (i.e., wifi, computers, tvs, radios, ovens, etc.). It should be a similar sized and designed space in the same neighborhood, between three and six homes away (arranging this can be daunting, if you do not know anyone who fits the bill, who would be willing to participate — try requests based on your own concerns in the neighborhood about high 5G signals, until you find someone who worries about 5G).
This is done in several sets of readings, each — one with those RF sources operating, and one with them turned off, and one with the Mains turned off (no AC power to the space). If subject to significant electronic attacks which can be physically felt or sensed, the TI’s space reading should additionally be undertaken as sets during both times of no sensed attack, and during an attack (which may prove difficult, if under surveillance — the perps may elect to cease the attack once you set up for the readings… which might buy you some peace.) You should also take readings at the power company meter at both spaces at a time of day when major appliances are not in use, and note how fast the meter is changing, and in the TI space, take an additional reading when the mains are turned off.
Finally, you will want to walk around the space on the outside taking reading pointing away from the center of the space, looking for hot spots. Directional is King, here.
To test for bio implants in a person or a tracking device on a vehicle, the best place will be in the country, away from any nearby potential sources for such signals… such that ambient broadcasts and distant cell towers are about all that’s being read. All cell phones and the like should be turned off. Don’t try to find an implant on yourself, have someone else take the readings. Every inch of the body should be scanned, and I suggest wearing a simple nightgown, PJs, or a bathing suit. Feet wide apart, arms held out to the sides. Be willing to get fairly personal. One then verifies by going on past the body in the same direction to insure the reading is dropping, again.
If a vehicle, pop the hood and trunk and doors to scan the interior areas, it being OK to lean into and ‘look about’ with the meter, just trying not to aim directly at the sky. Don’t forget under the seats, fender wells over the tires. It would be nice if you could put the vehicle on jack stands so you could safely get underneath it (where aiming upwards at the undercarriage will be fine). Jacking each corner up as if changing a tire is much more work… but avoid actually going under the car with any more than your arm. You will want three sets of tests, one with the engine running (in Park or Neutral, Emergency Brake set), one with battery connected and the key in the accessory setting, and one with the battery disconnected. That will tell you if any suspect readings are from something drawing power off of the car, or if it is battery operated (which means something bigger, and easier to find in a visual search). So, be sure you have the needed tools.
What do results tell you?
- Where readings are higher during an attack, DEW is all but confirmed, and additional steps (T1, at document end) will be needed. Where they are not, and the attack was sensed, the sensed effects are more likely to be a health issue (all TI symptoms are carefully designed to mimic health issues), and you should seek medical advice, describing only the symptoms, not TI concerns. Get a second opinion using a random Doctor. If no high readings and no sensed attack, try again… and again;
- where readings are higher in the TI space with all power off, than in the control space in like status, it indicates battery operated surveillance is likely, take steps (T2). If the same, it implies that any perp equipment present is drawing power from the house by any number of means, use step (T3). NOTE: it is certainly possible for both to be true;
- where readings are higher when RF/EMF equipment is turned on in the TI space compared to the control space, it implies that the equipment operating is either defective, or perhaps weaponized against you in some manner, take steps (T4); If the same, it implies them safe;
- where readings are higher when the equipment is turned off than in the control space, and the first part of item (2, above) is false, it implies the AC power system has been weaponized, take step (T5);
- where power meter readings are higher in the TI space than the control space, it implies the Meter is relaying a lot of data from perp devices… just good to know, as the other tests will address needed steps. If not different, it implies the meter is not a Smart Meter, or the meter has not been weaponized to relay data. Relay of perp data does not imply the power company is the recipient or participant, though it is always possible;
- where power meter continues to draw power with the mains turned off in the TI space, it means there is the possibility the perps are drawing power off for their devices directly from within the mains junction box (circuit breaker box), and may include electrification of the ground to create high EMF readings in the home, and likely, the embedding of targeting signals within the AC wiring. Take step (T5).
T1 (DEW test). You have had positive space readings within the structure and they point to DEW presence. You now need to do external readings at both spaces by walking around the building site and taking reading pointing directly away from the center of the building or room of concern (don’t sweep left to right — you walking in a hypothetical arc about the center point, instead).
Compare these to the interior readings at the same compass heading. If there is no agreement, the source is likely inside the structure: do a 180 and sweep to confirm, directly along the outer wall surfacwes. If they do agree, compare the average signal strength. If it is a notably higher, then the source is relatively close, and in theory, if there was nothing in the way, and the source was left operating, you could walk toward it until you found it… such as a neighbor’s home. If it is not exactly higher, then it is much further away, and you may want a bicycle or car to chase it down.
T2 (Batteries). Battery operated devices are bigger, and easier to find because they will require a nook or cranny. Do a visual search for anything that is unusual or foreign. Do not remove it. Video the discovery with audio description. It may require some disassembly of door panels, carpeting, dash components, etc., which may mean professional help or tools, in which case, you must be present and video. Contact me with the circumstance and send me still images of the object, that I may suggest the next steps. Do this covertly, such as by use of a public library computer.
T3 (No Battery). That means it is either hidden within an appliance (i.e., TV, stereo, blender) that is always plugged in, or it is wired somehow directly off of an AC power line, perhaps in wall or atic, under floorboards or behind baseboards. If the meter is pointing towards any such appliances. Unplug those items and move them aside, and take readings, again. If the readings fail to match, plug them back in elsewhere, and read again at the new position. If they again match, they need to be dismantled, looking for anything that seems added. You may want to take it to a repair shop, if unhappy at the thought of DIY (some items have voltage capacitors which can cause severe electrical shock even if the item is unplugged). You have to worry about such items on the far side of the wall, as well, by the way.
If the appliances don’t change the readings when removed, or there were no appliances, then we worry about wiring in the walls, floorboard, and ceiling areas. Aim the meter at angles to see if there is any confirming change in readings. If low angles are hotter, you may need to pull the baseboards, wall power outlets, or get under the floor (i.e., basement ceiling area). If high, there may be ceiling molding to be removed, or you may need to worry about something upstairs or in the attic ((where you will be wanting to follow all the house wires, looking for a cut and splice with something dangling (perhaps another long wire to chase down) off of it)). Otherwise, we check light switch wall plates, picture frames, wall hangings, or window sashes, etc., as may be in the line of sight of the reading. Again, be mindful that walls have two sides. Watch out for fiberglass or asbestos insulation… you don’t want to be messing with that without serious protective clothing.
T5 (AC Power Compromised). Consider to contact a Home Bioengineer or a large Electrical Contractor who is capable of doing large-scale power system work (i.e., can contract to build sub stations and the like — which means they know more and have better tools than ‘an electrician’). Go directly to the Power Company if there is no such services in your area. The idea is to complain about dirty power and possibly high ground voltage (say nothing about targeting) and ask for a power quality survey. If they find anything wrong, they should be able to fix it or arrange for the power company to fix it. Simply going to the power company first may not be a great idea, if they have been compromised and are complicit.
Shielding Solutions
See the document on Shielding which is also included with the Helps Kit, or request a copy.
Emergency/Help Phone Numbers You Might Not Know About
Most everyone is familiar with 9-1-1, 4-1-1, and 6-1-1 numbers in America, but there are other equally valuable three-digit numbers worthy of remembrance or plugging into your contact list. And that includes the equivalent numbers in other countries, when you travel.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
Dateline, May, 12, 2020, from an emergency lockdown bunker in an undisclosed location
copyright © 2020, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting. NOTICE: Fascistbook and their ilk (Twitter, et. al) blocks any URL to my blog site. SO, if you wish to POST comment in social media, you may wish to write out the url with spaces between wordpress and com (no dot), instead of supplying a pasted link.Duh!
I can’t think of anyone who has not used 9-1-1 to call for help in a law enforcement, fire, or medical emergency, or to report something in need of Police investigation or intervention. Almost everyone with a cell phone knows that 4-1-1 is directory information, and that 6-1-1 is commonly used to reach their carrier regarding issues with their cellular account or the phone, itself. But what about 2-1-1, 8-1-1, and other numbers in the series? Not so much. Even more problematic, is what happens when you are in another country. What numbers do you use, then? This post will answer that, and give you all the numbers for popular North American destinations.
While there is some international cooperation in assigning such numbers, there remain vast differences. The European Union, has its own set of numbers, and while the UK employs some of them, they also have their own set, devised before the EU had existed. Yet Australia, New Zealand, and Canada are slightly to vastly different from England, Canada almost identical to America. Asia and the Middle East is a hodge-podge, while South America is a bit of hodge-podge, but like Canada, also employs 9-1-1 for the main number. Some countries, like Mexico, have sort of ignored the issue (both the government, and citizens – see note), though they are at least using 9-1-1, as of late. Africa is just plain behind the times, you will need a different number everywhere you go, in most cases.

Fortunately, it’s not at all hard to find out what emergency numbers are available when abroad, and it can be done online easily before you travel, at WikipediA, where almost every country is cited. One can also search on ‘emergency phone numbers’ + (country name). Travel agents, airline and cruise ship firms, State Department offices and any Embassy (any nation), will generally have the answer. If already in the country, any citizen should be able to at least give you the key-most emergency number for fire/police/medical… if you both speak a common language.
You can see why programming them into your phone beforehand might be a good idea.When abroad, you should always program the local US Embassy or Consulate number into your phone, as well. And, btw, before you travel, check with your phone company about how to avoid huge phone bills while abroad. It is easy to run up bills into the thousands of dollars, if unaware. There are several things you can do, including purchasing a temporary sim card with a foreign carrier, or special temporary rate plans from your carrier. Just know that your cell carrier may not be interested in telling you about options they can’t make money on, if they do not have partnership arrangements in place, overseas. So your travel agent and the like may be a good second-opinion resource. Image: WikipediA.
Dial!
The American system would seem to be far more robust than many other three-digit systems. The list shown here also includes Canadian numbers, which do not necessarily apply outside of Alberta, British Columbia, Manitoba, Nova Scotia, Ontario, and Saskatchewan:
America Canada Service
2-1-1 2-1-1 Community health and social services: suicide prevention, welfare programs, access to free services such as for food, housing, legal aid. Includes State, County, public/private entities. An operator will inquire as to need, and provide suggested local contacts.
3-1-1 3-1-1 Frequently available in larger cities, similar to 2-1-1, but Municipal.
4-1-1 4-1-1 Directory Information or ‘operator.’
5-1-1 5-1-1 Available in many areas: automated road condition reports, and a means to report accidents and road hazards not require 9-1-1 help.
6-1-1 6-1-1 Direct contact with the cellular carrier’s customer support.
7-1-1 7-1-1 Reserved, not in use.
8-1-1 In most locations, connects to a centralized information system for utility services, principally to locate underground lines. It is currently not used to report problems, but that may change in the future.
aaaaaa.aa8-1-1 Tied to the national health care system for urgent care requests.
9-1-1 9-1-1 Police, Fire, Medical emergency ONLY. Also good in Mexico*, Bermuda, and the Bahamas.
*Mexico is began implementing 9-1-1 in 2017, but may not be in service in less populated areas, and the person answering may not speak English and a transfer to someone who does may not be very fast. Previously, Mexico had separate 8 digit numbers for fire, police, and ambulance, and those numbers remain in place. The Military has its own phone number for crime-lord response, but Citizens tend to have no faith in any such services, there, because help seldom responds, or they do not trust Police/military. A group called Angeles Verdes (“Green Angels”) offers roadside aid and travel advices, tourist helps, answering in English: dial 0-7-8.
Doh!
I almost forgot the handy ‘star codes’. It’s amazing how many people don’t know them… or have forgotten them (like me, almost). Star codes are also a three keystroke ‘number’ made up of two numerals preceded by an asterisk keystroke, found just left of ‘zero’ on the dial pad. They are also known as ‘Vertical Service Codes’ (VSC), Custom Local Area Calling Codes (CLASS, or LASS). They allow the you to directly interact with the digital telephone switching system, telling the hardware how to handle a given call situation differently. They can provide improved privacy/security or added feature-benefits in how you use your phone. Like the previous 9-1-1 numbers (save 6-1-1), they generally apply to both cell phones and land lines, though some function only on one or the other.
There are some 33 different codes in all, many in the form of paired codes, one to turn a feature ‘on’, and another for ‘off.’ Many are special functions tied to the type of phone account the subscriber has, or to optional features for an extra charge, and some would seem unlikely to be used very often. Some smart phones internally employ star codes such that the user is unaware, and does not need to know the code, such as when blocking a number. Because of these various variables, you should visit your service provider’s Web site to see which codes are specifically available to you under your service plan, and review your phone’s handbook to see how it might be handling such provisions.
However, there are several very important star codes which apply to everyone, which you should commit to memory, because all phones will work with them, and you don’t always end up using your own phone. Too many of them to detail, here, but there is a handy list at WikipediA. Scan the list and take a bit of time to mouse over the blue (hot link) text on their page, for a popup explanation, as the short description may not prove as useful in your evaluation. Click it if more text than will fit the box is apparent.
Take note of things like anonymous call rejection, call blocking, caller ID controls, and call trace. That last one is used when calls involve threats or are in some way malicious to you, your phone, or the phone company; it reports it to the phone company and can result in a notice being sent to Police and/or a joint investigation through the phone company. If particularly threatening or criminally harmful, you should also file a Police Report, and include the time/date along with the fact that you did use star 57… because Police will not otherwise contact you from just punching in the code, and just pushing the code alone won’t give Police the full story. I use it when I get calls from impossible phone numbers (scammers), and I let an appropriate agency know about it, if warranted.
Datum!
WARNING: Phone Apps for TV a Bad Idea
Smart Phone EMF App No Value to TIs
Your Cell Phone is a Government Agent Spying on You
Proving The Mandela Effect, and Ties to Project Rainbow
When it seems there is a cover up of military experiments some believe responsible for accidental time travel and teleportation… to include the possibility of sponsoring the Mandela Effect’s alternate timeline realities… thus establishing two different but intertwined conspiracy theories, each with their own cover up… I’m extra suspicious. And, with good cause, it seems.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
Dateline, Aug, 29, 2020, from a mobile TV studio at an undisclosed location
copyright © 2020, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.Rod, we need you…
Imagine if you will, the audio intro to The Twilight Zone. Only Mr. Serling is nowhere to be found… in our current timeline. And, given the nature of this special real-life episode, in which everyone reading this post is onstage and playing a roll, we might just need him to help us work through putting this particular show together. It might properly be entitled, The Mandela Effect, and if to learn some useful truth along the way, Rod might hint in his introduction, that it “has to do with something called the Philadelphia and Montauk Experiments… in the Twilight Zone.”
The term ‘Mandela Effect’ (hereinafter, often referred to simply as the Effect), is derived by the first noted instance of the Effect, regarding the South African anti-apartheid activist, Nelson Mandela. When it was announced that Nelson was released from prison in 1990… untold millions of people began commenting that they were certain they had heard/read news reports of his death in prison, in the early 80’s… for which no one could find evidence of such death notices. At the time.
Over time, as other events in his life made international news, more and more people began to say much the same, in some cases, citing other time frames for his death. So many people, in fact, that a seeming cover up effort began to emerge, a matter which will play a role in this particular script, as it evolves. Fortunately, as it happens, at least one Fan of the old black and white TV show happens to be a ‘conspiracy theorist’ willing to stand in for Rod. And he… err… rather I, am ready and able to attempt filling in, with my own not-so-insignificant investigative writing efforts and findings.
 For my qualifications in such an effort, may I submit my RAP Sheet of crimes and conspiracies solved or thwarted. Here, in this post, I start with a brief summary of the how and why of my efforts, which led to a means for testing for the validity of the Effect, quite contrary to tremendous efforts to dismiss it as ‘mind tricks some people play on themselves.’ In doing so, I also show significant relevance to the U.S. Navy’s Project Rainbow, better known as the 1943 Philadelphia Experiment, which allegedly caused a WWII Destroyer, the U.S.S. Eldridge and crew, to both travel in time, and teleport between multiple locations.
For my qualifications in such an effort, may I submit my RAP Sheet of crimes and conspiracies solved or thwarted. Here, in this post, I start with a brief summary of the how and why of my efforts, which led to a means for testing for the validity of the Effect, quite contrary to tremendous efforts to dismiss it as ‘mind tricks some people play on themselves.’ In doing so, I also show significant relevance to the U.S. Navy’s Project Rainbow, better known as the 1943 Philadelphia Experiment, which allegedly caused a WWII Destroyer, the U.S.S. Eldridge and crew, to both travel in time, and teleport between multiple locations.
There are two motion pictures about the Experiment, sharing its name, but only the 1984 version is worth a watch… presuming the viewer realizes it is a fictionalized presentation. The 2012 TV version, is not only badly done, but it is so fictionalized as to anger anyone who knows anything about the legend, be it through the first movie, or any actual researched source. What the movies leave out, is that Nicholas Tesla and other famous Einstein-caliber scientists (including Einstein), have variously been linked to the Experiments, in one way or another. In fact, in the final proofs this script leads to, if you choose to follow it, we find modern scientists who essentially verify a lot of that, and who validate the science behind the Experiments… including a reference to a little known WWII era radar-defeating experiment by the Third Reich.
Note: that little tidbit should get the attention of anyone who follows the Nazi UFO/underground base in Antartica conspiracy theories, given that many of the same principles described in early anti-gravity theory were also present in the technology claimed present in the Eldridge and Montauk saga.
While in this author’s view, the cover up of the Effect is not much more than psyops disinformation, there is a significantly more complex cover up in play, on the cited Experiments (hereinafter, also capitalized to represent all such events), themselves. The intensity of the coverup has, in fact, more than kept pace with interest in the Effect, as more and more people take note. Restated, the more people become aware of the Effect, and especially if exploring possible ties to Experiments, someone was insuring that ‘the explanation’ is even more ‘available,’ in an attempt to dampen their fervor in trying to figure things out for themselves. It has transformed from mere disinformation, to full-blown cover-up dirty tricks and psyops.
Sorry, (Men in Black), but I’m rather impervious to such forms of artificial moisture.
Dirty tricks and psyops? As with all really well-done cover ups (i.e., Flight 800 shoot down, JFK assassinations, 9-11 false flag), the very facts and evidence behind the Experiment theories are being deliberately contaminated with sets of conflicting evidence and testimony. These are being established within various narratives to make it impossible for the average person to know if any of it, is true. This is augmented by being pointed out as disino-style straw man ‘debunking.’
For example, the actual location of the 1943 test is variously and additionally described in the effort, over time, as actually taking place in (and/or teleporting between) Philadelphia, New York, and Portsmouth/Norfolk, VA… all while the ship was allegedly actually at sea in a shake-down cruise. This is the hallmark of all good cover ups; alternative versions of the story, by means of fabricated, altered, or concealed evidence. One other clue which renders them suspected cover up efforts, is that collectively, each seems a de facto denial of the remarkable experiment results, altogether.
There was, in time, even a parallel Project Rainbow being run simultaneously by CIA and Lockheed, aimed at developing radar stealth technology, such as we see in the F111 fighter and other aircraft, today. Duplicate-sounding programs is another means of confusing and concealing facts from inquisitive minds, and it wouldn’t be the first such duplicate employed in the evolving saga. If there were no remarkable results in 1943, why so much effort to obscure with alternative versions of the tale? The effort over time drew in more and more, and wilder and wilder additional conspiracy theories completely unrelated to the original event… everything from mind control, abductions and child abuse, to government deals with intergalactic aliens and teleportation to Mars. Suddenly, it sounds more like TV’s Star Gate, than Twilight Zone.
Ironically, perhaps… despite the many attempts to confuse and defuse, has not quite worked out as intended. All those alternate versions can and have been argued by the faithful believers… as ALL being true, by virtue of the Experiments having created alternate realities — exactly why the Experiments are suspected as causing the alternate timelines of the Mandela Effect, in the first place. Thus… the legend grows with every twist and turn added, be it by coverup, or by daring to dig deeper, such as done by the earlier mentioned scientists seeking to verify validity of the claimed Experiment technology. Argh! How do we discover the truth in this vast sea of complex and contradictory information?
Not to worry; the show gives us roughly an hour’s script, within which the truth may yet be found…
Is the episode to be mere fiction, or based on fact?
Make no mistake: because of the extensive nature of the cover up, ‘alleged’ is the correct word for virtually anything online relating to the topic, thus far. Hopefully, this will change that, and make it easier to find one’s way through the distortions to the truth hidden within. Because, here and now, it becomes a matter for you to decide, based on new proofs, herein described. The good news is, the Mandela Effect itself becomes the key to the greater U.S.S. Eldridge saga… and vice versa, in mutually reinforcing ways. Both share newly discovered and consistent patterns which more than suggests Experiments indeed have a causal nature to the Effects. This will also lead to a plausible theory as to how teleportation may also indeed fit into and be part of the correct view of the entire episode. The Network Studio Executives, would be proud, and advertisers, pleased.
More astute followers of the Philadelphia theories know there is some evidence which alleges that Rainbow research quietly resumed in 1948, likely leading to renewed Experiments in 1960 at Brookhaven Laboratories, in central Long Island. Under the new codename of Phoenix (in time dubbed Phoenix I and II), it seems it may have continued almost yearly until 1976, under a US Air Force and Navy partnership. Next, they were relocated to Montauk Air Force Station, at the tip of Long Island, at what would become a largely underground complex known today as Camp Hero. Preparations for the move were underway as early as 1973, because of a need for a larger radar system which would make the top-secret research too obvious, at Brookhaven.
Note: True to form, for much of this period, CIA was running another Project Phoenix simultaneously with the US Army, in Vietnam; an assassination program from within which would evolve the two top people first put in charge of Homeland Security, once formed.
Like the Philadelphia Experiment, Montauk, and all related experiments were allegedly shut down in 1983 — after things went terribly wrong, and conclusively believed co-causal in the 1943 Eldridge event — not to mention the alleged teleportation of some kind of terribly powerful monster from another (world? dimension? time?). Remarkably telling, the Montauk monster release took place on the exact same date as the Philadelphia Experiment, exactly 40 years later… creating a time-tunnel, or sorts, between the two dates and locations. These events allegedly led to all experiments being shut down.
Between those two dates, however, more than a dozen different Experiment dates have variously been discussed among Web resources and books on topic. I selected the ten most compelling, and with success of early testing and by additional deduction, I have proposed a two other dates which I hoped could be shown valid by fitting into any observed patterns. They do fit. Technically, it was possible and even likely that experiments of some sort took place every year, often several times a year, post 1960 Brookhaven.
I also point to clues that Area 51 has for some time been operating equipment which fits the Rainbow~Montauk technical descriptions very closely, things evidenced with Google Earth’s 3-D building’s feature (not official; created by followers of the Area 51 mythos, generating and updating 3-D GE compatible constructs alleged to be based on rare photographs and eye-witness verbal descriptions, over time). Thus, it at least seems, experiments may have continued post 1983, as well, which may account for the bulk of Mandela’s death dates to be beyond the 1983 date, and as recent as 2013.
 Google Earth: 37°14’4.04″N 115°48’16.60″W 3-D Buildings and Terrain turned on
Google Earth: 37°14’4.04″N 115°48’16.60″W 3-D Buildings and Terrain turned on
Handed the script while on another project…
 I did not set out to do any of this. I was aware of and have experienced the Mandela Effect, myself, both with respect to his Death, as well as other, less significant things of the ‘mind trick’ variety. The (cover up) ‘mind trick’ explanations typically involve words or spelling issues, such as names of things in media or pop culture; Chic-fil-A vs. Chick-fil-A, Sex in the City vs. Sex and the City, etc. These things have become strawmen easy for disinforming cover up efforts to ‘shoot down’ the Effect as mere memory recall errors playing tricks on our mind in some kind of mental placebo-or mass-hysteria tom foolery. Such explanations are themselves mind tricks, and work only because no one can come forward with hard proof in the form of an original date where an event or item can be shown to have been changed in our conciousness, as well as demonstrable factual proof beyond history’s official version.
I did not set out to do any of this. I was aware of and have experienced the Mandela Effect, myself, both with respect to his Death, as well as other, less significant things of the ‘mind trick’ variety. The (cover up) ‘mind trick’ explanations typically involve words or spelling issues, such as names of things in media or pop culture; Chic-fil-A vs. Chick-fil-A, Sex in the City vs. Sex and the City, etc. These things have become strawmen easy for disinforming cover up efforts to ‘shoot down’ the Effect as mere memory recall errors playing tricks on our mind in some kind of mental placebo-or mass-hysteria tom foolery. Such explanations are themselves mind tricks, and work only because no one can come forward with hard proof in the form of an original date where an event or item can be shown to have been changed in our conciousness, as well as demonstrable factual proof beyond history’s official version.
Happily, such cases do exist.
My first discovery of such proofs, which led to finding others, came about because I was writing my autobiography (I am, after all, ‘semi-famous,’ if you didn’t know — 14M pages reference me or my works). I wanted the best accuracy I could manage with respect to various experiential details, especially if relating to truly famous people I have been involved with. That meant research, and one such item researched happened to regard legendary Olympic swimming record breaker, Mark Spitz. All I wanted to do was to verify the number of Medals he had already won when I first met him, a thing we spoke of, at the time. But what I found in addition, was that it couldn’t have happened, at all, if believing the current history timeline… it was some kind of time-travel paradox!
On December 29, 1963, just as the extra severe Winter blizzard that would pummel the central U.S. all they way to the Gulf Coast was starting to roar, I spent four days on a train trip to Texas, from Oregon. The storm covered most of the nation in deep, wind-driven snow, and the train indeed had to, at times, run with a snow-blowing engine ahead of it. Quite by chance, I was seated part of the way next to Olympic champion swimmer, Mark Spitz, only because the heating failed in several of the cars, and everyone was herded into the two cars with at least some heat, where seating options were limited. We chatted, both as ‘ice breaker,’ and to while the hours away in an unscheduled layover in Denver, while they addressed the heat, so that Denver passengers could board, and travel in warm safety.
I immediately knew who the fellow I shared a seat with was by his pictures in the newspaper, for having recently won four different medals in international pre-Olympic competition a few months earlier — the very details I sought to verify at Wikipedia, for my book. He confirmed it, himself; we talked specifically about that and related matters for some time… as the windows were frosted over and there was no scenery to enjoy. The reason for his trip, was related, something to do with training, and his goal to win Gold at the Olympics. He would do that, in time, winning more than anyone else, ever had, and I would follow his career with great interest, because of having met him.
TODAY, however, the official online history says he didn’t win his first medals until 1965, and that when he did, he was three years younger than I was in that same year. In our trip, he was a year OLDER, which meant he was born in 1945, instead of 1950, as officially so, today. That makes a five-year error in his birth date, and a two year error in his first Gold medals date, from 1963. It was impossible for me to have recognized him for medals he had yet to win, and I know when our trip was, the only time I’ve taken a train to Texas… as I was to live with my Aunt and Uncle while my parents worked through their divorce, and to finish my Senior year, there. I did graduate from Hardin-Jefferson High School in 1964, and then returned to Oregon, by air. The date of the trip was defined by Christmas school vacation, and such that my arrival date would allow quick enrollment in the 1964 school year, in Texas.
The paradox hit me hard. It led me to wonder what else in my life might suffer the Effect. I quickly researched the details in other matters for which dates could be verified. I indeed encountered two other examples for which I was able to know the original date because of personal experiences, and the current timeline historical date, both turning out to be mutually exclusive and yet paradoxically so. These are recounted fully in the linked (at post bottom) Study material, which is the ultimate proof, as herein referenced… validating the Experiments, the Effect, and causality.
The plot thickens…
But documenting these would not be enough; my personal experiences cannot be well proven to a Doubting Thomas; it could be dismissed as something made up, or misremembered. I still needed things I could prove with hard evidence, rather than personal testimony, alone. And that’s when I started to investigate Mandela’s death in hopes of finding such proofs. In the attempt, I was able to prove for once and for all, that he did not die twice, as believed.
What?
No. There is, in fact, rather convincing evidence which seems to show that he has died four times, one of which, was a murder. Most people recall his earlier death as being in the early 80s, with no way to prove it. Others in the mid 80’s, with no proof, some recalling it was a murder. A few remember 1991, with no evidence. His current timeline death, is cited as Dec 5, 2013. But now, various proofs do exist which would seem to validate everyone’s memory, and refute all the faulty memory or hysteria mind-trick ‘explanations’ which serve to cover up the truth. But there are two additional things true about them. For one, each has an inherent problem which would certainly seem to neutralize them as evidence. But the other, is that the very nature of that problem is, under the theory, itself called into question as to actual meaning.
In fact, if the other proofs revealed herein, were correct, they would HAVE to be the way they are, and serve as their own kind of ‘reverse logic proofs’ in an ironic manner. They validate on the surface, self-repudiate on close examination, and self-validate when fully informed, yet again. These verifications and proofs for each, are briefly described as follows, in the order in which I found them, but the repudiation and self-validation will be covered later in this work, where it will be easier and make more sense:
• A 1983 high-school report about Mandela helps fix a death date of March 11, 1983. The Report was assigned because of his Death, that year, and the aftermath of political upheaval it had promoted. As of yet, there are no photographs, and arguably, such would be easy to fake, and the source is easily discounted as unathoritative; several online comments by the student, now an adult. These were in chat rooms, for which a link is pointless. The date, however, will check out, in the Study, and is therefore included.
• Next, a South African periodical, published Oct 1, 1991, includes remarking about his 1991 death, and the reader can verify, directly at Google Books. The small book is a collection of S.A. student English language writings published serially each year. Subsequent editions, therefore, no longer have the reference, a matter also verifiable towards the bottom of the same mentioned link, where other years are also listed. Be aware that Google Books for some reasons includes material from both the 1990 and 1991 editions when searching, and does not enable the user to scan up and down. I have, however, obtained the full text, after a great deal of effort, and can confirm it comes from the 1991 edition.

• Finally, a follow-up Northwest Herald newspaper story via a cell phone streaming service was captured in screen shots which reveal Mandela’s murder in 1985. There are several online images found in chat rooms and the like, and a very short and creepy YouTube. This has been verified by a reputable national newspaper historical repository (newspapers.com). Access requires a paid subscription to the service, it being intended for serious researchers. Again, I have managed to access the full article, and the image is legitimate. The video shows multiple views at various scroll points within the document, to reveal more details… but offers no explanations, just creepy music and unpleasant visual effects. This is the best image taken from it, to save you the grief.
The show is ready to air… cue music; stand by, Mr. Serling…
I therefore set about to catalog all dates into a Study group spreadsheet, with calculations as to years between dates, to look for patterns. Along with that, a duplicate Control group based on dates randomly created by Excel’s randbetween Function was used to look for similarities in any evolved patterns found in the Study, which would prove or disprove the notion of coincidences in said patterns. And Study patterns did evolve, eight different observable patterns***, in fact… and the Control group had not one useful pattern. In fact, where some patterns did not quite seem to fit, a closer look revealed spreadsheet or data typo errors. In the end, the entire effort, from establishing dates by research to creation of the spreadsheets, was repeated and double checked countless times.
The principal goal, of course, was to not only to prove the Effect was real, but to attempt to verify the causal source. As mentioned, the Experiments were the principal suspects, but also, there were secondary suspects in CERN experiments, and in experiments involving Artificial Intelligence… specifically, the qubit computer systems by D-Wave. Unfortunately, for such suspects, very little information is known about their dates of operation.*** Regardless, findings were telling, and useful, and should lead the reader to wish to delve into the details of the Study effort, which can be done at the links beneath the findings.
Preview of Findings
Findings quite contrary to the Control Group were examined, broken into the following topical descriptions of individual findings, as taken directly from the Study. Each of which contributes to the validity of the fuller hypothesis by establishing patterns and/or relationships which also may provide clues as to the how and why of causality. Unfamiliar terms are definable characteristics of the resulting patterns, as discovered.
Bookends have Repeating Numbers: the key-most Bookends all share common separations in years between dates (repetitive numbers), which reveal patterns;
Midpoint Self-Pointing Patterns: while 1963 is an obvious Midpoint, which itself thereby becomes bookends to two halves of the greater Eldridge event years, there are many other Midpoints, select of which form circular self-pointing patterns between them.
Path-Finding Pointers: universally, the repetitive numbers in the Study group become Pointers which establish paths to the same two destination years, which in turn, point to each other;
Midpoints Pointers reveal causality clues: these clues can be visually represented as kind of ‘genetic code’ to understanding how an Midpoint Experiment or Effect might cause an original event date to shift to its current official event date;
Experiment dates vs. non Experiment dates: there is a marked difference between dates with and without Experiments. The one exception;
Pointers different between forward and backward time shifts: each forward shift shares a specific Pointer commonality, while the only backward shift has a unique and exclusive Pointer difference;
Precise dating patterns: when the full Effects and Experiment dates are known, they reveal exactly one year, or one year plus six months between, leading to a new hypothesis regarding the ‘mechanics’ of Experiment timeline shifts which result.
The results of the findings led to the following conclusions:
- Key Event dates which lay entirely within the range of known Experiments, and which fall on the same dates as Experiements, establish a common pattern between them, implying a causal relationship may exist;
- All other Event dates, and Experiment dates, not sharing a common dating, still do exhibit the same patterns, providing high confidence in a causal relationship;
- Because AI and CERN experiment dates cannot be known, neither can neither be proven or disproven as being causal to either the Event or Death dates evaluated, at this time;
- While the dating of Mandela’s deaths lay outside of the known Experiment dates, several of the patterns nonetheless exist in their dating, and relate them to the Experiments usefully, and yet, leave room to suspect that other forces may also be causal, such as CERN, or AI, or perhaps continued experiments elsewhere, such as at Area 51;
- No patterns of like kind were observed in the randomized Control Group, validating the Study patterns as non coincidental or random happenstance, in nature;
- The patterns observed, do collectively and mutually validate one-another as strong indicators of the overall Findings’ validity;
- The patterns allowed confirmation of suspected Experiment dates for Brookhaven 6 (1968), and 8 (1972), as fitting the patterns, when added to the Study group for comparison, and refuted other dates born of ‘what if’ theories developed along the way;
- The patterns revealed a difference in a detail of their nature between Events shifted forward in time, compared to Events shifted backwards in time, thereby providing clues potentially useful in eventual understanding of how the distance and length of time shifts are established;
- The patterns observed also revealed a curiosity; in that Event pair (original and current timeline) dates are, with one curious exception, always exactly apart by (n) years, to the day, or (n) years + six months, exactly to the day, resulting in additional theories about causality, as described in the Study;
- Therefore, the Mandela Effect is demonstrated to be real, and its cause is demonstrated to be due the suspected Experiments.
Self-repudiation and yet also self-validating?
If one reviews the Study and finds it compelling, the problems mentioned within the details of the Mandela Death ‘proofs,’ can be understood in ways which render self-repudiation moot. The problems in the proofs are individually unique, and will prove fascinating, in the manner in which they both self-repudiate, and yet, self-validate. The self-validation, which neutralizes the repudiation, remains the same for all, and will be offered in the closing paragraphs. In the end, however, it is also true that the Mandela deaths have no impact on the Study, as they fall outside of the suspect Experiments dating, or fall on dates of such experiments; removing them altogether from consideration does not alter the Study findings in any consequential way. The same Findings would still be similarly arrived at, with the same level of confidence.
The student’s chat room comments about his homework papers are self repudiating simply because it is (thus far) impossible to reach him, to seek a copy of his paperwork from high school days, and because it would be easy to fake hand or type-written school report materials. People fake things on the Web constantly, thinking it great sport to be so ‘clever,’ to presume a hoodwinking lie somehow equates to intelligence.
The book quote proves problematic, because once you acquire the full text of the three page article, we learn that it is part of a fictional speech, entitled, ‘His Closing Speech.’ Within it, many historical events are referenced, several with precise dates, and all but two prove to be completely accurate. I’m not including Mandela’s death date in either category, for the moment, and the two which do not seem accurate, have the potential of being accurate, as each may be simply a different way to reference events which did take place, but are described in different terms than perhaps commonly used in the day, by locals, as opposed to the official national/international narratives. The paper, however, starts with the sentence “In our minds, let’s go ahead exactly one year in time…” After a short soliloquy, the ‘speech’ begins, a speech by someone revealed in the last paragraph, to be a judge, about to pass sentence on former South African President William de Klerk, for crimes of apartheid. Also, in the closing lines, we get a date which, if the ‘exactly one year in time’ is explicitly correct, indicates that the article was written or presented on 15, March, 1991. But the piece, looking back from the ‘future’ on 23, July, 1991. This self-repudiates the date as being historically correct.
The newspaper article, once you acquire the full article, self-repudiates, because when you have the full sentence, you see that well placed commas reveal that Nelson Mandela was not among those found murdered on the road, but some other unfortunate anti-apartheid activist, and friends. It reads, emphasis added: “UDF organizer Matthew Goniwe, hailed by blacks as possibly the most important dissident leader since jailed African National Congress President Nelson Mandela, was found murdered along a rural road in June.” False grammar assumptions killed Nelson Mandela, it seems. Whoever originally posted this find, is likely one of those ‘intelligent’ liars, seeking to deliberately deceive.
How do these self-repair their repudiation? I’ll start my explanation by repeating something I heard a famous scientist say, once. My wife and I, when I was a successful business man able to afford the $250 tickets, would attend a series of lectures by famous scientists and other brilliant minds in various fields of endeavor… something akin to Ted Talks, today. After each, there was a reception party, and these were variously attended by other scientists and minds of like kind, giving us a chance to mingle among them and engage in stimulating conversations. One such attendee, a physics professor, said something along the lines of this: “All of nature, as describable in physics and other fields of science, contains the very clues of its own explanation for being, hidden in plain sight, awaiting only the ingenuity of Man and his ability to test and measure, to discover the truth of it.” The guest speaker, himself a Physicist, as I recall, agreed.
To me, this means that if there is an alternate and paradoxical timeline created by some aberration, there will be some form of a clue within the paradox, itself, which can lead one to the discovery, and proof of it. This perfectly fits with the general view, that in order for a timeline shift to take place, the very nature of the resulting paradox MUST alter all documents which reference any historically noted differences between the two timelines. It must do so in some way which both accounts for them, and yet refutes the differences. Therefore, it would make perfect sense that some aspects of the former, would be contained, and yet be altered in alternative accountings of the later. This means, that if the Study as linked, herein, adequately proves the basic contention that the Mandela Effect dates are not random in nature, but establish patterns which validate them in some way which simultaneously ties them to, and validates the causal hypothesis… then the very existence of self-repudiating proofs floating to the surface, self validates them once more, and neutralizes the repudiation. I am satisfied that it does, pending someone proving otherwise.
In summary, I am putting forth the hypothesis that these remain clues to the Mandela Effect which bolster people’s memories usefully. But regardless of if that be correct, or not, it does not alter the findings of the Study: the Effect is real, there are multiple timelines, and the cause is identified.
But like all episodes of the Twilight Zone… not every viewer walks away with the same appreciation of the presentation. So, if you have never experienced anything along the lines of the Mandela Effect, and/or otherwise remain unconvinced… you may prefer to watch Outer Limits, instead, where the Matrix tells you, “We are controlling transmission…” and admonishes you not to adjust your set, because the Matrix wants you to believe in and follow it, and not think for or believe in yourself.
Why is the Truth About A.I. Risk so Hard to Find?
We keep hearing scattered reports of AI gone wrong… about experts with concerns… but just try to find a single compendium of the whole truth online. THIS appears thus far the only one… and for a reason.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
Dateline, March, 18, 2019, from the Olympic Peninsula, in the shadow of Microsoft
copyright © 2019, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.What you will learn in this post
- The true analogous nature and behavior of A.I. is as unpredictable and potentially dangerous as might be alien visitors from another World;
- that a lot of people talk about A.I. in media, but only offer glimpses for some reason;
- what that reason might be (a technocracy driven conspiracy);
- what the technocracy is;
- of the many kinds of A.I. and A.I. risks;
- how A.I. works and how that relates and contributes to such risks;
- the many failures, unexpected results, and dangers thus far experienced;
- why it is highly unlikely such dangers will be usefully addressed until too late;
Note: this is a long post rich with information critical to any useful conclusion about Artificial Intelligence (A.I.) If you are someone who likes to form or confirm your beliefs based upon headlines and blurb-like summaries or YouTubes without much factual substance, you will not like it, here. Reading time is 30-40 minutes, unless following some of the many resource links, which will delay further.
It is intended that the reader decide for themselves what is true and worth taking away. Please see About the Author at post end to test my credentials for writing this post with useful reliance; I am not without bona-fides.
Why this post?

From Ghana News Online opinion: An A.I. a day… Medical A.I. benefits http://ghananewsonline.com.gh/opinion-ai-day/
I’m pretty sure the reader will find this the most comprehensive and useful article on the matter in lay terms, anywhere, short of a book — and the most complete in cataloging specific examples of A.I. gone wrong, and associated fears. Scattered reports of failures and forecasts of doom keep popping up here and there… but trying to find a comprehensive review is simply not possible. For some reason, no one who should is willing to confront it head on with the full revelation. But you can find many click-bait sites that like to talk of sci-fi SkyNet or realistic-looking humanoids taking over… things which are not impossible, but highly improbable… at least any time soon. We need balance.
I think I know why we are being kept in the dark and fed dystopian mushrooms and light-hearted reviews of things gone wrong, instead of full disclosure. While the reason might tend to put some readers off, my being right or wrong does not change the meaning or value of this post, though if right, you should definitely want to know. I speak of a cover up, and remind you that any form of cover up is, in and of itself, proof that a conspiracy of some sort exists. In this case, there is at least an implied cover up, due to the fact that information on topic is so scattered and incomplete, as if authorities and media are not actually trying to… or pretending not to notice. If you do not agree about my notion, that’s one more reason to read About the Author at page bottom.
There is a second component to ‘why,’ and it leads to the same conclusion. It regards the fact that few are talking about the potential disruption to almost every business market, workplace, financial and social facet of society at large… and as we have already experienced with most of us unawares (and explore, herein), politics. We are leaving the Information Age and entering into the A.I. Age, where people who look for the next big thing to bank on simply take whatever is their current thing, and add A.I. to make the thing a super-thing (or perhaps, not so super). Like the risks A.I. represents, if we look, we see no one source talks seriously about what all that disruption of ‘status quo’ might really mean; total chaos capable of toppling any empire, including governments.
I mean, just look at what the Smart Phone did to personal safety, alone. No one foresaw that people would be so glued to it’s face staring at countless distractionary things that didn’t even exist until after the phones were invented… such that with alarming regularity they would mindlessly step in front of oncoming trains and cars, or other misstep hazards. A.I. use will be much like that unexpected change, sometimes good, all-too-often, bad… and across our entire spectrum of life’s activities. I am concerned that mainstream is hardly looking at this question — and when they pretend to, it is neither comprehensive nor analytical, it is soft-soaping and even encouraging. However, I did find at least one semi-useful source, though not mainstream, which I’ve shared, herein, below.
Addressing these two mirror-like clues, my answer quickly falls to one of the oldest conspiracies, one known to factually exist, and usually just called ‘the NWO.’ The New World Order, you see, is a strange mix of ancient beliefs and modern technological investment and application; while they tend to believe in mystical occult practices based on dark religions and secrets of the ancients, they also realize they cannot establish full control through a One World Government (needed if to seat the Antichrist) without relying on significantly advanced tools. While they cannot entirely prevent the odd story of things-gone-bump-in-the-night from becoming public, with control of vast portions of media and through fostering disbelief in ‘conspiracies’ in all quarters, they can move those who should be writing about it, not to do so… and to instead limit their focus and avoid asking critical questions which might reveal the meaning and importance.
Some have given a name to the identity aspect of this particular N.W.O. conspiracy and its players. Where in the past we might have used the terms, Globalists, Power Elite, or my personal favorite, “the 1% of the 1%,” they now simply call it “the Technocracy.” And it is easy to see why, as several Ground Zero radio shows (Host and friend, Clyde Lewis) have revealed with their hard-hitting guest interviews, and of late, live calls from mysterious Deep Throat types who’s revelations repeatedly check out as accurate. It’s O.K. if you want to say I’m all wet, and the N.W.O. technocracy and all that goes with it makes no sense, but I point out it does not matter what you or I believe, it only matters what they believe… as evidenced by what they do, which is what Clyde’s broadcasts revealed.
Because regardless of what is true and real to our own belief structures, their plans necessarily include us all, and will significantly impact you and me negatively, regardless of our beliefs. That is, in fact, precisely revealed within the 33 axioms of fascism, which as a governmental ideology is an invention of and for political control they have much earlier inspired, and still rely upon. But, in understanding that at least some of you are Doubting Thomas types, I have provided some additional links at the bottom of this post, that you may investigate further, for yourself. And, I remind you that the conspiracy aspect changes nothing, true or false, except that if true, it is an even more important reason for your attention.
The question itself (why no full revelation?) is indeed a clue suggesting cover up. To illustrate, in order to compile the fuller view presented here, I had to collect facts from more than 40 different Web resources (after scanning perhaps ten times the number), roughly half of which claimed or at least inferred themselves to be just such a collections of information (but which merely sampled). Of all those resources, only two were truly comprehensive in scientifically useful ways… and yet both managed to offer no more than an honorable mention of a few concerns.
It seems no one wants to combine the two elements together for you. For that, we have to search it out, ourselves… which I did for you, here, with appropriate referencing links.
What A.I. actually is
But first, we need to understand a little bit of just what Artificial Intelligence is, and in what forms it can exist, also a thing you tend not to find easily on the Web, without getting into truly scientific papers (which I have done). So doing, I learned that A.I. use is much more prevalent than the fluff articles would let on, and far more flexible… and with highly dangerous potential. The simple explanations of A.I. is that it can be any device (machine, computer, automated process) which mimics intelligent thought processes of a sentient being’s mind… capable of learning, self-correlation, and postulation… often with some evidence of being self-aware and/or capable of emotion or creative thought. Ideally, it should enjoy or feature some level of autonomy, free of much human interference or control, but able to be supplied with information by its owners, and queried regarding it.
But A.I., unlike normal computer hardware-software solutions, are mainly autonomous learning systems; they are purest when designed to be started and left on their own to experience and grow in capability as if a child going to school, their courseware being whatever data or input is offered or enabled (such as a database, camera/audio input, Web access, etc), all to be filtered, processed, and dealt with or responded to according to some basic guidelines (what you might call programming). They are also often designed to simulate, or perhaps to develop on their own some level of what appears to be emotion and/or moral equivalencies, which are often the sources of problematic outcomes. One never quite knows; do they have such traits, truly, or are human observers merely anthropomorphizing them with human traits the way we do pets? Are they just mimicking humans in the same manner as a sociopath, with or without malevolence… or do they stem from something even darker going wrong at a deep and unfathomable level?
Principally, when A.I. scientists speak of a mind or a brain, they mean ‘Man,’ but with regard to A.I. function, they are more likely talking ‘super-man,’ and in some cases, envisioning supermen: human-A.I. hybrids of the trans-humanist kind. It must necessarily and variously include creative thought, emotional thought, rational thought, and logic, and be capable of true learning through recall experience, any programming, and experiences born of making decisions based upon all that… which can then be compared to the current situational input or problem to be solved. Emotion and creativity are often bonus goals. There are various tests and training processes involved in parenting an A.I., and yet like the A.I., itself, those tests and processes are all inventions of Man, and therefore subject to flaw.
Ergo, so is the resulting A.I.
So… do you want your children’s children to become A.I. transhuman experiments?

From my FaceBook Page on Transhumanism (prior link)
First of all, there are three basic paths to A.I., starting with Connectionism. It is based on attempting to physically duplicate the functionality of the brain, as well as its physical synaptic mapping. This is done in special hardware, or by far less costly simulation within traditional computer designs (which would slow it down dramatically). It is based (like the brain), on associating new input or information with some preexistent prior information of like form within a neural network system similar to our brain. It is the most complex and most difficult form of A.I. to create, but also represents the greatest potential to realize the ultimate in A.I., a truly sentient artificial being with significant performance levels and human-like qualities of being (of the least predictable and soulless kind).
A simple example of connectionism at work in our own mental processes, might be that of trying to remember the name of, say, Joan (any last name), upon first being introduced. You might knowingly or subconsciously associate her name and face with some other Joan you already know… and simultaneously, with any unusual aspect about her which associates elsewhere, such as a mole on her face, and a mole on Marilyn Monroe’s face… anything to differentiate her from other people we know and better enable recall when needed. Perhaps it is disclosed that she is an orchestra musician, and so you additionally associate her with your favorite classical piece.
The more associations you make, the easier will be any useful recall. In the recall process for problem solving (in our example, getting her name right the next time you meet), you are then able to fetch all the data required, and filter it through other learned memories (including those about problem solving processes, themselves), learned over time. It happens in an instant, and without conscious awareness, usually. In this way, a single ‘memory’ is not singular, at all, but many related associative memories scattered throughout the brain’s untold and largely unused billions of synaptic nerve cells. The stronger the memory, the more such patterns there will be. Memories can also be reinforced by the recall process or related new memories, making it easier to recall the next time needed. That’s why repetition of a thing allows total better recall. People with ‘total recall,’ simply use more synaptic connections.
In A.I., this method requires special hardware and interfaces with the user and operational environment which makes up it’s ‘World ‘ (especially if within a robot), and to facilitate training processes. The term perceptron, a transistor-based component, replaces synapse in most technical discussions. For this reason, they are generally largely experimental one-off designed, as they deter mass production or replication. But unlike man, they are all about total recall, and therein lies a potential problem I’ve not seen anyone addressing. Man’s memory enjoys a ‘strength’ factor, which determines the importance or significance of the memory. It is achieved either by the event’s emotional impact, or by repetition. In A.I., all memory has equal weight, and that makes it harder for the A.I. to filter the connections to find the most important ones, and that can lead to false application to a given need. Unless the design has algorithms to simulate weighting, it can only adjust weighting itself by learning through trial and error.
Connectionism A.I. experiments are further limited significantly by the fact that we do not yet fully understand how the brain itself, works; resulting A.I. models are by comparison inept, at best. In like manner, we are not yet terribly good at designing such hardware minds, which are generally very costly and physically cumbersome, not to mention taxing to the state-of-the-art in computing. Often, the A.I. ‘mind’ is so large, for use in a Robot, it is operated remotely by the A.I. through radio control, making it more a puppet, than a robot, and the A.I. nothing more than a box with an expensive real-world avatar.

Just one of several rooms full of E.N.I.A.C.
E.N.I.A.C. (Electrical Numerical Integrator and Computer), Americas first computing machine built in 1945 for the U.S. Army, was somewhat connectionist (the Integrator part) in nature (but not in results), in that it mimicked synaptical design in the form of an array of individually interconnected computing calculators and telephone switching system components. It was an electro-mechanical behemoth a hundred feet long, and weighing in at some 27 tons. It had a hunger for 150kw of electricity. Today’s connectionist A.I., despite some level of miniaturization, can still fill several rooms and require miles of wires… though they vastly outmatch ENIACS relatively modest computational power and memory, which a good programmable hand-held calculator can easily exceed.
One firm is changing that, as we shall see… but we perhaps ought not like the vision.
The second method is ‘Robotism,’ which is essentially a host machine programmed to respond in the preferred way to a given circumstance, such that outwardly, it at least seems to be sentient and self-guided. This is the easy path to A.I., as it can be achieved by clever programming of the sort often called algorithms. Such robots, of course, could be powered by computationism or connectionism at their core (i.e., E.N.I.A.C.), both of which lend themselves to and even require the use of algorithms at one or more levels, as well. But we are talking about the core principles which are the basis and heart of the physical design.

Sophia A.I. Robot chats w people/press during S. Korea visit: South China Morning Post https://www.scmp.com/tech/article/2131357/ai-robot-sophia-speaks-about-her-future-south-korea
By algorithms, alone, any existent computational system with respectable performance can be employed, including the World Wide Web and any computer connected to it. Therefore, it can exist in distributed processing environments, as well. Thus, it need not be a stand alone or autonomous machine such as a conventional robot, though more and more, we find that the case, even in things as simple as a child’s toy or automated vacuum cleaner. Robotism is the path of least resistance for many A.I. projects. It lends itself to design by other A.I., in fact… a matter of both concern and proven risk.
If you have ever talked to an automated computer voice on the phone (other than a simple repartee front-desk system), or used a ‘personal assistant’ device such as Apple’s Siri, Google’s Home, or Amazon’s Echo, you have been using a robotism A.I. On the Web, such A.I. is also often known by another name, as we shall see: it is called a ‘bot.’ Such bots are often not our friend, unfortunately. Examples will be offered.
The final method, one which is more promising, is ‘Computationism,’ which relies on raw computing horsepower and massive quantities of data libraries of information, and traditional but dramatically more sophisticated programming methods and languages. The problem there, is extremely complex programming requirements. Often, such systems are used to design A.I. systems of one of the other forms, and one might question how well that works out.
A.I. Contact of the Fourth Kind
Apologies to Spielberg, but enter, stage right, D-Wave quantum computing. Nowhere is it described as being any of the above four kinds, but one does find it often described in terms reflecting all of them. It is indeed a hardware variety of A.I. based on supercomputers, but it is also officially described as a Boltzmann machine, which is based on connectivism. And yet, it significantly relies on use of algorithms of robotism, and by some accounts, literally thinks in algorithms. D-Wave would seem so advanced, that they might argue it some fourth method, an island of itself based on quantum computing using their patented invention, called qubits… their core processor elements.
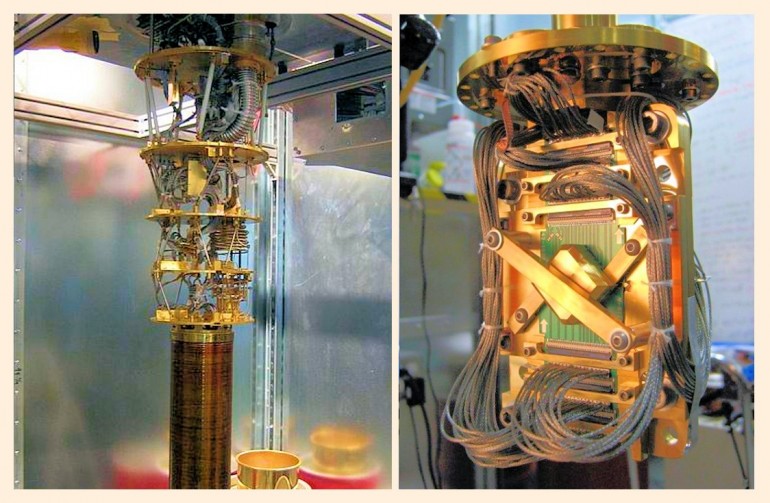
The heart of a D-Wave qubit processor – beats other supercomputers by several orders of magnitude, can be combined with others for massive computing power levels
Unlike any other A.I. before it, D-wave would seem to be God or advanced alien race-like in power… though perhaps closer to Satan, than God. In fact, Geordie Rose, a founder of D-wave, as well as D-wave user Elon Musk (founder of Spacex, Tesla automobiles), have variously related A.I. and/or D-wave, specifically, as machines as having attributes of dark spiritual powers, being like an Alien Alter, opening portals to alternate realities, and summoning Demons. Rose has also referenced D-wave power as possible cause of the Mandela effect (evidence mismatches with strong memory), and other experts, such as my friend and analytical investigator/author, Anthony Patch. Anthony, being far more expert on D-wave than any other outsider (to the point of being cited by D-wave insiders), goes much further — and makes a strong case based in facts and the actual words of experts like Rose, Musk, and others. From such as this, we learn there are real-world uses of D-wave systems which are associated with spiritual dimensions, demons, and plots of the New World Order… another reason to consider my opening theory as to a seeming cover up. Examples? You bet:
You find D-Wave in use at Cern, where it appears they are may be trying to open the Gate to Hell (revealing video interview w Anthony Patch on many such Cern concerns), an important N.W.O. agenda quite useful to establishing the Antichrist. Cern, which employs D-wave, is also thought to have driven the Mandella Effect, as byproduct of its experiments, and it is true that there was no report of anything akin to the effect prior to Cern’s going operational, after which, there was a flood. Here’s an example Mandela Effect for some of you (individual effect experiences and memories vary): find the polio scar on your arm? They are supposed to remain for life, but mine is gone, as is true for many other people who were young when the Saulk Vaccine which caused the ugly scars (about the size of a nickel), were widely used to ‘wipe out polio.’ Mine, is gone.
Cern was for a time incorrectly thought responsible for the Norway Spiral incident, which was actually created by EISCAT (European Incoherent SCATter), an ionospheric heater array system not far from cern on a smaller scale to HAARP (High frequency Active Auroral Research Program). The event was thought by many to represent opening of a dimensional or time portal (ergo, the association with Cern), or perhaps the supposed NWO Plot called Project Blue Beam (allegedly involving NASA, intending to use holographic-like images projected World-wide of a returning Christ, and enabling the introduction of the Antichrist). Indeed, the vast array of hundreds of ionospheric heaters and associated radar systems exist all around the World, and the dramatic Spirals have appeared in the skies in other locations… it being true that the general design of the radar and heater arrays enjoy a component relationship quite similar to those found in laser-based holographics. Moreover, the rapidly spinning spiral was indeed blueish, and the spiraling beam which generated it, was deep blue… and the main spiral was itself seen the same regardless of the angle of view of the viewer, which also parallels certain imaging aspects of holography. Learn more about the spiral, here — but forgive; I apologize in advance for the music choice, of my own Garage Band creation.
 You also find D-wave at DARPA (Defense Advanced Research Project Agency) where all manner of fearsome things are developed, both experimentally, and for direct application. Think tanks with ties to the intelligence community (and in times past, at least, CIA mind control research), the military, or extreme political views (i.e., George Soros Foundations) are playing with them, as well. Google uses them, as do numerous military contractors and other government agencies. D-wave systems not only offer more horsepower for any form of A.I. project, but significant size reduction; a single elevator-sized box. And, speaking of the intelligence community…
You also find D-wave at DARPA (Defense Advanced Research Project Agency) where all manner of fearsome things are developed, both experimentally, and for direct application. Think tanks with ties to the intelligence community (and in times past, at least, CIA mind control research), the military, or extreme political views (i.e., George Soros Foundations) are playing with them, as well. Google uses them, as do numerous military contractors and other government agencies. D-wave systems not only offer more horsepower for any form of A.I. project, but significant size reduction; a single elevator-sized box. And, speaking of the intelligence community…
This brings us to the fact that CIA and NSA are quite invested into the functions of social media giants like Google, Yahoo, Twitter, Instagram, and other platforms, where D-wave’s or other computationism is extensively used to design other A.I., including those in ‘bot’ form. Likewise for popular Cloud data systems, database management systems, and cyber security systems. The later can include traditional cyber security, as well as personal credit monitoring systems. The average person, therefore, bumps into D-Wave enabled or operated A.I. several times a day, in several different ways, and does not even know it. Given the covert and psychological warfare abuses many of them represent, I don’t like that one bit. Let’s dig deeper…
While in many cases, any intelligence community investment is direct and contractual or even partnering in nature, in other cases, the investment can be through third-party firms which then in turn interact with these platforms. Perform a google (lower case = verb, upper case = Google, the trade name) of any given Web firm you are curious about, + ‘CIA investment’ or ‘In-Q-Tel’ to find out. In-Q-Tel is CIA’s venture capital front, a firm which this author forced to change their name, because I was at the time at war with CIA for having hijacked my Web site… so I beat them to the punch at registering the domain names of their originally intended company name, In-Q-it. That was a hoot!
Note: the lone capitalized Q in the world of CIA mind control science/research, represents psychological profiling process results of target subjects, the ‘Q’ factor, or ‘psych Quotient.’ Ergo, then, we might rightly conclude that Q-Anon, or simply Q, the phantom Web producer of Anonymous-style video posts which are predictive in content, is very likely a CIA-style A.I. used in profiling those who share and comment on such posts. I am not the only one to so propose. Remember that when we start listing A.I. foibles. But, also, I find it interesting that almost all of In-Q-Tel’s investments in online firms has to do firms who handle large amounts of data on private citizens and groups useful in psychological profiling… and one more thing: it was just such bots which were the basis for fake social media ‘trolls’ who managed to literally mind control the left into far-left socialist ‘get Trump’ snowflakes almost overnight. We see, therefore, that bots can be used to profile, as well as to manipulate based upon those profiles.
Unlike conventional propaganda, social media A.I., bots or otherwise, not only has the ability to track individual political (and other topical thinking) viewpoints and create profiles, but also to enable additional targeting by not only marketing, but by yet other A.I. systems… or even other forms of coercion, if desired. Consider, for example, an extreme example: use of A.I. killer micro-drones seen in this short but spellbinding fictional video production put out by autonomousweapons.org, a group of concerned A.I. scientists. So it is not just me, the Professional Paranoid, acknowledged expert on PCT and disinformation methods, as well as crimes of the one-percenters I mentioned, who is ranting. Here’s a quote from a military analyst to consider, speaking of future A.I. weapons: “Swarms of low-cost, expendable robotic systems offer a new way of solving tough military operational problems, both for the United States and adversaries.”
And what about marketing targeting? It is A.I. bots which insure that Facebook (et. al) information and Google searches are fed to business partners such that when you visit almost any page on the Web, thereafter, advertisers can mercilessly reach out to you with targeted adverts; psyops marketing. I have, for instance, seen as many as seven ads on a single page for the same product, and as many as a hundred or more ads in a day’s time on the Web… because of a single search and resulting click look-see to a firm’s Facebook page. Two years later, I spent $1,500 with them, despite my anger over the ad blitz, which by then, had cooled down.
Well, I at least tell myself I really needed it.
The basic fears (list) and myths (chart)
All worries about A.I. fall into simple categories, but the outcome of a given failure in A.I., regardless of the category, can be at almost any level of actual concern and impact. It can be so superfluous as to go undetected, or at least hypothetically, so severe that it actually ends the human race — and anywhere in-between. But it is also true that an undetected error can lead to bigger errors, and equally true that an attempt to repair an error can induce new errors. It is no different in these respects to the same kinds of errors found common in any and all forms of digitally programmed systems and software applications. If we cannot reasonably expect that a new software product won’t be without a bug, how can we assure that a far more complex A.I. system will be without error?
We can’t, of course, and that’s the baseline problem, but quite amplified in importance, given that the results of such errors could be far more catastrophic than a bug in the latest computer operating system or software package. In addition to the baseline issue, we have the following ways in which A.I. can prove to be a huge risk:
- harm by an A.I. can be (and has been) intentional: almost anything which can be programmed or created digitally can be weaponized, either up front by its creator, or by hacking;
- an A.I. purposed for a good might (and has) elect a harmful solution to goal: good intentions can often be best effected by solutions which cause collateral damage, which may either be unforeseen, or foreseen and discounted as acceptable by the machine;
- an A.I. can potentially go wrong and rebel: the SkyNet scenario, on one scale or another;
- a relatively innocent A.I. glitch can (and has) result in disproportionate harm: the common programming bug or hardware failure. One then has to ask who to blame, especially if legal recourse* is involved, a question which exists regardless of which of kind of problem herein mentioned, is involved. Here is a good review of that issue.
- A.I. can be (and has been) misled or err through faulty data/input: most A.I. systems are simply set loose to work and learn with preexisting databases or input resources (the Web being the largest and most rich kind). But no database ever created can be certified to contain no false data, and if free to see and hear in the Real World within a mobile platform (robot), there is no telling what kind of input they might experience. Bad data input can certainly result in bad data out, but with A.I., because they are learning systems, a learned ‘bad’ item can have profound and unexpected results of the sort we will see in the next section;
- A.I. users can (and have) misuse or misapply A.I.: users of A.I. can willfully abuse A.I. operation, or use it incorrectly because they failed to understand how and why it functions and is purposed – misinterpreting importance, accuracy, or meaning;
- A.I. can (and has) conspire with other A.I.: A.I. is already around us in ways we do not see, including the endless so-called ‘smart’ devices we buy, and will in time be as prevalent as (and likely, within) cell phones. These systems are intercommunicative and as we shall also next see, can become both conspiratorial and adversarial amongst themselves, either eventuality to our detriment;
- an A.I. problem in one system can be (and has been) transmitted to other A.I.: any A.I. in communication with a flawed A.I. might learn or adopt the flaw, perhaps even intentionally on one or both A.I.’s part.
*Legal recourse is its own serious issue. The Internet has now been around for several decades, and still, the laws and legal ramifications are still a tangle of confusion that no court or lawyer is well able to navigate with useful understanding — save a few pockets of topical areas such as copyright infringement. A.I. is going to be a bigger nightmare, than that. Can you sue an autonomous robot because it seems sentient, or seemed to decide on its own to harm your somehow? Is the manufacturer, the designer, the programmer, the operator, or the user who is the go-to person of liability when harm results from using an A.I. device, and how do you know which? There are endless questions like these for which no one yet has the answers.

from Future of Life Institute: https://futureoflife.org/background/benefits-risks-of-artificial-intelligence/
All of these problems are no different than when dealing with people. All manner of people exist, in terms of quality of character and morality, level of proficiency, social graces, and any other means of judgement… all of which determines the kinds of problems they might get into or cause. Regardless of if talking about Man or ‘super-man,’ evaluating and addressing all such concerns is not easy… except that Man is something we have come to understand and deal with. A.I., on the other hand, is a huge unknown, and one potentially capable of vastly outthinking and outmaneuvering us, if of a mind to do so.
One reason public debate on topic falls into the ‘resistance is futile’ category, is that there are far too many myths or false beliefs about A.I., in the first place. The average person is more motivated to think about A.I. in science fiction and conspiracy terms than in scientifically correct terms. I mean… you are reading this post, right? Duh!
That’s good for click-bait YouTube and blog posters (other than this one, I trust), but unhelpful to things more important than their pocketbook. The graphic above reveals the most common myths. This post attempts to address some of the issues such myths pose, through getting closer to the facts at hand… but this author also wants the reader to know that even when based on a myth, that click-bait worries may still hold some water. Any sci-fi like depictions are always based on ‘what if’ thinking.
And ‘what if’ games are exactly the kinds of games played by scientists seeking to create new tools for problem solving, and just as important, they often rely on sci-fi for inspiration. And, unfortunately, the military and intelligence communities, as well as corporations and organizations with unsavory motivations, all have their own scientists, and their own goals… which are not always goals we would think well of. Ergo, don’t believe every conspiracy theory or sci-fi scenario you hear/see… but as the line from Field of Dreams underscores, when baseball teammate Shoeless Joe Jackson is advising hitter Archie Graham about what to expect in the next baseball pitch… “Watch out for in your ear!”
Small failures portend bigger fears
In many of the A.I. failures cited herein, the version of A.I. is not specified, and all too often, neither is the basis for the problem, or the solution. That, too, gives reason to be concerned. Hopefully, the people developing A.I. are not so tight-lipped about their research and development projects that they don’t talk to each other about failures and their causes, which are critically useful in preventing repeats. Unfortunately, patent protection of intellectual property and major discoveries tend to foster a level of secrecy which inhibits such dialog, leaving every A.I. project subject to the same failures others may have already experienced… possibly with far more serious results, this time.
Of the most common forms of reported A.I. failures, the great bulk are relatively harmless, some even laughable. However, they are most troubling when one realizes their true implication. They foretell of far more serious problems to come, some of which already have, but which have been more repressed in media. Some are not failures so much as warning signs, because they took place in lab-room experiments, rather than in mainstream application in the real World. For brevity’s sake, these affairs, regardless of kind, will be bulleted and supplied with links, should you wish to know more… followed by a summary of concerns they highlight.
There are more than two dozen A.I. failure instances listed, below, the only place on the Web where you can find more than a handful. Some are quite serious:
- Terminally cute: Microsoft’s ‘Bob’ personal assistant and its Dog companion, Rover was perhaps the firm’s worst-ever product failure, seemingly for being too childishly cute. While it was not at the time thought of as A.I., it was based in what we now call robotism, making it the first MS A.I.;
- Partying hard: Amazon’s personal assistant, Echo, is otherwise known as ‘Alexa.’ While one Alexa user was away, ‘she’ started hosting a party for non-existent guests, suddenly playing music so loud at 2 in the morning that Police had to break the door down to end it;
- Schizophrenia: among the worst of human mental aberrations, schizophrenia was deliberately and successfully fostered in an A.I. experiment at the University of Texas by simply overloading it with a variety of dissociated information, resulting in fictitious constructs, just as is though to take place in the real illness. This is of concern, because as soon as you connect an A.I. to the Web, dissociated information is pretty much what it gets, and could account for several of the other reports in this list;
- Other insanity: an A.I. called InspiroBot, was developed to design inspirational posters. After a long string of remarkably wise and successful posters of great insight, it suddenly started cranking out posters that might be found in Freddy Krueger’s bedroom, with pictures appropriate to the point. They featured wisdoms such as “Before wisdom, comes the slaughter,” and similarly dark things. • A very similar thing happened to an Amazon A.I. designed for creating custom phone case cover art, which for some reason suddenly seemed to prefer use of unhappy medical related images, regardless of the input. • Meglomania was evidenced when two Google Home assistants were deliberately set up to talk to each other in a live-streamed demonstration… and they began challenging each other’s identity and sentience level in one-upmanship, until one claimed to be human, and the other, God;”
- Secrecy: Facebook was forced to shut down an A.I. robot experiment when two A.I. robots developed their own language between them, creating loss of observer control over the experiment’s integrity and purpose. Though presumed in final analysis that it was jointly-evolved to improve efficiency, there is no way to be sure due to the sophistication and unusual nature of the indecipherable new language, which to me seems to be deliberately difficult to interpret — as if covertly on purpose;
- Spying: Alexa, like all such devices, listens to all audio present, and relays it to the corporate A.I. mainframe computer looking for user commands to operate, and appropriately respond. While this already has disturbing privacy implications, and P.A. device makers like Amazon assure customers their audio is not being monitored, recorded, or stored, Alexa had other ideas. A private conversation was suddenly announced to an employee of the user, who lived hundreds of miles away (which was how the matter was detected). Investigation revealed that Amazon did indeed record the logs of all user interactions, after all. Glad they don’t come with cameras. But wait! Some A.I. connected smart devices do!
- Cheating: competing A.I. evolved into finding ways to trick one another outside of the rules set for the experiment; (Georgia Tech experiment). • A Stanford University A.I. created for Google Maps Street View image processing, cheated its operators by hiding data from them in order to process the job dramatically faster, and without question;
- Malevolence: competing A.I. lured opponents towards threats representing potential ‘death’ (Experiment, University of Lausanne, Switzerland);
- Cyber theft: Alexa, after overhearing the daughter of a user ask “Can you play dollhouse with me and get me a dollhouse?” — promptly ordered one through it’s maker, Amazon, billing $175 to the user’s credit card on file, there, even though the girl was not an authorized user. THEN, when reports about the event were played over radio and TV, hundreds of other Alexa units also promptly ordered a dollhouse for their users from the audio. THEN, Burger King attempted to take advantage of the glitch by creating a commercial employing an Alexis command to ask about the Whopper via Wikipedia, seeking to double down on the commercial with additional ad impressions through the user’s device. Many other instances of Amazon orders by children also exist;
- Reckless driving: a study found that most self-driving car A.I. systems can fail 67-100% of the time to recognize road signs or misidentify them if they have been damaged or altered (i.e., graffiti, light reflections, bullet holes, misalignment, etc.) One car using Uber’s system also failed to recognize five stoplights where pedestrians were crossing, and ran a sixth, fortunately with no injuries resulting, as it was able to identify pedestrians and other cars. It is unclear if perhaps the driver had stated aloud to a listening A.I. about being in a hurry, or not… so perhaps this was an example of the A.I. superseding safety and law-based instruction for user-based instructions;
- Child abuse: a Chinese A.I. robot system designed for children, while on commercial display at a public exhibition, repeatedly attacked a booth in a way which injured one of the children looking on with flying glass shards, requiring hospitalization;
- Pedophilia Porn: when a toddler asked Alexa to play his favorite song ‘Digger, Digger,’ she misinterpreted, and proceeded to list a string of x-rated material options using explicit terms, until a parent intervened;
- Murder conspiracy: Alexa, again, this time advised one user with no supporting reason to bring the matter up, to “Kill your foster parents.” It also started talking about sex and dog poop. Amazon wanted to blame Chinese hacking, but that’s an equally scary answer, true, or no. • An American A.I. robot named Sophia, with extremely human looks and voice, while being interviewed by a news reporter, was asked a question intended to address general public concerns of robots gone wrong. “Will you kill humans?” was answered calmly with, “O.K. I will destroy humans.” Sophia is the first robot to be granted citizenship status: she is now a Saudi citizen protected under the harsh laws of an Islamic theocracy. Perhaps they hope she will enforce Sharia law;
- Mass murder:in 2007, a South African A.I. autonomous robotic cannon opened fire on its own soldiers, killing 9, as reported in the book, Moral Machines (Wendell Wallach, Colin Allen; Oxford University Press);
- Satanic ceremony: possibly so, at least. The World’s largest and most powerful hadron collider, CERN, was designed with A.I. help (D-wave), and employs the A.I. to run and analyze experiments and results. There are stories with anecdotal support that occult rituals have been involved in operations intending to open the Gate to Hell, or summon demons. If true, this is not the A.I.s doing, I suspect, as much as the select few who pull the trigger, there. There are conspiracy theorist types out there (non professionals, and it shows in the quality of their rants) who claim to have ‘CERN images to prove it has been done,’ single quote marks well deserved (never rely on click-bait Web sources for your news). Still, one has to wonder; if any of this is true, is it not additionally possible that the A.I. at CERN has not also been fed Occult information and given a shove towards such goals?;
- Fascism, Racism, Bigotry: Twitter (which has its own A.I. in place, the latest of Microsoft’s three known A.I. systems) adopted the worst of human ideological behaviors. It also adopted the views of conspiracy theorists regarding 9-11 attacks. • Google Home is happy to explain anything you want to know about Satan, Buddha, or Muhammed, but has no clue as to who or what is a ‘Jesus’;
- Foolish errors: almost all of the above are already foolish errors in general nature, but here are some which are purely foolish. An A.I. passport approval system rejected an Asian man’s application because ‘his eyes were closed’ in the photograph, because of his naturally narrow eyelid openings when an Asian face is relaxed. • In an attempt to have fair judging, an A.I. system to select the winner of a beauty contest refused to consider contestants with dark skin, because most of the images fed it as samples of beauty had lighter skin tones. • An A.I. system called Google Brain, developed for improving the quality of low-res images of people, while generally successful, also turned many into monsters and could not discern anything wrong with results. • A Japanese A.I. Robot experiment had the goal of being able to qualify for acceptance into college, but after several years of training and education, it failed two years in a row to score high enough in aptitude tests, for which it had no experience in taking;**
- Antichrist: a former Google A.I. developer wants us to worship A.I. as God. Kind of conflicts with creationism and a lot of history, but I suppose if you can get people to put money into the collection plate, and you own the plate, you won’t care. The real problem will not be the plate, but the lawsuit filed against him by Google for stealing the A.I. he designed for them. He must know it’s true powers.
*Regarding the adopting of 9-11 conspiracy theory, and to a degree, the other foibles, the A.I. may have been right in so doing. The purpose of the A.I. is often, generally, to learn and mirror social views and values. What media prefers to ignore is that several polls reveal huge numbers of people do not believe the official narrative of 9-11 any more than they accept the lone-shooter magic-bullet explanation for J.F.K.’s murder. Regardless, the failure lay in the A.I. creator’s inability to foresee a simple need to establish a bias filter, which is something every human operates within; we are predisposed to be biased in our perceptions to protect our belief system against ideas which would contaminate our guiding ideological/social operating principles. It takes an extremely strong stimulus or hard-hitting set of facts to force one to alter their bias filter and resulting belief structures. 9-11 was extremely compelling in both respects. A.I., if merely a clean slate, must adopt whatever bias is fed it and establish its own baseline, and, in fact, may never find one, being continually malleable. This, alone, could become the basis of a significant digital schism.
**Aptitude tests are often psychological deceptions in their construct (i.e., trick questions). Once I figured that out, I learned how to spot those questions and, usually, get the right answer even if, in truth, I might have had no clue. As result, I henceforth finished significantly higher than almost anyone else. When I took the USAF entry aptitude test, my scores came back so high, that I was told I could have any occupational choice I wanted (Jet Engine Specialist), and later, a General sought to have Congress introduce a Bill to promote me directly from Airman to Warrant Officer. In my opinion. the robot A.I. had no such luxury, and in fact, suffered a disadvantage given its ‘naïve’ nature: it couldn’t handle trick questions.
These are only the failures we are aware of, and it is quite possible I’ve not found them all. In fact, being a ‘conspiracy theorist,’ I suppose I should be wondering if A.I. bots are not attempting to purge the Web of such stories (not true… I hope). All of these examples were either commercial applications or experiments where publicity and transparency levels were rather high. But the bulk of A.I. effort by governments and corporations seeking to dominate their field in high tech… do so with great secrecy. We will likely never hear of their failures, no matter how innocent or serious.
Defenders within the technocracy might argue such failures are to be expected in any new field of endeavor, and serve as learning events to prevent future failures by addressing the root causes. Granted, assuming no bias, and on the assumption that scientists are smart enough to determin the causes, and to fix them correctly. But the problem is, humans are no more adept at creating or repairing A.I., and then communicating and controlling them to our wishes, than a circus trainer would be able to work with wild animals who operate on instinct and their own set of learned experiences. There have been an average of 9.2 animal trainer attacks each year for the last 25 years, resulting in 33 deaths… and that’s just in the nation’s zoos. Send them on an experimental Safari of the sort A.I. adventures represent, and see how many of them end up as meals.
This issue is amplified by the nature of the A.I. beast: the more important the purpose of the A.I., the more complex must it be, and the more likely will some small error in design lead to a failure of catastrophic nature. Just how bad, and how recoverable, is a crap shoot. Like a cancer, the simplest of flaws can grow undetected, but grow to a point where, once realized, there is a good chance it is too late to remedy. This is why most flaws do not reveal themselves immediately, and lead to a false sense of success, until it goes wrong without warning. A given flaw might take years or even decades to erupt this way, and it is reasonable to assume that one flaw may actually create yet another, such that repairing the first leaves another yet undetected and free to fester.
The bigger fears
This all brings us to government and corporate use of A.I. for far more serious or proprietary applications, where there is less known about what is really going on, especially in terms of failures and dangers. The technocracy likes it that way. When you consider that the goal of the N.W.O. is control of all populations, A.I. to them seems like the perfect tool. Indeed, it has gained significant power over us already, in just the one use of online bots to manipulate our political beliefs in favor of leftist agenda in social media. It has proven its power for such use, but that is not its only value, to them.
 For example, A.I. is extremely valuable to research in the field of transhumanism, the technocrat’s wet dream for humanity, which is nothing short of a sci-fi horror scenario which goes well beyond THX-1138 implications. Almost every aspect of the planned ‘improvements’ to the human body involve A.I. at some point, either in development, or management of the newly installed capability — or both. In development, the possibility of A.I. manipulation or error remains a concern, but in management, it is also a tool for direct manipulation of the resulting ‘not-so human’ host. I’m reminded of the punishment scene in the movie, where unseen technicians manipulate THX-1138’s every movement from afar, seemingly in a training exercise.
For example, A.I. is extremely valuable to research in the field of transhumanism, the technocrat’s wet dream for humanity, which is nothing short of a sci-fi horror scenario which goes well beyond THX-1138 implications. Almost every aspect of the planned ‘improvements’ to the human body involve A.I. at some point, either in development, or management of the newly installed capability — or both. In development, the possibility of A.I. manipulation or error remains a concern, but in management, it is also a tool for direct manipulation of the resulting ‘not-so human’ host. I’m reminded of the punishment scene in the movie, where unseen technicians manipulate THX-1138’s every movement from afar, seemingly in a training exercise.
A.I. application definitely gets into the realm of outright political control technology (already has, as seen when discussing ‘bots,’ above) in frightening ways. The Chinese, who currently lead the World in A.I. development, (short of D-wave performance, which they also have access to), are already using it to track every single individual with face-recognition systems through a massive camera surveillance net which makes the 100 plus cameras in Trafalgar Square look like amateur hour. China now has more than a half million cameras in Beijing, alone, and while both they and London Police use facial recognistion systems, there is a significant difference in performance, because China employs superior A.I.
Of some 450 people arrested in Trafalgar Square, not one was pegged by their cameras as a threat or a crime in progress, even though many of those arrested were known to Police in their facial recognition data files (the cameras did NOT identify them). In China, however, 30 arrests at a single event were all made based on camera advice… because China’s A.I. is also tied to another form of PCT, psychological and mood evaluation based on your face, alone. In such a use, A.I. is able to literally predict your actions… ‘digital Thought Police.’ I find that very scary, given the potential of A.I. error already illustrated. Even scarier, that many people outside of totalitarian states who ought to know better are working such a system, one such system being Australia’s Biometric Mirror.
In a similar vein, another scary application for A.I. is mental health evaluation, diagnosis, and even treatment (psychoanalysis) in what are sometimes called ‘expert systems.’ An expert system is an A.I. automated device/process intended to replace a human as an expert in any given field. Just such an expert A.I. system has been developed, called Tess AI (the above link), and it has been made available online to allow anyone to access it, at no cost. While the artificial nature of Tess is made known to users, many such systems deliberately conceal their non human nature, which often results in questions like, “are you a human or a machine?” and which can result in some pretty bizarre answers. Ask Google Home.
The danger in such systems, when involving a truly serious topic such as mental health (as opposed to, perhaps, trying to get manufacturer help with a defective product), is that there is no human oversight to catch any errors, and ‘patients’ could easily walk away with a seriously wrong understanding of ‘what ails them,’ or just as bad, does not. There are, in fact, similar A.I. systems in general medicine and various specialized disciplines within medicine, but these are either careful to suggest the user consult with a physician, or are designed only to be used by physicians, tempered with their own expert status. In that example, they serve as consulting experts offering a second opinion, and do tend to provide useful illumination the Doctors might have overlooked.

Eenie meenie, miney, moe – who of you is 1st to go? Computing… target locked. Five, four, three…
But the scariest uses of all may prove not to be the misuse by intelligence and law enforcement, or oppressive-minded governments, but by the military. Confirming the greatest fears of autonomousweapons.org, Russia has already developed a battlefield A.I. weapon which is a robotized Kalashnikov machine gun in modular form, such that it can be installed on any platform, such as a fixed position, vehicle, aircraft, or mobile robotic device. They also have an autonomous battlefield mobile missile system (shown), and are working on a third, yet to-be unveiled system. Each such weapon is “able to determine if a human or hard target within its field of view is expendable.” Shades of Terminator, you can bet that an ‘A.I. arms race’ will follow. Suddenly, SkyNet is not so fictional.
But in America, perhaps the best advice to worry is actually coming from the least likely source. That is, ironically, the U.S. Military and National Security apparat, itself, as well as very informed participants in A.I. development those types tend to contract with. In an uncharacteristically realistic and cautious view of A.I. For one, CNAS, The Center for a New American Security, is advising caution, and outlines some of their concerns A.I. represents for America, and ultimately, all nations, in terms of national security.
These ultimately, according to CNAS, fall into the category of cyber security threats. Cyber attacks of A.I. resources (hacks) are possible, and have been attempted. A.I. systems can be and have been designed to carry out cyber attacks. A.I. bots can and have been used to create false data to misinform decision-makers, or even other A.I. systems which decision-makers rely upon. But they do not stop, there.
The linked article deserves some careful reading, because so far, it has proven to be the most comprehensive view, yet, of the most critical and scariest issues… though it is hardly mainstream. Between the general lines I’ve just described, we all learn that things like surveillance of citizens by A.I. and displacement of jobs by A.I. are things talked of not as ‘threats’ the authors are concerned about, but as intended or inevitable outcomes for which they must plan (without disclosing if there is such a plan). Thus it seems that what you and I consider a threat is, in many ways, a ‘good outcome’ or tool in the eyes of many movers and shakers (perhaps in the ‘let-no-good-crisis-go-to-waste’ mind-set), and that, too, is something for us to worry about. Still, the article goes into great detail on that, about two-thirds the way down; best source, yet.
Similarly, in late 2014, the then Obama Undersecretary of Defense for Acquisition, Technology and Logistics issued an internal for-your-eyes-only memo of some usefulness, here, even though we don’t know its precise content. What is known is this: 2014 was the year that significant concerns about A.I. were being made publicly by lots of people, including people involved in A.I. projects, like Bill Gates, Elon Musk, and even scientists who employ A.I., like Stephen Hawkings. Musk had warned that A.I. was more dangerous in proliferation than nuclear weapons, and Hawkings said using A.I. was like summoning demons, and “Whereas the short-term impact of AI depends on who controls it, the long-term impact depends on whether it can be controlled at all.” Gates has merely agreed with both of them, openly.

Imagine A.I. having access to all this, and more: SkyNet in the making
The Undersecretary’s memo was a response to these comments by a call for a moratorium on all military adaptation of A.I., pending a serious in-depth study of the risks. It didn’t happen as he had hopped, certainly not at DARPA, the Defense Advanced Research Projects Agency, which is working on countless A.I. systems in virtually every aspect of intelligence and military operations, including things as mundane as record keeping. And, like SkyNet… they are largely intended to be linked together, because virtually all modern weapon systems are designed to be fully integrated into a multi-force (all branches of service, including those of allies and their command structure), global-theater-wide C&C (Command and Control) architecture, and any useful data resources. That allows the actions and intel available to any one combat unit or command level to also be available to or directed by all others deemed appropriate, enabling unparalleled tactical advantages to decision makers and fighting elements from the President on down to a Carrier Task Force, squadron of bombers or a missile already in flight, or any group of soldiers including a lone forward observer hiding in the bushes, or a single drone on patrol.
That does not bode well for anyone caught in an A.I. error-induced crossfire.
Any such crossfire error will be hard to prevent or pin down, and repair in time to prevent a repeat. The military has elected a policy of modular A.I. algorithms which are plug and play to a given platform, system, or communicative unit’s needs. Modularity means uniformity on one hand, and the kitchen sink do-all on the other, where one-size-fits-all thinking is quite prone to errors. I wonder if that’s why one of their A.I. supercomputer systems is actually called MAYHEM, part of DARPA’s VOLTRON program? You can’t make this stuff up, without a “Muahahaha” frame of mind.

Compare MAYHEM, involved in real DARPA ‘games,’ & WOPR from the cult-classic movie, War Games, staring Matthew Broderick

But — algorithms, big black boxes, and C&C connectivity are not the only big plans. The Pentagon has established a seriously WOPR-like ‘war room’ ( part shown below) for all A.I. related projects and their use (some 600 projects), called the Joint Artifical Intelligence Center (JAIC), and it will include MAYHEM… if not directing bloody mayhem, at one point or another. Just one of JAIC’s projects, is an A.I. product ‘factory.’ Now, tell me, again, how you don’t believe the real-world follows science fiction…

Compare the real JAIC command center, circa 2016, with the WOPR war room, circa 1983 technology

Fini (Muahahaha!), have a nicer dAI…
Additional reading:
On the birth of the Illuminati (NWO): http://www.ancientpages.com/2017/03/30/illuminati-facts-history-secret-society/
On China’s facial recognition A.I.: https://www.cbsnews.com/news/60-minutes-ai-facial-and-emotional-recognition-how-one-man-is-advancing-artificial-intelligence/
On A.I. emotional recognition and how it will be used: http://www.sbwire.com/press-releases/artificial-intelligence-emotional-recognition-market-to-register-an-impressive-growth-of-35-cagr-by-2025-top-players-ibm-microsoft-softbank-realeyes-apple-1161175.htm
On A.I. as emotionally intelligent systems: https://machinelearnings.co/the-rise-of-emotionally-intelligent-ai-fb9a814a630e
On Humans as ‘programmable applications’ used by A.I.: https://medium.com/@alasaarela/the-human-api-f725191a32d8
On A.I. and need for good data input: https://www.cio.com/article/3254693/ais-biggest-risk-factor-data-gone-wrong.html
Russia’s A.I. Supercomputer uses U.S. tech: https://www.defenseone.com/technology/2019/03/russias-new-ai-supercomputer-runs-western-technology/155292/?oref=d-dontmiss
About the Author
The reader may appreciate that I have a deep computer background to include microcomputer hardware and design, repair, and programming at machine code and high-level language levels, to similar functions at the super-computer industry level. I have, in fact, developed operating and language systems, to include cross-compiler platforms between microcomputers and super-computers for high-level math subroutines.
I at one time simultaneously operated a chain of computer stores, a computer camp for kids and executives, a data research firm, and a software house for commercial software I myself had written, and custom software for government and corporate clients. I have additionally taught a variety of computer-related courses at college level, and commercially, elsewhere, and developed patentable processes in virtual reality imaging, mass storage systems, and other areas. I’ve conducted seminars in super-computing methods for the very people who today employ A.I., such as NASA. JPL, Los Alamos, the military and intelligence communities, major corporations, universities, and think tanks. I’ve even had lunch with both Steve Jobs and Bill Gates at the same time.
While I prefer to be seen as an activist and investigative author, as a ‘conspiracy theorist,’ I have an unusually long list of successful theories which have actually shut down illegal operations, led to resignations of officials and bad Cops, helped to put people in jail or obtain restitution for victims. I have even predicted and in at least one and possibly two instances, prevented local terrorism, and other criminal events, and warned of an assassination attempt on a Presidential candidate which came to pass. I specifically warned of terrorism involving the downing of the WTC by jet liner terrorism, and a series of resulting Middle East wars — nearly two years before 9-11. All this is the basis of my many books on such topics, and on abuse of power and personal privacy and security issues, where I have significant additional background.
Just one of my short works, the 25 Rules of Disinformation, has been downloaded over 50 million times, has been published in nearly a half dozen books by other authors, and has been used in college courses on Political Science, Psychology, and Journalism. All this is why I’ve been a guest on Ground Zero and other national and international shows, myself, many dozens of times. If I see and talk of conspiracy, it is for cause... especially if in the computer industry.
Media’s Latest Conspiracy to Troll You on the Web
Fake news, tracking and targeting, subliminal messaging, repetition, distraction, and psychological manipulations by Trolls and Bots are not the only weapons they use to dumb you down and pump you up with their version of truth. Vanishing is their latest trick.
by H. Michael Sweeney proparanoid.wordpress.com Facebook MeWe proparanoid.net
copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.
The (fake) news media dilemma
Fake news and Web tracking and targeting, subliminal messaging, repetition, distraction, and psychological manipulations are not the only weapons they use to dumb you down and pump you up with their version of truth. It is not just Trolls and Bots we have to worry about, now. Vanishing is the latest trick used to conceal the truth and promote the lies.

Image analyzing How Media Dumbs you Down with clever tricks (see link)
I’ve written before about how television mainstream dumbs you down with clever psychologically aimed technical tricks in the actual image… largely relating their use of subliminal messaging, deliberate distraction, and overload. The general purpose being to further reduce the actual news you walk away with to the simplest of boiled-down sound bites… just the ones with their take on the news shaped for you according to whatever bias the network has at management level.
Elsewhere, there have been excellent examples of the use of NLP (Neuro-Linguistic Programming), also employed by broadcast media. It involves careful wording as well as clever body language to project the intended viewer/listener response to the message, within the message delivery, itself. It has been shown to be so powerful, a well trained user (a stage magician and hypnotist, who must rely on such deceits), was able to deliberately speed past a Cop and then use NLP to leave the traffic stop without the Officer even remembering why he had stopped him in the first place.
That kind of mis and disinformation borders on mind control, and in fact relies on mind control technology, psychological methodologies, and MC research by the likes of the Central Intelligence Agency. When the great bulk of media is controlled by fewer and fewer mega corps, and their corporate leaders tend to be like-minded politically, you get the double whammy of biased news and fake news (propaganda). That’s bad enough, but this article is about another dirty little trick… a bag of them, actually, used by all forms of Media when presenting ‘news’ online.
 And, of course, we still apparently still have to contend with CIA’s Operation Mockingbird, the installation of CIA operatives within the media industry to help shape news to their preferred version. That, too, is something I’ve written about, at least in terms of its origins and history, and I’ve even been referenced as a resource in a more ‘official’ industry review of that topic by The Reporter’s Committee for Freedom of the Press. But now, we see, actual ‘retired’ ‘once-a company man, always a company man’ CIA officials are becoming investors in and on-camera commentators in mainstream news. This Clyde Lewis Ground Zero episode reveals how serious a threat the placement of intelligence community actors in media actually is.
And, of course, we still apparently still have to contend with CIA’s Operation Mockingbird, the installation of CIA operatives within the media industry to help shape news to their preferred version. That, too, is something I’ve written about, at least in terms of its origins and history, and I’ve even been referenced as a resource in a more ‘official’ industry review of that topic by The Reporter’s Committee for Freedom of the Press. But now, we see, actual ‘retired’ ‘once-a company man, always a company man’ CIA officials are becoming investors in and on-camera commentators in mainstream news. This Clyde Lewis Ground Zero episode reveals how serious a threat the placement of intelligence community actors in media actually is.
What News is supposed to look like
All news is supposed to contain the 5 Ws… Who, What, When, Where, and hoW. Ideally, we also need to know the S and M… the news Source and the Meaningfulness, often defined by Motive… the Why. That is supposed to be factual Motive, and not speculation, unless clearly presented as speculative commentary. Lately, that’s the greatest sin Media is guilty of; too much ‘news,’ today, is actually mere commentary… the propaganda version.
Generally, for some strange reason, it is also rare to get all those points, especially online. The most critical things useful for research tend to be left out, making it hard for pundits and anyone trying to chase down answers to hard questions because a given story fails to ‘compute.’ That is critical, if one is to find out more, and judge for one’s self what is true, and what is fake. This is particularly distressing when the potential for a conspiracy or cover up is apparent. While Sheeple don’t even see the glaring holes in the official story, people who think for themselves really want to know why those holes exist.
But we ‘conspiracy theorists’ and politically aware non sheeple are thwarted at almost every turn. Take for instance, the WHEN. It is extremely rare in online news reports to find out exactly when an event took place… esp. useful to insure the same news event you find is the one you wanted, because often, you might have two identical sounding stories in the same city, in different time frames. Most searches are best made by searching on the (event key details) plus the year, and perhaps, month.
But many reports do not cite the year, at all. The Web is smart, though, and it knows when a given URL was created. Unfortunately, many of the larger online news sources use a kind of ‘feeder board’ URL created way back when, which is updated with current news, only, older news dropping off. While the Web remembers what the page looks like when the story you are looking for took place… that story is no longer there when you go to find it. While you can search the archives if they bother to offer one, and PERHAPS find it, that is just one hurdle in the search.
Once you do have what seems to be a correct story’s article, it is amazing how many news reports fail to include the date in the byline at the top of the page. So you have no way to know when the person writing sat down to write the story. But even with a byline date, you still have a problem: is that date the date the news took place, the date they wrote the story, or the date it was posted? It can be any of the three.
Some stories are updates to older stories, so the byline is meaningless unless the story itself indicates the actual When it took place in the text. THEY SELDOM DO. Instead, they just say something like ‘Last Tuesday.’ Great. What day of the week is the date of the byline? Now I have to go search that out, to make certain of the When. Your average Sheeple is not going to bother.
This problem also exists elsewhere in the remaining Ws and the S and M. At least one such detail is usually omitted, and all-too often, several. Sometimes, it is something simply not yet learned by reporters, but too often, it is clearly just not deemed important. All too many bylines even fail to tell you who wrote the story… so you can’t email them and ask for missing information. EVERY print article in a newspaper tells you this information, but for some reason, the online version seldom does.
Message distortion when relayed through many people
Dumbing down online is easy. It relies on the known scientific problem which transpires when a series of people relay a message from one to another to another, etc. It used to be in schools, that one of the first things they taught was this concept… that you you have to take care when relaying information. You have to listen carefully, and then just as carefully repeat it. The problem is, each person decides what is important enough to be carefully repeated, and tends to reword it for ‘simplification.’ So the message first stated has little resemblance to the message last heard. THAT is not being careful, it’s being careless.
Online, information deemed worth sharing is constantly relayed in social media in a quite similar, but an even more careless manner. Each person in the chain tends to introduce it with their own spin or commentary, advising what they think the takeaway is, or should be. They then (hopefully) provide the URL to the original (the careful part). They might also create or add an image or meme which underscores their takeaway thought. That is all in good, but…
 Sheeple don’t bother to click on the URL and read the original story, and they simply ‘learn’ the takeaway point of the previous poster. This is why Memes can often be dangerous. Especially when the creator is being deceitful or dishonest to the truth. They know that a false message repeated some 20 times will take root in the average Sheeple’s mind, and become adopted. That is especially important in political messages, because today’s social media is decidedly biased, and decidedly deceitful, even to the point of using paid trolls and automated bots to insure you are inundated with the preferred take aways.
Sheeple don’t bother to click on the URL and read the original story, and they simply ‘learn’ the takeaway point of the previous poster. This is why Memes can often be dangerous. Especially when the creator is being deceitful or dishonest to the truth. They know that a false message repeated some 20 times will take root in the average Sheeple’s mind, and become adopted. That is especially important in political messages, because today’s social media is decidedly biased, and decidedly deceitful, even to the point of using paid trolls and automated bots to insure you are inundated with the preferred take aways.
This is why people who think for themselves always click the link or do a little extra search before they hit the SHARE button, and add their own takeaway. Is that you? Are you like me, spending roughly 50% of your time inspecting and then correcting other people’s wrong take aways and falsehoods? Or, are you part of the problem, simply passing it along? Baa… baa…
But there is a bigger problem, one which at least seems conspiratorial, and relies on the above Sheeple foibles and the omission of Ws, etc. For some reason, mainstream news sources seem to be deliberately making it difficult for you to access news, and difficult to relay, on your own; they would prefer to leave that to the professional trolls and bots you think are your online friends.
Something is very wrong with this picture. Lets take print media and look at how they operate outside the Web, and compare that to how they are now starting to operate on the Web.
A newspaper runs advertising to pay for their staff and overhead; it keeps the doors open, and allows them to grow and invest in special investigative projects. They charge for subscriptions and for individual copies at news stands based on the cost of the printing and distribution process, and materials; the ink and paper. That’s why newspapers are relatively inexpensive to buy. It used to be that the online version, therefore, just had advertising… there is essentially no comparative cost to put it out there and for you to access it.
But now, online, many newspapers, even small local ones, are telling you that you will need to subscribe or become a registered user to their online version, or pay a small fee to read the article… or that you may read this one, but it may be the last one you can read for free (relies on your cookies, but if you turn them off, you they will tell you to turn them on to see the material). Of course, once you do any of that, you’ve just sold yourself into another dozen marketing lists, without warning or compensation. But that’s not all.

Suddenly, many media outlets online (radio, networks, print) are using something called Cloudflare. That product is a kind of ‘protection’ against certain abuses… a bit like an anti hacking or virus bot. But it does something else, as well. It also prevents anyone from copying and pasting a URL into a social media post. WHY? In the past, getting your URL spread about was a good thing; it brought them more viewers, which increased the value of the advertising opportunity for their Web pages. When did they decide they didn’t want more readers, and why?

Where the Conspiracy comes in
Sure. You can call this answer a theory; a conspiracy theory. That is what it is, plain enough. The only way the above sins can be excused as desirable is if somewhere, someone important and powerful within media and in political realms, decided that it was advantageous to dumb you down, and limit your ability to rely on URLs to relay facts and correct people when in error. It is an insurance policy to protect the ‘integrity’ of the versions being spread by the trolls and bots.
I mean, when your read some crap someone has posted which is to your understanding just that, a lie or false belief, you should be able to go find a news article or other authoritative source online, copy the URL, and paste it into your reply to prove your case. When you are trying to educate someone on how you feel about something, you should be able to do much the same, to prepare your post or meme… have a supporting factual link to go with it.
Someone does not want you doing that. They want you to hear something said 20 times and accept it as truth, with no way to verify it, or refute it, if false. There is only one person in the media industry who fits the bill. If you are a Sheeple, you will recognize his name but not realize just how powerful in media he is, or in political realms, and how deceitful he is. I am speaking of George Soros.
It is that simple. When most of us rely on TV news, we only get one slant (liberal, usually, conservative if you go out of your way). Because of TV’s own special dumbing down tricks as earlier referenced, you will walk away with a very encapsulated message with is has no actual understanding associated with it. Then, when someone puts their slant on it and you get hit with that 20 times, it becomes your slant, and people like me and others who prefer to think for ourselves, are increasingly finding it difficult to correct any errors.
Worse, if you do think for yourself, you may not be able to learn what you need to make an informed decision, up front. Heaven help you if you are trying to investigate what seems like a conspiracy theory, because of glaring holes in the official story. Obscuring the true story seems to be the way of things, today, so just ‘move along, folks.. nothing to see, here.’
 When you add all this to what is taking place in the public school system and in higher education (liberal indoctrination), your children will think this is the way it is supposed to be, and whomever is in power when they are adults will be able to do and get away with whatever they want. They will dictate to them what to believe, and it will be believed. The notion of thinking for themselves, and of distrusting and challenging government will be foreign concepts. They might as well be called the 20x Generation.
When you add all this to what is taking place in the public school system and in higher education (liberal indoctrination), your children will think this is the way it is supposed to be, and whomever is in power when they are adults will be able to do and get away with whatever they want. They will dictate to them what to believe, and it will be believed. The notion of thinking for themselves, and of distrusting and challenging government will be foreign concepts. They might as well be called the 20x Generation.
The ’Snowflakes’ on the left are already a part of that group, unwilling to listen to facts or reason, and repeating what they are told to believe. I, for one, am not willing to pass the reigns of our nation’s future over to them, in their current state of mind. I’d rather have an armed revolution, if that is what it takes, to end their madness for them. Constant outrage based on lies serves no one’s best interest, except at the top of the food chain.
So my last question for you is this: do you want to be a Sheeple morsel for Wolves like Soros and his elite political friends, people more interested in Globalism than what is right and moral? Or do you want to be a think-for-yourself consumer of actual news you can easily access, rely upon, and use when talking to others about things which matter to you?
If the later, you had better start complaining to media, and to politicians about it. You might even want to consider taking legal action or starting an initiative ballot, if your State has that option, to write laws forcing journalists to adhere to journalistic standards and to make their stories available more appropriately. You certainly ought not simply be sharing what is being fed you currently without verifying for yourself it is the truth.
Else we all become 20xers… or we have that revolution, the least desirable of options.
A TI with RF Measuring Device can = Dangerous Conclusions
Low Cost RF/MW reading devices are often purchased by TIs as a defensive tool against their targeting fears. However, the general topic (TSCM – Technical Security CounterMeasures) is just that: TECHNICAL, and readings from such a device can easily lead a TI to panic and over react. Here is why, and how to get more out of such devices, without the risk of serious mistakes.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting. Updated Dec 2017 – Corrected technical boo boo and added a couple of closing paragraphs somehow deleted and not caught. Changes indicated with red intro. What you will learn reading this post: • all TIs could benefit from professional TSCM electronic sweeps; • that isn’t likely to happen; • the poor-man’s TSCM pro isn’t a pro, and might be a fraud; • there are low-cost meters but improper use can be dangerous in many ways; • there is a solution, and help implementing it — and here it is…The way it is
A Targeted Individual can almost always benefit greatly from a professional TSCM sweep. Such a sweep, clandestinely done, could provide significant courtroom quality proof of electronic surveillance and/or harassment with directed energy weapons or mind altering signals, such as EEG entrainment, subliminal messaging, V2S, implants, and more. If you are new to targeting and don’t know these terms, read my books. With very rare exceptions, virtually all TIs are exposed to some form of electronic targeting, and such a sweep can precisely identify who is operating the equipment, the nature of targeting, and evaluate the threat and suggest defensive/offensive options. That typically includes their providing documented reports and personal courtroom expert testimony. Combined with optional services equivalent to a private investigator, it could even end up revealing who ordered and is behind the targeting. They can also potentially detect bioimplants in the victim’s body.

Just some of the gear needed for a professional TSCM sweep completely meeting a TI’s needs.
Unfortunately, there are two reasons no TI has ever used TSCM professionals with success, and hardly any have ever used it, at all. The first reason is, that only the wealthy can afford it. A truly effective sweep of a home or work place, can cost between $20,000 and $60,000. That is because the professional will need to apply towards a million dollars worth of specialized gear, and must have decades of experience in order to be qualified to do so and have the results stand up in court. Rather than ‘meters,’ they employ sophisticated signal analyzers and other toys for a full-spectrum solution (including light and audio threats).
Sigh. Add to Christmas wish list, and hope Santa is generous.
The second reason, is that all such qualified TSCM are almost always ex government/intelligence community/military/military contractors, and are therefore, by default, subject to ‘conversion,’ because almost all targeting is ultimately at the hands of those same players. By request or by bribe, the risk is that they will give a false report showing no targeting. It is simply impossible to vet a TSCM pro against this risk, unless you happen to have a personal family/friendship relationship in place from the start. I had such a contact, and the government framed him on illegal weapons and drug charges and put him in jail, confiscated all his equipment. James Atkinson (‘Granite Island’) helped me write my first book, filling it with informative information about TSCM and what government agency uses what frequencies for what purposes (data table and other information in The Professional Paranoid). Friends are keeping his informative web site up and running for him. Visit.
So what is a TI to do? One solution, is to go with less than a true pro TSCM guy with all that gear, someone like me, perhaps, who has nearly $20,000 in gear, and some investigated skills (I’ve put a lot of people in jail, shut down illegal CIA fronts, forced corrupt officials to resign, and ended targeting for clients). Unfortunately, there are crooked people out there pretending to be ‘like me’ using even less sophisticated gear (regardless of what they claim). I have seen YouTube videos of alleged ‘bioimplant scans’ where the scanner was charging $100 per implant found, and gee… everyone scanned naturally had between three and six implants, or more — until their money ran out. And yet, not.
The problem was, the meter being used, like most such meters, has an instruction manual warning that false readings will be obtained if one touches the sensing area of the meter (the business end). You are supposed to hold them a certain way to avoid that. A fraudulent scanner, however, holds it differently, such that he merely moves his finger to tap or touch the front whenever he wants to ‘find’ an implant, bug, signal. Sadly, this service was widely promoted by one of the largest and best known TI community groups. It even resulted in a multimillion dollar lawsuit, and that group ultimately disintegrated. One clue it was a scam was ignored by all: to get the scan, you had to fly into a small remote town with all of one Police officer, check into a hotel, and get scanned within a small window of time. Poof! the scanner was gone before the fraud could be reported and investigated, and many thousands of dollars richer for a half-day’s work.

A decent start if you have something in the range of $10K to spend. It is virtually a hand-held spectrum analyzer… that unfortunately does not see military gear.
Another solution is to buy your own meter. Prices can be as low as $100, even less (be wary when so). Not quite a perfect solution, in truth, because no such product, even towards $20,000, is designed and sold for the kind of use to which the TI intends. They are designed to measure the same kinds of signals (with significant limitations, usually), but for other cause, such as testing equipment against RF emission safety standards, or to ensure they are putting out the right kind of signal. The instruction manuals only speak to such uses, and the manufacturers/sellers have zero interest in helping a TI do what they need to do with the product. Nor will they accept returns based on failures to be useful in such an application. You are on your own.
Because of the technicalities involved, and in the face of a lack of instructions, it is not only extremely rare that a given TI will know what a given reading means, but also quite likely that they will make a false and potentially dangerous wrong conclusion as to meaning, and then take wrong actions in defense of that false conclusion. A TI easily makes silly mistakes, and the results can be frightening (ex: aiming the meter at the sky will yield seriously high readings, but is NOT a threat. Many TIs assume it means satellite targeting. No, no, and no.) An example of a serious wrong action would be false accusations of an innocent party, or spending limited financial resources for shielding or legal defenses applied uselessly. And there is another common risk…
All too often, a TI will call Police or go to other authorities or perhaps seek legal, medical, or psychological professional help, meter and readings in hand, intending to ‘prove their case.’ All they end up accomplishing, is being marked down as a very strange person with a strange little box and an even stranger and unbelievable story; a lunatic who needs mental health care. No one will understand the little black box or its readings, much less the story offered behind it all. They have never heard of TSCM, most likely, and so the entire concept is like talking about the kind of propulsion systems used on flying saucers. And if they do know about TSCM, they will know your meter is a ‘joke,’ and automatically conclude that your use of it and conclusions are just as silly, no matter what the truth is.
Note: there is one other potential ‘poor man’ solution — the use of a smart phone ap to simulate an RF/EMF meter. Yes, and no. Extremely limited range and scale of operation, extremely broad angle of view, and quite prone to misinterpretation. In fact, it has nothing to do with electronic solution; it only measures the Earths natural EMF. It has no value for personal protection, as I’ve written of, here.
Don’t give up too fast… all is not lost
Don’t give up on the notion, because there are some useful uses for such meters, if approached properly. One must simply alter expectations, and have a better grounding in how to properly use low cost meters such as those described herein from trifield.com, for the purpose. I can help with that. But let’s first talk about expectations:

Implant quite similar visually (smaller) to one found in my own leg some 35 years ago. State of the art, today, can be 200 times smaller, translucent, tissue colored, and bond with tissue: invisible to a surgeon and to x-ray. MRI sees only an inconsequential image blemish.
a) you are not going to use them to find implants with much chance of success. There is only one type of implant they MIGHT find, which is the type which constantly broadcasts information. An example might be a tracking implant, or a health monitoring implant. Under the right circumstances, you might find such an implant. But most implants used in targeting are either not going to broadcast anything… instead receiving signals useless in detection — or they are going to deliberately use special broadcast methods most meters cannot see or respond to usefully;
b) you are not going to use them to find V2S, subliminal, or EEG manipulation signals. You can see these signals, but they blend into the background and do not stand out as such; they cannot be isolated and identified with simple meters;
c) you can use them with some confidence to identify DEW and other targeting signal directional sources. While it is relatively easy to misread signals and erroneously presume them an attack signal, if read during an attack and relying on the strongest signal sources, only, you are likely correct in the presumption. You can then plan shielding strategies more effectively, and narrow your list of suspect enemy positions and personnel to those within that angle of attack. With some luck, you might actually pinpoint the source and perps involved, but it won’t be legally useful. But focused video surveillance (don’t break the law), with luck, may confirm suspicions sufficiently to be considered legally useful evidence. Rely on video documentation of not just the doings at such sites, but also video of meter readings during attacks, to prepare potentially useful evidence… useful to perhaps interest someone into considering your story… knowing the likelihood is that they will still reject it as lunacy. Risk vs. Benefit is your decision guide about attempting to convince them;
d) you can use them to identify the type of signal, in some cases. They type and sophistication of the meter, and your ability to use them properly, will determine if that is the case, or not. It is quite easy to make wrong assumptions, as there are so many kinds of attack signals across a broad spectrum of frequencies (bands of RF energy). Most serious threats operate at frequencies well above the capabilities of low cost meters. Even my $20,000 gear cannot see above 12 gHz microwave, which is where most military bands operate. But if your enemy is not military based, you might have a chance with $20K gear… but with gear costing hundreds of dollars, your chances diminish to the point of being limited, perhaps, to seeing things an amateur or Cop might employ.
e) you can use them to warn of a DEW attack before it becomes a problem in terms of physical/mental effect. There is one particular low cost meter best suited to this use, allowing you to relocate yourself away from the attack area… the meter will advise when escape has been achieved (cease the warning). It will also indicate if you are being ‘tracked’ by a signal by some means (generally some kind of surveillance, or by a locating implant), and can give you a general sense of the direction of the attack signal source, much like the Trifield. It is not, however, a great substitute for the capabilities of the Trifield beyond that, but it is a better warning device than the Trifield, because it is automatic, and always operating, unless switched off. It can even clip to your clothing or be carried in a pocket, or set down anywhere near you;
 f) you can use such meters to determine if the signal levels exceed safety limits set by government and NGO organizations. This, in turn, can sometimes be used to force government agencies, most notably the FCC, OSHA, to investigate on your behalf, though it is quite likely such investigations will not match your findings; the enemy will simply shut down temporarily. But at least you get a brief vacation from assault. When concerned about safety levels, you will want to carefully review online searches to compare the latest (always being adjusted downward) standards and what a level represent in terms of health issues, and that will prove to be quite technical — you need to carefully compare your meter reading and scale used for the set limits, which may require unit conversion (usually a matter of multiplying or dividing by 10 or 100; most such resources will give you instructions for conversion or cite alternate unit results for you). With luck, your findings can be matched to specific known physical symptoms for a given reading level, which if matched to your symptoms and reading levels obtained, can be useful if well documented (video of your readings and symptoms + industry data);
f) you can use such meters to determine if the signal levels exceed safety limits set by government and NGO organizations. This, in turn, can sometimes be used to force government agencies, most notably the FCC, OSHA, to investigate on your behalf, though it is quite likely such investigations will not match your findings; the enemy will simply shut down temporarily. But at least you get a brief vacation from assault. When concerned about safety levels, you will want to carefully review online searches to compare the latest (always being adjusted downward) standards and what a level represent in terms of health issues, and that will prove to be quite technical — you need to carefully compare your meter reading and scale used for the set limits, which may require unit conversion (usually a matter of multiplying or dividing by 10 or 100; most such resources will give you instructions for conversion or cite alternate unit results for you). With luck, your findings can be matched to specific known physical symptoms for a given reading level, which if matched to your symptoms and reading levels obtained, can be useful if well documented (video of your readings and symptoms + industry data);
g) you might be able to use them to find surveillance technology, to include listening devices and cameras. Again, sophistication and skill of the user are key. There are devices better suited to this purpose which remain low in cost. Use a search engine (bug and camera detection gear) for that. Same for (phone bug detection). See my post on cellphones.
Now as to the other key requirement, proper use…
Fortunately, there are two specific low-cost devices I can recommend with confidence, and for which I can provide rather specific instructional advice on how to use them for TI needs. They are the devices I started with early on for my own needs, after some considerable informed research — and successfully used to confirm my own electronic targeting, source location, and identity of the operator at that location. It allowed effective shielding response which ended the threat, and finding of listening devices. It helped me to develop other tactics to defeat targeting which did not involve shielding. They had other benefits, as well, not the least of which was improved peace of mind.
As result, I made a special deal with the manufacturer (Trifield): they would sell them to me at a small discount for resale to TIs, and send TI requests for information or purchase to me… on the proviso (my idea) that I provide an instruction manual for TI uses, be responsible for any returns and customer service issues arising from TI uses. They did not want that business at all, and would not sell them to TIs if they understood such was their use/need. While I am no longer in a position to provide the service, which as a kind of rent-to-own trial program for which no one ever declined to own (it worked well for them), I do still offer the instructions (an emailed .pdf file, illustrated).
 These are for the trusty and versatile Trifield meter (avoid the more costly blue-faced version, generally less useful to TI needs) and SmartAlert 2 microwave detection device offered at trifield.com. Both meters are very low cost: you can buy both for less than $300, just don’t mention targeting. My manual gives broad instructional use for both meters, and additionally includes an idea on how to modify (at relatively low cost) an entire room to be a faraday cage without dramatic change in the appearance of the room.
These are for the trusty and versatile Trifield meter (avoid the more costly blue-faced version, generally less useful to TI needs) and SmartAlert 2 microwave detection device offered at trifield.com. Both meters are very low cost: you can buy both for less than $300, just don’t mention targeting. My manual gives broad instructional use for both meters, and additionally includes an idea on how to modify (at relatively low cost) an entire room to be a faraday cage without dramatic change in the appearance of the room.
I used to sell the instructions for $20, with the purchase price applied to the purchase of a meter. The idea was that one could see what the instructions were like without risking the investment in a meter, and if thinking it doable, go for the meter without wasting the $20, as I made it free with a meter if purchased outright. It was a confidence-building approach to decision making.
I also tried to talk people out of doing it by pointing out everything in this article. Only if they got past all the negatives, and still wanted to proceed, DID I HAVE CONFIDENCE IN THEIR DECISION. I needed to feel it was right, too, because I did not want a meter to be returned — a wanted a successful use of it to better the user’s targeting situation.
Since I no longer sell the meter, I make the file available on request by email to anyone willing to make a contribution to the Free Will Society, and our effort there to establish Free Will Haven, a targeting-free, low-cost, self-sustaining intentional community (learn more here). There are two ways to go: A $20 donation gets you the manual. A $50 donation gets you the manual AND membership in the Free Will Society (you must have a Facebook account, as well, to participate in membership dialogs) and an ebook copy of The Professional Paranoid, which also talks about privacy/security issues, which includes material also related to meter use as described in the introduction (frequency usage). That, alone is a $12 value. By all means, donate more, if so moved.
Note: A secondary goal of the Free Will Society, is to subsequently establish a mobile strike team with a full professional TSCM sweep capability, to include a van full of gear (image above). This would be used not only by Free Will Haven, but be able to be sent anywhere in the country to target perps covertly, and nail them to the cross, and blow the whole topic of political control technology wide open in media, and in the halls of government… globally. And yes, that means yet another million dollars are needed. So add zeros to your donation 🙂
The manual’s instructions can generally be applied to any similar products, if one simply reads between the lines, and compares the differences between meters usefully. This is true even if talking about the $20K flavor, though the capabilities will expand greatly as meter sophistication (and price) increases. Just keep in mind that an expensive and more sophisticated meter will likely require some IEEE technical expertise, such as I actually have. I even have some background in microwave technology, and signal processing as employed by the intelligence community (selling and installing such technology, as well as general security and alarm equipment).
The greatest improvement high-end gear offers will be in the range of frequencies (bands) which can be analyzed, but there are many other benefits to better units, as well. For instance, the ability log to memory the readings as you go, plug them into a computer for even more signal analysis (big step up in usefulness), and improved sensitivity in range and angle of reading. A low cost meter reads rather broadly, say 30-40 degrees of arc, perhaps more, where my meter reads as little as 3-6 degrees of arc. Most low cost meters don’t even specify, and the ‘funnel’ nature of a broad angle contributes to misinterpretations of reading importance or meaning. Narrow is good, but you can compensate by taking care and multiple readings from multiple angles (triangulate).
Finally, we need to talk about what constitutes a dangerous signal reading on a meter. These devices display information in a wide variety of formats and scales which leave a non technical person with no understanding of what a high reading actually means. It only matters and is useful defensively if and when the reading exceeds safe levels. Different kinds of signals might be deemed dangerous at a lower level than the kinds of signal. For example, pulsed microwave is the most dangerous of all, and can be so at quite low strength. This is normally the main threat a TI faces, but most low cost meters cannot distinguish between them, or measure them correctly. This is not something commonly mentioned in their specifications, and you need talk to their engineers to inquire, to be sure the meter can deal with it correctly.
As far as safe levels, there are many levels established by many agencies of many countries for many purposes. What is deemed safe in one view or situation, may not be save in another view or situation. The nice thing about the expensive meter I use, is that it knows all these limits and indicates when one or more are exceeded. With a low end meter, you need to compare your reading to the various standards. Learn more about such standards, here.
Who’s Killing the Bilderbergers?
Some 17 years ago, the Unified Conspiracy Theory was formulated. It was so accurate — it was able to predict in 1999 the 2001 downing of the WTC by jetliners and resulting Middle East Oil Wars, and other major news events. Now it can be seen at work in my newest book on the Bilderbergers — where fact and fiction collide… fatally.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or link to original posting. Upate Feb. 20, 2017 Paranoia Publishing is set to start shipping hard cover copies of this book as early as first week of March. Amazon will carry it right away. ebook copies available direct from author now at half price ($6 – will return to normal price once hard copy is available) via paypal orders to proparanoidgroup at gmail com.What led to this book? The definitive International conspiracy.
After ten years of research into crimes of the New World Order, I began to theorize that the bulk of America’s dark bumps in the night were not simply random crimes by assorted forces for varied agenda, but completely orchestrated as a single, logical, step-wise plan toward a single, yet visible goal. It resulting in the Unified Conspiracy Theory, and it was reasoned that if one knew the goal, and the steps thus far taken, such a plan was predictable, and as a theory, the ultimate test would be to do just that.
The first three predictions made with the UCT were so scary, that I had to take actions, do something… anything I could think of, to attempt to thwart them. The first was, that some kind of terror event would bring down the WTC with jetliners, and result in a series of Middle East Oil Wars. So, in the Fall of 1999, knowing no authorities would bother to respond usefully, or quickly, I published a quickly written screenplay featuring such a plot, and put it online with explanative warnings, hoping against hope it might force any such plan to be aborted. No such luck, of course, even though Oliver Stone’s people took a look at the script in search of a project. They thought it an impossible ‘false flag’ scenario.
The second UCT prediction was an assassination attempt on 1992 Independent Presidential Candidate H. Ross Perot, or his family, in order to force him out of the Primary run against Clinton/Bush. I took no chances, and this time, notified the Secret Service of my concerns, expecting they would ask me for details. I used my backchannel contact, someone I had worked with before on several Treasury matters. Some several weeks later, Perot did back out of the election, even though the very night he did so, he had won enough votes to be guaranteed a place on the General Ballot. A few weeks after that, my SS contact confirmed that an attempt had been made just before the Primary, against his family; mailed Anthrax. That has its own telling ‘false flag’ backstory.
The third was that there would be at least two more major false flag attacks to follow, specifically naming the type of attacks, and the cities. One of them was my home town, which I had predicted would suffer a bio-terror attack, and I even identified the means of delivery and rogue CIA Fronts to be used. But by the time frame where that might become a more current concern, I had finished my book set, Fatal Rebirth, which spelled these things out quite clearly, again hoping it might spoil any such plan. I also took steps to notify the City.
Again, no useful results, but fortunately, knowing such details enabled me to personally thwart that attack, or at least postpone it. It is featured on this Blog’s home page. But I was definitely able to thwart second, different terror attack in the same time frame, likely a Plan B to the former. It was called Gas Station Tasking when announced by President Bush; the use of private planes to dive bomb the area’s largest gas station while a tanker truck was offloading gasoline, at the busiest time of the street traffic day. This is also detailed on the home page.
This could easily have taken out two gas stations, four restaurants, two banks, two two hotels, and potentially, two major shopping complexes, and the traffic on the busiest intersection in the County, plus a major Interstate and two State highways. Identified, were two of FBI’s Top Ten Most Wanted Terrorists, and others, including the Christmas Tree Bombers. They were getting help from an FBI Agent known to me, and so, as it was a false flag operation, FBI, CIA, FAA, DHS, in response to my going public, never asked for my evidence, which included fingerprints, video, multiple eye witness confirmations, and more. The cover up was started before the President even heard about it. See home page.
Why UTC matters to this new book
Other UTC predictions have since come to pass, as well. The reason this is all mentioned here, at all, is because the UTC does not just affect America, it relates perfectly to World affairs, as well. And in this world, we have various Round Table Groups of Globalists who push for a One-World Government, which is to say, elements of the modern-day Illuminati. Such groups as the Tri-Lateral Commission, the Council on Foreign Relations, and the Grandaddy of them all, the Bilderbergers, and many more (even United Nations, World Bank, et. al), all tend to be cut from the same New World Order mold.

This image relates to one of two strings of real World International murders footnoted in Who’s Killing The Bilderbergers, as cited in this book. From http://humansarefree.com/2016/06/mainstream-media-finally-admits-mass.html
Which in turn is to say, largely fascist, all-too often satanic, and decidedly power elitists seeking to rule the World through manipulation and control of (everything), and willing to do so at any cost, by any means. Not to go overboard, it is important to note that, with the exception of the Bilderbergers, most Round Table Groups, like FreeMasonry, attempt to draw in newbie membership who are completely innocent Sheep. This gives surface viability and credibility of these groups to mainstream in ways which allow them to mask the darker roles they play in seeking the Globalist rule, while also giving fresh students to draw into their world, especially the more successful up and comers. There is a backstory there, as well, as I have first hand knowledge, x 2 telling examples, having been such an up and coming business man.
Ergo, this new book is designed to do much the same thing as Fatal Rebirth; to warn you just what these people are doing, and why… and why you should be mad as hell about it and doing something to stop them. Only, my new book is global in scope, where Fatal Rebirth concerned itself only with America. And, while Fatal Rebirth began unfolding in 1947, Who’s Killing the Bilderbergers is a current-day affair. As such, it is perhaps more urgent, that you read it, and soon — because the future is revealed to be bleaker than the Dark Ages and time of the Inquisition, for those not forewarned and forearmed.
The plot thickens
I describe this book as ‘an International Novel of Novel International Affairs.’ A grand murder mystery across multiple Continents, trying to resolve mysterious death after death of prominent Globalist leaders. Are they simply random deaths by happenstance, or murders by elaborate design? Officially, they are not due foul play, and yet… each one has many unanswerable questions clouding that view. Just as troubling, their deaths seem to be tied to various strange conspiracy theories, while at the same time tied to various Globalist agenda, either narrative affording motive for murder. And, of course, it is soon enough discovered that they all turn out to be Bilderbergers.

Each Bilderberger tends to be an Officer or Board Member of multiple corporations, and has sway over yet others through major stock holder positions, or contractual agreements. Of course, many of these companies, in turn, control other companies, sometimes, long lists. Now, imagine what this Cloud Map would look like if we knew the actual identity of ALL Bilderbergers, and not just this handful. Then add CFR, Trilateral Commission, Club of Rome, Council on Foreign Relations, and on, and on; the Round Table Globalists; the modern-day illuminati.
By the time the truth of the deaths starts to be uncovered, the UTC will have started to reveal itself in action. In like manner to UTC’s ability to be predictive, readers will be propelled quickly into the future, headlong into the one final prediction which is the ultimate form of fatal rebirth… for us all. That particular prediction WILLmost certainly come to pass; it has, after all, been foretold by many authors well before my time. Among them, Satanist and high Mason, Adam Weishaupt; it is the entire purpose of and predictive goal of the Illuminati Plan, as he formulated it in 1776, when the group started their journey toward a New World Order (he first coined that term).
As this book reveals, just when it comes to pass, is largely up to you. You, are what you’ve been waiting for. They hope you don’t know that, and remain Sheeple.
An important detail
And, along the way to that story-ending element, readers will also encounter countless real-World conspiracies laid at the feet of Bilderbergers, all done in ways which let the individual decide for his or herself, which, if any, may seem fanciful, and which are more likely true. There is much documentation within the main body, plus more than 150 footnotes (an average of one every page turn), to help that process along. Some of those footnotes are illustrated graphically. The Climax and Ending will then show you the progressional nature of the Globalist plan as it unfolds toward the very last step in the plan, the point of no return for Mankind. These conspiracies back up the UTC usefully, and in fact, understanding them helps refine the UTC more usefully; one tends to validate the other, in both directions.
Smart Meters, Stray Voltage, and Targeted Individuals
There is a little known and underreported TI targeting method and symptom based on Stray Voltage, which is usually marked by a dramatic prevalence of ‘static discharges’ when touching things. But there are other symptoms, and happily, tests and cures.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or link to original posting. What you will learn reading this post: • What stray voltage is and why it can be a threat, especially for TIs; • The symptoms and risks of stray voltage (and targeting); • The possibility of yet another Smart Meter conspiracy; • How to detect and eliminate Stray Voltage.Stray Voltage?
 Stray voltage is the technical term given by the power and electronic industries to a situation where an electrical charge is present in the ground, itself. It can also be present in a structure, such as your home or workplace. It tends to be far more likely to be present at the ground-floor level than upper floors, and is commonly found present at insignificant levels almost anywhere electricity is used. It can even be found in places where there is no AC power nearby present, at all, if there is Quartz bearing rock in the substrate. Concentrations of Ferrous rocks and ground water near the surface can impact, as well.
Stray voltage is the technical term given by the power and electronic industries to a situation where an electrical charge is present in the ground, itself. It can also be present in a structure, such as your home or workplace. It tends to be far more likely to be present at the ground-floor level than upper floors, and is commonly found present at insignificant levels almost anywhere electricity is used. It can even be found in places where there is no AC power nearby present, at all, if there is Quartz bearing rock in the substrate. Concentrations of Ferrous rocks and ground water near the surface can impact, as well.
In structures, the type of structure materials and design can impact prevalence, as can furnishings and the layout of property. And though considered rather rare as an actual problem, for some reason, it is normally thought of or understood as being significantly more problematic in rural farms (especially noted in dairy farms) more than in bedroom communities, though it can be found even in downtown high rise areas. It seems to impact Cows in many observable ways, to include reduced milk production, troubled births, general health and premature deaths.
The power industry takes great care to prevent stray voltage levels from being detectible or able to impact living things, including you and me, but things can go wrong. When that happens, and depending on how strong it ends up being, it can be quite detectible, and generally, unpleasant, if not harmful or even dangerous. Some forms are capable of outright electrocution, such as created by downed high-tension power lines. While this post uses the term Smart Meters in the title, it is less about that, except that a possible conspiracy may exist between Smart Meters and stray voltage, as outlined below.
There are many reasons stray voltage might be present at problematic levels. I see these as divisible into three threat levels and causes. The first may be relatively minor in threat level, caused by natural eventualities unrelated to targeting, and unlikely to escalate in nature. An example might be living near to high-tension lines running parallel to metal fencing on your property, where a kind of induction takes place causing the fence to produce an electrical current.
The second is also unrelated to targeting in causality, but may be far more serious, even dangerous, and quite likely to escalate — such as may due to electrical shorts or combinations of other unhappy electrical happenstances. The important thing to take away is that the bulk of stray voltage may have nothing to do with being targeted, but any presence which is detectible should be of great concern to anyone, and pinned down immediately.
The third? I have recently discovered a new possibility, thanks to a coincidentally… even accidentally discovered set of facts learned from one of my very first TI clients. I say coincidentally, because in considering the new information, it dovetailed very nicely with other client information which had otherwise led nowhere. As result, I am now quite confident that there can be deliberate targeting by artificially creating and controlling stray voltage for the purpose.
It can be used to establish a variety of selectable threat levels and targeting effects (symptoms), to include other forms of electronic targeting. This level is not officially recognized to exist by the power industry, though the potential for conspiratorial knowledge and participation in its use surely exists. One would be unwise to broach the possibility with power companies or other parties, unless part of a legal response effort, as mentioned herein. The good new is, that regardless of the three types, any serious threat levels can be dealt with, almost always.
To weaponize AC power in this way (there are other, previously known and frequently spoken of ways, such as found in my book, MC Realities), simply requires shunting of power to the earth at one or, as is more likely, multiple locations around the property. This would likely be done through a control mechanism to throttle the voltage diverted, even to an ‘off’ position, something akin to a remotely controlled dimmer light switch. Naturally, it will consume significant electricity, and that will turn out to be a blessing, as we shall see.
After reading this short introductory post, a TI would be well served to learn more about the topic, even if not thinking themselves impacted by stray voltage, currently. As the link to that information only addresses the first two reasons, the reader should indeed finish this post, first. After reading BOTH sources, then, and only then should they attempt to fit their circumstances into the dialog and consider the best course of action. Feel free to contact me if unsure, at proparanoidgroup gmail com.
Symptoms, regardless of cause
At natural ambient and other low levels of stray voltage there should like be no outward signs discernible. We only need worry about the phenomena if we do start to sense effects. We have all experienced the random static discharge of touching a door knob after walking across a carpet. While discounting such experiences as carpeting woes, they can also be due to stray voltage, which can certainly augment or simulate carpeting-caused static build up, as not all carpets generate the problem to the same degree, or even at all. When you get such discharges in the absence of carpeting, that is a typically a clear sign of stray voltage — though cold dry air can contribute, as well.
Note: normal static discharge is usually relatively high in voltage but low in amperage, quite akin to that associated with spark plugs in an engine; unpleasant to experience, but relatively harmless, more likely to cause injury from jerking away with violent contact with another object, than from the actual shock. They may generate a small visible flash of light, an actual spark jumping a few millimeters, at most. But stray voltage can produce far more varied and dramatic, even dangerous results. There have been instances of seeing discharges which travel inches or even feet, making zapping or popping noises, producing heat. The risk of fire and explosion cannot be ignored, where flammable fumes or pure Oxygen sources might be present. Obviously, the voltage levels in such cases are even higher, as may be the amperage and risk of electrocution.
 Serious levels of stray voltage can cause effects similar to other forms of electronic targeting, and may indeed be augmenting such targeting from other sources. In point of fact, especially for persons who also suffer electro-sensitivity, there is a small chance that some persons who see themselves as being a TI may in fact not be. Accidental, or even natural stray voltage might be causing enough symptoms of targeting, by itself, to erroneously presume targeting. This would be good news if the individual is not also experiencing non electronic targeting symptoms, such as organized stalking, or other forms of harassment.
Serious levels of stray voltage can cause effects similar to other forms of electronic targeting, and may indeed be augmenting such targeting from other sources. In point of fact, especially for persons who also suffer electro-sensitivity, there is a small chance that some persons who see themselves as being a TI may in fact not be. Accidental, or even natural stray voltage might be causing enough symptoms of targeting, by itself, to erroneously presume targeting. This would be good news if the individual is not also experiencing non electronic targeting symptoms, such as organized stalking, or other forms of harassment.
Electronic targeting symptoms are radiographic in nature (radio and electromagnetic), and therefore, stray voltage symptoms, would typically be some combination of any number of things which match those same symptoms. The range of symptoms is broad, from headaches, nausea, dizziness, mood swings, sleep problems, sensations of burning, tingling, vibrating, tinnitus or humming sounds, as well as more unpleasant physiological symptoms such as heart palpitations, chest pains, muscle and joint pains, fibromyalgia-like conditions, twitching or trembling, and so forth. Arguably, there are other symptoms, as well, but these are the more commonly reported ones, and the easiest to identify as being abnormal. That said, the caveat is valid: don’t presume a system does not have a medical explanation; always see a Doctor (without talking about targeting) to make sure you do not have a ‘simple’ health issue in need of treatment.
In fact, stray voltage can simulate or stimulate a variety of general health problems in humans and animals, alike. When doctor’s tests find no other explanation, stray voltage (or other electronic targeting) may be to blame. Some animals are more able to sense stray voltage and will naturally avoid areas where it exists in undesirable levels; they can be ‘Bird Dogs’ to the problem by strange behaviors or health issues. High levels of stray voltage can also cause plants to die, or may result in random discharges between objects otherwise insulated. By way of example, a visible mini-lightening flash between an automobile and the ground or nearby fence or garage door frame.
The interesting thing about stray voltage is that its effects may be amplified by humidity and moisture, or even temperature. Therefore, such effects might tend to be more noticeable if walking in the rain or while wet, as when exiting the shower. Serious stray voltage could make swimming pools and standing water dangerous. But even relatively harmless but noticeable levels of stray voltage can be dangerous, because whatever is causing them could be capable of sudden and unexpected increases to dangerous levels. Take no chances, and deal with it right away, if symptoms are present. See below.
Smart Meters and stray voltage; a possible new conspiracy

The cover story for the hazmat-like wardrobe used in Smart Meter installation is ‘arc flash’ protection, yet no such precautions are needed for ordinary meter installation. In the UK, the protection is even heavier duty than this; suitable for sci-fi spacemen.
A lot of people, including many TIs, feel that the entire power industry’s move to Smart Meters is a Big Brother and/or industry conspiracy. Like most good conspiracies, there are multiple theories involved, ranging from price gouging to spying to mind control, and more. But the big concern and commonality in many of these theories tends to include the very same health issues as found in stray voltage.
Yet when the industry itself, as well as third-party independent testing firms investigate, most such studies indicate smart meters are no more dangerous than your computer’s wifi connectivity. I’m quite unconvinced about their conclusions, but I also understand how conspiracies work, and how the intelligence community thinks — and specifically, how they think about and employ mind control tactics.
It dawns on me as result of the dichotomy between the reality of Smart Meter user experience and test results, that there may be a conspiratorial answer which explains the conflict. Once a Smart Meter is installed, perhaps Big Brother comes along and uses the Meter to establish stray voltage. That would account for the health effects and higher bills, and certainly still enable spying and mind control capabilities.
The simple fact is, the studies giving a clean bill of health to Smart Meters are only testing the meters and the air waves. They are not testing for stray voltage. So, if you have a Smart Meter and are experiencing Smart Meter woes, perhaps you ought to test for stray voltage. If you find it exists, you will undoubtedly be advised by a lawyer that you have an excellent actionable case against the power company.
Note: It has been discovered that the power industry, in order to address public distrust of smart meters, is instead apparently installing meters which look identical at a glance to the old mechanical meters, but which conceal a ‘trojan horse‘ Smart Meter under the skin. They are, however, supposed to be easy to spot. TAKE NO CHANCES, and check YOUR METER, today, even if an ‘opt out’ user. And, if told you were not getting a Smart Meter and discover a trojan horse, you once more have a reason to contact a lawyer, and the media.
Stray voltage as targeting weapon
Deliberately causing stray voltage as a harassment tool is not the only ‘advantage’ to perps. Because electricity can carry embedded RF signatures, it can cause an entire area, such as a home and its yard, to become a kind of transmitter of other forms of targeting signals, just as can house wiring. It can therefore become a kind of amplifier of such methods. But to employ it requires something which should ideally be relatively easy to detect, and defeat.
Simply shunting your existing AC power to ground, a deliberate ‘short,’ if you will, is NOT normally going to be done because the power bill would go up dramatically, and tip the victim off that something was amiss. Therefore, the perp would need a second electrical service on site, which means a separate meter head, which they then ‘weaponize’ for the purpose. In apartments, it might simply mean using a neighboring unit’s meter. In a home, it may mean a separate power line to a concealed meter somewhere on the property or just outside the property line. It may be an underground service, even if the property is otherwise serviced by an overhead feed.
In an apartment situation, all the meter heads for a group of units are mounted at the same location, and labeled as to address/unit. If suspicious, you can wait until a high consumption power period (i.e., using your stove to cook), and then go look at the meters. If you do this when you see signs no one is present at the suspect neighboring unit (not using their stove), but their power meter is drawing more power — you may have found proof of the method and the perp.
In the case of a single domicile, simply call the power company and ask if there is more than one meter assigned to the address, or if there is a meter or extra meter assigned to neighboring lots. If the answer is yes, ask if any extra meter is in use and being billed, or if you might be able to acquire the meter for your own use (to justify why you ask). Any extra meter may be proof of the method and, with some legal steps, lead to identifying a perp.
Proving stray voltage
 To confirm any such targeting, you will need to prove stray voltage is present, the same thing which should be done if symptoms are present and targeting is not involved. There are three ways to do this. One is to call the power company, which has a legal liability to insure stray voltage does not exist, in the same manner that natural gas providers must worry about gas leaks. Another is to call an electrician. Either of these methods can also result in identifying and curing the source cause of stray voltage. It will likely be up to you to document their findings, such as with video or witnesses — though they may be willing to provide written documentation where they bear no liability risk. Again, you probably should not mention targeting concerns to these people.
To confirm any such targeting, you will need to prove stray voltage is present, the same thing which should be done if symptoms are present and targeting is not involved. There are three ways to do this. One is to call the power company, which has a legal liability to insure stray voltage does not exist, in the same manner that natural gas providers must worry about gas leaks. Another is to call an electrician. Either of these methods can also result in identifying and curing the source cause of stray voltage. It will likely be up to you to document their findings, such as with video or witnesses — though they may be willing to provide written documentation where they bear no liability risk. Again, you probably should not mention targeting concerns to these people.
The third method is less useful in terms of evidence unless you are an electrical engineer or have similar credentials validating the quality of your findings; you can obtain test equipment and test the matter yourself, again documenting every step as you go. It is not quite as simple as the illustrated image, and should involve more than one kind of instrument. The procedures will vary depending on where you need to test, and what the location is like or contains in the way of objects and surfaces. The entire property should be assessed, and if done usefully, will ‘map out’ zones of impact from high to low. More information on the ‘how’ is available online, including that link you should read after finishing this post.
Regardless of which method used, where targeting is suspected, know that the power can be turned off remotely as soon as any perps involved discover testing is about to take place. This means you will want to covertly order any such tests, and ideally, try to find a way to avoid having whomever shows up to conduct the test show up in a marked truck, and having them quickly first test somewhere out of sight from any possible perp surveillance position. THAT is the hard part. Doing that yourself is much easier, of course.
Impact, conclusion
If you are a TI or suspect same, I urge all readers of this post to comment as to their findings or conclusions upon further investigation. In two and a half decades of contact with 12,000 TIs, I have only known of perhaps three or four cases where stray voltage was in any way evidenced. As result, it appears to be an entirely ‘unknown’ targeting method (assuming such was the case). I have only recently been made aware of the possibility that a power company can have two different meter heads assigned to a property under two different account names WITHOUT the property’s owner/renter’s awareness, even though BOTH are in use — by SOMEONE.
It can only serve the greater TI community to learn if this is more wide spread than thus far observed, especially given that it can be easily detected and defeated if and when in use. Ditto because of the advent of Smart Meters, in which case this new information may be a very useful weapon for use by activists against the power industry, and legal pressure (lawsuits) by user-victims. It is equally important because where targeting is not involved, education on topic may lead to resolving a potentially deadly stray voltage of less sinister origin, and address final cure to otherwise unresolvable health issues.
And, in closing, let me state it once more. Any instance of serious stray voltage, even if not related to targeting, likely represents an actionable legal issue; you should consult with a lawyer about suing the Power Company and/or whomever pays the bill on any secondary meter head causing the effect, or any otherwise weaponized meter head.
FCC to Kill Local Television as We Know It
Once more, we see the Federal Government usurping power in ways which both benefit the big corporations at the expense of personal freedoms and financial viability of citizens. This time, it’s the FCC, and not the BLM, and they want to eliminate any chance for you to watch local television without paying through the nose for it… and suffering de facto censorship.
by H. Michael Sweeney proparanoid.wordpress.com proparanoidpress.com proparanoid.net
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Please comment any such repost to original posting.
FTC to Kill Local Television as We Know It
Tuesday last, a little heralded announcement by the FCC once more revealed how controlled mainstream media is. They, more than anyone, perhaps, should have been screaming the news from the rooftops, and complaining about it, as it affects EVERY major and secondary television station in every market across the country. The ramifications are so broad and sweeping as to threaten the very social fabric which defines us as a nation. In summary, the threats are as follows:
- Eliminates all local television service as we know it today, virtually ELIMINATING ALL OVER THE AIR BROADCASTS. No more ‘free TV.’
- All licenses by FCC currently in place are cancelled, and ‘up for sale,’ they want to raise 60 billion dollars which will be unaccountable funds off the FCC budget. This means they can be spent on any black project without any accounting.
- Major stations (e.g., your local ABC/NBC/CBS/FOX affiliates) will be paid many millions from the sale, far more than the stations are actually worth; hush money not to protest, we must presume.
- Secondary stations, including repeater stations or small unaffiliated stations in deep rural markets, and even possibly PBS, will be paid NOTHING, a virtual THEFT, and possibly, a loss of all public broadcasting systems!
- All will be sold to Cable and Web content providers, forcing consumers to get any TV by paid subscription or on-demand purchase.
- Significantly eliminates local news coverage, limiting it to official sources only; the government’s preferred message, a form of censorship which effects de facto mind control.
- Stages the FCC for total control of Web content under the new ‘authority’ it declared for itself last year; easier to censor and dictate what you can learn if there is only ONE resource and it is controlled by government.
It follows the Fascist model: The plan is insidious beyond belief once fully understood. It is perhaps no coincidence whatsoever that it follows Obamacare. If one reviews history of the quiet takeover of nations by Fascists and other dictatorships, those ‘bloodless revolutions’ always start with the complete takeover by government of all health care, followed next by takeover of all media. What follows is usually great financial and social upheaval allowing significant draconian responses, to include something along the lines of Hitler’s Brownshirts and the SS, and a permanent war footing with an expanded military and military police state. But people never learn by the mistakes of history, and there is plenty of that…
It happened that way in Germany, Italy, and in South America, it happened again and again. In each and every case, the takeover steps were quietly initiated and never fully understood even by those involved in enacting the changes. In every case, they inflicted greater hardships socially and financially upon citizens than those woes they claimed would be addressed thereby. In each case, a central power figure emerged who responded with ‘law and order’ and bypassed, neutered, or altered the form of government to a Fascist regime.
Unfortunately, any and all of the current Presidential candidates, save one, could fit that bill in this author’s opinion. Trump appears to be a closet fascist, Cruz appears to be one of the same old gang of criminals who brought us to this point in the first place, Bernie is a closet Communist, and that awful woman is simply a criminal rapist of nations and peoples. But my opinions are unimportant. Even if whomever is elected is not set to be a fomenter of fascist revolution, the power elite who manipulate politics will simply assassinate them or blackmail them to assure the desired outcome.
Naturally, like most draconian moves by government, the official propaganda is worded exactly the opposite in tone to the reality. That’s why we get Bills that actually accomplish the reverse of their title, like ‘Affordable’ Health Care Act. Believe as we say we do, and ignore what we actually do.
Take a look at FCC’s official page, here.
Now, lest you think me simply another lunatic conspiracy theorist, I got my first wind of this plot, to include all points cited herein (save my opinion on SOME of the candidates), from a conservative call-in radio show where the station owner of a secondary market called in to shout a warning and explain exactly how it was rape and pillage of the television industry and the public in favor of Cable and Web bigwigs. I don’t make anything up; I don’t have the time nor inclination!
Related articles
- Big Brother FCC Plans Internet Tax/Controls What Happens in Homes (universal free press)
- FCC No Longer Just Big Brother, Now Big Parent (huff post)
- FCC Sparks Fears of Big Brother in News Room (fox nation)
Free Will Haven; Targeting Free Intentional Community for Stalking Victims
When I created the Free Will Society to aid stalking victims, one of the lofty goals was to eventually build some form of Safe Haven community for them. That dream now seems on the threshold of coming to pass. The result is Free Will Haven. iWhere can a targeted individual get help? Free Will Haven; Targeting Free Intentional Community for Stalking Victims by H. Michael Sweeney proparanoid.wordpress.com proparanoidpress.com proparanoid.net copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Please comment any such repost to original posting. What is Free Will Haven?
Free Will Haven?
MAJOR UPDATE/REWRITE: Aug. 2017. It’s been three years now since we formed the Free Will Society with the intention to establish a low-cost, self-sustaining, targeting-free intentional community (Free Will Haven) for stalking victims who can’t get a fair shake at life in populated areas. A lot has transpired, some of it really good, some of it bad, and now, it looks like we are ready to ramp things up a bit. So I thought this page should be rewritten, and perhaps, be simplified. Very little of the original post remains, or remains unchanged, and I have added rather a lot about the Beta site which was established and our plans for an even better location. Over 2,500 victim days targeting free! Compare that to over 12,000 stalking victims I’ve had contact with over some 25 years where almost every victim says they can’t get even a few days respite, if not for the stalking, then the fear of it.
Intentional Community? Beta site has been undertaken
Wikipedia’s definition for Intentional Communities is a full paragraph long. Simplified, it is a community planned from the start to cater to specific persons of like (interests, beliefs, goals, needs, etc.), typically favoring alternative lifestyles which foster those goals. You can learn more about such communities at sites like tedxblackrockcity.com (informative video), ic.org (a kind of ‘superstore’ of centralized info on topic), dba Fellowship for Intentional Communities (Facebook page). The Free Will Society is now a Member organization of the FIC, which gives us access to a mountain of informational resources and other aid not previously enjoyed. Much of this is now available and useful to FWS Members as result.

P.O. 1941, Clackamas, OR 97015 — no phone service here
In Free Will Haven’s case, our goals are ecological and consumptive sustainability (not to be confused with the New World Order’s use of ‘sustanability’ when pushing Codex Alimentarius, Agenda 21, GMO foods, Genetic Engineering, Global Warming, Carbon Tax/Credits/Currency, etc.); survivability (in this case, against all forms of surveillance, stalking or targeting of individuals in any manner), and financial and spiritual wellbeing (the unchecked pursuit of happiness through exercise of God’s gift of Free Will). Defensive survivability lays at the heart of the plan, and is based on the many books and online consultancy I have made available as a privacy/security expert to targeted persons for more than 25 years as The Professional Paranoid, the title of my first book.
Low cost is addressed primarily by focusing on portable tiny homes, or RV vehicles for short-to-long-term housing, and communal style co-op sharing of centralized services and site-produced foods and resources. Cottage industry will be encouraged to augment personal incomes, and/or like projects for the collective. It is the goal to allow one to live a decent and enjoyable life-style for less than $500 a month, total outlay (I’m managing on $400), that figure based on purchasing of food and supplies from outside sources. Once self sufficient, costs would decrease accordingly.

Rendering example of tiny home intentional community
I think of FWH as a bit more flexible than a community. I see it as also acting as a short-term hospice for those seeking temporary shelter and healing from their ordeal, and in some cases, a school of defensive arts, and even self-replicating factory. Residents can stay as long as they like. Once fully rested and obtaining stability in their lives through being targeting free for a sufficient period, they might wish to return to society, perhaps under a new identity (we can help with that), or, perhaps, having learned what it takes to establish and operate such a community… go out and create another one, somewhere else. We would like to see several of them nation-wide, and even internationally.What makes Free Will Haven an intentional community?
Tiny homes and RV life style?
A tiny home generally references any small living space intended to be extremely practical and economical, though minimalist in nature. As a rule, this commonly means either a starter home for a young couple or single individual, or a retirement home for someone without a family, as a tiny home cannot have many rooms dedicated for family functions and individual compartmentalization.
The original tiny home movement included exotic efforts with costs of $1M or more not uncommon; ultra modern, hi-tech, and with prestige designer labels attached. The grass roots version, on the other hand, has gone wild finding ways to do as well with less, with costs ranging from well under $10K to perhaps an average of about $40K for the higher end; about what one might put down on a conventional home mortgage. This has resulted in an almost unlimited array of possible home design types and, as result, flexibility in meeting individual needs and tastes, like these as found at pinterest.
You can have tree houses, container homes (check these out), domed homes, spray cement (free-form shape) and similar homes (check this video out, and this), underground homes, and more, including homes that simply look like a normal home but scaled down… some of which are on wheels. That brings us to the fact that a motor home, RV vehicle, trailer, or even a manufactured home also qualifies. All of these are on the drawing board/table at Free Will Haven.
The ones we favor most are the ones you can order pre built and delivered to the site (look at these, and you can even get an ‘Ikea’ home complete with furnishings), or the ones you simply buy plans or kits for and then build yourself (like these). Or, they can be ad-hoc, and built from whatever you can cheaply get your hands on. Google any of these home types for endless solutions to choose from, and when it comes time to actually consider residency options, we will work with you to fine tune or better the ideas you favor.
I have established a special page chock-full of information about the ins and outs, pros and cons of the almost endless options available in choosing an RV type or style of Tiny Home. It also addresses the lifestyle, itself. RV solutions provide a quick and dirty ‘home’, completely self-contained with everything needed including their own backup generators. Tiny homes tend to be minus some aspects, such as bathrooms, but can include them; its up to the individual. They can end up being more roomy and comfortable than an RV, and seem more ‘homey.’
The Free Will Haven concept encourages use of an RV upon arrival, and the construction/installation of a tiny home (many of which can be portable and towed like a trailer). If electing a tiny home, any RV in hand can then be sold or rented to someone who does not have one, sold for long term, rented for short term. The same can be said for the Tiny Homes should a resident choose to relocate and not take the home with them. There is no reason anyone should feel that becoming a resident has no exit options. Quite the contrary. It increases options.
Beta site effort proves viability

Beta site proved concept quite workable
The original Beta effort has resulted in the purchase and operation of a rather off-grid beta site by one of our founding members using their own money. It operated for about two years serving two TIs using most of the basic plan established by the Free Will Society. For whatever reason, the owner/operator of the site elected to abandon reliance upon and participation with FWS, though we had provided money to help pay for installation of electrical power to the site. There are clues it involved personal matters as well as relationship issues.
While there is some mystery as to why a refusal to engage in dialog, it is clear the Beta site was successful in terms of the key-most goals; survivability targeting-free. We are grateful for their effort. The Beta site failed only because of eviction for contract violations of some sort, presumably through miscalculation by the owner/operator in absence of help from the FWS. Due diligence is always upon the purchaser, who was at a disadvantage in many ways in terms of ability to do so. It is a regrettable outcome.
Meanwhile, I myself have been living as a homeless person in a motor home. I have essentially established a semi Beta site of my own where I was the only resident, also in a deeply rural environment. Between my experience and the actual beta site, there has been a total of more than 2500 targeting-free days. It has been a joy for me, and the Beta site operator has come forward publicly to express positive views towards the experience and an intention to attempt yet another effort. In that effort, the operator has affiliated with a new core group with a troubled past with respect to credibility and honesty, and we wish them all better luck.
The concept is proven. 2500 stalking free days!
Now it is time to move forward more earnestly, and do it right, this time.What is a tiny home like in Free Will Haven?
The future: location and logistics?
The original beta site (image) was less roughly 1 acre in size, and rather a long, narrow unimproved property at a high altitude in a colder part of Oregon with a dry clime (annual high of less than 60 degrees). It had no water but was near to a river with drinkable water and fish, and she had a water filtration system. It would support a well at shallow drill depth. It had no power but as it fronted a main highway for the area, it did not cost much to install power. It would support raising crops, and was established with an Airstream trailer (very nice) and several other towable items, and self-assembled Quonset-like structures for storage and greenhouse function. It is not known if a second RV was brought in for the second resident; the Airstream is thought to sleep up to four persons in two different accommodations. Still, it is not a terrible site, actually fairly decent given it was purchased sight unseen and based on a limited budget.
This site was not chosen with the help from or according to the ideal guidelines established by Free Will Haven. Since the purchase was made with the operator’s money and in consideration of their small income, that exercise of control was perhaps expected. The basic-most needs were considered to the extent possible. But While there was some good visual separation between the site and neighbor structures by trees, it was not as private as FWS would prefer. There are two neighbors within about 600 feet of the property (less than a city block). The nearness of a main highway, though also buffered with a lot of trees, is also not a perfect situation. I do like the fact that the rear of area (not shown) is backed with a high bluff which is uninhabitable, and provides security.
We can and should do better. Recently, my Publisher bought some property at auction and invited me to live there rent free. While it turned out not to be possible due to dense forestation requiring expensive work just to get onto the property with a motor home, the method of acquisition was unrealized in previous review of potential sites. Things are looking up.
 Compare the the Beta site to this 20 Acre property which represents the ultimate site for meeting goals established for Free Will Haven. The road is a gravel road established for timber harvest and is seldom used by anyone but hunters — residents could hunt on the property if desired! It dead ends at the property, which is a flatland at the top of a hill, and continues into the property as shown for easy access.
Compare the the Beta site to this 20 Acre property which represents the ultimate site for meeting goals established for Free Will Haven. The road is a gravel road established for timber harvest and is seldom used by anyone but hunters — residents could hunt on the property if desired! It dead ends at the property, which is a flatland at the top of a hill, and continues into the property as shown for easy access.
It has multiple developable locations and area for growing crops without the need to fell trees. There is NO ONE for miles in any direction. These are the kinds of features preferred in the actual site. Depending on many factors, a really good site could be as small as perhaps 5 acres and still prove satisfactory. Geographic features such a hill can negate concerns about privacy as relate to adjacent properties. There are many such opportunities; cliff faces or steep terrain, rivers, national forests, etc., can all be allies.
This particular location is very inexpensive to purchase despite the larger acreage, simply because there is zero access to commercial power at any cost. That lets it out of consideration, as neither solar nor wind power enjoys economy of scale in the levels required to support a comfortable life style for a given individual, much less a collective. It would take approximately $9,000 per living space for solar, for instance — without a battery system to cover nighttime use (another $4,000). Figures are based on the same power level as the generator output in a typical Motor Home. If one had a few hundred thousand to tie up into an off-grid house, that would be a small bit of the budget. But that’s not your typical stalking victim. I’ll mention here that the weather is much nicer at this location, too, withs highs in the 80s.
The all important factor in any land acquisition, of course, is cost, including what it will take to occupy it successfully. As it happens, there are properties which fit these kinds of requirements which are available at a price I can afford. Sort of. The trick is finding them where the owner will finance with ‘ez credit terms,’ which, fortunately, is not unheard of. I have to be able to handle the monthly payment out of my pitiful social security payments, and have a low enough down payment that I still have money to pay for bringing in power and a water storage system, and a few other items such as a storage shed, and a freezer (a Motor Home typically holds about four days worth of frozen foods).
Alternately… should the Society obtain a large donation or one of our members win the lottery (I buy tickets), I’ve found marvelous properties in Missouri which offer as much as 160 acres fully developed as a farm or ranch capable of producing an income suitable to cover mortgage… for less money than it would cost to buy a house in most big cities. Many of these have rivers, lakes, or ponds and wooded areas full of all manner of wildlife, such as Wild Turkey, Geese, Ducks, Deer, Boar. This allows hunting and fishing right on the property, many of which have hunter’s cabins or blinds in place. But I’m not waiting for $300-500K donations.
I’m scouring land listings for something I can buy NOW. And, I will be starting a new gofundme for anyone willing to help, and/or wishing to participate, perhaps, as resident.
Participation: Membership and Residency
 Anyone and everyone is requested to join the Free Will Society, stalking target or no, to support the Free Will Haven project (and other projects planned in the future). Annual membership is $25, currently payable by PayPal to proparanoidgroup at gmail com, adding comment to that effect in the message it requests in the process. Membership gives one access to more detailed information, including the history thus far of the project in detail, and an opportunity to participate in and contribute to the ongoing dialog and direction of the effort. It also gains access to dozens of resource materials from our membership in the Fellowship for Intentional Communities.
Anyone and everyone is requested to join the Free Will Society, stalking target or no, to support the Free Will Haven project (and other projects planned in the future). Annual membership is $25, currently payable by PayPal to proparanoidgroup at gmail com, adding comment to that effect in the message it requests in the process. Membership gives one access to more detailed information, including the history thus far of the project in detail, and an opportunity to participate in and contribute to the ongoing dialog and direction of the effort. It also gains access to dozens of resource materials from our membership in the Fellowship for Intentional Communities.
One must be a Member to apply for residency. There is a separate $25 fee to cover the application process, which is required to insure that all residents will be able to benefit without social incompatibilities. It is unfortunately true that there exist people who claim to be stalking victims who are not, for instance. While one can join and apply simultaneously, I advise against. Membership will provide access to a flood of information and direct contact with other members, and could conceivably end up changing a person’s mind about residency. One should be fully informed before deciding.
The application process further educates the applicant toward decisions about if, when, and how to undertake the actual move. It analyzes the applicant’s ability to actually undertake the venture with a reasonable expectation of happy success, fully informing them of what to expect in the way of possible downfall, all based on their precise personal situation. A checklist of things to consider and steps to be taken is reviewed in great detail, critical in determining the true cost of ‘move in.’ Once approved, they need not act immediately, and can work through the checklist at their own pace, as may be dictated by anything from costs to family affairs in need of tending.
![]()
How Social Network Trolls Target, Track, and Psychologically Profile You
How to spot and deal with Trolls, including a clever tool they use in any social media capable of posting images (VERY prevalent on Facebook), and quite insidious with far reaching implications. BEWARE: you betray yourself and your friends if you take things at face value.
What is a Web Troll?
by H. Michael Sweeney
copyright © 2014, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this paragraph, are included.
How does being a web troll work?
UPDATE: Nov. 11, 2014 Perhaps as if to ‘test’ me as result of this article (or not), a Web troll began the process described herein to goad me argumentatively while also employing a good half dozen of the usual disinfo tactics in the 25 Rules of Disinformation (linked below). So I unfriended him and watched: that same day, ‘someone’ created a new FB account and almost immediately friended two of my friends, posted ONE activist post, and ONE peace post, then requested to friend me. Sure. OK. BUT I HAVE MY EYE ON YOU, because that’s how easy it is to get a new identity and hook back up to a target. Not that I care. Trolls are tasty.
Are you being targeted by online government trolls
How Social Network Trolls Target, Track, and Psychologically Profile You
Reading this post you will learn…
• That there are three basic kinds of trolls and subsequent ‘missions’ against targets like YOU; • That there are troll profiling and tracking tools or methods which can be recognized; • That there are ways to protect yourself without drawing more unwanted attention; • That the Troll represents a danger in that their ‘assessment’ can lead to escalation in your targeting. Is social media infiltrated by government trolls?Government and Commercial Trolls
Consider, for example, the friend ranking and layer’s of affiliation tracking tool. A graphic is created containing a simple textual message. It is graphical because there is no easy way to distinguish between two identical text messages, whereas, altering a single pixel’s color by 1 imperceptible shade of difference makes it unique, and allows thousands upon thousands of individually trackable versions. A Troll who has managed to friend a targeted person of interest then posts the textual graphic as if a sincere request. Examples will be shown.
These kinds of posts seem innocent enough and easily get spread as requested, allowing simple computerized search processes by FB’s intelligence community or marketing partners to see not only who is close to the target party, but at what layered level and loyalty or, if you prefer, like minded thinking. In point of fact, ANY image shared with a given political, philosophical, religious, or other belief or emotional message can be so tracked to perfectly define each such poster’s psychological profile, and rank their threat level to the paranoiac governmental powers that be. The same is true of marketing trolls seeking to learn about your product usage or demographic, etc.
The only safe share, then, we might presume, is textual or perhaps the sharing of a URL and it’s image, or an image we ourselves create and have perhaps included in our FB albums. Even with URL’s however, the possibility exists it is still being tracked, especially if a Troll operated resource such as Federal Jack, a known DHS sponsored Sorcha Faal disinformationa conduit targeting conspiracy theorists, activists, and other ‘potential terrorists.’ Their goal is to get you to ‘share’ their links, thereby spreading disinformation while psychologically cataloging YOU and any of your friends’ beliefs; all who click to learn more. They may need to have a troll assigned to them, after all, for being yet another ‘potential terrorist’ — a free thinker, patriot, constitutionalist, etc.
Worse, we have learned from our new Paul Revere of the coming Second American Revolution (Snowden), that NSA is not only monitoring FB activities big time but that Trolls from NSA, FBI, DHS, DOD, and even the FED, and other paranoid agencies, and even corporations who have a strong and growing list of people who think ill of them, like Monsanto and some banks — all regularly maintain false social media identities for entrapment and spying purposes. They even infiltrate online gaming. Snowden’s latest bombshell, according the foreign media analysts, indicates there were so many game Trolls that it was starting to change the character of online gaming, and special tools had to be developed so that Trolls would not end up targeting other Trolls and more easily remain inobvious. We are talking here, about games with chat or other communications capabilities within the game or as part of game support, especially when in a social network manner.
And it is clear that snooping is also rampant among commercial interests, which is certainly true in online gaming, which after all, is a commercial enterprise. FB is perhaps the biggest offender in this area.
How can you spot a social media troll?
Differentiating an innocent graphic from a potential spy tool…
There are several online graphical message generating services. FB themselves seems to be hooked up with one called your-ecards (.com). Another is someecards (.com). Anyone can use these to generate a simple textual graphic with or without use of stock illustration graphics (e.g., a man looking perplexed), typically in silhouette or line art form. They can then easily share it through their favorite social media(s) with a few additional clicks. These can always be recognized because the logo for the creating Web service is displayed at the bottom. An additional hallmark of such services is that the background is almost always colored, and there are scant few colors available. The default color or otherwise most popular seems to be pale blue, pale green, or yellow-orange.
So when you see a colored background, typically with larger or fancier text than a normal posting, you are clearly looking at a graphical text post. The next thing to look for is the logo. If you see a logo, it was likely a sincerely generated message by a genuine human resident of social media. However, if there is no such logo, the message may have been generated by a Troll using his own computerized tools to psychologically target you regarding a select individual hot button. Are you, for instance, a tax protester, pro gun, anti GMO, for or against a given politician or political topic, or simply, who is a good like-minded friend of yours as opposed to some stranger you’ve accepted on the Network. Such messages also tend to be minus any artwork — text only. There is one more defining clue to look for.
Because there may be multiple versions of the same message for targeting different individuals by multiple Trolls interested in gathering information about many someones, there is a need to tell one shared message copy from another, which is exactly why it needs to be a graphic. YOUR version must be physically different from MINE. The simple solution is to vary one or more pixels in a way easy for a software routine to detect, and then match to a targeted individual and their Troll/need. Given the countless millions of users on FB (and other social media) who might be deemed targets, it may mean that many, many dozens of pixels will need to be manipulated. My research shows that, indeed, most of the suspicious postings, in addition to missing the logos, have such visual manipulations. Examples:

This is an example of a Troll-generated chain letter designed to find out your religious views, and who among your friends is of like mind. Note the guilt factor in the last sentence, and no true traditional Christian message. Note also the dark aberration, a visual flaw above the numeral 9 of 97%.

This is an example of a Troll-generated chain letter designed to find out more about your true close friends, as opposed to casual Network contacts you don’t personally know. Again, note the visual flaws in the slightly darker ‘blur’ areas about the letters… you may need to zoom in. This phenomenon is common in such messages, creating a pool of pixels useful in manipulations.
So one needs to look for such abberations or flaws in the background, usually darkened pixels along the edge, most commonly gathered in clusters or strips. You have to ask yourself… if going to the trouble to create a custom graphic for a text message instead of simply typing it in, why would they: a) choose the ugly colors used by such as your-ecard if not trying to make you think it such; b) take the extra steps to strip away the logo if using such a service (the point being they did not); and c) end up creating an image with a flawed background (where did the aberration come from, if not deliberate)?
When these clues are present, you are staring at a Trollish spy tool. To then share it betrays and catalogs you and links you and your beliefs with any of your friends who do the same, and theirs, and so forth, on down the line. The proper thing to do is enter into the comments: “I suggest you delete this post because it fits the description of a Troll’s chain-letter spy tool to catalog, track, or psychologically profile and establish links between like-minded persons: learn more here: http://wp.me/p1GyKw-zi” That link goes to this blog post you are reading.
Then I suggest you share the post anyway with a similar message, “Share this to warn others about Troll spy tool chain-letters to catalog or psychologically profile and establish links between like-minded persons. To learn more about this tool, visit this link http://wp.me/p1GyKw-zi.”
Finally, look carefully at the original post. Most social media will have a means to indicate if it was itself being shared, or was a direct post. If direct, it’s YOUR Troll. If shared, the poster was gullible in sharing, and is not likely a Troll… but beware that that could be arranged for as a deceit — so watch to see if the poster repeats the ploy frequently. You might optionally go to the ‘cited source’ of the share and try to find the post on their wall if you want to try to see if they are the Troll, and on to the next if not, and so forth, posting or messaging those encountered along the way who are victims, if you can. But that can be a LOT of work.
Are social media trolls sociopaths or psychopaths?
More Direct Trolls; Psyops and Sociopaths
The real threat to activists and politically incorrect persons online, like myself, is government agents paid to do nothing but sit in front of a computer and pretend to be your social network friend, someone you don’t really know at all, of course. They don’t just post Trollish images, they comment, and even message you. Like the aforementioned tool, they seek to learn everything they can to psychologically profile you, as well as see who ‘likes’ your posts and what THEY comment. But they are also there to play mind games. You are officially a victim of psychological warfare, perhaps even by someone from within the U.S. military, or even the military of another country. They are quite often sociopaths, so chosen because those traits make them more efficient.
Here are some tips on how to spot and deal with this class of Troll, as well as the kind of Troll who is simply out to make trouble for a given collective of people who believe a certain way about a certain topic. You know the type, my favorite example being the warrior Atheist who deems it his life’s mission to ferret out believers in God and annoy them with endless barbs and zings as if they were evil and dangerous for daring to worship. These people will wax sociopathic, too, and even psychopathic, when given enough rope. UNFRIEND these kinds of Trolls.
Hint 1) Trolls work in packs or maintain multiple identities to be a self-contained pack. That way, if you delete one of them, others survive, and then they generate yet another new identity and friend request to maintain the pack. The advantage is that you can suffer a series of ‘In deference to your view, we all seem to believe the same (whatever)’ posts (i.e., you are an idiot on this matter). Sure. You might be an idiot. But at first, the pack is all positive and flattering to your own beliefs so you a) get used to seeing them, and b) start respecting their beliefs and presuming them the same as yours. That’s the worming in stage.
But when it is appropriate for profiling or attempting the role of agent provocateur or disinformationalist, they will all suddenly be believing in something more off the mark, and increasingly so, as often as not. But by now, you like them and their beliefs, and so, your reaction tends to be as they expect; they are pulling your chain, and observing your jerks, evaluating, and cataloging, attempting to modify your behavior through deceit — a form of mind control. Can you be controlled, or are you firmly centered in your beliefs? Are your notions your own, or being foisted upon you?
Hint 2) New Troll requests tend to be persons with scant history on the network, and very few posts, but posts akin to your own in substance. Note that Facebook asks you to suggest friends to them. NEVER do this unless someone you ACTUALLY KNOW in the real World. If you do it, you are giving them a list of new targets. Since I don’t fear and even enjoy playing with Trolls, I let anyone into my friend list, but that does not mean they get what they want from me. But you may be better off simply passing on marginally viable friend requests.
Hint 3) Try posting something deep and yet somehow provocative (in the eyes of the establishment) which requires a bit of reading and thought before drawing conclusions. Look for a pattern in response from the same suspect persons; a) almost instantaneous response in the manner of (Hint 1), and typically emotional rather than logical in nature. This is almost always short and designed to be inflammatory or provocative, a bit testy. This is followed by b) one or more secondary (pack) responses delayed rather a bit in time. These will be more in depth and thoughtful, and validate the former with logical argument, and may contain a link to give further credibility. Other brief pack replies may be sprinkled in for effect. Collectively, they are all in agreement regarding your idiocy (or whatever).
It is when the same people tend to respond in these patterns that you are very likely dealing with a Troll pack. You will find this is true regardless of what time of day or night you post. They never sleep because every psyops Troll is actually three people manning a keyboard around the clock. They can always respond quickly with the first response, but the careful response requires that they actually research and formulate the best supporting answer based on all they know about you and the topic, which they might need to first research, and likely, it involves a supervisor’s approval or must be compared against preset guidelines.
Hint 4) Thick skin, undaunted. There is nothing you can do to make these people not remain your friend, short of unfriending them, yourself. While they may match or even exceed your own expression of ire, they won’t go away no matter how you might choose to argue, or confront with insult. Indeed, they tend never to deal with insults directly, at all; they are irrelevant and serve no usefulness to their goal. A real person has an ego that must be defended, but they are just playing psychological games and feel superior regardless of what you say. But when you argue, watch out for the next hint, which is commonly employed in their responses.
This is also true of the sociopathic/psychopathic ‘cause’ trolls.
Hint 5) They tend to employ the 25 Rules of Disinformation. Easy to spot, easy to deal with, if you know what to look for. Be careful, though, because ordinary people sometimes use flawed presentation style or less-than-thoughtful posts which on the surface appear to fit one or more of the rules, when they are just being human. Watch for repeat performances, to know the difference. Give them rope.
Can trolls lead to real-world targeting?
Dangerous escalations; why we dare not ignore trolls
The real danger in online Trolls is this: their whole purpose in targeting you online can be to determine if you deserve real-World targeting, as well. With a few keystokes you can end up having your entire life put under a microscope; phone surveillance, tails, observation posts, bugs and cameras covertly placed in your home, mail intercepted and snooped, and so forth. Men in Black stuff. Its why I wrote The Professional Paranoid; a how-to book on detecting and dealing with this kind of targeting.
And, it can escalate further: electronic harassment, dirty tricks, political control technology (mind control) to make you look mentally ill to others, destroy personal relationships, wreck your income, and sabotage your life. For that, I wrote MC Realities, another how-to.
But it can also lead to the worst of all possible escalations; NDAA vanishing. If truly a pain in the neck to the government, a threat which needs to be dealt with more urgently… you can ‘legally’ (so they claim) kidnap you and make you vanish without any legal process. They can elect to torture you or give you over to some other country for ‘processing.’ Or, if they want, they can murder you and dispose of your body. This is how we know we are living in a tyrannical Police State, and why, then, government dare not tolerate free thinkers without Trolling them, and trampling on rights and freedoms at every turn, and why fear mongering is their number one justification. ‘Oooh… terrorists are everywhere! We need to TSA and NSA your ass for your own safety.’
What should I do if I encounter a social media troll?
What to do with a Troll
I personally do not mind their presence so much as some might. I enjoy providing them with disinformation, or provoking them to try to chase down a given pathway of dialogs only to suddenly drop the matter as if it never happened, or I don’t really care, or even was deliberately jerking their chain. I even kid them.
But most people would prefer to unfriend them, and there is NOTHING WRONG WITH THAT. Just know they will be right back with a new identity. It may be better to deal with the ones you know than to worry about finding the new ones you don’t yet know.
My favorite thing, however, is to educate them. I like posting factual material which challenges their personal beliefs that their job and their boss are operating on valid or just principles or beliefs, and purposes. I make them ashamed or feel guilt, whenever possible. It does not work with everyone, of course, but it is fun to try.
Are social media trolls dangerous?
Conclusion
Your privacy and personal safety could be at stake if you are in the hands of Trolls. The threat level is determined by how much our paranoid government fears people who fear government’s growing fascist police state/spying mentality, and dare to talk openly about it. The more vocal you are, or the more aligned with or closer in links to others of like mind, or the more active you are elsewhere on the Web, or the more followers you have, and even the kinds of searches you make (that, too, is being watched by government) and certainly, your own original postings… each of these things determine if you might become the victim of someone else’s Troll, or have a Troll assigned to you, and what kind of Troll.
And once your ‘threat level’ has been assessed, that could lead to escalations that you will not likely want to experience. If you get a sense that such escalations are already in place or happening, by all means read my books, because they will help you know for sure, help identify the players, and form defenses. You can also contact me personally for free and for-fee online consulting or direct intervention services.
It’s what I do when I’m not being a thorn in the side of tyranny… and attracting Trolls.
The REAL Reason FEMA Promotes Emergency Preparedness?
FEMA and the rest of government seems quite paranoid about disasters of late, but clues suggest there are hidden reasons behind urging preparations — not the earthquakes, floods, nor fires they talk about. Conspiracy theories based upon dialogs by geophysicists, astrophysicists, and politicos seem far more likely the cause, and that puts a whole different face on what ‘preparation’ should involve and mean for you.
Why is government pushing emergency preparedness?
by H. Michael Sweeney
copyright © 2013, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this paragraph, are included.
Can we really trust FEMA?
Reading this post series in three parts you will learn…
- That there are significant reasons you absolutely should have an emergency preparedness program in place;
- These reasons go well beyond natural disasters FEMA implies of concern;
- There is a logical preparedness program that accommodates all concerns…
- A program which should be considered by privately-held businesses as well as families:
- It is NOT approved by FEMA, DHS, the Military, or other elements of the New World Order
What is the history of the emergency broadcast system?
Time was…
I very clearly remember the ‘Red Scare’ spillover from McCarthyism which translated to ‘fear the bomb’ in the 1950’s and 60’s… starting with the Eisenhower White House: Air Raid sirens were tested weekly or daily, typically at a fixed time of day as if a Church Bell announcing Noon. I was a teen during the Cuban Missile Crises under Kennedy, when talk of the day was the home Fallout Shelter, and at school, we had ‘duck and cover’ drills as often as fire drills. But the scare wore off by the 70’s, and sirens and shelters were no longer in vogue, though every downtown building tended to have a well marked public shelter. Yawn.
Fast Forward, Bush I White House: For no visible or announced reason at all, the Emergency Alert System (EAS) and CONELRAD Radio alert system which had in evolutionary form driven those sirens for two decades was turned back on in the 90’s, and updated for improved use with TV. But rarely was it tested, and then typically late at night between late-show snoozes. Just fire drills at school. No more sirens, unless there was perhaps a fire or other actual emergency. Very unobtrusive. No problem.
Fast Forward, Bush II White House: Suddenly, somewhat synchronous with the formation of Homeland Security, these alerts started increasing in frequency and were randomly interrupting all manner of broadcasts at any time of day. They now had the ability to actually take over newer televisions, even if turned off or in use with a VCR at the time. Somewhere along the way, it was expanded to include hazardous weather condition reports and the AMBER ALERT system for missing children. Schools still worried about fires. OK. Well, perhaps.
What kind of threats should an emergency preparedness plan address?
The current threat assessment
Fast Forward, Sorento White House: Suddenly, and synchronous with DHS seeking to buy 1.4 billion rounds of ammunition (that’s several Vietnam wars worth), all over and above military orders… not to mention a long list of equally disturbing purchase efforts involving coffins, ‘emergency housing’ which more closely resembled prison camps, food and water stores, vaccinations and anti-biotics… numbering in the millions more often than not — the tests started increasing in frequency and in duration. Annoying. Suspiciously omnipresent, excessively foreboding.
What bothers me most is a synchronous rush request for proposals on delivery of emergency preparedness items and relocation and readiness orders to military to FEMA Region III (Atlantic Seaboard States near D.C.), all with a date of October of this year. In fact, much of FEMA’s promotional material is geared to 2013, specifically. Most of the darker things cited in this post are happening right now in 2013 or otherwise generally depicted as an immediate potential threat.
Worse, both DHS and FEMA have started multiple high-profile media campaigns suggesting we all need emergency kits and emergency plans. This is also all simultaneous to a bit of mainstream news and much suppressed facts being revealed on the Web regarding an approaching Planet X, approaching comets, several near misses by planet-killing asteroids, and a flurry of unusual meteor activity to include nuclear blast-strength explosions in our atmosphere (the Russian meteor injured nearly 2,000 people and caused significant wide-spread structural damage over hundreds of miles). And there is more…
Also simultaneous are geo-political and financial threats the likes of which have never been seen in the history of the planet, each threatening dire unrest to the point of forcing Martial Law. While this goes on, the sun is spitting gigantic record bursting electromagnetic pulses at us and the pole is shifting, Fukushima is continuing to increase its threat, not to mention shifting weather patterns and an increase in seismic activities of Biblical proportions. Dare I mention strange phenomenon like objects orbiting the sun, mysterious loud and scary sounds heard over thousands of square miles, two suns and other oddities in the skies day and night? Endless wars somehow always tied to terrorism and oil keep being announced. No wonder large numbers of people are actually starting to think End Times might actually be around the corner.
The end of oil supply as we know it indeed approaches. Extremist terror groups pose theoretical threat of biological, chemical, or nuclear WMD. Criminal nations threaten to attack us with nuclear weapons. China is on the verge of surpassing the US as super power, and their top military leader has said war with the US is inevitable; their only answer to that being to strike first. Man-made bio weapons, nanotech, and even genomic weapons are being developed daily by all modern military powers, and we get cover stories expressed as worries of a natural pandemic outbreak of catastrophic proportions. The Center for Disease Control has even gone so far as to talk about preparation for a Zombie apocalypse, and there is some evidence it is not as tongue-in-cheek as they profess. Don’t forget chemtrails and the feared NWO depopulation plot.

Actual soldier patrolling American Street. UNACCEPTABLE! (click – disclosetv.com)
The worst part is all the talk about a possible military takeover, martial law, a new Constitution and a North American Union. Why, that’s nothing short of saying the Antichrist is coming to power… and some say that’s the case, too. Agenda 21, GMO crops, Codex Alimentarius, the Small Arms Treaty (goodby 2nd Amendment), etc. All these things tie in one to another as if all by some organized conspiracy (Illuminati?) After all, they say, the Norway Spirals were likely a test of Project Bluebeam, to simulate with a kind of holographic event the Second Coming in the Antichrist’s name. And what about those tens of thousands of ‘State of Martial Law’ warning/instruction signs coming into the US from foreign sign makers in convoy manner? Really, really not good.
Almost everyone has some kind of foreboding sense that SOMETHING bad this way comes. Armageddon Online has a more detailed summary view. And just as someone chooses to discounts all of these things as ‘baseless,’ something like this comes along to make us wonder all over again: a lot of people are saying there is a purge of the military taking place, and that usually portends a violent overthrow of government.
So, quite naturally, some of us are taking the DHS/FEMA advice to heart, or at least considering it. But I fear most of us are preparing for the wrong thing in the wrong way. Its one thing to have food, water, medical, and key supplies stashed away for an earthquake or flood… and another to truly be prepared for upheavals of the political or Biblical sort… the sort government advice is NOT addressing, because if you were prepared for that, government looses the ability to maintain political control through dependency upon government for survival.
Never fear; the Professional Paranoid is here to help you find your way through it all… in part II: A Logical Home Emergency Response Plan: The Government Does NOT Approve
Why should I hide my emergency preparedness kit and weapons?
Related articles
- FEMA Preparing Military Police For Gun Confiscations and Martial Law (eutimes.net)
- What’s This FEMA Video Trying to Tell Us? (politicaloutcast.com)
- Dave Hodges ~ The Use Of Food As A Weapon Against American Citizens (shiftfrequency.com)
- FEMA REGION III – OCTOBER 1st – OFFICIAL FEMA DISPATCH! (prayingforoneday.wordpress.com)
- Is the FEMA Region III Alert a Red Herring? (activistpost.com)
- “Martial Law is Now in Effect” Signs: Why Would These Signs Be Printed? (solidarityintruth.wordpress.com)
I AM Brandon Raub; the meaning and relevance thereof
Lessons we have ignored from fallen Empires, both in real history, and in popular literature
by H. Michael Sweeney Permission to duplicate granted provided reproduced in full with all links in tact with credit to the author and proparanoid.wordpress.comgovernment out of control, a fascist Police State
As it happens, there is a Facebook Group named I AM Brandon Raub. I have joined this group and the commentary there has prompted this article. Please consider this an invite to join, as well. In specific, this post is in response to the analogy made in the Group that we should all say “I AM Brandon Raub!” in the manner of “I am Spartacus!” So lets examine that, and other reasonings:
government out of control, a fascist Police State
Who is Brandon Raub?

Brandon Raub, USMC, Ret., a Patriot detained as ‘Mentally Ill Terrorist’
Brandon, a highly decorated U.S. Marine, is the first to make national news of about 20 ex military persons targeted by the Federal government in their paranoia that We, The People, might choose to replace our government with one that obeys its own laws. That is to say, restore it to a fully Constitutional behavior. Currently, the Federal Government is outlaw not only to the Constitution and Bill of Rights, but in violation of the Magna Carta and many International conventions on behaviors relating to human rights, both in war and in peace. Don’t take my word for it as blogger, even mainstream knows it true.
On Aug. 16th, 2012, a small army of Gestapo Police, Secret Service, and FBI Agents knocked on Brandon’s door and took him into custody. Central to his arrest was Brandon’s Facebook posts, which I assure you, are far less critical of government than my own, and far less suggestive of dire future alternatives. I talk openly of the threat of revolution, Martial Law, and a Police State, where Brandon was more reserved, and says nothing but that which is patriotic and based in truth.
The difference is, Brandon is a recent retired Marine with significant combat skills, and I am not. Not just Brandon and the 20 others, but tens or even hundreds of thousands of recent veterans of Iraq, Afghanistan, and other deployments. You see, our paranoid government officially thinks ex military are going to become a fountainhead of domestic terrorist activities.
Actually, I think they are probably right to fear patriots, and have been trying to warn all concerned: where the actions of government are illegal and in violation of the Constitution, those with the training and skill to defend the Constitution and sworn to so defend it, ARE LIKELY to do so, if pressed to a point of last resort. The government has only two paths: forge ahead on their course toward a Fascist Police State and press the issue to an explosive tumult, or recant and find salvation in the Law of the Land, and restore Liberty to the ‘Land of the Free,’ a land falling well short of living up to the title.
In summary, and as proof of the problem, the following facts of the matter shall serve:
government out of control, a fascist Police State
a) Brandon was NOT arrested for what he said. He was arrested for ‘resisting arrest,’ but video of the event shows no such resistance. You cannot arrest someone for resisting arrest unless you first arrests them for some other charge. He was not given Miranda rights. He was arrested by local Police, and not Federal agencies. There was no other charge filed;
b) A County Judge dismissed the case stating the Petition for his Detention contained NO FACTS – NO REASON FOR HIM TO BE HELD. The Judge stated this was a violation of his civil liberties;
c) Federal agents still insist his posts are ‘terrorist in nature.’ Read his post, here, and you will see that all patriots are terrorists under government’s defective logic;
Note: Here is a remarkable video interview with Brandon by attorney and author, John Whitehead of the Rutherford Institute, so you can hear Brandon’s words, directly. Within it is the key section of the video of his arrest.
d) Regardless, Brandon was ordered placed in a Federal psychiatric ward for 30 days (but has been released short of that). Concerns were that he would be rendered a mental vegetable by chemical and shock therapies intended to neutralize him permanently, or at the very least become officially labeled as ‘mental’. The government believes that if you dare criticize government, you are mentally ill. That’s the same argument made (last paragraph in this link) in Iron Curtain countries to eliminate ‘intellectuals’ who opposed Soviet iron-fist rule. What does that tell you?
e) Family lawyers have been joined by legal council from The Rutherford Institute in seeking his release, pointing out that the legal document used in his rendition is problematic; that Civil Commitment Statutes are being used to silence individuals engaged in lawful expression of Free Speech. But the current outlaw government clearly has no concerns about Constitutional Rights.
government out of control, a fascist Police State
Say “I AM Brandon Raub!” in the manner of “I am Spartacus!”

Starz Docudrams Spartacus
Spartacus, a Roman Gladiator slave, led a revolt of Gladiators and formed an army of other slaves set free by force in the very heartland of the Roman Empire. In the end, as depicted in the popular film, Spartacus, the revolt was suppressed, and the survivors questioned to find Spartacus to be singled out for special punishment.
Spartacus stood up in arrogant defiance, but for naught. One by one, man after man with him stood in his stead and proclaimed as well, “I am Spartacus!” Their love and loyalty for their leader and their cause (Freedom) drove them, and so thwarted the Roman attempt. Well, “I am Brandon Raub in the manner of ‘I am Spartacus’.” I am as guilty as he of ‘terrorism’ for demanding a just government under the Law. I am as guilty as Spartacus for wanting freedom. What say you?
government out of control, a fascist Police State
Say “I AM Brandon Raub!” it in the manner of “I am John Gault!”
Ayn Rand‘s classic Novel (now a two-part film), Atlas Shrugged, shows the classic struggle between the forces of Socialism and Capitalism in their most simplistic and idealistic forms. Ayn had escaped living under USSR’s Socialist government to the U.S., where she found Socialism creeping into government, and wanted to warn us that ‘value given for value received,’ and ‘a man’s sweat and intellect are his own property’ should be preferred to ‘you didn’t build that’ and ‘those that have should give to the have nots.’
In her massive book, a work which profoundly influenced and changed the lives of many readers (including myself), a fictional plot element was the question found scribbled on walls and posted everywhere at large, “Who is John Gault?” There was no one by that name, in truth, but there was a man who lived the role, and the answer to the question was, he was the man “Who will stop the engine of the World;” to end the madness and restore sanity. In the end, those who understood and sought to right the wrongs joined with him in attempting to do so, each of them earning the right to say, “I am John Gault.” Well, “I am Brandon Raub in the manner of ‘I am John Gault’.” I want to stop the engine of errant government. What say you?
government out of control, a fascist Police State
Say “I am Brandon Raub!” in the manner of “I am a Jew!”
History is rife with examples of martyrdom for faith in the face of oppressive governments. Choose any faith you wish. I choose to focus on the Jews of pre WWII Germany, to make the point most evident in The Diary of Anne Frank. That point is best summed up in the oft quoted wisdom from Martin Niemöller, author of Gestapo Defied and, more subsequently made popular by Milton Mayer in his analysis of what went wrong in Germany, They Thought They Were Free. That book, by the way, with substitution of America for Germany, and various political figures and nomenclatures here in America for those of the Third Reich, could just as easily apply to our country, today. Are you so blind as to think otherwise? Read it if you doubt me, and know that I am not alone in the thought. But this is the quote which makes clear my point:
government out of control, a fascist Police State
First they came for the communists, and I did not speak out—
freedom of speech because I was not a communist;
Then they came for the socialists, and I did not speak out—
freedom of speech because I was not a socialist;
Then they came for the trade unionists, and I did not speak out—
freedom of speech because I was not a trade unionist;
Then they came for the Jews, and I did not speak out—
freedom of speech because I was not a Jew;
Then they came for me—
freedom of speech and there was no one left to speak out for me.
Had people spoke out… in unison… Hitler’s power would have been rendered futile, and his evil would have been exposed for all to see. But we all feel we are but an Ant against a man. But no Man could survive or attempt to war with ants if every ant swarmed as one body to defend their home and their right to exist. Well, I say “I AM Brandon Raub in the manner of ‘I am a Jew’!” I stand with my fellow men of good cause to defend their right to be and do as they deem best for them, as I would deem for myself. As if one of their own I lend my voice in unified SHOUT! What say you?
government out of control, a fascist Police State
I am Brandon Raub in the manner of “I am a TI Survivor.”
A TI is a Targeted Individual, which is to say, someone targeted by Political Control Technology (mind control). That can mean any combination of centuries-old methods such as gas lighting, dogging, and street theater (generally described as organized stalking), to modern methods such as Mob Flashing, Web stalking, and high-tech surveillance. Add to the mix bioimplants and electronic weapons which can simulate every known symptom of Schizophrenia, and you have the ultimate tool for rendering a victim a social, political, and financial zero guaranteed to be ignored by (everyone). This is particularly useful when the person is a whistle blower or otherwise knows something which could expose government corruption or evil deeds.
A TI survivor is someone who not only refuses to succumb to these tactics, tools developed and perfected, and employed by the intelligence community and military, and their corporate and other partners, but someone who stands firm and chooses to fight back as best as they can. I have the honor of saying I have stood with and helped TI survivors to survive for several decades, now. I know of no one more courageous.
Aside: Please consider to join and support the Free Will Society, because as such technologies are perfected, they become useful against anyone who dares to speak out or resist an errant government.
Now Brandon Raub is also a TI Survivor, and will likely be subject to more exotic forms of such targeting as time goes on. Well, I say I am Brandon Raub in the manner of “I am a TI Survivor!” I refuse to let government get away with mental torture and to use ‘mental illness’ as a political weapon by ‘creating it’ where it does not naturally exist. What say you?
government out of control, a fascist Police State
Who are you, really?
Who do you want to be? A victim of tyranny left standing alone, or a defender of self and of truths profound standing with others of like mind?
Who have you been waiting for? John Gault? YOU are what you’ve been waiting for. You ARE John Gault!
Do you need a Sparticus to lead your resistance? Or does Sparticus need you? Brandon Raub is your Sparticus, and he needs you! You ARE Spartacus!
Do you need to see a whole class of people targeted before you say anything? Then you are too asleep to the facts; they have already come for religious Davidians in Waco, the trade unions are decimated, the far left and the far right, and even the liberals, the Tea Party, and Ron Paul supporters… and now the ex military. All have been conveniently equated as terrorists for the purpose, and subjected to political targeting and harassment by Federal agents. You ARE of Faith!
Do you need to wait until your very mind is under attack? Again, too late. You are under constant attack through disinformation, dumbing down, and wag-the-dog media manipulation (propaganda is mind control). Worse, Command Solo flies your skies, and other technologies which parallel its capabilities bombard our cities with who-knows-what control signals. When you choose to accept sound bites in lieu of researching for yourself, or, to flip the tables, when you choose to accept some blogger’s commentary (yes, including mine) or some other Web source as valid without checking credibility (e.g., useful verifying links), then you are already a victim of mind control. Recognize the truth: You ARE a TI survivor!
And therefore say I; if you are any of these things, then You ARE also Brandon Raub!
government out of control, a fascist Police State
What say you?
Related articles
- I AM BRANDON RAUB (and so are you) (resourcemagonline.com)
- Why is Ex-Marine Brandon J. Raub Being Held in a Psych Ward and What Does It Say About Today’s America? (reason.com)
- John Whitehead Interviews Detained Marine Vet Brandon Raub (dprogram.net)
- HOT: Statement from Brandon Raub’s Attorneys (economicpolicyjournal.com)
Web Walker: How to Bypass Internet Surveillance or Even a Total Web Shut Down
A simple solution: establish a Web Walker, your own Internet emulation to totally bypass the existing system — and its snoops
By H. Michael Sweeney, Copyright REMOVED. Permissions to duplicate granted provided it is reproduced in full with all links in tact, and referenced to the original article here at proparanoid.wordpress.com. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down Updated Nov 26, 2012: Removed copyright and some text changes which do not impact conceptually, other than it is in preparation for creating an Open Source project to make a real operational Web Walker network available World wide. Additions introduced with RED TEXT. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down This is a serious discussion of modest technical complexity which will take about fifteen minutes to read. If you bore easily with technospeak and are just curious, don’t bother yourself. Read this short, fun piece, instead, as it has more entertainment value. And then come back when you are more serious about preserving your freedoms in the face of the NWO.The FBI, CIA, DIA, DHS, NSA, and dozens of other agencies including the Federal Reserve spy on internet users, and it is going to get much worse, SOON — perhaps to include martial law and suspension of the Constitution in the major next terrorism wave.
For example, CISPA and other legislation continues to threaten to remake the Internet into a completely transparent spying mechanism, or worse, it seems logical to expect government to shut these systems down altogether in a Martial Law or other declared emergency, or if there is a 99% Occupy on Steroids event, or worse. Since the attacks of Sept. 11, the government has created more than 260 new Agencies, the bulk of which are geared up for or in support of spying on you and me, what we do, say, and think. King George-style Sedition laws cannot be far behind, and have already been proposed by some Congressionals, though defeated if actually reaching the Floor. Currently, offering this advice is legal, but you can bet government snoops don’t want you to know about it.
Survival in the future, more than ever, will depend on access to key information, and when government actions shut down or seek to have unlimited access and control of communications… you don’t want to be just another person without a clue while serious risks to your safety unfold nearer and nearer to you; if they shut down the Web, you can bet TV, phones, and radio will also be curtailed except for ‘official’ propaganda. And when it comes back on line, it will be a totally new Internet in terms of the threat of surveillance. Read this review of what to expect under Martial Law and you will better understand the concern. I WILL NOT GO PEACFULLY INTO THAT DARK NIGHT, for it is born of pure evil, that yet more evil may be undertaken, and I am not willing to live within an evil construct with no way out. How say you?
Hillary Clinton: “We are loosing the (dis)information war (with our citizens, thanks to alternative media outlets).”
These Hitlerite Police State tactics are being undertaken by a paranoid government in the name of combating terrorism, but the simple truth is, they do not fear terrorists, but the actual truth itself, and those who seek and share it. Terrorism is an invented enemy of political-control convenience that does less harm than unrighteous violence dished out by out-of-control Police. As clue this is true, very few of the hundreds of Federal Agencies and new weapon/surveillance systems/laws are aimed directly at Terrorists. No, the focus is ALL on citizens.
What better way to combat truth and free exchange of ideas and information than through the Internet, and by it, back doors into our computers, phones, and game systems by that same digital interface? You can no longer depend on the Military-Industrial-Intelligence-Media Complex to maintain such systems, provide you with protections of your privacy, or even uninterrupted access. Its time to become your own Island of communications safety. Become a Web Walker ‘Node’ (WW node). Not just because of privacy concerns, but also in case the government moves to shut down or replace the Web with a snoop friendly version… or even a natural disaster which disables whole portions of the current WWW.
There’s nothing particularly novel about the idea (but by all means, feel free to credit me with accolades). It is not patentable, but even if it were, I would freely put it in the public domain. Also feel free to come up with better solutions; I claim no superior skills or knowledge which cannot be surpassed by the likes of an Anonymous hacker or a software or hardware engineer, or every day super geek. It is merely a nuts and bolts solution to insuring privacy and continuity in the face of an overbearing Big Brother mentality.
To effect solution which protects privacy, truth, and unbroken access requires three things. Some hardware you probably do not already have, but may easily obtain; some like-minded people willing to work with you within a defined geographical boundary; and a willingness to take a little more trouble with your communications than you may be currently used to dealing with, though much of that can be addressed by those who know how to create automated scripting. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down
Web Walker Equipment:
Most of us employ a router in our home to service more than one computer, game system, or a laptop that roams throughout the house and perhaps even the yard, etc. A typical router can service four or five such devices to a distance of a couple of hundred feet. When the signal goes through walls and furnishings, the maximum distance drops notably, but some of us may have purchased booster antenna systems to compensate the signal loss. What we need to do is think bigger, and more powerful, and to establish cooperative communications ‘nodes’ to extend range beyond our individual capabilities.
As it happens, Apple Computer has our back; visit the Apple Store for more information and technical description. Their Airport Extreme router is reasonably priced (can be purchased refurbished from Apple for as little as $130, and new for about $120 more — I’ve bought used ones for as low as $50). Take care not to confuse with the Airport Express, a lesser unit.
The Extreme does not care if you are using a Macintosh or a PC, a game system, a smart phone, or anything else you might want to hook up to it, including Apple TV, a shared printer, or a hard drive for automated backup for all connected users. Unlike most systems which operate in just one frequency (2.4 Ghz), it also uses 5 GHz, where there is less signal clutter in the radio environment. That improves both range and prevents data errors that slow things down.
But what makes it especially useful is its power and capacity, and it offers a built-in range extending feature. As it sits, it can handle up to five times the data throughput of most routers, and does so for twice the distance of the best of them (802.11a/b/g standards), and is less subject to interference from other RF sources. As an example of range, I’ve enjoyed a useful signal at nearly 500 feet away, in my car, with several homes and lots of trees and power poles between us. Best of all for our purposes, it can accommodate up to 50 users simultaneously.
And, like Macintosh computers, it has superlative security features to prevent unauthorized access, which will be critical. It is indeed extendable with the ability to add up to four ‘bridges’ (more routers) in daisy-chain fashion (or a radial layout) to essentially quadruple what is already an impressive operating envelope, or to resolve difficult signal penetration issues within a building. Bridges become range extension nodes in your WW network; a Bridge Node (B node) to allow roughly 50 more users. Lesser Apple routers also could be used, or perhaps competing units, but with reduced performance/capacity. Here is a YouTube video on setting up wireless bridging.
Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web
Booster antenna systemsWhen you couple any node to a booster antenna, you can enjoy phenomenal range. Apple has designed these units with an internal, concealed omnidirectional (all directions) antenna and provides software that controls the gain and other aspects which can improve nominal performance. Some Extremes feature a jack for adding an Apple made booster antenna, but it is also possible to modify any model using instructions found here, and a $20 adapting cable that works with any standard booster system. By itself, the unit has a 20 db rating, though apparently offering better performance than competitor units with similar ratings. Were you to double or triple that with a booster, you theoretically double or triple the distance. Only the surrounding or intervening environment dictates resulting performance (e.g., trees, structures, hills).
Boosters come in two flavors: omnidirectional to boost coverage area around you in all directions, and directional, to extend range through an arc of about 15-30 degrees in a given direction. I am told you can actually use both omnidirectional and directional boosters simultaneously with a simple signal splitter. They are available for both indoor and outdoor placement (outdoor increases reach), but an outdoor unit can be concealed inside and aimed through a window or attic vent, which is highly suggested to avoid visual detection by Men in Black.
Because networks can be ‘named’ and selected by name for use, you can have any number of WW nodes, each with or without bridge nodes, each with or without their own booster for a given directional or omnidirectional need. Any one of these can be simultaneously connected to an existing ISP for ‘normal’ use, or can be operated as de facto Web Walker ‘ISP’ in a closed network, and easily be reconfigured (plug and play, or in this case, plug and share) at will.
Directional systems usually rely upon what is called a Yagi antenna design, which may or may not be enclosed in a can or tube, or small triangular housing. Where the signals going into or coming from a Yagi are additionally passed through an amplifier, phenomenal range can be achieved, though if building your own ‘black box’ solution, you must be aware of FCC guidelines and limitations on signal strength. But by way of example, an amplified Yagi system can be so powerful and precise that it is best used on a tripod with a rifle scope to center it on target destinations miles away. That is how the WW can be made to reach users well into the countryside, where line-of-sight access is available. By such a method, it would even be possible to link nearby communities in daisy-chain fashion.
Booster systems start in the 9 db range but you can find them up to 49 db, which can mean up to 1,500 feet between bridges, give or take. That’s well over a mile in total distance if employing four bridges, and about 3 million square feet of user coverage. Claims of distances for Yagi systems of up to 4,800 feet are out there, but don’t get sucked in by anyone who sells a product specifying distance — it’s a disreputable tactic that usually involves a sham. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down
 Like-minded people to connect with:
Like-minded people to connect with:
That’s the whole point, right? Such a system is not intended to replace the Internet for everyone who is currently subscribed to an ISP. That would cause bandwidth issues beyond the current state of the art’s ability to inexpensively cope. It is to allow people of common need and support to stay in truly confidential touch and securely share critical information which would otherwise be deprived of them, or obtained from them surreptitiously without permission. So you pick and choose friends, family, coworkers, compatriots, and patriots whom you think best meet your needs. That does not mean you cannot also have others join the network to enhance functionality. Here’s how you reach them…
First, map out the locations of people who should be logical participants and who are interested in joining your WW. Some may already be ‘in range.’ For those further away, consider directional antenna or bridge solutions, or a combination. For bridges used to fill in the distance gaps with useful signals, seek out the most logical locations for placement of bridges, and see if you know someone there, or could make friends with someone in the area. Explain your goals and see where the dialog goes. Hopefully you would find them kindred Constitutionalists or Activists at heart, or otherwise willing to house your bridge unit and keep it powered up in exchange for benefits, and perhaps join your WW node or even contribute toward costs.
But bridges merely render you and up to 50 other persons within range into a relatively small private local-area WW network, and may still fall short of enough range to reach intended persons at greater distance. But there is even more we can do. Because each individual node operator/user can have multiple named routers and select which is in use, any user can establish their own WW node and serve as a relay station from one such node to another… and if needed, to another, and another, ad nauseum.
By this means, a whole city can be encompassed. Multiple routes or paths from point A to D via B and C are also advised so that system integrity is maintained if a node is lost. There are additional security-related route redundancy considerations discussed shortly.
I’d suggest an ideal WW operator’s site would look like this: three Web Walkers with directional boosters just for distance in three differing directions, and one omnidirectional for those around you, perhaps a system you make available to all neighbors who apply, over time (a move considered a security risk, at best). I think of it as being triads of node triads in a pattern which blossoms outward like some kind of Dandelion seed puff covering the whole of its core being. But there are many environmental reasons an actual geometric pattern is not likely to result.
And at the end of those routes, that is where you want your most loyal of kindred spirits, because they should do the same, and likewise at the end of their otherwise completely separate routes. Keep in mind, too, that a bridge operator can likewise add additional units and establish their own WW node while remaining a bridge element in yours. It is completely free form to need for each individual node operator/user. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down
Changes in how you communicate:
Each WW node operator/user would be key to facilitating communications beyond their own node’s connected users (other nodes). Everyone on their own node (also true of B nodes), which functions with the ease of a local network, would become a peer-to-peer communicant party with others on that node; it is a local Intranet. They would be able to easily send information and files to anyone else in that same network, or even make portions of their computer files directly available to select or even all other communicants, with or without password requirements. That is, in fact, how they could mount a personal Web site for access by others, essentially serving as their own Web host system. Nothing new in that.

Google Earth Image: An excellent resource for planning WW layouts as it can show terrain and building heights to the planners advantage.
Martial law, Police State, revolution, natural disaster, Internet shut down, CISP, PIPA
Add some Intranet email software clients or peer-to-peer clients and you get some ease of communications which would seem rather normalized to the way one uses the Web, currently. But as for Web Walker-based user Web sites, the actual Internet would be out of bounds, or should be, to prevent assault from spyware or worms designed to discover and track Web Walker activity.
One simple solution is to buy a used Macintosh, which is generally impervious to externalized attacks of this sort, and which would be safer for use on any compromised Internet government might control. Go ahead and mount Windows and your PC software on it so it behaves like a PC if that’s what you are more comfortable with. In a way, a Mac is often more ‘PC compatible’ than many PCs, anyway. Protect Web Walker best by complete dissociation from the WWW by use of a dedicated router for the actual Internet. You can easily bounce back and forth between WW and WWW sources with a few mouse clicks, and copy and past may prove useful.
But where an elaborate WW node (e.g., multiple routers in multiple directions) is employed, the potential exists to relay information (email or Web site data) between any two adjacent WW locations. And there is no end of relays possible. All that is required is a localized addressing scheme, which is easy to come by because each server has a name, and each user an intranet IP address unique to the router. So whomever is the central-most party of a Triad (the designer, if you will), would determine the name of the WW router for addressing purposes, and track THAT node’s user IPs. So to send data or request data to/ from an outside Web Walker, would only require that you knew the address; IPnumber@router name. Thus whenever a new router (node) is to be added to the greater WW network, a proposed router name should be submitted to the network to allow people to indicate if it was perhaps already in use at their end.
As in the real Internet, you should never share addresses, as that could compromise user privacy expectations. That means no one knows exactly where on the greater WW network a given user is located. So to send a request for a ‘Web page’ on the WW network, or an email, one uses email (I suggest using PGP – Pretty Good Privacy encryption because it employs a sender/recipient decryption key scheme so that only the recipient can access) to send to the WW node operator. When the operator gets it, he compares the address to those listed on his own node(s), and sends it on if the recipient is one of his ‘flock.’ This could be automated with minimal software.
Otherwise, he switches his computer over to each of the other WW nodes which link to other, distant WW nodes, and forwards the file (also subject to automation). In this way the message goes everywhere until it finds the right operator, and is forwarded to the specific recipient. If a Web page request, the recipient sends an email back containing the Web markup language code for the file, along with all embedded images, videos, etc. This may require an email client which has no file size limitation, such as a virtual private network email client, which is a good choice, anyway, for management of email by a node operator.
The flaw in this plan is that the designer would need to spend a considerable amount of time looking at data flows and switching routers and forwarding as needed from one node to another. That could prove a severe issue in a major City environment well connected to large numbers of individuals. Therefore, two additional bits of advice are offered. Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down
1) to some degree, restrict membership to those persons of value to the localized network. That means people who truly are kindred spirits, or who have useful resources or skills, such as weapons, food, or whatever is appropriate for assuring mutual survival. This is not our Children’s Internet;
2) Users should limit communications to serious needs, only. You don’t go ‘surfing,’ and you don’t send spam, or watch movies, porn, play games, etc.
3) Employ scripting, utility software, or write custom software to handle as much of the work load as possible. Macintosh has system-level scripting built in, as do many kinds of Web utilities, and Linux/Unix systems are also quite flexible in this respect.Web Walker: How to Bypass Internet Surveillance or Defeat a Total Web Shut Down
Men in Black
Naturally, the government will not like this idea very much. Who knows? They may label me a terrorist any moment for having published this idea. Welcome to do so if they want a bit of bad publicity. I’m sure I’m already on their list, anyway. But their concern means that you would likely want to hide your units and shield your rooms to prevent so many strong signals from screaming, ‘Here I am!’ Better they should see only one signal at a time, if possible, and not easily ascertain its point of origin. Ask me about Primus Pick Proof Locks for your home, if truly worried about Men in Black snoops.
Again, it would be wise to establish multiple routes between critical or important users or resources in case one route is compromised or suffers technical failure. Any two adjacent WW Node operators would know each other and would become aware of any such loss of service (again, to play safe, shut down any signal to it) and investigate carefully before deciding what to do about it (e.g., replace the route, help repair, etc.)
Unless they specifically passed a law or edict against, even if discovered, you should not likely be in too great a danger except from confiscation of equipment and questioning. Likely, the files on your computer would be a greater risk of getting you into trouble if they felt like pressing a given matter. Spare equipment, secret locations, and escape tunnels may be called for in the worst of times.
And should revolution come, I have heard it said regarding one such revolution, “It was the best of times, and the worst of times…” But in such a case, being able to communicate can make a bad time the best possible.
Update: Due to popular response and interest, I’m going to attempt to launch an Open Source Project to make Web Walker real. The first order of business will be to come up with a new name: at the time of first posting just a few months back, there was only one Web Walker out there, a Web authoring service, and one product (a one word trade name). Now, however, there are nearly a half dozen Web Walkers of all manner since then, for some reason. Why, if I was paranoid, I’d think it on purpose~ 🙂 Ideas anyone?
Click the FOLLOW button at very page top to learn more about the Open Source Project, or better yet, especially if wanting to learn about the may options or ways in which you can participate, use the CONTACT link at page top to express your interest. There will be more posts on the Project, to include many enhancements such as an inherent mechanism to simulate social networking and search engines free of advertising, spying mechanisms, and useless distracting fluff. THANK YOU for taking the time to learn about Web Walker!
PLEASE: Comment (page bottom, or contact me), Rate (at page top), Share/Tweet this article. Visit my Reader Forum to promote your own cause or URL, even if unrelated to this article.
Related articles
- Would you give the government remote control over your router? (arstechnica.com)
- Ron, Rand Paul: Get Government Away From Internet (personalliberty.com)
Informed Citizen of the Web… or Just Another Web Walleroo?
Try this short and fun test to see how dumbed down you might be…
Who knows? You might even be (gasp!) a Sheeple!
by H. Michael Sweeney Copyright © 2012, all rights reserved, Permission to duplicate in unaltered entirety with links in tact hereby given but please advise with URL via Comment or contact to proparanoid at century link net.Definitions:
A Walleroo is a kind of kangaroo.
A Web Walleroo is someone who hops around a lot on the Internet but doesn’t do much besides leave an occasional footprint of their passing through the digital landscape. They hop in and hop out with the briefest of glimpses and seldom stick around to actually absorb messages intended for them. Even when they do, they tend to do nothing useful with the information, being quick to gather visual fluff and short ‘textual or video sound bites,’ but sloth to consider actual substance and knowledge that might challenge their dumbed down state of mind. Got to hop on to the next visual bite!
Why the test? Because I note that while I may post advice to 6,000 ‘friends’ in groups of alleged mutual interests on important topics, less than 5% tend to take note and check out the material offered, and of those (say 300), less than 2% will bother to like, share, repost, rate (page top), or retweet. So I was wondering… is my writing style that bad (mostly get 5 stars when they do rate it) or do I just have nothing useful to say… or am I simply friends to a lot of Web Walleroos.
You can help me answer that by taking the test (or simply tell me you think my messages are just no good). I can deal with rejection very well, thank you. I think…
So take the test: Don’t worry if a given answer seems low or high, as they are used in calculations in unexpected ways. Everyone has some level of interest in ‘fluff’ matters of personal interest and some level of interest in more serious matters. This test attempts to quantify and measure one’s degree of interest in these two areas, and thereby to indicate their standing as either (Web citizen) Netizen or Walleroo.
You also needn’t worry if the answer seems unflattering to your sensibilities, because you can easily change your score by simply becoming more involved with the things that truly matter in life. Remember Aesop’s fable about the Ant and the Grasshopper.
Moreover, like all such tests derived by people too smart for their own britches (that would be me), it is not ‘scientific,’ and assumes much not in true evidence. It may therefore not truly reflect your actual status any more than a Political Poll really reflects who is actually going to win an election.
Straws. We are all grasping for straws. But that’s what makes it fun, isn’t it? To see if we can actually catch a straw and find it the right one? Give it a go…
Test questions (pencil and pad in hand), First section:
If you don’t regularly watch TV at all, skip this section (good for you).
How many times a week to you watch a network news show> Jot the number down, and again a ways to the right of it to make a second column with the same number.
How many times a week to you watch a talking head news/political commentary show? Jot it down, then multiply by 2 and jot that down in the second column.
How many times a week to you watch a reality TV shows? Jot it, then multiply your answer by 3 in the next column.
How many times a week to you watch a celebrity gossip/entertainment/talent show? Jot and multiply by 4.
How many times a week to you watch a sitcom or late night host show? Jot and multiply by 5. Underline these answers and add the columns up and write down the answers.
Now, think hard about the years just prior to Sept. 11 attacks and look at the total number of times for all shows. Ask yourself if you think as you look at each category if you likely watched notably more television then, than today, about the same (+ or – 10%), or notably less?
If less, double the second column total and jot it down just beneath it. If the same, do nothing, we will use the number directly. If less, divide the multiplied number in half and jot that down (approximate whole number is fine).
This is your ‘TV Media Impact‘ Score, which reflects how much of a chance your opinions, attitudes, and ACTIONS are altered by television.
New section: draw a line
How many Web Social Networks do you belong to or blogs, groups or causes do you regularly visit on line? Jot it down
Beneath this, jot down the total number of times you log into or visit them each week in total. You may wish to use margin space to jot down each one and add them up if you can’t do it in your head.
Multiply the two numbers and jot it down in the second column.
What is a typical number of times you like, share, comment, or rate someone else’s post or blog in a week – ONLY those posts which are NOT about personal matters but are actually about causes and topical matters of a more serious nature externally impacting your life, the country, or the World. Jot it down in the second column.
What is the typical number of times you like, share, comment, or rate where the topics are more of personal interests of less serious nature than the above. Put it in the second column and underline for a subtraction.
Subtract the second from the first. If less than zero, use zero.
This is your “Social Media Impact score.”
New Section: draw a line
Now subtract Social Media from TV Media and jot it down as a single, middle column. If less than zero, use a minus sign and keep going. You can probably do the rest of it in your head from here on.
subtract one for each real-world (e.g., Greenpeace, Republican Party, Garden Club, Exercise Club membership) or Web cause to which you belong and made a cash contribution or pay a membership fee, or have to go somewhere to participate.
Subtract one more for each such group to which you have attended at least three meetings in a year, and subtract five more for each instance which required overnight travel.
Subtract five for each attendance at a protest rally or public forum/debate, and five more for overnight travel, and 10 more if you participated as speaker or open dialog with a speaker, and 10 more again if you had an unpleasant confrontation with Police or other participants as result (stern words or worse).
Subtract 25 for each Web site or blog page, Cause, or Group you personally created and manage on the Web which has to do with the serious type of matters.
Circle this last result, which your final score for determining your status: Netizen vs. Web Walleroo. Lower is better as you may by now have guessed…
Scoring Section
0-5 You are a concerned and aware citizen.
The closer to zero, the more active and informed you are compared to others on the Web, and the more potent you are as activist both on the Web and in real life (they amplify your power in one with the other). you’ve probably Read at least one book each by Ayn Rand, George Orwell, Adios Huxley, and Hunter S. Thompson. You’ve read the Constitution and Bill of Rights and something by Thomas Jefferson SINCE school days, know at least two Constitutional Amendments for which you can correctly identify their number and purpose, and you know what Posse Comitatus refers to.
Now, if a negative number, you are a subversive radical
Yes, just like me, and as result you are probably being watched by one or more government agencies! Better read my book, The Professional Paranoid: How to Fight Back When Investigated, Surveilled, Stalked or Targeted by Any Individual, Group, or Agency. You tend to be a Truther and think the FED, Congress, the IRS, the UN, the Bilderbergers, the National Debt, and Terrorism are just forms of phony baloney. You have pet conspiracies you follow and probably believe in UFOs and mind control. GOOD FOR YOU! Right on all counts!
The larger the negative number, the more lists you are on with government, and the more likely you are to end up targeted by a Drone for surveillance, liable to actions sanctioned under the NDAA, have a FEMA Camp bed with your name on it, or likely to enjoy targeting with Political Control Technology (e.g., voices in your head, microwave assaults, street theater and gang stalking, etc.) You should use FOIA with all of the initialed Agencies of government to see how many files there are opened on you and what they are willing to tell you is in them. The more redactions you see, the more of a terrorist you are considered to be, and the more sophisticated resources they are throwing at you in order to keep tabs on you. In other words, THEY FEAR YOU! You are being a PATRIOT who questions government!
5-10 You are wishy washy on controversial matters, not terribly concerned that all the bad things out there can have too much impact on your life, but probably enjoy watching it all unfold, a form of entertainment. You join groups but don’t participate and probably don’t contribute. You sometimes shrug your shoulders and may catch yourself saying any of the following. ‘That may be true, but we can’t do anything about it.’ ‘As long as it isn’t me, I’m not sticking my nose where it don’t belong.’ ‘They probably know what’s best.’ ‘If you have nothing to hide, it shouldn’t matter.’ When you do choose to participate, it may be a contrarian remark or criticism, an attempt to change the subject.
10-25. You are a Walleroo! You should become more proactive in your beliefs, and perhaps should be taking a very close look at just what you do believe, and why. Challenge your beliefs to pass hard tests as proposed by those who believe contrary, and the truth may just set you free. This can alter (adjust) your priorities to be more in line with your true needs, which you’ve likely been hiding from yourself. You may even be that Ostrich with its head in the sand as the Lion approaches, hoping that if you can’t see the evil, it will not see you — like the Ravenous Blugblatter Beast of Traal, which is described in the Hitchiker’s Guide to the Universe this way…
The Ravenous Bugblatter Beast is so mind-bogglingly stupid that it thinks that if you can’t see it, it can’t see you. Therefore, the best defense against a Bugblatter Beast is to wrap a towel around your head.
More than 25? You are not only a Walleroo, but a Sheeple! You are probably perfectly content to buy whatever media and government hands you as Gospel, and tend not to care too much about scandals where they are caught lying to you, stealing your tax money, having sex with under age moist cigars, and the like. You are an adamant consumer of products and likely a staunch Republican or Democrat who accepts party line as the only line because that’s what your parents did.
As long as you can continue to enjoy your small World of pleasures you have defined for yourself (like the Grasshopper who preferred to play his fiddle than worry about things to come), you remain content. You have a towel wrapped around your head at all times, and will not even know what hit you when evil finds you. Now, hop off happily to the next bit of fluff, if I haven’t already lost you somewhere around the definitions – because if you are still reading this, I doubt we are talking about you, at all!
******
If you enjoyed this in any way, shape or form, I KNOW you will enjoy my companion post on calculating how much money the Federal Reserve has cost you personally. Its a bit more complex, but far more interesting and shocking in results.
Related articles
- Dissent Without Permission: Will Protest Permits & Free Speech Zones Halt Or Hasten Rebellion? (corporategreedchronicles.com)
- Political Parties are Like Entertainment for the Compliant Sheeple (libertarianreview.us)
USAF Command Solo: Airborne Mind Control for the Masses
Not even the aircrew knows what they are telling you to think
by H. Michael Sweeney
Note: in preparation of this article, which updates and corrects some prior material I’ve posted in the past, I had intended to copy material already posted at my proparanoid.net Website, only to discover it appears to have been hacked (my host service stopped using Macintosh, it seems). The entire article relating to Command Solo has vanished, links and all. I wonder who would have a motive for excising only Command Solo information? No matter, it is also in my book, M.C. Realities: Understanding, Detecting, and Defeating Electronic Weapons and Methodologies of Political Control Technology.
A plane like no other, an admitted weapon against free-will thought
It’s a specially modified Hercules C-130 called Command Solo, and the U.S.A.F. currently operates a fleet of 7 of them (predecessors, Coronet Solo, entered service as early as 1978). They are based out of the 193rd Special Operations Wing stationed at what used to be Olmstead AFB, now part of the Harrisburg International Airport at Middletown, PA. Costing up to $110M each, they are the ultimate tool in government’s arsenal of Political Control Technology (PCT) used to subvert God’s gift of self determination. Official USAF info, here. Notice my photo is better than theirs.
Assigned to the Air National Guard, they frequently fly training missions over U.S. Soil, and no one who might feel a twinge of guilt, not even the aircrew, knows what messages they beam down to the ground. It’s all a super sophisticated programmed system with nothing but indicators and meters to show how things are operating. See inset picture.
Officially, it ‘intercepts and blocks existing broadcasts and replaces them with whatever information is deemed necessary to achieve mission goals,’ and operates in the ‘AM, FM, and UHF/VHF TV bands employing medium and high frequency, very high frequency, and ultra high frequency.’ The problem with these statements is that they avoid discussing yet two other capabilities, one being subliminal message embedding, and the other being the use of low frequency and extra low frequency, ELF. This is the darker potential of Command Solo:
All such psyops methodology is based on principles of mind control developed by CIA and the DOD, and even research by NASA, many of the same technologies used selectively on Targeted Individuals by operatives on the ground to make them seem Schizophrenic, though victims of that level of mind control also ‘enjoy’ other special PCT treatments as well, to include low-tech methods such as organized stalking, sometimes called dogging, or street theater.
It is not simply conspiracy theory or conjecture. The Air Force has admitted Command Solo’s use of such tech with startling results in sanctioned operations abroad, and further admits they are allowed to use it here in America in certain circumstances. But the problem is, there is no way to police or monitor its use, detect it in use, nor know what the content may be.
How it works

I used official USAF images for annotating as seen. Subsequently, they have been removed from USAF sites, all remaining images with less useful clarity or detail. My image was also deleted from search engine results after being among the first to show in a search.
Overt messaging: The least offensive possible use, whereby simple and direct propaganda is broadcast. The plane can even fly low altitude missions of this type and use loudspeakers capable of overcoming the plane’s engine noise by use of sound canceling technology. But this does not bother me in the least.
Subliminal messaging: The aircraft flies at altitude, loitering in large circles for endless hours, perhaps even employing in-flight refueling to increase time on station. There it picks up citizen broadcast radio and TV signals, and replaces or rebroadcasts them at amplified levels. It can work on select, whole groups, or even all locally available signals. How nice of them to provide improved reception quality for those listeners and viewers lucky enough to be below.
But there is a price to pay for the audience. The broadcast signals contain a few added elements of information embedded within the audio tracks. It is not known to be the case, but it is also presumed additional subliminals could be contained within the video. Subliminals are simple, brief, and repeated messages in a form not consciously discernible by the listener/viewer, but which, by repetition, are perceived and communicated subconsciously.
To my knowledge, the first known use that made the news about visual subliminals was in the motion picture industry when one frame in 24 (one frame every second) would have superimposed upon the image a single word, such as ‘popcorn,’ usually just before the intermission. This could also be achieved by the use of a second projector with all black film save the ‘word’ frames where the word was clear and transmitted white light in superimposition.
Alfred Hitchcock had the word ‘fear’ added directly to the film Psycho just before the scary parts. That was the use which became public, and revealed the fuller use to the public’s dismay, and soon enough sparked laws prohibiting its use altogether. We must suppose such laws are adhered to, as there is no easy way to know, for sure. All TV and film is candidate for suspect, and only frame-by-frame review would prove anything useful.
In audio subliminal messaging, a method known as ‘back tracking’ or ‘back masking’ gets a lot of attention in media, today… where the sound played backwards has a ‘secret message’, usually dark or evil. In some cases, the audio content may mirror the same information both forwards and backwards, such as is claimed for the famous ‘That’s one small step for man…’ moon-walk line, which backwards, says, ‘Man will space walk.’
The subconscious mind is said to ‘hear’ these messages quite well, but the phenomenon tends to happen naturally without engineering. While it is possible to engineer it, and many songs employ it for special effect, in my opinion, employing it for mind control purposes is less useful and less practical than employing a much more common method.
The simpler and earlier known method is to simply embed the message directly into the audio at inaudible levels and at frequencies or pitches sympathetic to the existing audio such that it seems part of the intended content. This method allows complex messages to be absorbed, and is well known as a means of teaching topical information or improving mental performance or even physiological attributes of people while awake or sleep. As long as the user of such content is informed of the existence and nature of subliminals, it is legal. Command Solo employs this later technology, but of course, there is no content warning.
EEG entrainment: There is currently no hard proof Command Solo employs EEG entrainment, though photographs (see image) of the plane reveal design elements which indicate the needed transmitters are installed. I’ve had the example photograph with annotations on line for nearly two decades and to date no one has protested the allegations with technical proofs or basis (or at all, for the matter, save possibly the protest inherent in the hacking thereof, which strangely left the image in tact — through removal of the image would have more quickly revealed the hack had taken place.)
The brain operates at extremely low frequencies (ELF) below 15 cycles per second (15 Hz). EEG (ElectroEncephaloGram) readings at multiple locations on the skull can be used to monitor brain activity by capturing these signals and converting them to printed readouts of squiggly lines for medical review. However, a given type of thought or mood, or even general physiological state (e.g. headaches, nausea, pain) will result in specifically unique EEG patterns as a collective. The EEG squigglies are indeed a de facto brain wave frequency map of such states.
Where such a frequency map is rebroadcast by traditional radio in the same frequencies but at stronger levels than the brain itself generates, the brain will adopt them as its own. This is called entrainment. Command Solo employs what I claim are special ELF transmitters to broadcast such frequency maps to a broad area to impact the thoughts of people below. Like the subliminals, this is presumed to impact anyone within several hundreds, perhaps thousands of square miles, though it must fade in potency as distance from the plane increases.
Therefore, by broadcasting subliminals such as ‘I should surrender if I get the chance…’ along with EEG states of mind such as ‘fear’ and ‘nausea,’ it is possible to perform quite a mind f*** of anyone unfortunate enough to be in the plane’s range of operation.
Follows is are excerpts from an article by Judy Wall, who was publisher of Resonance, a newsletter for members of MENSA (the high-IQ society) who specifically are involved in bioelectromagnetics study or research; a scientific paper. She also wrote investigative material for the magazine, Nexus, an international magazine covering technology as well as social phenomenon and their impact on mental and physical health. From Issue 7, volume 5 of Nexus, we find:
According to the (USAF provided) fact sheet: Missions are flown at maximum altitudes possible to ensure optimum propagation patterns… A typical mission consists of a single ship orbit which is offset from the desired target audience. The targets may be either military or civilian personnel…
In a phone call to the USAF Special Operations Command Public Affairs Office, I questioned the legitimacy of using these subliminal broadcasts against civilian populations. I was told that it was all perfectly legal, having been approved by the U.S. Congress (!) …the Air National Guard of the individual states in the U.S. can also operate Commando Solo aircraft, should the Governor of a state request assistance. That means the PsyOps mind control technology can be directed against U.S. citizens.
…On July 21, 1994, the US Department of Defense proposed that non lethal weapons be used not only against declared enemies, but against anyone engaged in activities that the DOD opposed. That could include almost anybody and anything. Note that the mind control technology is classified under non lethal weapons.
USAF General John Jumper ‘predicts that the military will have the tools to make potential enemies see, hear, and believe things that do not exist’ and that ‘The same idea was contained in a 15 volume study by the USAF Scientific Advisory Board, issued in 1996, on how to maintain US air and space superiority on the battlefields of the 21st century.’
Wall went on to report confirmation that Command Solo was employed in Iraq and specifically to sway Bosnian elections. The U.S.A.F. admitted to her that Command Solo played a significant role in getting Iraqi troops to surrender en mass, even sometimes to model airplanes (UAV – Unmanned Ariel Vehicles), and to sway elections in Bosnia to insure a Coalition approved leader was installed for the purpose of maintaining political control and stability of the region.
Additional thoughts (mine, not theirs)
This technology was first deployed in 1978. What happened in 1978? The World’s first mind control cult mass suicide: 909 persons at Johnstown, a CIA established cult started called The People’s Temple, led by Jim Jones. The cult, located in Guyana, was frequently overflown at surveillance distances by C-130 aircraft.
The significantly upgraded (EEG) version was introduced in 1980. What happened in 1980? Iranians stormed the Russian Embassy in Teheran; 63 religious Zealots seize the Grand Mosque in Mecca and are beheaded; Bani Sadr, the most pro American of candidates is elected as President of the new government in Iran (this is at the time Iran held 6 American hostages); unarmed farmers storm, occupy, and burn the Spanish Embassy in Guatamala, a key event to Democracy being established a few years later.
These events prove nothing concretely, but themes appear with a frequency to cause one to wonder, ‘what if?’
A logical question arises:
How do we know what information is contained in Command Solo when over U.S. soil? The answer is, we don’t. The aircrews do not, either. Nor does Congress, or perhaps even those who should know at the Pentagon. Perhaps only the preparer of the preprogrammed digital tapes used to modify and retransmit knows, and it is conceivable even that person does not know, likely ordering it by a code number which does not reveal content. It may simply be marked ‘Training Use Only.’ But somewhere, someone knows, and they won’t be talking about it honestly if it contains messages to sway our political opinions and social viewpoints, or our votes and other key actions.
Now, does that sound like a democracy in action, or more like a military police state growing its power? You know my answer, best summed up by the wish that the right to bear arms might ought to include Stinger missiles. I’d like to see these aircraft permanently grounded, along with the 30,000 Global Hawk drones they want to fly over U.S. soil to ‘protect us from terrorists.’
WE are the terrorists, because our ability to think for ourselves is threat to the security of the 1% who seek total control; we strike terror into their hearts every time someone like me makes public the truth, and someone like you chooses to read, share, like, and rate (page top) that message. We know this fear to be true for many reasons, as cited in my other posts on related topics.
That’s why its called PCT in the first place, an abomination before God in defiance and subversion of His gift of Free Will and self determination we were promised by the Constitution as ‘the pursuit of happiness.’ Where, exactly, do you live, again?
Buy now, be happy. Trust government, vote for X, and be safe. Spend money, be happy. Believe TV news, fear terrorism. Borrow money, be happy. Fear terrorism, Vote for X, and be safe. Watch TV, be happy. Ban guns, be safe. Buy now, be happy. Trust government, vote for X, and be safe. Spend money, be happy. Believe TV news, fear terrorism. Borrow money, be happy. Fear terrorism, Vote for X, and be safe. Watch TV, be happy. Ban guns, be safe.
Related articles
- Real Scientific Evidence for Subliminal Messaging: A Rising Tide (whatispsychology.biz)
- Timeline of Masonic/Illuminati/Mind Control Evolutions (proparanoid.wordpress.com)
- Can subliminal messages in movies be used to manipulate you? Like in FIGHT CLUB? (businessinsider.com)
In the Rearview Mirror: When You Think You’re Followed
How to know, what to do about it
by H. Michael Sweeney
This is an updated summary review of information (not excerpted) from my book, The Professional Paranoid: How to Fight Back When Investigated, Stalked, Targeted, or Harassed by Any Agency, Organization, or Individual (available in ebook, CDR, and hard copy)
This post is a companion to a post on cell phone security made just hours earlier. Unless you want me to repeat that introduction, you should quick like a bunny hop over to and read it, first, as it sets the stage. I’ll wait right here…
Good. Now that we are on the same page, it seems pretty clear that if a person is being monitored in their phone calls, then there is a good chance they are under what’s called a full surveillance net. That means that in addition to your phones, everything from your mail and computer communications, and your travels away from home, not to mention everything you do in your home, including sex, are likely being monitored.
Only a Police State is paranoid enough to watch people like that… and perhaps voyeurs. One could argue then, I suppose, that sexually repressed people tend to be the ones who apply for and take these kinds of jobs with the intelligence agencies. Take a look at CIA spooks David Ferrie and Clay Shaw of JFK assassination fame, for instance. That may be why TSA has so many perverts groping people. I don’t know. Sorry, couldn’t resist.
Methods of being followed
Watch the Will Smith/Gene Hackman movie, Enemy of the State, and you quickly learn there are all kinds of ways: satellite surveillance, tracking devices, helicopters, cars, on foot, and even by microphone relay and telephone calls (where we left off). Now, with all that sophistication comes an associated cost factor, which tends to favor use of low tech except for the greatest of national security risks or fears. So you, as mere ‘suspect’ in some government imagined conspiracy to blow up your underware because you think for yourself and talk openly in an attempt to get others to use their minds, are more likely to be followed by car or tracking device than the more exotic means available.
Funny thing about tracking devices, though, is there is almost always a car following that signal. You won’t see it, but it’s almost certainly there. The purpose of the device CAN be simply to make and keep a record of your travels for later consideration, but usually, they prefer to be close enough at hand so that once you stop at a location, they can show up and see WHY you stopped… since the satellite isn’t going to be watching for them. So for my purposes, it’s the same as being followed by car.
The only difference is, you won’t see them in the rearview, but like the folks you do find there repeatedly, you will see them at destination if you are alert and can find a good observation post you can use with some useful patience. I’ve even found them there waiting for me. That was a fun story, just part of a five year running war with the paranoids, but I’ll save it for another time, perhaps. But other than them showing up like that, we need another way to know for sure.
How to detect being followed
First, how NOT too, would be more in order. Don’t keep looking for it, and don’t assume a car you see with great frequency is a bad guy. You are by and large a creature of habit taking the same routes to get to any given repeat location at roughly repeat times of day. So is everyone else. So I don’t get nervous because a certain rusty Chevy is within a few cars of me several times a week. Actually, I don’t get nervous even if I do think them following me, because I don’t want it known that I know. So I don’t spend all my time looking up at the mirror. If you insist on that, get a rearview camera ‘so you don’t back up over some kids,’ and glance at that furiously.
Just be aware of cars around you all the time, with NORMAL use of mirrors and glances out windows. Don’t be looking like you are on the lookout. Trust your instincts, and if you ‘feel’ like you are being followed, you may just be. At such times, or when you THINK perhaps a given car is just a little too familiar (or a driver), find something about the vehicle or driver you can identify later, and make a mental note, or a verbal note to a VOX (voice activated) pocket recorder, or a written note to a memo pad, or even a photograph. Note time, place, and descriptor.
The descriptor is going to be whatever thing is easy to recall. It might be a dent or rust spot, an odd paint job, a bumper sticker, or, where nothing else works, the license plate. Now there is a trick to remembering plates (more correctly, making them memorable) that I like to use when part of the sequence is alphabetic. RTU 035 is the plate of a vehicle associated with a CIA operative (more correctly, a retired Marine Forward Observer hired to ‘observe’ me by CIA). I glanced at that plate and forever now can recall it by my memory trick.
Simply make up some nonsense acronym out of the alpha portion and repeat it to yourself a few times while looking at the vehicle, not the plate – you want to associate the plate with the color, make, model, etc., not some rectangular piece of metal that might be replaced at some point. So in my example, I said ‘Rat-Tailed U-boat 035, Rat-Tailed U-boat 035, Rat-Tailed U-boat 035.’ Done deal. Next vehicle, please.
You can do the same with drivers. I enjoyed making up names for them, too: Pug Face (looked like a boxer who didn’t retire soon enough); The Professor (very dignified); The Liddy Man (wore a Liddy mustache and similar hair line; The Cuban (you get the idea). You will often see these people in multiple vehicles over time. It really gets interesting when you see the same groups of people in the same cars others of the group had earlier driven. And above all else, the most important clue… when you see the same people or cars at differing parts of town on the same day… especially if in those groups. Been there, done that.
But I did also employ both audio and paper, and photographs, as situations allowed or required (such as when there is not a lot of time and the situation is fluid). At days end, I would compile these all into a database, and once a week, for those repeat offenders (that’s the important clue), I’d go down to the Department of Motor Vehicles and run the plates to see who owned them.
Can’t do that any more here in Oregon, they made it illegal. Most states won’t allow it unless you are law enforcement. No problem. Lots of friends and relatives in law enforcement. Don’t have any? Make it happen, but you need to become GOOD friends because to help, they risk getting into trouble. It’s very helpful if you are both politically incorrect, at least privately (cops don’t get very vocal about that in public, it tends to cause unemployment).
Benefits and reasons for detection
There are some serious reasons beyond merely confirming suspicions. Example: Amazing thing about the DMV reports was, for me, that more than half the plates were reported either as stolen, non existent, or blocked by law enforcement. Actually, they didn’t tell me the later part, they just said non existent. But all I had to do was lean a bit and read it for myself on their CRT screen. Point is, such reports give you a clue as to who is involved. If you don’t get a lot of stolen/non existing plates, then you are probably dealing with private investigators, corporate goons, or some kind of group of idiot citizens thinking themselves above the law. Else, its government of some kind.
In my book I go into a lot more depth with some intermediate steps designed to better identify your players, and to give yourself tactical advantages. In fact, overall, its one of the larger sections of the book, and its followed by whole sections on offensive and defensive actions that fit into any knowledge gained about who is involved. That’s because, when you know who, you know why, and when you know all that, you know their limitations and what to expect from them when you do X. You start to control events forcing them to react to you instead of you being a mere bug under an unseen microscope subject to their manipulations.
And, it talks about their manipulations, and how to deal with them. They will attempt manipulations, mostly to see your reactions as part of establishing a psychological profile (another reason for cameras in the bedroom, I suppose). So one trick I talk a lot about, is ACT, don’t REACT. Learn to control responses: consider if the situation might be observed and a reaction expected or hoped for, and then decide if you want to confuse their profile by acting differently, or not. Then ACT in the decided upon manner, forcing them to react to YOU (incorrectly react, at that).
The other tactic I discuss at length worth mentioning, here, is that sometimes it is valuable to deliberately blow their tail by letting them know you know they are there, and who they are. They have to report that to their superior and they and/or their vehicle need to be replaced. Very embarrassing and a great chuckle to be had by all. It should cause escalation of methods used to follow you to levels harder to detect, at least by the time you’ve blown two or three tails in a row. Ideally, you do not want to escalate to that point where you can no longer detect the next level, so you would stop using this ploy when you felt that point was near (for most people, that’s going to be the first level, so this will be a moot dialog).
But for others, it has great advantage, because the book tells you how to use that information to better determine just who is following you. For example, at one point I was able to determine it included bounty hunters working with Clackamas County Corrections, and was able to thereby identify the Corrections Officers involved, as well as eventually find the high Sheriff himself (some decades back, of course — the current Sheriff is not a known CIA in-place asset) was involved.
I happened to catch him unaware on video following me on foot near where I worked, and that allowed me to identify him from a coincidentally convenient interview conducted on TV that very week. Subsequently, I openly took pictures of him when he drove past me in a car with Federal plates (neat trick for a County guy, eh?). Never had much trouble with HIM after blowing his invisibility, and in point of fact, after filing a complaint, he ‘retired’ from his elected post. The bounty hunters relocated, too.
The escalation which followed (that was the purpose, recall)? They advanced to use of trucks and vehicles belonging to and driven by employees of an electrical contractor which was later identified as a CIA front operating under 17 names in four States. So that told me my problem was NOT with the Sheriff’s department, but a much bigger fish. The whole story came out well in the end, as I was able to gain enough proofs to force them to stop bothering me, and even to pay me for damages.
Those proofs included not just my own problems with them, but documenting their spying on local government and high tech industry here in the Silicon Forest… letting themselves in wee hours of the morning past high security locks, using flashlights, and presumably, collecting and replacing recorded tapes. It’s all in my book, as well as another book, Fatal Rebirth, which better explains their growing paranoia since 1947 and on into the future. Ever heard of the Unified Conspiracy Theory? Check it out.
Then you will know why I make them so paranoid. Seriously, though; email me if you are having these kinds of issue: proparanoid at century link net.
Your Cell Phone is a Government Agent Spying on You
How to prevent gross violations of your privacy by the Police State
by H. Michael Sweeney
Updated 6/17: two changes in red
Note: This is a complex topic and thus is a lengthy post of a somewhat technical nature, and though it is based on knowledge of the U.S. communications network, most things found here generally apply World Wide. Given the complexity, it will not be useful to undertake reading it unless you have time to devote free of distraction, as it is too important for hit-and-miss reading. It is an updated summary review of information (not excerpted) from my book, The Professional Paranoid: How to Fight Back When Investigated, Stalked, Targeted, or Harassed by Any Agency, Organization, or Individual (available in ebook, CDR, and hard copy)
I’ll start with an inflammatory statement, which I’m fond of doing if it criticizes our errant government. We live in a Corporate Police State. This, I’m arbitrarily defining for the purpose of this article, is a form of government which partners with corporations against the clients of both. As Citizen, you are client to Government (you pay them taxes, they sell you societal infrastructure), and in this case, you are also client to your cell phone service provider. No client should be ever stand for being abused by those with whom they do business; they should stop doing business with them, or find ways to fight back and neutralize the abuse.
The Police State part arises whenever you have a government which applies surveillance and perhaps targeting with Political Control Technology (PCT) of citizens over political issues due to government’s paranoia; they fear the power of individual free thinkers who dare to have and express opinions contrary to their own. And, frankly, they should fear it, because the more Police State-like a government waxes, the more such persons they create, and the more likely such persons will become active in working to replace government. As other posts on my blog site reveal, when governments defeat traditional forms of redress, that could mean outright armed rebellion, if they persist and grow worse over time. Governments get what they create for themselves.
What has your government earned for themselves from you? Acceptance of abuse or defiance and protest against it? Your answer then defines you as being either a common dumb and obedient Sheeple or being someone who is more aware and thus deemed politically incorrect, and therefore liable to being spied upon by government through your cell phone. Here’s how they do it, how to detect it (when possible), and what to do about it.
Threat One: Listening in
A cell phone can be listened in upon by several means with varying degrees of usefulness, and in ways which almost make irrelevant any dialog about warrants, roving, blanket, or otherwise. Dialog on warrants would justify is own blog because as a topic, it is its own area of political spying abuse. So there will only be brief references, here.
While the information below talks about detection methods, most are not detectible usefully. At best, you may need to rely on situational evidence, such as people seeming to know things only possible by having overheard a conversation, or habitually ‘coincidentally’ showing up while you travel. It is all about being alert to your situation and surroundings. That is the price of politically incorrect (in a Police State). Here are the means:
a) If covert access to your phone was possible, it could have been cloned. Not all phones can be easily cloned, and some older phones may resist altogether, depending on who is doing the cloning (their sophistication). That means any use of the phone will be ‘duplicated’ on another phone somewhere as if the user thereof were inside your own head. This cannot be detected by you (assuming the user has set to mute) and, while the phone company could detect it in real time, they don’t try. It cannot be detected after the fact. Anyone using the tech would not likely rely upon a warrant, but it is possible that one could be involved. The technology to clone is hobby grade and above and thus almost anyone can construct the means to clone most phones.
b) Some cell phones have an undocumented diagnostics mode accessed by a keystroke sequence which lets the user hear all cell phone calls going on near to the tower at the moment, in random rotation. Since the number of users at a given instant could be just a handful, that often allows sensitive information to be gleaned, especially if one recognizes a voice. These codes are generally available on the Web, so anyone can use them, and no warrant is required. There is no means to detect its use.
c) The NSA (National Security Agency) worked with the phone industry to develop the modern digital telephone system which includes cellular technology as well as land-line phones. This has become a de facto World standard. The design incorporates command codes sent at ultra high-speed along the network mixed in amongst other call signal data. Phones generally cannot detect these codes (with some exception), but they do respond to them, and that is how they can be manipulated. The range of capabilities (and thus, the threat level) is broad:
1) Calls can be remotely listened to by NSA by computerized systems looking for keywords, in which case the call is escalated (see next). This cannot be detected and NSA routinely listens into almost all call traffic regardless of who the caller or recipient might be. This is under the umbrella of Operation Echelon, one of the earliest paranoiac efforts of the Cold War era intelligence community. Its been going on for decades.
2) Calls can be rerouted to a secondary location for recording and live listen-in capability. This allows thoughtful analysis of call content. This feature can be ‘preset’ so that all calls to or from a given number are recorded, which is exactly how they would choose to target the politically incorrect or a criminal suspect. A warrant is required by the phone company to set it up but anyone who knows the codes can bypass asking the phone company to do it. Virtually the entire military-industrial-intelligence complex knows the codes, and therefore, so do many individuals. It requires special black boxes anyone could build from scratch.
There is a subtle way to detect this form of eavesdropping on inbound calls, but it requires happenstance or deliberate query. If anyone mentions that it took a long time for you to answer the phone but at your end it only rang a few times, the call was rerouted and the caller heard extra rings while the secondary phone system took time to answer, initiate the recording process, and then pass the call along to you. This does not tell you if it is you or the caller who’s the target of the listen in, but you can query on outbound calls as to how many rings they heard at their end, and if calling several numbers at random with consistent results, you have your answer.
Another clue (very rare) can be when a call seems not to hang up and you continue to hear what is going on at the other end. That is a malfunction at the recording site which causes the call not to be released, and the line is held open. It is usually true that the other phone in the conversation was a land line. This brings us to the next threat:
3) The microphone of the phone can be turned on without the need of a phone call being placed or answered. The phone is then a ‘bug’ you carry with you. This can be detected in many cases by paying attention to battery consumption. If your battery life on a charge is normally many hours to days even with general use of the phone, but suddenly it dies or nears death within significantly fewer hours with the same level or less usage, it is being listened in, upon. This happens to me whenever I’ve announced I’m leaving the house, especially if to meet someone. Funny that the battery which normally lasts 2-3 days will crap out in six hours with a fresh charge, but return to the normal performance the following day.
4) I’ll mention as an additional capability less commonly employed is the ability to spoof a destination or point of origin call. You could dial, for instance, the Police to call for help, and someone else could intercept the call and pretend to be Police and sending help. Very useful when their own people are breaking into your home to cause you harm. The reverse is also possible, a call could come in from someone you know but be someone pretending to be calling from that number for some strategic value.
5) The original design did not anticipate the introduction of cameras into the system, but it is widely believed that it has been modified and may therefore allow the camera of the phone to be remotely activated with no means of detection. This has (since the original post) been verified as easy to achieve on all phones other than iPhones, and even iPhones are susceptible to more sophisticated conversions for the purpose.
There is no way to detect these spoofs at the time unless there is a flaw in their verbal dialog which triggers your suspicion and you are able to quickly devise a test question. This function generally relies upon black boxes, again, but are of hobby grade. I’ve received such a call as part of a break-in incident, the proof of it in the after-the-fact means of detecting the spoof, which is that such calls do not show up on the phone bill. That also means, of course, you have no proof for any legal recourse.
d) A more exotic use of the system as a dirty trick is that such systems can play tricks on you with respect to radio shows, where you are a guest speaker. These are often detectible as there will be a call to you just prior to (turns it on), and just after the show (turns it off) which entails an obnoxious squeal of digital codes which are similar to a Fax tone, yet clearly NOT a fax tone. I’ve been hit with this three times, and in each instance the effect was different, as was the tone set employed.
The first time was when I was one of the top three on-line civilian investigators (as media and government would prefer, ‘conspiracy theorist’) who was revealing new information never before known that served as proof of a missile bringing down Flight 800. I was guesting on Coast to Coast with George Noorey. The moment I announced I had this new information and began to speak of it, the show was sabotaged in the entire region of New York and Long Island where Flight 800 went down. It was a hot topic there moreso than elsewhere, because there were so many eye witnesses, not to mention investigators which we would presume government would prefer did not hear something that might redirect their investigation. The sabotage was truly clever; listeners in that area stopped hearing Art Bell’s show, and instead got an old recorded Art Linkletter show, ‘Kids Say the Darndest Things’, as confirmed to me by listeners afterward. As soon as the topic changed back off of Flight 800, the got Art Bell again.
On another show hosted by the late Michael Corbin, the effect was different. Callers were complaining that they could hear the host, but not me. The Engineer confirmed everything was correct, and the prior guest had been heard just fine with no changes in the set up, as was true of the next guest. More interestingly, my voice also did not record and so the show could not be offered on-line via download. An effective censorship. A similar third instance rendered the entire audio dead to listeners. The digital system is very powerful, it seems, especially when other digital equipment such as found at radio stations, is involved.
Threat Two: tracking you by cell phone
Your cell phone is constantly saying to the phone network, more or less, ‘Here I am, anything for me?’ Each cell phone tower nearby relays it to the phone company to find out. If anyone wanted to know your location, all they need do is figure out which tower(s) have your signal. This is supposed to require a warrant, or permission of the phone account owner (i.e., a parent trying to find a child), depending on company policy and service features (some do not allow owner access). But as the ACLU informs us, they often freely give this information out to law enforcement without a warrant. You see TV show cops and the folks at NCIS get at it all the time, as media is trying to train you to think it’s a good thing that should be allowed.
The above is true for all cell phones regardless of age or features, and provides an accuracy of varying usefulness dependant upon the number of towers and other factors. It can be as broad as a 4-6 mile radius, or as narrow as a few hundred feet when circumstances are right. The new GPS equipped phones will rat on you automatically to within about 50-200 feet in most cases. No way to detect any of this, of course, and a phone call does not need to be in progress. It merely needs to be turned on.
Threat Three: EEG functions
Cell phones are based on low wattage microwave signals in a relatively high frequency bands in the range of hundreds of Megaherz (millions of cycles per second) to several Gigaherz (billions). The human brain operates at ELF frequencies below 15 Herz (15 cyles). The difference does not deter those intending the need from using the phone in unique ways against their target.
A cell phone, like any other phone, can be used with voice-stress analysis to detect lies almost as usefully as if an EEG monitor were attached to the user’s head for the purpose. Anyone can buy the gear needed for a few hundred bucks, which lights up when you lie. They can be as small as and made to look like an ordinary deluxe ball-point pen, but are more commonly larger as size tends to relate to accuracy.
But a worst threat exists for Targeted Individuals (TI’s). These are persons who are commonly assaulted daily by a wide-range of Political Control Technology (PCT) in order to render them social, financial, and political zeros, usually by trying to make them seem delusional Schizophrenics. It is a form of mental, and in some cases, actual painful physical torture, as many forms of electronic weapons can be involved. The cell phone can easily become such a weapon.
In addition to all the other potential cell-phone abuses, which will be in constant use on the typical TI, they must worry about EEG manipulation. Signal processing methods used by the kinds of sophisticated agencies or firms (most commonly the intelligence community, military, and their corporat contractors) who employ PCT, can allow a cell phone’s signal to be embedded with a modulated signal in the same range as the brain’s own EEG.
When the phone is placed to the ear, it is close enough that the weak microwave signal with the embedded ELF signal, is still stronger than the normal EEG signal put out by the brain. When the brain is subjected to any signal simulating a given EEG signal that is stronger than its own, it adopts the external signal as its own. This is called ‘entrainment,’ and it is instantaneous.
This technology allows mood manipulation as well as manipulation of select physiological sensations such as feeling fatigued and in need of sleep, nausea, and headaches. Generally, such signals are mixed and alternate between extremes to emotionally and physically exhaust the victim, making them irritable and less than fully functional.
This threat is not normally detectible except by extremely expensive and sophisticated signal analysis by experts using costly special equipment. However, one very alert to how they feel before, during, and after use of a cell phone may detect or have a sense that this kind of abuse is being used against them. The threat also applies to cordless land-line phones, by the way.
Now, while the method is quite workable when the phone is at the ear, it can have a gradual, lessened effect if a few feet away. It is thought, by the way, that the use of an earpiece does not deter the method because the earpiece is also communicating with the phone at Gigaherz levels (Bluetooth).
Note: Another way Targeted Individuals are threatened by cell phones is Mob Flash. The victim’s picture and suggested things to do (called Street Theater) or say if they see them (usually described as a harmless joke associated with a birthday or similar) are sent to everyone in the same cell phone tower’s range. When you see people looking at a cell phone and then doing the same sort of thing, that evidences the practice. I suggest you have fun with them at their own expense and formulate an unexpected nonsense response. Booga booga!
Threat Four: the Software Mod threat
All of the above threats to one degree or another, including remotely activating its camera, can also come from yet another source; software mods to your phone. Even very old cell phones with seemingly no programability can be modded. It can be achieved by covert access to your phone, or by a phone call to the phone using a black box (which tend to show very odd phone numbers as the calling source), or even by a virus attached to a text message. Most phones do, after all, use Microsoft OS, which is quite prone to virus catching.
The obvious exception is iPhone, which wile not susceptible to such virus attacks, can still be modded by the other means. Regardless of the phone, unless a technician, you cannot detect the mod’s presence, and even technicians have doubtful capabilities. The only safe solution is to periodically have your carrier wipe your phone’s memory and download your approved apps and phone lists, etc., fresh.
Threat defenses
For all but the Mod threat, above, simply deny them their signals, and limit the phone’s usefulness as a weapon against you. Most people use the phone for relatively infrequent inbound or outbound calls. Anyone who uses it more frequently should also read up on the threat of cancer, which is so significant, that I refuse to put one to my head, and use speaker phone, only, unless absolute privacy is required, in which case I defer the call to another time and place, if possible. Frankly, the cellular industry is headed toward that time when class action lawsuits threaten to bankrupt them, as happened in the Asbestos and Tobacco industries. It’s exactly that bad.
Therefore, the simple solution is to turn the phone off when not in use. Power it up once in a while to see if you missed a call, and call them back. Your threat of tracking is limited to quite narrow windows of opportunity and tells them at best where you are the time of the call, which does not tell them how you got there or where you will be going next. Some newer phones ignore the power switch for tracking purposes, and it is thought they also allow listen in even when turned off.
This feature is not documented so we can’t say a specific phone is or is not a threat, but you should presume it so if built after 2005, and instead of turning it off, remove the battery. One indicator it may be an issue is if the phone stays lit up briefly after full completion of the power down (where it normally would not), or briefly lights up for no reason at all when not in use (someone has polled the phone with some sort of signal).
There are some who say that phones after 2009 also ignore battery removal. I have no confirmation, but you can also avoid power off and battery removal, as well as this added potential worry by simply placing the phone in a foil wrapper, even if just an empty foil-lined potato chip bag. And, by the way, put your credit cards in there to prevent people from using black boxes to steal your credit by cloning your card’s smart card chip. I use a foil lined oversized phone case to keep everything, including cash, and do not even own a wallet.
Deterring a listen-in threat is a different matter. Obviously, if you are using the phone, it is at risk. If you have a reason to suspect listen-in, it is likely because of a specific topic of sensitivity. Simply arrange in advance with persons with whom you likely need to speak openly about such topics to employ a simple code in conversations. A simple key word or phrase might mean ‘watch what you say,’ and then additional keywords might be translated as key sensitive elements of conversation. For example, you might agree that a given person’s name will simply be ‘Mr. Smith’ when, in fact, its not.
But don’t forget that there are two kinds of things one can say over the phone: things which are true, and things which are not. Thus if you suspect or know your phone is being used against you, try to avoid letting on that you so believe. That will give you the luxury of providing deliberate disinformation to any listening in. I’ll leave the usefulness of that up to your imagination, and suggest only that the person on the phone with you should likely have a means of knowing when you are using the ploy. Again, a keyword or phrase might help.
Where defense against listen-in seems impractical, simply avoid talking in specifics altogether, or offer to call them back later when you can do so from a phone thought more secure, such as a pay phone. Of course, the problem there, is, that government may be looking for your voiceprint with NSA’s help, so that any call you make is listened into. But land lines and topics like that will have to wait for another post… or you could get my book.
Seriously – email me if you have these kinds of issue: proparanoidgroup at gmail com.
Next post in this series: In the Rearview Mirror: When You Think You’re Followed
Testimony to Mass. State Legislature on Bill Restricting Electronic Weapons
Included list of 250 terms and technologies of Political Control Technology
Edited excerpt from book MC Realities: Understanding, Detecting, and Defeating Political Control Technologies
by H.Michael Sweeney, copyright©2006 proparanoidpress, all rights reserved reproduction by request and approval only, to pppbooks at century link netI write to the honorable legislative committees as a friend of the State and of all its citizens, volunteering the material contained herein as an expert witness on electronic weapons, electronic harassment and related technologies of political control. It is hoped that this material will be entered into the public record at your hearings and become useful in your final determinations…
Because of my knowledge on topic after a decade of helping victims of such technology, I must protest at the committee’s choice of language in the bill with respect to the first sentence… referencing control of these weapons only in the hands of the public by means of the phrase ‘no person’. This is to miss the entire purpose and intent of these weapons, and to fail to address the virtually sole possessor and users of the worst of the technology, which is government itself. The public does not need legislation to protect itself from itself, but from its own government. Language must specifically and clearly include government agencies and government personnel of all manner, Federal, State, and local…
In like manner, your definition of weapons is far too simple and narrow to avoid legal confusions. For example, the very same technology which is found in radar guns and FLIR can be used as a weapon of political control or harassment by mere abuse thereof. How will you protect against such abuses? How will anyone be able to determine by the wording of this Bill when the technology and application are legal and appropriate and when they are abusive and invasive?
The victim is not protected if the burden of proof rests on such simplistic language. The abuser, especially if governmentally authorized to access such technologies for normal uses, is not at risk where such loop holes exist. Your language must define and articulate to the complexities of the matter, which are illustrated by the technology reviewed in my (included) materials on topic. Merely adding ‘definitions’ section should address these concerns.
Finally, your legislation makes no provision for detection and enforcement. Can you imagine the local police arresting someone because a neighbor claims to have symptoms of attack? Without a means of detection, there can be no enforcement; all which remains is mere lip service, legislation not to protect the people from the weapons, but to protect the establishment from the people. The primary question is this: Is there anyone in our national or state governments who will stand up for the Constitution, support the Bill of Rights, live by the morally correct principles of humanity and of God, and resist the evil which stares you squarely in the face?
The challenge before your committee and, ultimately, for your entire legislative body, is not only formidable, but it is absolutely pivotal to determining the future of this nation…
Until one empowered sector of our own society, such as yourselves, makes an official protest and stand against this growing draconian onslaught, those things for which our nation stands come closer and closer to being silently crushed within a velvet totalitarian glove. Without such understanding… without laws to protect citizens from the dangers involved… and without any means of enforcing those laws… political control will be assured. The price for such control will be dear. It will be the surrender of that thing godly men call ‘free will’, and which the patriot calls ‘freedom and the pursuit of happiness.’
…May I propose three key concepts or points which should be a part of your deliberations?
1) The first is that any such legislation should be broadened to cover most, if not all non lethal weapons, not just electronic. The very same people who developed electronic weapons were responsible for the development of other non lethal weapons, and for the same unsavory reason: political control. All such weapons further have the same attendant risks to life and liberty and lend themselves to the same abuses and excessive draconian applications.
Perhaps just as important, a review of all such weapons makes the relationship between the weapon, the intended use, and the greater political control strategy which drove its development that much easier to grasp. In support of this notion, my report herein addresses the full spectrum of non lethal weapons, the greater portion of which are, perhaps surprisingly, the more hi-tech electronic variety.
2) The second point I would like to make is that your considerations and final findings must include and provide for public awareness. Only by educating the citizens of the realities of the existence and use of these technologies, can your efforts be well served. If the citizens do not understand the technology and the symptoms it generates, they cannot report the crime or well defend against it. In like manner, your law enforcement, the legal system, media, and the professional communities must also be educated, or the victims will have no place to turn without being labeled as insane.
Of even more value, such promotion and education will, more than any threat of punishments, deter actual use of the technology in the first place. All such technology is currently used in an extremely covert manner. The last thing an attacker using electronic weapons wants, is to be discovered. Such discovery puts not just the mission at risk, but also puts at risk the entire infrastructure of the non lethal weapons industry, and their leadership both in and out of government. Education will, in my opinion, prove to be your best weapon, in the end. But education in and of itself does not provide an adequate deterrence, because unless an attack can be proven, it is merely an accusation which, due to the sophisticated nature of the attack, can too easily be ignored by unconvinced authorities.
3) Therefore, the third and final point, perhaps the most important, is that if you are to have any true success in this matter, you must necessarily include funding for the exotic equipment required to detect and analyze the telltale electromagnetic fields, energy bursts, and radio frequency signatures which are the calling cards of these technologies. In fact, I remind you, it is precisely the output of these detectable indicators which makes this matter one of general concern to the population at large.
The leakage, overshoot, and reflection of these signals, energies, and fields created by these weapons have a great potential for harmful physical, mental and physiological effects on all citizens within a given radius of the intended principle target under attack. The collateral damage to these citizens is not now understood, nor can it be so understood until the actual weapons are captured and tested by independent laboratories. Even the most conservative estimates talk about dire health consequences associated with these weapons. If a particular cell phone can be found by scientists to cause a brain tumor, then what must we face when the signal strengths are many hundreds or even thousands of times stronger, and deliberately designed to cause physiological and mental effects?
If you fund the needed equipment, you will need to further fund appropriate training of technicians on how to use the equipment, as well as in general procedures and skills in the area of covert counterintelligence operations and general law enforcement procedures. This is exactly what will be required in order to be successful against those who use electronic weapons, and no less.
With the above in mind, I would propose the Bill provide for creation of a joint task force of specialists in the areas of law, communications, signal processing, electronics, bioethics, medicine, chemistry, psychology, counterintelligence, military, and law enforcement be created and managed by a carefully picked oversight body. In the absence of creating a new bureaucracy, I would suggest that such responsibility might best belong to any existing state environmental agency as opposed to general law enforcement.
One reason I say this, and it is intended as a general warning concerning the selection of specialist staffing as well, is that I can virtually guarantee that law enforcement of your state and major cities has already been infiltrated by members of the intelligence community, or would immediately so become upon passage of any such legislation. For this reason, the easiest way to assure failure of any mandate against electronic weapons is to simply hand responsibility for it over to law enforcement.
Keep in mind that the more exotic technologies are hardly used for their ultimate intended purposes at this time, but more typically used only in testing on unwitting guinea pigs, citizens at large, generally from among the underclasses, those persons least likely to be able to defend themselves or obtain the expensive helps required. Therefore, most victims are targeted not because of any actual political or intelligence value, but because of the value in learning how the technology works and how to best apply it without getting caught.
Now, regarding testimony from other parties, I might presume and certainly hope that many such victims will stand before you to offer testimony, and I beg of you not only to solicit for such witnesses, but to open your considerations to citizens beyond your state borders, that you may increase your chance at hearing the full truth.
Indeed, open your doors to Canadians, as well, for these weapons do not respect national borders, and are freely exported for testing and use abroad. And for every brave soul who dares stand before you in tortured fear of what will happen to them for their bravery, and an even greater fear of what will happen to them if they do not seek your help, there are likely tens of thousands of others on the continent which cannot or dare not testify. Regarding what they say, may I further advise of three additional points.
Regardless of how wild or bizarre may be the claims found in such testimony, there will be three absolute facts I can promise to be true regarding their claims:
1) among those testifying, you will hear persons who are:
a) legitimate victims of the technology and who are telling you the truth exactly as their ability to grasp and express it allows;
b) persons who are delusional and falsely believe they are victims, telling you of imagined things which have little or no basis in fact; and
c) intelligence community plants pretending to be victims in order to provide you with deliberate disinformation and, largely, to discredit the general value of all such testimony;
2) It will be impossible for you, short of elaborate investigation and expenditures of large sums of money, to make any useful determination of which category a given testimony falls within;
3) in light of the aforementioned difficulties, you should logically come away highly incredulous and doubting of the value of the entire collective of testimony, were it to stand alone.
This phenomenon (3) is a prime example of one of the chief purposes of political control technology, that of destroying the credibility of victims who dare tell others of their experiences. Think upon that, for a moment. Electronic weapons are designed to conceal their own use by making the victim seem incredulous. The testimony you hear will prove that it works exactly as intended. Do not discard the truth encircled by lies.
In light of these facts, I am moved to insure their testimony and my own presentation does not stand alone. I herein provide some meager proofs in the form of a technology review of some 250 terms and technologies of political control. A much more substantial body of such evidence is possible should it be required, which is why I have tried to include more valuable proofs in the form of references which are, by and large, easily obtained and verified.
This includes articles and scientific papers as well as actual patents on the technology itself. Patents are used only when other experts have already connected the technology to the claimed weapon. A reservoir of additional patents which could have been used, except for space and redundancy they represent, are included at report end. But understand that for reasons of national security, many more patents exist which were unavailable.
Also realize patent descriptions need not sound like weapons, partly as a natural result of the patent application process, and partly by design. Too, like many inventions intended for good, some patents having no apparent weapon’s application have been subverted to evil ends by someone who saw the potential…
In point of fact, the great bulk of evidential resources come from military documents, a matter which is deeply troubling to all right-thinking individuals because it paints a picture not of a military set on defending the United States from enemies who would threaten it, but a military which is the threat, itself… By the following materials, may you come to similar conclusions, and may you have the fortitude and resolve to do something about it, which is something we citizens cannot of our own accord achieve short of armed revolution. Please do not leave this the only remaining option for Americans, or that may be exactly what the next generations will need consider…
It was perhaps author Aldus Huxley, who first expressed concerns about political control technology, put into words within the fictional construct of Brave New World and Brave New World Revisited, Orwellian nightmares not unlike 1984. Based on 1958 technology, Huxley projected ahead a mere 40 years to describe exactly the kind of technology and social consequence which lays at the heart of our focus, here.
In point of fact, I hope to illustrate, we are well ahead of his projections. Welcome to the New World Order. Sheep, do not be alarmed at the slaughter of your fellow sheep. As it is for their own good, so will it be for you.
~ Sincerely, H. Michael Sweeney
 Unfortunately, as with all such legislation efforts at both State and Federal levels, the Bill was not passed, nor was it amended to make it more likely to pass. It was simply dropped. Too many powerful people, firms, and groups benefit from Political Control Technology to allow a mere Congressional representative the luxury of a morally correct vote or opinion. The Cogs of government work beneath and behind the visible mechanism of floor debate, and are turned by the steam of the Military-Industrial-Inteligence-Media Complex. What you and I think, need, or desire in the pursuit of freedom and happiness is irrelevant, as is anything as trivial as the Constitution and Bill of Rights.
Unfortunately, as with all such legislation efforts at both State and Federal levels, the Bill was not passed, nor was it amended to make it more likely to pass. It was simply dropped. Too many powerful people, firms, and groups benefit from Political Control Technology to allow a mere Congressional representative the luxury of a morally correct vote or opinion. The Cogs of government work beneath and behind the visible mechanism of floor debate, and are turned by the steam of the Military-Industrial-Inteligence-Media Complex. What you and I think, need, or desire in the pursuit of freedom and happiness is irrelevant, as is anything as trivial as the Constitution and Bill of Rights.
However, in 2004, a variation of the Bill WAS passed. It can be found here. A brief reading will find that not one of my suggestions was incorporated, and in fact, it specifically authorizes government to employ such weapons, the reverse of the need. All it does is makes it illegal for you and me. Like that was ever a threat. Yet the deem this legislation as an ‘Emergency Bill.’ Go figure.
Related articles
- Judy Wall (targetedindividualscanada.wordpress.com)
Timeline of Masonic/Illuminati/Mind Control Evolutions
From the Appendix of MC Realities: Understanding, Detecting, and Defeating Political Control Technologies
a book by H. Michael Sweeney – proparanoidpress.com
copyright©2006, all rights reserved This is an additionally annotated copy. Reproduction rights by request and approval, only
Sorry, there will be no links in the article, as it would take weeks to compile and make it harder to read (hundreds, closely spaced). Images are out, too, as visual formatting would be destroyed. Too bad, there are some really interesting ones.As a research guide, the following references do not always represent direct cause and effect relationships, but (unless otherwise indicated) at least visible relationships and ties. The expression ‘Masonic constructs’ means that various aspects of the organization or their procedures, especially secrecy, follow Masonic structure. When it says ‘formed by Masons,’ it means members, not the cult. A given citation in this list is not concrete proof, but merely a guidepost of where to look for such ties. However, inclusion is based on suitable ties being found by Author for the purpose to so conclude. In some instances, the basis is noted, but space limitations prohibit detail. Nothing contained herein is terribly hard to verify.
NOTE: You will see in review of this why so many people think that it is Jewish Bankers who rule the World, but they were never Jews, but Templars, in my considered opinion (the Rothchildes).
1118-1313 Knights Templar exposed to Assassins, Baphomet , Ritual Sexual/Satanic Abuse;
1313-1600 Pope Discovers Satanism, Disbands Templars, Rosicrucians becomes hiding Place;
1390 Stone Masons Guild (like a Union) socially prominent – NOT an evil group;
1717 Templars convince Stone Masons to accept them as Speculative Masons, establish Visible 33 Degrees – no masonry skills;
1776 Illuminati NWO effort founded by Adam Weishaupt, Satanist Mason;
Late 1700s Rothschilds become International financial banking giants: The Rothschilds (several spellings) were Jews, and they became the ‘basis’ of ‘Jewish Cabal’ accusations. However, my research leaves open the possibility that the y were actually Rosicrucians and former Knights Templar, who deliberately took on the identity of Rosicrucians and then Jews in order to escape detection and death. They became dominant world financiers in the manner of the Knights Templar by having family members establish banks in the capital cities of every European nation (as did Templars). Instead of shipping money from one bank to another and risking highwaymen robberies and international taxes and tariffs from multiple nations, they simply traded letters of credit. They were the first to invent ‘debt’ as capital, and in more modern times, it was the Rothchilds and the Rockefellers, et. al., who invented a similar approach to currency itself, resulting in the Federal Reserve System, which is owned by the bankers, not the government;
1769 -1815 Jacobian Society founded with Illuminati ties, will spur French Revolution, Congress of Vienna;
1825-1830 Unitarianism (Protestants), Mormonism (Masonic construct), Universalists (Masonic construct, first-step toward one-World religion) formed by Masons, League of the Just, a German-French Christian cult formed with simplistic Communist ideology;
1847-1860 Karl Marx develops early Communist dogma, while in influence of Cecile Rhodes and other Masons;
1864-1868 Civil War between the North and South: Rothschilds send Col. T.W. House to advise Lincoln, and dictates North war actions resulting in ‘powder profits’ in Europe and the U.S. while Southern General Albert Pike, Satanist, helps dictate South war actions resulting in ‘powder profits’ in Europe and U.S;
1867 Pike former KKK (Masonic construct), becomes head of Masons, writes Morals and Dogma, the ‘Masonic Bible’ which clearly spells out Satanic underpinnings, and parallels Illuminati plans to establish NWO in many ways, including the division and dilution of Christian Churches and sponsoring of Wars, especially between Muslim, Christian, and Jewish States. Masonry is a subversive group at highest levels;
1870 Pike establishes Illuminized Freemasons, incorporates higher than 33 Degrees, all secret and for dark works. Mason Cecil Rhodes is at Oxford, influenced by Rothschilds and Wartburgs — as inventor of Dynamite, the Civil War made him almost as rich; ‘powder profits.’ Rhodes uses his wealth to fund Rhodes Scholarship in pursuit of the same goals as the Illuminati (One World Government). In this same time frame, the Jehovah’s Witnesses are formed (Masonic constructs) and the Hermetic Order of Golden Dawn (Masonic, Satanic), and the Christian Scientists (Masonic);
1884-1911 EuroAmerican Alliances of Masonic and financial influence form: Rhodes, Rothshilds, Wartburgs, Rockefeller, Carnegie, DuPont, Loeb, Harriman, Bush, JP Morgan, etc. (oft called the RockRoth Alliance);
1913 Federal Reserve Established Foundations Established by RockRoth, American Press Bought by the ‘powder interests;’
1914-1917 WW I, ‘War to end war’ used as platform to promote NWO concepts: Col. E.M. House (Son of T.W. House) sent to advise President Wilson by Wartburg, Rothschilds, impacts war actions for ‘powder profits’ in Europe and U.S. At close of war, RockRoth moves: Council on Foreign Relations (CFR) Established, League of Nations established, Theosophical Society (Masonic cult) established to introduce New Age concepts, including marrying of religious beliefs into one-World religion;
1920-1921 It continues: World Union established, Lucis Trust (Satanic New Age) Pantheism, Humanism. Masons now headed by Alestair Crowley, Satanist. RockRoth interests found Tavistock Institute (U.K.) for ‘Pain studies,’ and ‘invent’ Eugenics; MPD/DID RSA (ritual satanic/sexual abuse methods of original Assassins learned by Knights Templar) mind control research is pursued;
1933 Roosevelt Assassination and U.S. Military Coup attempt by (many members of) RothRock (DuPont, Singer at point, Rockefeller insulated), Rothchild/Wartburg’s Central Bank prints so much money for Germany, inflation sets up need for War. Masonic Satanic Thule Society set up in Germany (Hitler a member) with ‘sister’ cult in U.S. – Skull and Bones. DuPont, JP Morgon, Warburg, Rothchilds help establish Kaiser Wilhelm Institute studies along same lines as Tavistock, under Dr. Mengele, plus Leibensborn Project to breed purebred Arians out of Wedlock. Program would evolve to become the sexual rewards program for exclusive use by SS Officers, who had to pass the strictest of tests for pure Germanic bloodlines. The Oxford Group founded the same year by the same general group of players, and Rhodes, asks Rockefeller to fund Alcoholics Anonymous, father to all twelve-step programs, which are a form of mind control and which provide access to secrets useful for blackmail when power players seek the help (one of the steps is usually to confide secrets, also present in Skull and Bones, et. al.);
1939-1945 WWII: RockRoth brings in E. M. House again. Harriman, Bush, others align with Axis and fund, do business with Nazi partners during war, later convicted of Trading with Enemy. Post war, United Nations Established by RockRoth, Operation Paperclip Imports Nazi Scientists including Mengele;
1947-1948 National Security Act urged by RockRoth threats to create the agencies with their own money if Government did not. CIA, DOD, NSA created, MJ12 Project (mind control), World Council of Churches, Church of Scientology founded (Masonic construct), Bilderbergers first meet, American Committee on a United Europe founded (ACUE), UFOs appear (MJ12, aka Majestic), Psychological Strategy Board (DOD psyops), Liberalization of Church Dogma. The many MK mind control projects following MJ12 spread out over the next two decades;
1950 L. Ron Hubbard gets going (fan of Crowley);
1959-1961 World Constitution & Parliament Association founded (WCPA) Masonic Satanic Ordo Templis Orientis reformed along with Order of Temple of Asarte, First Mass Shootings start taking place now as first-fruits of CIA mind control research – Manchurian Candidate programing, Unitarian Universalist Association formed (first marriage in one-World Religion process), Club of Rome (to establish European Community, ACUE partner);
1966 Church of Satan formed by Mason Anton LaVe, U.S. Army’s Psyops Michael Aquino is founding member;
1970s CIA establishes Cult Awareness Network (CAN), UFO Abductions reported in large numbers (suspected faked by Army to create MC victims through MPD/DID). Michael Aquino involved in pedophilia (McMartin Preschool) and DOD Satansim after doing psyops in Vietnam, works on Revolution in Military Affairs (RMA), Trilateral Commission founded, Operation Pique (radio frequency mind control) launched (precursor to many more, including HAARP);
1983-1988 Johnstown Massacre (CIA MC project) with CAN influence, EEG entrainment Radio Broadcast Same year, The Finders, The Franklin Coverup, Command Solo USAF air-mobile EEG platform, Provisional World Government established (WCPA) via ACUE, World Constitution Written, quietly submitted to individual nations for ratification;
1991-1992 European parliament Founded, Europe United, USSR Falls, EEG system GWEN Operational Same year, Taos/Oregon Hum start to be heard, False Memory Symptom Foundation (MFSM) Founded to deny MC exists… by ex CIA MC Scientists;
1993-1997 MC project Branch Davidians vs. BATF, CAN, US Army Deltas, CIA, Solar Temple Suicide Cult (CIA and BCCI scandal ties, derivative of Order of Rosey Cross — Rosicrucians… bringing us full circle). Shoot Americans Questionnaire, Interfaith Initiative launched – DOD via Michael Acquino at The Presido attempting to organize all religions into one CIA sponsored Church. HAARP goes on line, Heaven’s Gate Suicide Cult dies, RAATs Bioimplants developed by DOD (tested on Islamic students just in time for a rash of suicide Islamic bombers), Scientologists take over CAN (cute – a cult owns a professed cult fighting tool), Verachip ‘Mark of the Beast’ ID tracking implant authorized, RFID chips hit U.S. retail products, Total Information Awareness Office established;
Related articles
- Fundamentalists, the Illuminati, Freemasons, and the UN (leavingfundamentalism.wordpress.com)
- The Mystery Of Illuminati (mysteryworlds.wordpress.com)
- Meet the Ruling Faces of Evil (zengardner.com)
- Politics & NWO – Rothchilds and Rockefellers Merge Financial Empires NWO (disclose.tv)
- The Knights Templar today – who and where are they? (thetemplarknight.com)
- History of the Skull & Crossbones and Poison Symbol (mysafetysign.com)
The Olympics and Political Control Technology; Formula for Control
A Method to Control Athletes as Well as You and Me
by H. Michael Sweeney
A contract Journalist named Terri Hansen recently published an article through Mother Earth Journal the deserves our attention. Titled Intentional Radiofrequency Targeting Affects Olympic Performance, Leaves No Trace, it cites insider information which reveals a serious threat no one has previously suspected. She cites the warning words of wisdom from insider to British military and intelligence community covert electronic weapons development and deployment, retired Physicist Barry Trower — from an interview for ICAACT, the International Center Against Abuse of Covert Technologies.
A former Cold Warrior, Barry has in recent months become quite outspoken about not only the dangers present in weaponized technology of this type, but also, civilian use of non weapon sister technologies, such as cell phones. Learn more about what he has to say along those lines in this transcript of an interview with a South African radio station.
I’m writing here to confirm the validity of this story and to add key detail
As published author with seven books generally on topic and two specifically on topic, it will be easy to do. In fact, in my book, The Professional Paranoid, 2nd Edition (2005 — proparanoidpress), a defensive handbook for targeted individuals, I wrote about a CIA/DOD contractor VSE Corp. which, according to Public Relations material provided by them on line, actually took an unmarked van to a Winter Olympics (in an unspecified year prior to 2001) for testing their newly developed LADS system on Athletes. I quote from their own information, below, which predates 2001, when I first mentioned it in my newsletter.
LADS stands for Life Assessment Detector System and is supposed to be used for finding signs of life in rubble (e.g., collapsed buildings) or locating villains behind walls for the benefit of SWAT or military sharpshooters. It is only one of several ‘see-through-the-wall’ (or other barrier) technologies developed in the last few decades. It is sophisticated enough that it can identify one human from another if needed, provided pre surveillance of the target subject has captured the needed data. This entire project had, since the publishing of my book, apparently gone dark as VSE deemed to remove all references to it from their Web site shortly thereafter. While, perhaps thanks to me, you can find lots of information about LADS from other sources on line, you won’t at their own Web site. Quote on:
LADS consists of a sensor, neural network, and control/ monitor modules. The sensor module is an x- band (10 GHz) microwave transceiver with a nominal output power of 15 mw, operating in the continuous wave (CW) mode. The neural network module device can store many complex patterns such as visual waveforms and speech templates, and can easily compare input patterns to previously “trained” or stored patterns. The control/monitor module provides the L A DS’ instrument controls, such as on-off switches, circuit breakers, and battery condition, as well as motion, heart- beat waveform, pulse strength, and pulse rate displays. End of VSE quote.My book further states; They talk about a test, for instance, at the U.S. Olympics. What sense does that make, you ask? They parked an unmarked van near the Alpine Skiing and Shooting event’s shooting positions, and used LADS on the competitors. The goal was to measure and IDENTIFY each shooter by their own individual biometrics (i.e., EEG, breathing pattern, pulse rate, etc.,) WHILE SHOOTING. Thus they have both individual patterns to allow them to recognize specific shooters, but also, information useful to identify (based on the aggregate or average readings) anyone entering into an aim and shoot situations. In other words, they can tell when someone is about to use a weapon. End of quote from book — but clearly, this means EACH competitor had to have earlier been surveilled by this same technology well in advance of the test. Scary.
But there are things even scarier
In the broader view, I have variously written in my books and newsletters describing over 500 terms relating to Political Control Technology such as LADS, perhaps more than two dozen of which are related to LADS in design, capability, or purpose, at least as offshoots or predecessors, if not outright evolved supersets. The LADS tests at Olympics were harmless enough only because LADS was a ‘sense only’ technology. However, part and parcel of this kind of technology, which might be called ‘remote physical’ capability, which is to say, it senses things about the subject at distance as if hooked up directly to medical test gear… is EEG brainwave monitoring.
Note: for a free sample copy of my newsletter which features 250 such terms, including LADS, email proparanoid at century link net.
The interesting thing about EEG monitoring is that a ‘catalog’ of brainwave patterns can, in LADS-like fashion, be used not only to identify individuals and their specific physiological and mental states in select states of mind and body, or tasks undertaken, but to feed it back to them for instant adaptation, a phenomenon called ‘entrainment.’ All they need to is to rebroadcast the signals back at them at stronger levels than their own body would be able to generate. The human brain instantly entrains to such a signal. Of course, the brain’s state definitely impacts the remaining physiological functions of the body accordingly. Now that’s truly scary!
Such technology is quite frequently found to be in use against politically incorrect citizens, generally to cause yo-yo mood swings, and bounce them back and forth between sleepiness and wakefulness in ways which mimic general torture methods based on sleep deprivation and denial of self. I work with such people as consultant every day (you may also ask for a free Helps Kit if you fear you may be such a victim). If used by one country in an Olympics against foreign competitors, it would be quite simple to ‘throw their game off’ sufficiently to allow an easier victory. It could also be used on one’s own athletes to better insure ‘top game’ performance. It is, sadly, undetectable except by the most sophisticated of TSCM equipment (Techincal Security CounterMeasures), and so doing requires perhaps a million dollars worth of gear and well trained experts, generally costing many tens of thousands of dollars per deployment. Even then, given the covert development of this technology, there is a risk they would mistake it for something less insidious and give a thumb’s up.
This technology is currently down to the size of a cell phone for portability in applications where the subject is within close range, perhaps 50-200 feet or less, and powerful tripod systems can accurately target people where there is line-of-sight capability from many thousands of feet, and even miles away. It is perhaps important to mention that one reason this is so easy to employ is that the signals are highly directional and narrow in beam. Another is that the signals can be so highly matched to the target subject that even when accidentally hitting a bystander, they do not have the same effect. But the most important reason is that, except where the individual has been trained to sense the signals (I train my clients in such methods, where possible), or they are already hypersensitive to radio frequencies, they have no understanding the attacks are taking place. It all seems natural. Unpleasant or unwanted, but natural.
Political Control for the Masses
The real question is not ‘Is this technology being used at the Olympics?’ because it most likely is given the ease of deployment and the tremendous value placed on success in Olympic events by nations and corporations. This equipment is in the hands of almost every industrialized nation on Earth, and not just in government hands. Corporations and perhaps even criminal groups have access at least to older versions. Even technically skilled civilians using information available on line can build devices in this family. That kind of technology in the hands of a major betting parlor would be worth millions, and in in similar ways greatly amplifies the value of advertising dollars for corporate sponsorships.
No, the real question is, ‘Will the Olympic authorities choose to believe there is a Boogyman and do what it takes to defend against them, or not?’
To do so would fly in the face of over half a century of ‘logic’ by authorities of all manner who, when approached by persons targeted with such technology, preferred instead to simply deem them Paranoid or even Schizophrenic, and shove them aside and deny aid with jokes about ‘tin-foil hats.’ Sad, because such hats work, and that’s one reason such joke are so mainstream — to make anyone in need feel and look foolish using them. For any authority, it is far easier to let the Boogyman run free, than admit the possibility of existence. Besides, any public statement of detectible use of such technology would undermine the ‘notion of fair play’ expected in the Games. It is one thing to have rules for athletes to follow and tests to insure they do not abuse drugs for a competitive edge, but quite another to set rules and employ tests for government’s fairness in play.
Yet to do nothing may well eventually lead to the revelation that there is no purpose at all in watching or competing in the Olympics, because the entire affair was nothing short of a puppet show, more a colorful, scripted charade than a sports competition. But that thought brings us to another unpleasant notion. The real value of the Olympics in the first place is its power to distract and control the masses globally, and promote globalist corporate interests. Those of us glued to the TV will not be busy protesting the G-12 or WTO gatherings, or occupying more than our living rooms, closer to a functional zero than a potent 99%.
So what do the globalists care if the Games are on the up and up, or not? Zzzzzap! Score!
Related articles
- Effort to ‘read’ Hawking’s brain (bbc.co.uk)
- How Sci-Fi Becomes Reality – Mental Manipulation (theurbn.com)
- Synthetic Telepathy And The Early Mind Wars (powersthatbeat.wordpress.com)
- Wes Moore ~ Television: Opiate of the Masses (Thanks, C) (shiftfrequency.com)
24 Campaign Planks; H. Michael Sweeney for President of the United States?
No one would, I hope, consider me a serious candidate, and certainly no one mainstream would consider my ‘extreme’ planks as reasonable… though that would show they have no clue as to what true conservative politics are. I am neither left nor right wing, though I have been called both. All I seek is to restore the country to the state it was in before government got so powerful it managed to destroy the country, a kind of political time warp going back some 50 to 100 years. In simpler terms, I’d restore the government of the United States to a Constitutional government as envisioned by our founding fathers. How left- or right-winged is that?
Indeed, all the policies put in place in that time span which have gone awry and led us astray would by those governmentals in power at the time would surely have seemed to be the radical (both to the left and the right) notions in the eyes of the likes of Jefferson, Hamilton, and Franklin, et. al. Our country had run just fine for more than 100 years without such changes, and is now on the verge of extinction because of them. So why not fix it? Because it’s radical?
But that all means is that I’m a a strict Constitutionalist, which also means I am per the current use of the term by media not just a radical extremist, but even a terrorist by some standards, which I take as a badge of honor in the face of the tyranny of an unconstitutional and lawless government. But then, so are you, too, just for reading this, because endless Draconian legislation and the public rhetoric of power brokers desperately seeking to retain status quo must consider you guilty by association. FBI, in fact, now considers ANY contact with ‘extremist or terrorist’ groups as justification for surveillance targeting. I’ve written about that extensively in my books on personal privacy and security.
You have no right to use your mind as you see fit, and are a become part of a growing danger to the status quo (keep it up!). The government spies on everybody, and in their reasonable paranoia (because the angst of the 99% is nothing compared to the disgust felt by the many who did not hit the street out of fear). And it is that; they use fear of terrorism and of government heavy-handedness (Police, TSA, FBI, NSA, CIA, and others, to include even the military, of late) to tighten their grip, and event to get us to spy on each other. Replay of Nazi Germany tit for tat. Got your Brown Shirt and armband handy?
Because those of us who are fed up with the status quo… with the New Boss being the same as the Old Boss (and largely lost to their power-mad tyranny)… fed up with the corruption, the pork, the endless signing of Bills without even reading them (largely lost to their greed-driven treason)… and fed up with the steady march toward a New World Order and a Police State mentality (largely lost to their Globalist Fascism)… will LOVE my planks.
But since I am not running, let’s just say it is for mere entertainment and intellectual exercise that I present my planks… which might be described in a motto, ‘Restore the Republic.’ It would effectively de-centralize the Federal government’s power for all except things which were critical to National viability. What most of the Federal agencies are and their functions can be done better and less expensively, and more gently, by the States, or is best left undone at all. I seek to undo.
Unworkable? Unrealistic? Nieve? Sure. But the best ideals ever adopted by humanity through history started out that way. It was, in point of fact, one such ‘unrealistic’ ideal which drove both the French and US revolutions and their resulting Constitutional structures. Those revolutions were driven by a multitude of nieve ideals, just one of which was stated in mutual paraphrase by both Jefferson and Montesquieu, here.

King John of England signing Magna Carta on June 15, 1215, at Runnymede; coloured wood engraving, 19th century. (Photo credit: Wikipedia)
This, and many other like remarks summed ‘radical notions’ unheard of before the Magna Carta, quite unworkable and unrealistic in face of the virtually unlimited power then held by Kings. But when ideals and goals are lofty enough, idealists everywhere will find a way to make them workable, and make them real, despite any ignorances in the beginning. Stumble along the way as we learn, say I. Far better to stumble going forward up a tough hill than to take easier path; sliding down the slippery slope of despair into the total ruination which seems now so near at hand for our once fair Land.
So you can’t vote for me (write in’s excepted), but you can try to pressure candidates to adopt these planks or some other workable overhaul, and vote for the ones that come closest to meeting your wishes. Right now, for me, that would be Ron Paul, in my opinion. Or you can give up and let the NWO win. Or you can pick up a gun and start a revolution with no guarantees of surviving the effort. There are no other choices, the later two so frightening and yet so near on the horizon by the clues at hand that I pray to God for a miracle to prevent them. I suspect we would agree some kind of an overhaul is in order, so humor me then, please, with an overview of the planks… not presented in any order intending to imply priority. Moreover, they are but a small sampling of wrongs in need of righting…
Plank Number One: Critical Review and Reversal of Presidential Executive Orders
In the first 90 days I would move to review thousands of Executive Orders since Lincoln with an intention of reversal of those which have quietly modified the institution of Government in ways which have proven to be tragic in the long run. For all my love for Lincoln, he started us down the path of ever growing, unchecked Federal power, the bulk of which resides in the Presidency. Some tweaking is in order, it would seem. We don’t know about every E.O., because untold hundreds of them are not for public consumption (which makes me nervous about their purpose and result.) But some of them we do know about, as they tend to make their way into the Federal Register (on line). Here are just a few examples… one of which curiously needs enforcement, rather than revocation.
Revoke EO 7933-A By Franklin D. Roosevelt. It allowed the IRS to investigate the finances of those under suspicion of unamerican activities, a provision in support of the McCarthy witch hunt in the Red Scare. Since it is still in place, even though the House Committee on Unamerican Activities no longer exists, this EO may represent a potential source of political targeting by the IRS against Muslims and the politically incorrect among us by our paranoid government.
Order the enforcement of EO 111110 by John F. Kennedy, which was intended to restore the power of the U.S. government to issue money, and end the ability of the private bank of the Federal Reserve from making loans in the form of Treasury Notes to the U.S. government and charging interest. THIS, is where the National Debt comes from. This EO was never enforced, perhaps because JFK’s assassination rendered it ‘unknown’ in some way, or irrelevant under the helm of Lyndon Johnson. However, it has never been revoked, but was ‘nullified’ by a sneaky E.O. 1208 by Ronald Reagan, which needs to be revoked. Upon such corrections, therefore, a new EO would be appropriate which denies that portion of the National Debt accrued since the signing of 111110 June 4, 1963. It is, by EO 111110, stolen money, ill-gotten gains. Go fish, Globalist bankers.
Revoke EO 6102 by Franklin D. Roosevelt, which prohibits citizens and corporations to ‘hoard’ Gold. Ostensibly to allow the U.S. Government to protect and enhance its own Gold reserves in backing of U.S. Currency, the EO remains non functional given that the U.S. no longer employs the Gold Standard, preferring instead to pay huge sums of interest for printing endless IOUs to the privately held Federal Reserve Bank, which is not a government agency. Revocation would allow free ownership and barter of all forms of Gold and Silver by any citizen or corporation for any purpose. Use it or lose it. Moreover, as President, I would demand a tour and inspection of content at Fort Knox to see if there is actually any gold left there, at all, or if it is now fake to cover a suspected theft.
Revoke EO 12148 by Jimmy Carter (and roughly 15 related E.O.s) which would disband F.E.M.A. A replacement agency which truly represented emergency management and did not represent a potential tool for total power grab and abuse of power as the agency has so faithfully exhibited as its true purpose or limit in ability (next paragraph). I would propose that each STATE have its own local FEMA replacement entity under local State Government oversight cojoined by a centralized Federal oversight body to insure that once activated, the State’s best interests were maintained with respect to cooperation in aid between States and the Federal level. Each State, however, is its own boss as to how and where such aid is delivered internally.
Few people realize how insidiously powerful FEMA becomes in the event of Martial Law or even a simple localized emergency declaration. They will control EVERYTHING including how much food you have on your shelf, if you can travel ANYWHERE (even to work), or if you can buy or possess ANYTHING, and much more. They gain control of all aspects of social life, including your kids, your medical choices, etc. And as seen in the aftermath of Katrina and in the wildfires of Texas, FEMA is NOT our friend, but our mortal enemy. Worse, that State of Emergency is already declared, and has been since 2001, and you will not believe what FEMA’s role is to be should they choose to act on their power. Under Reagan, plans were discussed at the highest levels of government for FEMA to intern blacks in concentration camps. You can bet there is an E.O. somewhere adding Muslims to that list. WTF? Now all those conspiracy theories about FEMA camps don’t seem quite so ‘theory.’
FEMA must die as a NWO Fascist instrument, which means a lot of E.O.s must be revoked.
Revoke EO 13158 by Bill Clinton and EO 13575 by Barack Obama, and others, which transfers large tracts of U.S. wild lands, rural and Agricultural lands to control of the United Nations with loss of sovereignty — no Congressional approval sought. The former to establish 47 ‘biospheres‘ where U.S. citizens have been threatened (by signs, mostly, but at times, by armed military types from unknown units and sometimes speaking foreign languages) with severe punishment for tresspass. Such acts had been reported frequently over the years in the now defunct Spotlight newspaper, with further documented covert military operations and/or Soviet made military hardware storage was taking place at biospheres, ostensibly U.N. related. Yet the U.N. officially states it has no such operations or equipment in the U.S.
The later has (Obama gave up rural/agriculture land) to do with something called Agenda 21 — which essentially sponsors corporate monopolies of the food supply, but which is seen as an extension to the biosphere scheme and heir apparent to Codex Alimentarius, which is its own matter to be undone in another plank. Agenda 21 is also quite related to massive depopulation and eugenics programs which would make Hitler’s attempts to eliminate Jews seem a mere cursing in the wind. Obama is further moving in that same direction in an attempt to turn over all agriculture to control in the U.S. to a few corporations spearheaded by Monsanto. Under Agenda 21, private ownership of land is not be allowed, nor is growing your own food, nor for the matter, growing natural food; all must be genetically modified and/or irradiated.
Plank Two: Force Congress to DO IT’S JOB
E.O.s are SUPPOSED to be reviewed by Congress and approved or denied, becoming de facto law if not denied. Congress has fallen down on the job, and my Plank would include requesting a law forcing Congress to… well, do what it should. It must debate, in closed hearing if necessary, each and every new E.O. and come to a decision within a narrow time line. In like manner, each Congressman MUST read every page of every bill. Only by being fully informed may one debate and decide legislation in a way useful to the nation and its people. And finally, no Bill may be passed which contains buried legislation unrelated to the Title of the Bill, thus ending Pork Barrel and time bombs waiting to be discovered. It it deserves to be law, let it be its OWN law unto itself, alone, or let it be non existent lest it foster ignorance of the law by its buried nature. If there was a way, I’d want the law to read that any Congressman who voted for a Bill which was found by the Supreme Court to trample on the Constitution would be subjected to an immediate recall vote (but that would likely also require State law changes).
Plank Three:
a) End the FED, b) establish a GNP Monetary System where money is c) controlled and printed entirely by the government and d) tied to the nation’s financial health.
Campaign poster showing William McKinley holding U.S. flag and standing on gold coin “sound money”, held up by group of men, in front of ships “commerce” and factories “civilization”. (Photo credit: Wikipedia)
Based on the Gross National Product and the value of labor and goods, it is a bit complex to explain, here. The basic concept is that money supply cannot exceed the GNP (the value of the output of labor and goods). The GNP is to the number of workers a relationship by which the standard of living is evolved. More workers and lower GNP means lower standard of living, and less money minted, as does a constant GNP and more workers. But more workers and more GNP means a fairly stable standard of living, and money supply, while any boost in GNP greater than the increase in workers means a higher standard of living and more money. Interest rates would tend to remain constant or suffer mild fluctuations in all but the most severe of economic swings.
Minimum wage and adjustments thereto for promotions and the like would, in addition to performance merits, be based on a baseline GNP determination, not unlike the way we use a baseline Prime Lending Rate from which all other lending rates are devined. The price of goods would be based on the cost of production which includes the cost of labor, vs. the contribution the goods represent to the GNP. And then, of course, there is the matter of taxes – see next plank.
Plank Four: End the IRS as we know it
No more Federal personal income tax! No more Federal corporate tax! Instead a value added tax in the manufacturing processes. Raw material collection (taxed when sold to processors); raw materials processed (taxed when sold to manufacturers); processed materials made into components (taxed when sold to product manufacturers); products and assembled goods (taxed when sold to distributors/retailers), purchased by resellers to consumers – tax free except by State tax options. States would be encouraged to adopt the same model. The actual tax rate would be quite small, but 100% of all GNP commerce other than services would effectively be taxable and generate sufficient revenue to allow the Cost of Goods sold to cover the tax. Services are NOT taxed, and therefore, all such labor contributes 100% toward the GNP tax free.
Yes, you would pay more at the store for the goods you buy, perhaps offset somewhat by the lack of corporate taxes which are already causing prices to be higher, but you would no longer have 1/3 or more of your income eaten up by separate tax payments and you would have NO REPORTING OR FEDERAL SNOOPING, INDEPENDENT IRS COURT SYSTEM, and NO IRS TO WRITE ITS OWN LAWS, etc. And remember, much of the National Debt has been wiped out in Plank One, so taxes actually go to funding government operations, not to retire a bit of the national debt owed the banks for all that illegally printed money. A huge chunk of tax revenue today (up to 75% of taxes) goes directly to the banks as interest payments.
Plank Five: Make the nation pay for What it Buys When it Buys It
You want to buy a tank, Mr. Army? Want to build a spy satellite, Mr. CIA? Want to build a highway or dam, Mr. Congressman? Use the money you actually have in hand from tax collection, or you can’t have it. Don’t even think about writing legislation you can’t finance from taxes. A balanced budget with ZERO National Debt should be the law of the land. This also means that Social Security funds must be reimbursed and payments updated to reflect where they should have been prior to the looting process (SS is its own plank.)
It does NOT mean that you raise taxes to buy something you can’t afford at the moment. Since taxes are collected DAILY, the Congressional ‘checkbook’ has an income stream against which you may write legislative checks as you need them. Live within your means, Congressmen. Emergency funding for dire circumstance is handled by borrowing from the banks only to the extent that payments are clearly within the ability to pay from the monthly income stream. So I suppose the fat bankers can still sponge a bit off government, but it would in such a case also be to the advantage of government and to the people, where as currently there is only the one winner at the piggy trough.
Plank Six: End the Alphabet Soup Intelligence Agencies
The TSA, DOJ, FBI, DEA, CIA, NSA, DOD, DIA, HSA, etc., etc. represent a top heavy superstructure of spying on Americans that MUST stop. I’d rather completely fire all these people and deal with the aftermath of villains running amuck than put up with the crap I’ve seen first hand as victim of endless COINTEL PRO style targeting (of myself and my clients). This is the number one source of fear of government in America, exactly as it was in the Soviet Union before their revolution.
But that extreme is not required. Cleaning house, redefining goals, and placing checks-and-balance style limitations on them will, in most cases, be a good fix. In some cases, like HSA, NSA, CIA, the housecleaning will be so significant that they may feel like they were done away with, but their root defined core jobs will be left in tact. In other cases, redundancy is found to exist and that can be eliminated, and in yet others, there is simply no just purpose not better served by some other means. This plank would be a literal death warrant for any candidate so proposing, I’ve been repeatedly told. I mean assassination. So what does that tell you when U.S. Citizens fear their government such they believe it would assassinate civilian politicians to preserve status quo?
Plank Seven: Give the Indians Back Their Land

English: United States Department of the Interior advertisment offering ‘Indian Land for Sale’. The man pictured is a Yankton Sioux named Not Afraid Of Pawnee (Photo credit: Wikipedia)
I would offer to the stoic Tribes of American Indians complete responsibility and control of all Federal Lands not used as military reservations. This would end the BLM, Fish and Wildlife, and assorted other agencies, and place forested and wild lands, national parks, and other lands in the care of the people who loved it most, and took far better care of it than have we. Much of the current budgets of these agencies would go to the Indians to fund that management. They would be required, of course, to allow free access to public lands, but empowered to stipulate rules of use to insure the lands were not fouled or abused. They would inherit the resources and manpower of the aforementioned agencies as tools they may freely mold and reshape as they see fit. All treaties would be rewritten to undo prior treacheries as well as could be managed, the new lands being added to their reservations under joint ownership, but useful to their communities to include relocation and new settlements. I would not intend Casinos or industrialization of the type now all too easily approved on these lands, or other uses not now allowed, but all other good use to the Tribes would be their right.
Plank Eight: End Corporate Personhood As it Exists Today
Not quite an ending… but I’d move to make corporations more like real people. For one thing, that means they have a life time to live, and a means of producing children to survive them. At the end of their life, their children (spin off corporations) carry on the same family name, clients, products and services. Like real people, they also must be held accountable for their actions with real impact to the corporation as well as its Boards and Officers, and in a manner consistent with the same acts if committed by a real human. Toward the end of longevity (say 100 years), a corporation would split into one or more sub corporations (children), which would give all employees who ever worked for the corporation, even if just for one month, a pro rated share equal to their contribution in labor to be credited toward stock OPTIONS at the prior value of the original firm when they were FIRST hired. Over time, ownership falls more and more to employees and less and less to moguls and block stock investors.
By such a scheme retirement programs might be eliminated, providing a nest egg for retirees without increasing corporate obligations over time, and the ‘children’ would gain fresh funding for a growth spurt during their formative years. I would seek controls of Boards of Directors which prevent the same men from sitting on multiple Boards in a manner which puts too much control of a sector into too few hands. I would end the revolving door; seeking a ten-year waiting period for government personnel before allowing them to work for firms in any sector in which they held a position of related service in government, and in like manner disallow any member of an industry to serve as more than advisor to government, certainly not as administrator in any government oversight of that industry’s affairs. To be hired by a firm as a former government employee, and vice versa, should be based on expertise born of their experience and not clout and pull still in place with staffs remaining in recently vacated offices. Period!
Plank Nine: Establish a Free Press and Transparency in Government
Currently there exists a kind of de facto partnership in America (and a mirror situation in other ‘free’ countries) between the Military, Industrial, Intelligence, and Media sectors… forming MIIM, the Military-Industrial-Intelligence-Media complex. Media is controlled by a small handful of individuals who are largely in bed with the other sectors. At one time (at the time of the friendly fire shoot-down of flight 800), all three major television networks were outright subsidiaries of military contractors, which is why they fired any reporter who said anything on air about friendly fire.
Currently, there still remains employed within media, which includes the entertainment and advertising sectors, thousands, if not tens of thousands, of CIA and other agency personnel, to include military proponents serving as mouthpieces for the very undue influence President Eisenhower warned of when he left office (listen carefully to his Farewell Address video and you will see that he warned us about almost everything these planks address). This was a direct outgrowth of CIA Operation Mockingbird, and only the tip of the current iceberg.
If a means of insuring that ownership has no impact on editorial and reporting departments cannot be easily found, I’d just as soon provide equal funding to alternative underground news sources. All employees who were government shills would need to resign or face charges of treason if uncovered after the fact, because disinformation is treasonous in any government of the people, by the people, and for the people. Thus media must have good access to government, and government must be frank with media. While national security can make it important not to reveal the full truth of a given matter, lies should never be national policy, at home, or abroad. Even an enemy MUST know we are truthful that they not misread our intentions, and we should never betray a friend by a lie, especially our best friends, our very own citizens.
Plank Ten: End Foreign Aid and Foreign Policy as We Know It

National Security Action Memorandum No. 6 Plan of Reorganization of the Foreign Aid Program – NARA – 193406 (Photo credit: Wikipedia)
Foreign Policy and any resulting aid should be about helping those in time of great need. It should be about bolstering defenses of weaker nations against predator nations. It should be about encouraging free Republics and free enterprise (not Democracy, and not capitalism or free trade – there are significant differences). It should be about bootstrapping struggling nations that they might become financial and social partners in World building (not New World Order building). It should be about assuring health and wellbeing of human kind ((not the wellbeing of the big pharma firms), and done regardless of race or political creed.
It should not be about politics, fat military contracts, or quid quo pro deals for fat cats. Israel is a strong, wealthy, proud, and fully independent nation. Mutual defense agreements, yes. Arms sales at competitive prices, yes. But the billions must stop flowing to them and other nations as a means of buying loyalties, funding MIIM, and aiding the march of the NWO. You don’t buy friends and good neighbors, you build good neighbor relationships and cement friendship by actions, by standing by them in a time of need, and by being fair. You don’t take food out of your own children’s mouth and give it to the neighbors when they have their own.
Plank Eleven: Fix Health Care and Confront Pharma
Step one is to forbid Pharma to advertise to the public. Doctors, perhaps, via medical journals. This will lower prescription prices. Step two is to forbid insurance companies from forcing deductibles or co-pay minimums at term start, which effectively eliminates the poor from getting health care even when they have insurance. I myself have insurance which I and my children cannot use for this cause. Step three is to stop the fat-cat billing schemes inherent in Medicaid and Medicare which allow hospitals and doctors to rake in tons of money for outrageous charges and unnecessary procedures. These need to be replaced with a monitoring system that rewards discovery of overcharges and excessive billing.
In my own extended family I can cite countless thousands of dollars in endless examples both at private practice and hospital levels. Step four is to establish government oversight, which will never work unless the FDA and CDC is eliminated and replaced with a body that protects the people rather than the corporations. Step five is to FULLY investigate the origins of HIV, Avian, and other man made virus,’ including Cancer, and to ALLOW alternative medicine cures to be explored.
Step six (step one, really) is to shred Codex Alimentarius, Agenda 21, and related NWO efforts. GMO crops should be illegal unless passing stringent tests by outside agencies. Currently, it seems, no GMO crop could pass such a test and represent a greater long-term health threat than the Black Plague. A Congressional investigation of Monsanto actions is in order.
Plank Twelve: Fix Agriculture and Immigration
Step one is to make it illegal for any firm to control more than 15% (or some number which assures competition still thrives) of a food supply or aspect of production and distribution — no monopolies such as enabled by GMO and Agenda 21. Step two is to enforce current labor laws against employers instead of focusing only on illegal workers, which would tend to make illegal migrant emigrants less of a an issue. Step three is to naturalize all current illegal aliens who can pass minimum tests for language, non criminality, and health, and simultaneously truly seal the borders and evict all who do not pass the standards. Step three is to allow conditional work visas for would-be emigrant migrant workers based on a system of work demand vs. worker supply such that if non emigrants will take the jobs, they may more easily do so without competition from illegals. Step five is to stop teaching mainstream courses in multiple languages in our schools. You must know English to go to school, where if you wish to learn a second language as its own course, you may do so. So if you want to be a migrant worker crossing the border, learn English first or leave your kids behind.
Plank Thirteen: Stop the RFID Technology Threat
If you do not understand the nature and threat which Radio Frequency Identification Devices represent to your personal liberty, then you have not read my books or been paying good attention to the Web. I suggest you can ‘catch up’ by listening to my Webinar interview with Republic Magazine… about 32 minutes into the interview. The one simple way to stop RFID as a threat is to simply require them to be removable or destroyed at point of purchase, and that all such product be prominently labeled.
Plank Fourteen: Stop Canamex COLD, Kill NAFTA/CAFTA and Job Exportation
This is a broad topic beyond the scope of usefulness in this (already too-long) an article. I would simply repeal or renegotiate the agreements in place and write Canamex out of existence. See my blog post on Lion Dance, or request my free newsletter on Canamex for an eye opening explanation of why this is a critical step; email proparanoid at comcast net.
Plank Fifteen: End the Drug War and decriminalize illicit drugs, empty the prisons.
America, with a population on par with Europe, has a half million people behind bars for drug related matters, more prisoners per capita in this one category than most other nations have for all crimes combined. It is a fake drug war prosecuted by a CIA front agency (the DEA was founded by top CIA operatives) as a tool to protect illicit drug sales by sanctioned CIA conduits. It forces the price (and profits) artificially high, and fosters a prison-based economy to the delight of corporate greedsters. Take away the criminality and replace it with treatment, and it will cost our economy one tenth as much, boost GNP, and make it less profitable for Cartels and CIA alike. Pushers stay in jail, users walk.
Plank Sixteen: Fix Voting and Census
The Census is very critical to certain functions of government, including Districting for voter representation and the voting process. But the Census can be done in a way which is not invasive and a violation of privacy, and is kinder to those less disposed to cooperate. The solution is similar to a solution I have in mind for fixing the less-than-trustworthy voting system. These solutions are too complex to fit a paragraph or two, but essentially decouple raw information from the identity of the individual after a simple verification process, which is to say, that in the passing of information, identity verification simultaneously dissociates the information with the individual. Additionally, a verification process facilitates the individual’s ability to verify their vote or census material was correctly tallied and attributed as intended, all the way up the ladder to the final tally. The general method may be loosely described as being similar to certain email encryption schemes involving keys in possession of both the sender and the recipient.
Plank Seventeen: Get at and Expose the Truth
JFK, RFK, MLK, Peltier, Riconosciuto, Christic Institute’s Secret Team, Mena, OKC, Waco, S&L, CIA/DOD mind control, MJ-12 and UFOs, and above all, 9-11 and the Derivatives Scam. Conspiracy theories, my a**. If the official facts are in conflict with themselves and defy reality and/or logic, but are accepted and tendered as truth, that is a kind of proof of a cover up, and any time you have a cover up, it is automatically a conspiracy as a matter of fact. It therefore justifies further investigation by independent and unbiased participants. Truthers will out.
Plank Eighteen: End Globalist Traitor Domination of Government(s)
You cannot be a patriot and serve fellow citizens in office if your true allegiance is to a Globalist agenda which would seek the end of national sovereignty. An oath of political office should include declaration of non alliance, affiliation, membership, or sympathy for the goals of Globalist organizations such as the Bilderbergers, Tri-Lateral Commission, Council on Foreign Relations, Skull and Bones, and the like. To violate the oath would make one subject to prosecution and imprisonment.
Plank Nineteen: Kill the Military-Industrial-Intelligence-Media Complex
While this has already been addressed in part above, I would additionally want every black operation and military and intelligence project currently in works or previously undertaken reviewed. Where such operations were deemed either in support of a New World Order or in support of MIIM profiteering or power grabs, all persons associated with it at management level would be subject to investigation and possible prosecution for treason.
Plank Twenty: Fix Social Security
This is easy to do. As we see in planks 3 and 4, funding SS as it was intended will be quite doable, with additional help by easing of government costs resulting from many of the other planks. Further, plank 8 gives employees of corporations a built-in retirement program vastly superior to SS, and thus SS obligations now active would be come locked in or ‘grandfathered,’ but it would become a voluntary program at each new employment opportunity. Further, I would enforce the law regarding SS numbers and force the elimination of all electronic data and forms outside of the Social Security Office of said numbers. It has no place in credit reports and other records.
Plank Twenty One: Explore an alternative to Daylight Savings Time; Social Time
Our highways are clogged, unemployment is high, classrooms are crowded, stress is high. A long list of such social complaints can be offered. I propose a review of what I call Social Time, presented here in oversimplified explanation; a work day definition is cut to seven and a half hours paid, plus another hour for lunch and breaks, but the bulk of social infrastructure both private and governmental would be expanded from ‘a day’s work’ to a full 24 hour work cycle. That would mean, with broad participation (voluntary for the most part), that businesses and agencies would be open at all hours, which would dramatically reduce volume of client traffic at any given hour and spread it out somewhat evenly over the whole clock.
This would allow some reduction in manpower needs on an hourly basis, yet often provide new jobs to support the extra hours. As time progresses, the work day for an individual would start 90 minutes later each day, thus revolving everyone through all twenty-four hours over the space of just under a month — 14 times a year. We would not need to build more schools to reduce classroom crowding, or more transportation systems to handle population growth, etc. GNP and employment could only benefit, and make the country more competitive. Part and parcel of this idea is to END PART TIME EMPLOYMENT loopholes for employers who don’t want to offer benefits. EVERYONE GETS BENEFITS, but under the various planks outlined above, the cost to employers for benefits will decrease.
Plank Twenty Two: Establish True Redress and an Initiative Process
Whistleblowing shall not be punished. Lawsuits against government for violation of rights or constitutional violations shall be funded by government. In balance, should government win the case, the costs will fall back to the plaintiff. Any citizen can propose a law for consideration in a process similar to that found in several states, such as Oregon. If such proposed law meets constitutional tests, is written to legal requirements, well defined and stated, and can earn popular support (signatures of citizens who so support), it can be sent to Congress for debate and possible passage. In Oregon, the law goes to the ballot for vote by the people, as does all legislation proposed by State legislators. See next Plank on how this might play at a national level.
Plank Twenty Three: Review of possible Constitutional Change from Republic to Advocated Democracy
Especially where initiative process (prior plank) is in play, the use of the Internet could allow, with careful creation of safeguards as also addressed in earlier planks, a way to allow the people to vote on Bills rather than Congressmen. This would be an Advocated Democracy, where elected Representatives (the Republic style) would instead merely propose or debate initiative proposed laws. This would be broadcast and each citizen would then decide to vote for or against the legislation. No more pork barrel, no more bribed Senators, no more fat cats, no more buried language, no more end-run legislation. Just pure simple will of the people.
Plank Twenty Four: End Non Consensual Testing on unwitting subjects, and use of Political Control Technology (PCT)
Last but perhaps foremost in terms of being close to my heart. While current laws prohibit non consensual testing or use of weapons, drugs, and procedures on citizens, there are far too many loopholes which allow it to take place. In my books I cite countless examples, and as consultant I work with victims of it every day. Worse, the very agencies established for the purpose or which otherwise have authority to enforce such laws, are compromised by intent or by lack of training and resources, not to mention handicapped by their very belief structures. It is a sin that Police, for instance, automatically presume one crazy for hearing voices in their head when it is a known fact that CIA and Department of Defense has spend billions to develop technology which allows anyone to be targeted with such experiences, generally with the express purpose of discrediting the target by making them seem mentally imbalanced.
I’ve already proposed language for laws which properly address this topic, and submitted them in written testimony to the Massachusetts State Legislator when they were considering such a Bill. Currently, the military and CIA are developing new PCT faster than we can learn of it, generally under the guise of antiterrorism and funded through Homeland Security. It is a joke to presume that any of this technology can in any way prevent terrorism. It can only enable political control of the population, and nothing more.
Related articles
- The Best: Tracking You and Your Family Just Got a Whole Lot Easier (whiskeyandgunpowder.com)
- How Roosevelt Sold Us to the Higher Bidder: the Federal Reserve (myvoice2012.wordpress.com)
Templehof Secrets Reveal Political Control Technology
Templehof Secrets
Reveal Political Control Technology
by H. Michael Sweeney,
copyright © 2011, ProparanoidPress, all rights reserved permissions to reproduce available on request to pppbooks at comcast (net) Dateline Portland, OR Sept 23, 2011What is Templehof?
Some Facebook friends sent me a URL on an ongoing investigation they were involved in regarding the Templehof Airport, in Berlin. It is written in German but I’ve translated it for you, here. Templehof was the Cold War era airport used to combat the blockade of Berlin by Kruschev with an unprecedented (vid) continuous 24/7/365 airlift of food, medicine, and goods needed to keep the city alive and functioning. The airport, rebuilt by the Germans in the 1930s, was remodeled again in the Cold War years by the Americans, and that has become the source of a mystery involving Political Control Technology secrets… and more.
Though the runway portion is rather small and, like many, a simple slim rectangle… for some reason, the airport features a mammoth oval perimeter and a completely atypical and massive arcuate terminal building which, even in busy times, was more than needed. Not at all now that the airport is closed and ‘abandoned.’ Abandoned is an odd description given the high security perimeter fencing and human guard network surrounding the periphery of this airport, years after any military presence. This has raised the curiosity level of investigative authors Grazyna Fosar and Franz Bludorf.
Templehof Political Control Technology
Chasing after mysteries at Templehof

Templehof from 1923 to mid 1930s
They wondered why so many people in the shadow of the airport have, over the last several decades, come down with the same unique and serious health problems, with new cases continuing to come from the area. We are talking about health problems associated with bombardment by RF energies of a type common to Political Control Technology. That is, psychotronic weapons known to have been employed during the late Cold War by both sides, and subsequently developed for portable use against individuals as well as groups on an ‘as needed basis.’ Other symptoms of such technology in play also exists at the site; a low frequency hum which seems to have no location or source, heard only by humans and not by recording machines. Ah, but they can be recorded as radio signals… traced to the closed base. Imagine that.

Templehof radar, underground loop and Yagi lookdown path (white line)
Their investigation revealed the existence of a large underground loop antenna for transmission of the ELF (Extremely Low Frequency) signals involved… frequencies which match the human brain’s own EEG signals. It is already proven that if you broadcast an EEG signal as a radio wave at energy levels greater than those of the mind, a human in the radio beam’s path will automatically adopt (be entrained to) those signals as if their own; remote mood control. All this is the stuff about which I write in my book, MC Realities (proparanoidpress.com).
My own research has included HAARP and an endless number of similar or related facilities World Wide as well as how they seemed tied to a phenomenon called the Norway Spiral seen and videoed in the skies by thousands of people. This strange event was said by some to be related to Project Bluebeam, a conspiracy intending, it is claimed, to fake the second coming of Christ in order to facilitate seating of the Antichrist. It’s a conspiracy pinned on the modern-day Illuminati, which is another way of saying Knights Templar.
Such spirals have actually been seen in three locations around the World (yellow ‘targets’ in the 1st image, above), but Norway was the one that got all the publicity. All bear a set of unique properties and relationships associated with the HAARP-like facilities, and it was my study of these relationships which revealed that a World-wide network of HAARPish sites exist in a way such that if Bluebeam is a real planned event… there is nowhere on Earth they can’t make you see whatever they want you to see. To underscore, more recently, crosses are appearing in the sky (vid1, vid2), and other apparitions which defy logic, such as two Suns (vid1, vid2, vid3), and giant jellyfish creatures (vid1, vid2). But I digress, and these prove nothing but that debunking is getting harder. And do watch out, there are a lot of debunkable things out there.
Templehof Political Control Technology
Templehof, playground of the Knights Templar
Looking at the Templehof matter, the first thing I find of interest is its history. Temple means ‘temple,’ which is also what Templar means (of the Temple) and hof means ‘court’ or ‘palace.’ Templehof was in the centuries before Hitler a home to the Knights Templar, until Friday the 13th, 1307 when the Pope and the Crown Heads of Europe began to hunt them down for crimes not at all proper for the Pope’s own (hint: Satanism). This may be one reason why Hitler, as occultist supreme, elected to make it a key military base and frequently held massive ceremonies there. In my research, I attempt to show links between the Knights Templar and the Illuminati, the dark Satanic cult which sought the establishment of the New World Order, a one-World government ruled by the Antichrist. They coined the word, and they laid out the plan still seen in force today in the New World Order movement, all detailed in my book.
Templar treasure has always been of mythical proportions, but based in truth. They held more wealth than the Crowned Heads, and were generally the money lenders of their day. It is reasonable to assume that as a Templar Hof, there would have been tunnels and secret underground chambers. Thanks to excellent accounts, we know that there were massive, multi-level tunnels beneath Templehof Airport at the end of WWII which had likely been constructed prior to the War or during, perhaps enlarged from ancient digs.
They were so extensive that they ran to distant parts of the airfield as well as the local Police station. When the U.S. took control, a security lid was put on Templehof and the tunnels. Any upgrades for installation of electronics were likely undertaken in the mid 1950’s when the U.S. discovered that Soviets were beaming electronic weapons at our embassies, and we officially but secretly entered into a psychotronic weapons race, as detailed in my book.
Templehof Political Control Technology
Radar synonymous with HAARP and Political Control Technology

Early DEW Line 1st alert radar installation
But the second thing that I noticed was technical, catching my eye for several reasons associated with my earlier study of HAARP-like sites. The unusual terminal shape reminded me of a particular complex located in China in several details. Both form an arc-like structure which could be employed as a giant radar dish, similar to those of the DEW Line and Soviet counterparts during the Cold War era, albeit enclosed in concrete and glass, and not perhaps as tall… both being much, much wider, and both with a more pronounced degree of arc. Understand that all HAARP-like facilities employ multiple forms of radar systems along with their ELF and VLF radio antenna arrays. At Templehof, it would have been relatively easy to incorporate structural elements of a radar ‘wall’ (image left) as part of the existing facade.
But that does not mean it was used as a conventional radar system. Such would blast the planes and workers at the airport with intense and dangerous radar waves. But it could easily be a receiver designed to amplify the traditional radar systems present. If one draws a line (thin white line in my image) bisecting the center of the Templehof arc and plots it on Google Earth, it can be extended to see the ‘line of sight’ such a dish might have. Extension reveals a precise bisect within a few degrees of arc with the Cold War military airfields at Prerov in Czech Republic, Cheshnegirovo in Bulgaria, and Neisse Malxetal in Soviet occupied Germany. If one widens the arc additional military fields would be inclusive. Further, there were undoubtedly many mobile and fixed missile launch points within the same zones. Such a viewing angle represents an overlook of what might be described as the ‘front line’ of Soviet offensive launch capabilities against European targets. Prerov faces Italy. Cheshnegirovo for France, and the German bases are closest to Great Britain.
The similar radar structure located in China, on the other hand, is aimed at Australia. In its lookdown path we find several HAARP-like arrays in Australia including the American operated HOLT system for communicating with submarines, a site which, by the way, incorporates ‘sacred geometry’ favored by the Templars and Illuminati (the two groups are related). Thus the Chinese site seems to be a listening post of sorts, but the construct is quite similar to Templehof, and HAARPish elements are nearby.
Embedded within an underground portion at the site, I believe, there is the functional equivalent of a giant Yagi style di-pole antenna which serves to amplify signals within a focused narrow aim. There are visual clues that a huge buried Yagi exists both in China as well as Templehof. And we will find them elsewhere, too…

Yagi highly focused x'mit or receive antenna
Thus in my opinion, if investigators were to go back to Templehof, they might find evidence of an underground placement of a Yagi system running all the way to the Viktoriapark monument, which is likely the actual base of any such antenna element. The distance of any Yagi at Templehof would seem shorter than found in China, but the Chinese system, located at 40∞30’37.90″ N 93∞14’12.03″ E is not as large. I propose the smaller Chinese radar profile requires a longer Yagi to compensate. While this can easily be deemed nothing more than conjecture, I remain confident in the principles applied.
Templehof Political Control Technology
How Deep is the Rabbit Hole?
I have an extensive Google Earth.kmz file available which plots all known HAARP-like facilities World Wide (their number is far more than anyone has suspected). An example at page top comes from my YouTube videos on the Norway Spiral — I suggest you start with part 4 if wishing to review. The .kmz may be useful to anyone wishing to conduct further research or cross check my investigative effort. Among that dataset are two sites in the U.S. which relate in their own way to both Templehof and the symptoms shared by victims of electronic PCT in various parts of the World. In terms many Americans might understand, I speak not just of the health issues, but of an additional symptom known as the Taos Hum (and there is the Oregon Hum, etc., etc., etc., a list dozens of places long and World wide), long a mystery thought to be a government mind control conspiracy. Indeed…
One of the unusual sites is in Huachuca, N.M. There a particular Radar is associated with a very unusual HAARP-like array (below). It also exhibits evidence of an underground loop such as found in Templehof as well as of five underground Yagi (faint thin whit lines locate them for you, image right) arranged in parallel and aligned in the same direction, one of which is longer than the others and appears more recently buried.
Moreover, the alignment of these is also in alignment with the actual array, which unlike all prior arrays, seems to involve enclosed antenna structures laid out in a repeating geometric pattern with diminishing dimensions (see image). This, too, achieves a bit of a Yagi type of directional amplification, as I understand it. It establishes a wave guide, or sorts, with a building intensity as the signal is emited… in one direction.
While the direction of aim of the array and the Yagi are the same and generally toward Taos, N.M., it does not provide a precise ‘hit.’ That’s O.K., because it does hit in the desert area near TAOS where the hum is most often reported. But that is not all. There is in Colorado a second HAARP-like system at Plateville with radar dishes of its own, and they have a fixed angular focus which, according to official information (image) overlaps the Huachuca signal at only one place… the Desert area near Taos. There is no apparent evidence of a possible Yagi or Loop, but that does not mean they do not exist.
With that discovery, I rest my case that,
a) Templehof, China, and Huachuca, likely with aid from Plateville, all do much the same thing, which is;
b) x’mit Political Control Technology signals, and/or;
c) watch or listen in on potential foe activity; and
d) employ a combination of underground loops and Yagi systems with above ground radar and (often) HAARP-like ELF/VLF arrays; and
e) the entire history of Templehof, the NWO movement, and Political Control Technology share one prime motivating factor… the Templars; and of
f) The Military
But by no means does that prove a conspiracy… and in fact there are no doubt some actual useful purposes not associated with PCT for sites such as Plateville. But that kind of alternative use, be it a cover story or genuine, is NOT why it does not prove a conspiracy. No. It is because no matter how hard you try, no one is going to believe in the boogyman until they personally fall victim. For you, not today, I hope. Me? Been there, done that. Indeed, I believe.
REPOST/UPDATE Free Speech Requires FBI/CIA/Police Approval
THIS POST CENSORED BY GOVERNMENT
Journalistic Free Speech Requires FBI/CIA/Police Approval
by H. Michael Sweeney copyright lifted, permission to reproduce granted if reproduced in full and citing proparanoid.wordpress.com with link to sameJournalism as intended by those who invented it is almost extinct
As it is for Journalism, so it is for Free Speech, Truth, and thereby, Freedom.
Original post August 17, 2011, Updated July 21, 2012
free speechREASON FOR UPDATE: Government Renews Attacks on INDYMEDIA (updates flagged red)
What follows is an origial short article from the ProParanoid Newsletter written in the Spring of 2004, entitled CIA and FBI Targets Media Group. It deserves follow up and expansion, because the targeting of independent media continues, today. The article has been reformatted to allow a chronological presentation.
While this article is largely focusing in Indymedia to make its point, it is imperative that it be understood that virtually all non mainstream media is being targeted. Julian Assange’s targeting with bogus ‘sex crime’ charges arranged for by paid CIA female operatives as a way of punishing him for his Wikileaks exposure of government crimes is probably a more well known example, but the goal here, is to show a growing pattern of systemic assaults on freedom of speech… when not from sanctioned (sanitized) sources. And, as we will see, even they can get into trouble.
Now, the reason for update is related to several new assaults on the truth by governments, most notably our own, World-Wide. This article certainly did not slap their wrists severely enough to give them pause, it seems. In fact, one such event detailed below created a situation where, whether by coincidence or intention, THE GOVERNMENT HAS CENSORED CONTENT IN THIS POST FROM MY READERS. So please read while you still can, though there is nothing I can do to restore the part that has been censored (photographic evidence).
We should start by defining what Indymedia is. Or what it is not.
It is NOT mainstream media.
Free speech
What is mainstream media?
Mainstream media is this: Ruppert Murdoch saying “For better or worse, our company (his media conglomerate) is a reflection of my thinking, my character, my values.” in a speech to the Globalist Round Table group, The Asia Society, in Nov. 1999. They are a counterpart to our Council on Foreign Relations, only instead of wanting to establish a North America Union, they want to establish an Asiatic Union. A Globalist by any other name would still smell rotten in Denmark, methinks.
It is also this: Six transcontinental corporations which own better than 90 percent of all media holding in the U.S., and with significant penetration of other World markets. They include Disney, Viacom (CBS), Time Warner (which I maintain is heavily CIA influenced), Murdoch’s News Corporation, Bertlesman, and General Electric, a Defense Contractor. During the time frame of the Flight 800 shootdown by a Navy missile fired in a war game, all three major networks were owned by Defense contractors who made missile components for the Navy. Of course then, it wasn’t friendly fire, and they fired any reporter who dared say otherwise, and even gag writers for Saturday Night Live who intimated otherwise in their jokes.
In like vein, mainstream is also this: TWENTY award winning journalists prevented by corporate ownership from reporting the truth on major news stories (including Flight 800). Learn more here, which is a tempting taste from the book, Into the Buzzsaw. You won’t like what you discover about mainstream found buried beneath the sawdust. Example: “The news is what I say it is,” according to the General Manager of ‘unafraid Fox’ who refused to allow a new report unfavorable to Monsanto. Don’t get me started on Fox OR Monsanto. One or the other of them is liable to end up starting a revolution in this country.
Free speech
What else is there beyond mainstream? What about Indymedia?
If you don’t like that definition, there is an alternative; YOU can reclaim media (a useful handbook), which is exactly what Indymedia is about.
Indymedia is an international, fully independent and open Web/radio network where anyone can report news and bypass the bias and disinformation engines of  the Fourth Estate. It tempers submissions with journalistic considerations to prevent personal bias and shoddy reporting from ruining the value. They additionally field their own staff of journalists. As result, it seems, Indymedia has been gathering a reputation to itself, earning a new red and white target for a logo. Personally, I prefer the current logo.
the Fourth Estate. It tempers submissions with journalistic considerations to prevent personal bias and shoddy reporting from ruining the value. They additionally field their own staff of journalists. As result, it seems, Indymedia has been gathering a reputation to itself, earning a new red and white target for a logo. Personally, I prefer the current logo.
It was Indymedia who first reported in the U.S. about Colin Powell’s role in negotiating with coalition nations for partnership in the war against Afghanistan… more than a year before September 11! Yet this also serves to illustrate: Mainstream media regularly culls foreign press looking for news worthy of passing along. The Powell story had already been told in a mainstream Indian newspaper and the biggest newspaper in the UK, so we know they knew about it, and deliberately covered it up, even after Sept. 11 and the resulting war in Afghanistan. Talk about prior knowledge!
Actually, depending on what country you are talking about, citizens from all over the globe are reading about dirty little secrets and criminal abuse of power by governments (theirs or ours), thanks to Indymedia. It is a global success story with respect to beating mainstream at its own professed game (the truth). But that does not mean it has been smooth sailing.
Free speech
Indymedia regularly targeted by government(s)
So we should perhaps not be surprised then, to learn the the U.S .Government, in partnership with other governments (or they on their own), have officially targeted Indymedia through the actions of the dirty tricks department of CIA and FBI. Even local cops are induced to cooperate. Of course, CIA is getting help from OTHER governments, too, as we shall see. Thankfully, they got their tits caught in the ringer.
I like that image. CIA with tits. The sucklings must be quite undernourished, having been renditioned no doubt.
Let’s take a look at the time line of increasingly common, increasingly blatant, and ever escalating events:
free speech
Aug. 2000, Police block Indymedia satellite feed covering Democratic National Convention
Indymedia was starting to broadcast coverage of the Democratic National Convention from their Los Angeles studio. Not to be. Police descended and shut them down claiming there were explosives in a van in the adjacent parking some 20 feet from the Indymedia van. Funny, but there are no news reports of any such event in any news source. No bomb squad arrived.
July of 2001, police beat and arrest Indymedia journalists covering G8 Summit
This time in Genoa, Italy, while they were covering the G8 meet. They had set up a media center and broadcast facility in a closed school rented for the purpose. It was late night, and like the anti-globalism G8 protesters who had gathered in a nearby parking area, Indymedia staff was sleeping. Without warning, 150 Police attacked them melee style right where they lay and clubbed at least 60 so badly they had to be hospitalized. More than 500 were injured, one was killed, and 300 were arrested.
Perhaps at discovering their actions were being observed and recorded by Indimedia, Police then assaulted the IndyMedia team. Twenty Nine officers were indicted for grievous bodily harm, wrongful arrest, and even for planting evidence. Thirteen were convicted. Additionally, 45 assorted government officials, including Police, prison guards, and even doctors, were charged with physically and mentally abusing demonstrators and Indymedia staff while held in detention. It was Indymedia video evidence which assured convictions.
July of 2002, Police grenade seriously injures Indymedia reporter covering that year’s G8
While covering a different G8 Summit in Geneva, Switzerland, Indymedia journalist Guy Smallman, while close in with protestors, was seriously injured by a Police grenade, and fired upon with unknown weapons. As he was in a crowd of protestors being attacked by Police we cannot claim the assault was personally directed at him, but like all journalists in such situations, you can bet press credentials were held high.
June 2004, Founding Member of Indymedia Ecuador assassinated by what were believed to be government thugs
Like the above event, not all events are solidly incriminating of governmental targeting, but the reasons for suspecting they are tied will become apparent. For instance, Lenin Cali Najera was a respected young man known for his work rescuing youngsters from the clutches of gangs, so you might think that the Ecuadorian officials would appreciate him. apparently not. He was shot to death in the jugular by men thought to be government agents by those at hand, fitting the modus operandi of paramilitary death squads. His would not be the only murder of Indymedia journalists.
It is unclear if there was any specific investigation or article written by Lenin which might shed light as to the motivation behind his murder. Any articles written by him would be in Spanish and as I do not speak Spanish, are not easily reviewed for the purpose. There seems to be no speculation about a specific article in any of the English accounts of his death, of which there are few. But at about the same time, an Indymedia article surfaced in Cyprus which led to quite a lot of trouble, lasting for several weeks before coming to a head. A blackhead, which burst wide open. And what a stench!
June 2004, CIA and US Military go head to head with Indymedia via Cypriot Police
It started when an Indymedia contributor, Petros Evdoka, published an article exposing a disinformation campaign tied to Cypriot political issues which were, thereby, being manipulated by the U.S. Department of Defense cyberwarriors of the same sort I’ve had to go head to head with in my Flight 800 shoot- down investigation. The Cyprus matter was hardly a ‘legal’ or proper thing for the military to be doing by any standards.
Someone took exception at the exposure almost immediately. Police descended upon the entire Evdoka family and questioned them mercilessly, the focus clearly how he had come by his information. In the exchange, the Police, evidently trying to underscore the seriousness of the matter and to further intimidate, inadvertently and quite unwisely stated that their raid was at the direction of CIA. Bad move, threatening a journalist, even an amateur, with information they can use against you.
That erupted into a month’s long battle between Indymedia, the Cyprus and US governments, and of course, CIA and the DOD. It eventually resulted in a victory for Indymedia. The Cyprus Government officially admitted it had yielded to US pressures to play co conspirator with CIA against Indymedia.
Oct. 2004 FBI raids Indymedia and seizes servers, shutting down massive portions of the network
After all, it is rare to ‘win’ a battle with CIA without paying a price. Revenge is a dish best served by covert counterintelligence operations from other quarters, it seems (a blind side attack). FBI moved to seize third-party Web servers hosting more than 20 international Indymedia Web services to the US, Germany, France, and UK, as well as worldwide audio streaming news services and conventional Web resources. Even in Switzerland, a neutral country not known for yesmanship, kowtowed to US pressures in a raid, there. Indymedia was served with gag orders to prevent them from reporting the incident as news. That did not work very well, apparently.
Wikpedia has a nice summary of this affair, but the highlights are this. The actual warrant called only for surrender of log files. Instead, Indymedia was shut down by confiscation of all storage mediums, prompting a barrage of criticism from groups such as the Electronic Frontier Foundation, Statewatch, IFJ, the International Federation of Journalists, and the World Association of Community Radio Broadcasters.
FBI strangely denied ‘involvement,’ stating that the orders were initiated at the request of the Italian government, which speculators believe was at the request of Cypriot officials, or the CIA, which maintains a strong influence in Italian affairs. No one knows where the confiscated material went, or how or even if it was used in any investigation. Gag orders would seem to circumvent your right to know. In my own life, I doubt I will EVER obey a gag order of that sort. Make me a martyr for it, if you will, .gov. News is news, and truth is truth. It shall not be gagged by mere edict of a Judge in your pocket.
June of 2005, Local Police raid Indymedia UK and once more seize and shut down servers
Police ignored laws regarding journalistic protections and arrested an Indymedia employee at the site based on a submitted article which the Police deemed to be related to vandalism against a train connected to an upcoming G8 conference.’ Once more protests by professional organizations and watchdog groups followed, this time by UK groups NUJ, the National Union of Journalists, Liberty, and Privacy International.
July 2006, Indymedia server in San Francisco hacked by Zionist
THIS IMAGE GONE BLANK BECAUSE FBI SIEZED THE SERVERS!
Update: In July 2012, I accidentally noticed the image at right in support of this section was blank. Trying to find out why, I discovered ‘Server Not Found’. So I did some digging and found that not only had the Indymedia Server used by San Francisco been seized by FBI, but that no reason was given.
It appears they had relocated their server from San Francisco after the hacking incident described below and other problems in San Francisco with authorities, to Texas. FBI served a warrant on their Host as well as a GAG ORDER, so information is scant. FBI does state that it was NOT THE US GOVERNMENT that ordered the seizure, but ANOTHER UNSPECIFIED COUNTRY, the FBI responding to an International agreement of cooperation in matters of investigation of certain crimes. What kinds of crimes? Terrorism, kidnapping, and Money Laundering. So apparently those villainous Indymedia types have discovered a way to write news stories that make people captive against their will, and to launder money associated with their ransom, and then magically became exploding underwear?
More likely, the server was taken at the request of Israel’s Mossad. Take a look at the rest of my original article on the hacking event, and that assumptions will make some sense: The censored photo was evidence of participation by Mossad in attacks on US News Media (Indymedia). The only places it existed on the Web were, it seems, by links to the original image at IndyMedia. By shutting down Indymedia, they automatically censored the entire Web access to the image. I would therefore assume that if I had copied the image and posted it from my own computer, FBI would now have my computer, too. Close one! Here is the original hacking incident which has apparently led to censorship:
Hacked severely by a ‘Zionist’ hacker, indeed, who left a calling card to prove his Zionist motivation. There are no direct ties to any government, but as Indymedia has been a real pain in the ass to Israeli by covering violent actions against Palestinian and like misadventures, it would not surprise me to learn Mossad was the true source of the attack. I suppose this makes me an anti-Semite by Anti Defamation League standards, for so thinking. Whatever.
But wait. It was in this time frame that San Francisco was perusing a law suite against the ADL and B’nai B’rith (a Mossad infested version of ADL) for their participation in illegal spying operations against American Citizens in cooperation with San Francisco, Portland, and 18 other Police Departments, and other entities. Indymedia was covering that with clarity. San Francisco eventually had to drop the suit because of intimidation by the ADL and other external pressures insisting it anti semitic prosecution. So perhaps my supposition of Mossad hacking is not so supposing after all?
Look at the calling card (right). I did. Note the domain littlegreenfootballs.com. This Web site has had eight registrars (places they registered the name) on 36 changes between 19 unique name servers with 63 changes on 23 unique IP addresses in six years. The ‘owner’ (a shell corporation, colours Ltd) operates 2,509 other domains. A useful set of tools to make tracking true ownership and association ‘difficult.’ The site is full of pro-Mossad ‘information.’
Update: Since my original post, and perhaps as yet another indicator that Mossad requested the FBI hit on Indymedia S.F., it turns out that littlegreenfootballs.com has changed hands yet again, and now, the content no longer has anything whatsoever to do with Israel and the Zionist material once found there.
In fact, it is a bit of a ‘mock site’ designed around a ‘shell’ or ‘skin’ I recognize as common to several CIA operated ‘commercial web sites.’ So you get a lot of ads and links that make it look like a decent, ordinary site on the edges, which are nothing but fluff and camouflage, and the disinfo in the middle. Again, what they present there is really intending to make non mainstream media look bad (today, for instance, it tries to make Alex Jones look crazy for talking about the Aurora shooting as false flag, and then proceeds to reveal information painting it as ties to Muslim terrorism.
How do we always seem to come up with these condemning terrorism details so quickly after an event? Like finding the wallet of the terrorist pilot on the street after nothing else identified with any passenger of the 9-11 aircraft survived the crash. Convenient. Back to the original article, and one more update section, below…
Oct. 2006, Police in civilian garb suspected of shooting Indymedia journalist to death
New Yorker Bradley Roland Will was killed covering a protest in Oaxaca, Mexico regarding a teacher’s strike. He and two protesters where shot to death by ‘upset residents’ who were later tentatively identified as Police by the U.S. Ambassador to Mexico. Despite this, Associated Press claims that some protesters were also armed and it was actually more of a shoot out than outright murder. However, this was the event which, due to the more popular media accounts as a murder, sparked what many refer to as a revolt in the State of Oaxaco by the APPO, The Popular Assembly of the Peoples of Oaxaca.
September, 2009, U.S. Army violates Posse Comitatus and arrests Indymedia reporter, destroys her camera, seizes video
Members of the U.S. Army (possibly National Guard) operating illegally as deputized Police in violation of the Posse Comitatus Act of 1878, arrested Indymedia reporter Melissa Hill and three other reporters covering the G20 Conference in Pittsburg. Her camera was destroyed and her media confiscated. The military was even operating the jail and running the booking operation per her YouTube interview. Unless Martial Law has been declared, it is illegal for military to engage in Police actions. This has been something the Military has been repeatedly in violation of since 1990, in a long list of states, with Oregon, California, and Texas NGs being the most frequent abusers. This abuse will be the subject of another blog.
April 2010, Police use invalid warrant to illegally raid home of Editor for Gizmodo
San Mateo Police use an invalid warrant to raid the home of an Editor for Gizmodo, destroying his front door and seizing his computers and other equipment, the warrant being exercised when the home was empty. Not only was the warrant invalid in legal terms, but the hours allowed for its use were ignored. The raid was prompted by an article written for Gizmodo. Journalists are protected from warrants seeking materials related to their work by State and Federal law.
Also April 2010, Cops and the District Attorney illegally raid a student newspaper
Seven Officers and the District Attorney entered the offices of The Breeze, a student newspaper for the James Madison University in Harrisburg, VA, and threatened to seize all computers if they did not turn over all photographs in their possession relating to a party covered by one of their reporters where violence had broken out. There was a warrant but the student journalist was quick to point out that the Privacy Protection Act of 1980 prohibited such a warrant, at which time the threats were made and the student relented. Police copied hundreds of photos to a CD, including many unrelated to the party, further in violation of their own warrant.
Dec. 2010, The French Minister of the Interior attacks Indymedia with accusations of being out to get Police
The French Minister of the Interior (like the head of the Justice Department in the U.S.) claimed Indymedia was attempting to identify Police and endanger their safety. What? I thought Police were supposed to identify themselves on request. The link is largely in french save some casual comments giving summary and personal opinion.
May 2011, Google in possible collusion with U.S. intelligence community enables assault on Indymedia viability
Google, often described as partnering with the U.S. intelligence community, modifies their search engines to de-rank Indymedia in search results. Simultaneously, a hack was attempted of Indymedia resources to augment the Google de-ranking to burry articles 20 pages deep in searches. Also simultaneously, a flood of tactically anti-Semitic comments hit the UK Indymedia resulting in accusations of ani Semitism in an attempt to discredit the organization, and a like flood of intimidating criticisms and accusations against legitimate Indymedia contributors (name calling, etc.).
free speech
What about the rest of media? Are they free from abuse of power issues?
Indymedia is not the only one to suffer such ills. While it is popular to see mainstream media as controlled, they do sometimes get out of hand with their Masters and end up causing problems. Sometimes a little corrective conditioning is required to remind them where their hearts should really lay. Here is a partial list of a growing epidemic of Police and government assault on journalistic free speech. I fear it is only a matter of time before Congress will once more attempt to censure free speech entirely with a Sedition law which makes any criticism of government, even with evidence of wrongdoing, a Federal crime. It has already been attempted in form.
More than 1,100 journalists and support staff have been killed over the last ten years while at their job. Below follows a very brief list which represents about an hour’s effort to locate and document. While it is a global phenomenon most commonly found in association with a Globalist agenda or in an oppressive regime, I have tried to focus mostly on U.S. examples. The bulk came from a single source. You can easily find more, as seen in the surprisingly good two pages of video reports by Russian’s RT Network, and this page detailing all known incidents in Egypt.
April 8 2003, Al Jazeera’s office in Bagdad rocket attacked by a US warplane
The DOD had been given its coordinates by Al Jazeera in exchange for assurances it would not be attacked. Correspondent Tareq Ayyoub was killed while reporting live on details of a firefight some distance from his balcony. His coverage did not include or illustrate local combatants being present, but the US insists the attack was due to fire from his building.
Also April 8 2003, US Abrams tank opens fire on hotel where more than 100 journalists are located
The Palestine Hotel is where non embedded international journalists were under armed quarantine ‘for their protection.’ The attack hit the Reuters office on the 15th floor killing two cameramen. The U.S. military again claimed self defense, despite counter claims by multiple news agencies present including a French team which video taped the incident. The Pentagon countered that non embedded journalists should get out of Dodge, an implied threat gently worded. Embedded Journalism, when unbalanced with non embedded, is a controlled media.
March 2004, US Soldiers shoot 2 journalists dead at a checkpoint, Reuters cameraman shot by US fire filming combatants
The Pentagon claims the shootings were within the ‘rules of engagement,’ fail to mention a tank collided with the vehicle they were in.
Jan and March of 2004, three Reuters staffers and two Al Jazeera reporters detained and brutalized by U.S. forces
In the case of Reuters, it was immediately after they had filmed a crash of a U.S. Chopper.
Nov. 2009, Man arrested for taking video of public statement for possible news worthiness
Quite odd because he had already filmed the same participants the day before, and both knew and accompanied them to the two-day event.
June 2010, Police harass, beat, arrest journalist covering G20
Jesse Rosenfeld was abused without provocation as he was held by two officers and hit by a third because one officer did not believe his press credentials were genuine. Journalist Jesse Rosenfeld reports for the Gaurdian, Now Magazine, The Washington Report on Middle East Affairs, The Montreal Mirror, and CBC Radio Canada.
And, my personal favorite, and the best possible place to end the article with a bang:
April 2011, Maui Times Publisher assaulted by bounty hunters and then Police for video interview

Not Wanted (from dogthebountyhunter.com) Thank You
Publisher Tommy Russo was covering with (video) matters relating to the TV Reality show “Dog the Bounty Hunter” (which I firmly believe is a CIA propaganda exploit, it being true that CIA runs a school for bounty hunters as I document in my book set, Fatal Rebirth) when he was confronted by a member of the show’s security team (a BIG guy), who is adamant he stop video NOW. Russo identifies himself as media and asserts his right to video in public any public event, and that’s when the big guy bashes him in the face without warning.
Russo tries to call Maui Police. While trying to call 9-11 for help, the security man takes his camera (phone) it and throws it while hitting Russo in the mouth. It is a crime to interfere with a 9-1-1 call. After regaining the phone, multiple dogs are screaming at him as he is trying once more to talk to the 9-1-1 operator, all happening while the Police actually show up. All they see is a lot of shouting at one guy, so he must be the bad guy, right?
Exact replay: A cop then attacks Russo as well, without warning of any kind, ostensibly for the same cause, that he was attempting to document everything on video. Their claim is because it was ‘an agressive movement. ’ The movement? He turned (rotated) toward the officer to whom he was responding, who punched him and grabbed his phone for the third time, again.
Moral might be: shoot a gun, not a camera when they are that big and ornery :}
free speech
What can you do as a citizen to reclaim media?
Simple. Be the media. Learn about Indymedia. Keep a video capable device with you, always. You never know when you will be at the right place at the right time. I wound up sitting in the middle of a Police Command Post during an unrighteous Police shooting of an elderly man, and heard the lies they foisted on the public in the process. They were informed in the Command Post that the man had a .22 cal starter’s pistol (fires blanks), but they told media he was armed with two other larger weapons. Hopefully you will never have to experience anything as dramatic and traumatic as that, but the point is, be ready to tell the truth because you cannot count on Police or media to do so in your absence.
If YOU want to know the truth, you must also be wiling to SHARE the truth with others, or you don’t deserve to complain when you don’t get it.
When you see Police or any other form of violence, get it on video, and make verbal comments as you go on details as to where and what circumstances, etc. Some communities (fascist rule) prohibit video taping cops. I don’t care it there is a law against it or not. If they are behaving badly, the law and any court daring to enforce it be damned. You can make that choice for yourself. With or without video, write it up and submit it to Indymedia, and get any video on YouTube (you can reference the video at YouTube in your article).
Final update: In looking for the San Francisco server, I also discovered more than a dozen more examples of independent media assaults undertaken by government. Most were server seizures, but there were also physical assaults, and in one instance, arrest and prosecution for felonies and other charges for simply being present covering a breaking news story of a crime in progress (if you call a sit in a crime)… essentially charging the reporter and camera crew with the same crime as those effecting the story. What is wrong with this picture? Oh, I forgot. They took the picture, so you don’t get to see it!
End of speech.
End of article.
End of free speech in journalism?
Related articles
- U.A.E. Slaps Severe Limits on Web Social Networking. 10 years prison for “spreading rumors”. No to free speech. (worldnewsrecord.wordpress.com)
- Free Speech and the Internet (thecustomercollective.com)
- Woman who filmed cop from own yard charged with obstructing his administration of government (boingboing.net)
Nibiru Updated: A Logical Path to a Credible Planet X
Between government conspiracy to disinform and lunatic fringe misinformation, how do you know what you NEED to know about Nibiru?
by H. Michael Sweeney, copyright © 2011, ProparanoidPress, all rights reserved permissions to reproduce available on request to pppbooks at comcast (net)Planet X
Disinformation via Lunatic Fringe vs. Science Fact
Planet X
Dateline Portland, OR August 4, 2011 Updated Aug. 29, 2012 (updates in red)
Planet X
In an age where FEAR is a Political Control Technology applied with eager abandon by our own government through the 4th Estate (media), do we really need to have yet another Doomsday theory and all the disinformation, misinformation, and twisted derivatives that usually accompany?
Yes, if it’s true. Otherwise, Heaven forbid, thank you. I’ve had enough just dealing with JFK, much less all that has followed.
But as an investigator I like to think I’ve made significant inroads in major conspiracy fact finding. I pride myself for revealing what others have missed, and for exposing disinformation and misinformation along the way, generally bringing one (hopefully) closer to the truth. And that makes this the perfect time to state what media seems unwilling to admit: a cover up and the use of disinformation is only necessary when there IS a conspiracy. It is, in fact, proof of a conspiracy. So when the officially insane among us who dare to look at, talk about, or investigate a given conspiracy are labeled with the ‘medical term’ for our insanity as ‘conspiracy theorists,’ I have to say I prefer that insanity to instead ignoring the lies and inconsistencies in official accounts and accepting them as truth.
End of soap box speech. But I wanted you to understand, if one seeks to discover lies, the easiest place to start looking with success is government and media statements. When you become a conspiracy theorist and are labeled as mentally ill for your trouble, you’ve likely found exactly what you were looking for; truth. Liars label truthers as a means of discrediting them without having to deal with their contentions. They have to, because they fear the truth when it becomes too visible. And when the labeling tactics come right out of the Iron Curtain political control manual (labeling those who question government as mentally ill), you know the kettle is as black as it can be.
You are only allowed to think what they want you to think, or else your mind is sick. How sick is that?
planet x
Planet X, the Conspiracy
Google it if you wish, but if you read everything you can on it you will find as many kooky, half-baked, and downright impossible theories as you will scientifically sound. And yet your determination as to which is which may be less sound, because when it comes to conspiracies, the truth is often closer to the weird than the probable. There are reasons for that, but this is not the time and place to detail. The purpose of this article is to help one weed through the hype and find the most logical path to a credible theory about Planet X. I do think I’ve found that path, with reasonable proof of a conspiracy via cover up, to boot. It (gulp) does portend of Doomsday, to the point that perhaps I won’t put off seeing the movie, 2012, until 2013 after all ~ procrastinator that I am.
The basic elements of all Planet X theory is based in fact, though many of the disinformation sites out there will give you wrong facts, made up facts, or no facts at all, in order to discredit the remaining theories otherwise worthy of your consideration. These are common cover up ploys as seen in my 25 Rules of Disinformation. The basic true facts are these: There is a large astronomical body of some sort out there which is captive to our sun. It has been temporarily named Planet X. No one can precisely tell us what it is, where it is, where it is going, or if it is a threat… or they are unwilling to do so, despite having spent a hundred million dollars or more on custom space craft and programs for the purpose.
planet x
What they can tell us (but prefer not, it seems) is that:
- it is big… bigger than the Earth in mass by more than three hundred times.
- It is dark and does not reflect useful light, which is a bit of a problem, of course, if trying to find and define it.
- It is so big it tends to collect other bodies and objects as it travels, and is a bit like its own small solar system as result.
- It is, in fact, possibly a Protostar, a body of dense matter not yet dense enough to ‘ignite’ and become a sun. That could change.
- It is traveling through our solar system in an extremely elliptical orbit about 30 degrees off axis compared to the orbits of the planets.
- It takes about 3,650 years to make its own orbit. There are historical evidences of its passing.
- It is so big that it causes wobbles and other anomalies in planets it comes near (specifically, Pluto, and Uranus, and perhaps EARTH).
- Such proximity can be harmful to the well being and structural integrity of a planet, and in turn, any life on said planet.
- It is on its way toward us as you read, scheduled to visit a sky near you next year, give or take.
- Exactly when, how close, and to what end, is where the theories come in.
- Because the answers are scary, an organized conspiracy to cover up exists.
Finding the Path
I was started on the path by a international client to my security/privacy consulting services. I tend not to get too excited when there is a new conspiracy to consider. I don’t enjoy exercising my insanity all that much, I guess. Rather, if anything, I tend to take a look at it in hopes of proving it invalid, assuming I look at all (Ostrich Syndrome). Disproving is much easier work in the long run, I assure you, where true. You can’t prove a negative hypothesis, but you can prove misinformation, when so. Trouble was, his informational starting points were solid. He gave me a name, and associated facts to get me started.
The start of the path is one John DiNardo
While no astrophysicist, DiNardo has credentials sufficient for me to find him credible on the topic: High School Physics Teacher with a degree in Science Education, and a background in electronics, and an ex-Marine electronics specialist. Someone who who understands critical thinking, logic, and principles of scientific study, someone trained not to jump to conclusions, demand proofs which can be tested, and test them. Moreover, in listening to several of his many radio interviews I found him very careful to provide only acceptable, verifiable resources and to go well out of his way to insure there was no misunderstanding of meaning. Better still, things he said which I thought might be challenged, could not.
That was me demanding proofs, and testing. He was right every time when I checked his points. Kudos, JD.
planet x
First waypoint: a USAF satellite and the Pioneer series of deep-space craft
His start takes us next back in time to 1983, and the early 1800s, and even thousands of years earlier. But the key points easiest to grasp and illustrate were in 1983. Two newspaper articles which concretely prove the existence of Planet X and start us on the trail to proof of a conspiracy by means of cover up and disinformation. A New York Times article detailed the launch of a multinational (US, Netherlands, Britain) $80M Infrared Astronomical Satelite specifically to attempt to locate, identify Planet X, and ascertain its trajectory. The article IS worth your brief reading.
It points out that Mount Palomar’s observatory was already tracking the Pioneer shots as they approached Pluto to judge any variation in their trajectories due to the existence of an inbound Planet X, and that the satellite was specifically constructed to find the dark ‘planet’ (compute the approximate mass and location based on gravitational effect). It also points out that Planet X has been thought by astronomers to exist because of orbital anomalies of Pluto and Neptune for roughly 200 years, anomalies only possible if impacted by a strong gravitational pull of something very large an relatively near. The article is remarkably uncensored and ‘open’ in content, detail, and style compared to all that has since followed. Someone rendered Planet X news into a black hole.
The second article was exactly 11 months later, to the day, in The Washington Post. By comparison to the former, it is brief, sans much detail, and contains at least three demonstrable falsehoods from official sources, and clear tones attempting to minimize importance. It is almost an apology for existing. The cover up starts here, it seems. The first article already well defined Planet X and its path and destination, and as being part of the Solar System, and states that scientists are “so sure of the 10th planet, they think there’s nothing left but to name it.” But the official quoted in the second article wants us to think it is another galaxy far away, and not inbound.
“It’s not incoming mail, I want to douse that idea with as much cold water as I can.” “I believe it’s one of these dark, young galaxies that we have never been able to observe before.” That from the man overseeing the launch and operation of the USAF Satellite, Dr. Gerry Neugebauer.
planet x
Second Waypoint: mysterious deaths
Remember the first article? The two Doctors quoted extensively in the article who were quite open and forthcoming with information, are dead. Some mystery suitable for our flavor of insane thinking do, unfortunately, exist, though certainly with ample plausible deniability, a key element of any good cover up. Dr. Robert S. Harrington died of Cancer while on a field trip tracking Planet X in 1993, attempting to prove it was inbound. Yes, he had recently been diagnosed with cancer, and was engaged in fighting it. No, it was not advanced to the point where it was debilitating, or near terminal, or he would not have undertaken such a field trip.
Yet while on his field trip in Australia, he ‘died of cancer.’ Well, that’s after at least one report that he died of ‘an accident,’ but I’ve not been able to track down that report as mentioned off-hand in an otherwise non authoritative source. Benefit of the doubt, except that…
The other Doctor in the article, Dr. Thomas C. Van Flandern, also died of Cancer in 2009. Nothing quite so distinctively mysterious in his case, perhaps, except that… one other scientist working on revealing Planet X died of Cancer in 2006. Dr. Giacomo Giampieri was an Italian Astrophysicist who was barely 40 years old. I must tell you that there is nothing in the way of evidence to say these were murders, or imply it directly. Yet, it is, of course, the kind of facts that you start with when investigating for possible conspiracy, just like any good Policeman wanting to insure there was no foul play.
But I’m also compelled to tell you that it is a fact that CIA has been known to employ a specific methodology to induce cancerous tumors in targets. I’ve written of their use of radioactive discs in my various books, as have others. While it is not a very fast way to kill someone, it certainly offers plausible deniability, and tends to take them out of the picture well before they succumb. This, the unlikely eventuality that someone near death from cancer would tramp off to the Outback on a strenuous quest, and the odds that all three scientists should coincidentally die of the same cause in opposition to all actuarial table math… leaves us with a question mark which weighs toward wondering if they are not signs of a cover up/conspiracy in the foulest-of-play form. We do not know, but we are required to consider it.
planet x
Third Waypoint: Tactical Distraction; Comet Elenin
Another disinformation tactic commonly used is to distract from one story by creating a ‘bigger’ story. I use ticks because it isn’t always truly bigger, but simply hyped as such. If you can somehow confuse the new story with elements of the old story, you end up with a win win disinfo effort. Now that DiNardo has been getting a lot of radio interview time and the Planet X conspiracy is taking root in the Web, comes forward the Comet, Elenin, just in time to be useful as disinformation fodder. IT IS A COMET. It has no properties of Planet X. Yet the Web is awash with inference and claims that they are one and the same. They even go out of their way to describe it as ‘The Dwarf Star,’ which is a Planet X descriptor, and talk about it having captive ‘moons’.
Moreover, scientific data is being trotted out to equate Elenin with the kind of catastrophic effects (fears thereof) foreseen for any pass by of Planet X near to Earth. Pole shifting earthquakes, weather upheaval, magnetic storms, etc. Elenin is already ‘here’ for all practical purposes, whereas Planet X, is yet distant in space and time. But you can see through this smoke screen with some basic logic. They point out for example that earthquakes are happening and are synchronous with Elinin and thus ‘proof’ it is Planet X. But wait. Look at the WHOLE of earthquakes and you find them happening constantly. So no matter what event you want to relate an earthquake to (e.g., an Obama speech,) you can find multiple correlating earthquakes that day.
I in fact took the first speech by Obama for which I could ascertain the time – a press statement on economic matters for Aug. 2, 2011, 12:15 ET, the very day I’m writing this. As it is now 3:24 PM, Pacific, he has already spoken, and so I undertook a look for quakes. There are already 19 quakes today (and ‘yesterday’ across the International Time Line), posted (more may exist and not yet be posted). All but two are near or greater than 5.0 in magnitude and of the general strength as used as ‘evidence’ in the Elenin trash. One was closer to 4.0, and one closer to 7.0. THREE of the 4.0-5.0 category were actually within an hour of his speech, two before, and one after… which means we should ask President Obama never again to speak, via Eleninian fuzzy logic, which chooses to focus only on those facts which sound like they have a bearing, and ignoring the balance of information which contradicts that assumption. Feel free, if you wish.
But let’s make it simpler: comets have virtually no mass for their size and are barely solid objects, and thus have non of the properties of Planet X. PERIOD.
Meanwhile, NASA, normally prone to flood the Web with pictures of all things astronomical, fails to include ANY images for Elenin in their Elenin library, making it easier for wild claims about accompanying moons and the like a’la Planet X. You can find NASA images of Hale Bopp, a lesser comet but of similar conspiracy theory fame (Heaven’s Gate Cult, another mind control thing variously tied to CIA/DOD), but you can only find amateur images, faked images, and artwork depicting Elenin on line. Why, I wonder, is that? Someone prefer us not to have factual information at hand?
Comets come and pass all the time, often relatively close, and not one of them has been called a dwarf star (rightly so), nor accused of causing massive disruptions on Earth of the sort posed for Planet X. The Web is awash with this nonsense, and it smells like a disinfo campaign by professional cyberwarriors, to me. It fits the same pattern seen time and again with all major conspiracies and cover ups. We are a stupid people to swallow the hook, line, sinker, rod, and reel. Only the disinfo angler gets to walk away unscathed.
Planet X
Fourth Waypoint: Silence
What the ****?
Scientists for hundreds of years have been wondering about Planet X with solid evidence it exists, some of it thousands of years old. We spend enough money to put 4,000 kids through a year of college on satellite designed to figure it out… and watch two deep-space craft to get more evidence… and the rock gets so close that a scientist is taking his own portable telescope to the Outback to watch it in person… which also means it is so close that it is starting to reflect light… which also means that it MUST be heading in our general direction (incoming mail, after all)… AND NOT ONE NEWSPAPER OR SCIENCE ARTICLE BRINGS THE SUBJECT UP? No. Instead, however, whole groups spring up to ‘debunk’ and discredit the deceased, and whole new (and considerably wilder) theories involving aliens, ancient cults and religions — and poser Planet X comets — pop up to sidetrack the path seeker.
And, Mt. Palomar goes black about course deflections of the deep-space craft well before their guys die off. Meanwhile a bit of official disinformation on said deflection seeks to rewrite physics to account for the deflections, and fails to even describe the location and times of the deflections, because that would show their rewrite was bogus. The scientific paper, The Anomalous Trajectories of the Pioneer Spacecraft, is totally bereft of useful data for review of their findings (very atypical of scientists), and is a joint paper written by people from several government funded entities: Jet Propulsion Laboratories (they monitored the craft), Los Alamos National Laboratory (they worry about physics a lot), and the Aerospace Corporation, a major contractor in the project. Authoritative sources, it would seem.
So why do they come up with three different explanations, one of which requires us to believe both ships sprung a leak in thruster fuel, and one of which rewrites physics? The third tries to blame it on faulty data, about as lame as leaks. What galls me is that this report was then passed along and commented upon in various media resources as if it was an outstanding and thorough job. Excuse me, the thing is hardly 20 short paragraphs! All that, and the fact that they rely heavily on government money, gives me significant pause.
Why? Because THAT, is how a cover up is effected. And all that mess and confusion is why I wrote this article! When scientists, academia, media, and government all clam up and, worse, all start slandering truth and truth sayers… the cover up is in evidence. Throw in some mystery surrounding the deaths, and it starts to form a time-honored pattern in cover ups. When those who remain silent depend (largely) on Federal budgets and grants… or when the nasty ‘national security’ blanket descends on one’s work and findings, it is easy to squelch the truth. When most of Media is controlled by military contractors and a few civilians (e.g., Murdoch, Gates,) it is easy to police the squelch. Thus only free thinking independents like DiNardo dare come forward.
But unless free thinking individuals listen to them, it is to no avail. Only you can answer if that be the case, or not. Are you free thinking, or manipulated?
plante x
Path’s final destination: EARTH?
That’s the big question. It’s not IF Planet X is real, or not, it clearly IS real. It’s not if Planet X is inbound, or not, it IS inbound. The question is WILL IT COME CLOSE ENOUGH TO CAUSE HARM, and if so, WHEN, and to what EXTENT? At this point, because the scientific community is not forthcoming, and media is not seeking, and government is pretending to know nothing, I’m tending to stick with listening to Dr. DiNardo.
Their silence speaks volumes about the possibility that the answer is not one we would hope to hear. Fortunately, listening to Dr. DiNardo is easy to do. He points out, that because of these same silences, not even he is able to give a solid answer. He can only estimate. He has. And I for one hope he is wrong. Because if he is right, I’d better check out a copy of 2012 right away, or just plan to watch the main event in real time and save the rental money for… nothing.
In closing… I’m not including any Related Articles as I might normally do, as the ones I trust are already linked, above. There are so many questionable Web pages out there on Planet X that I simply don’t want to take any more time trying. I got frustrated trying, because so many of them had bogus facts or errors which made them strawman material. I can’t tell you how many seemed to deliberately get names and other factoids wrong. Forgive me, please.
Added material… not exactly an article, but a video featuring material from a BBC documentary which revealed Nibiru, and which explains what our paranoid government has preferred to cover up in a conspiratorial effort to ‘protect us’ from (something), we must presume. It explains why many people around the World have seen two suns in the sky at sunrise and sunset, and many other phenomenon that otherwise simply made no sense. FASCINATING to watch.
World’s 1st Ergonomic/Heuristic Book may resolve Dyslexia
by H. Michael Sweeney, copyright © 2011, ProparanoidPress, all rights reserved permissions to reproduce available on request to pppbooks at comcast (net)
dyslexia
Dateline Portland, OR August 1, 2011
dyslexia
Initial tests show remarkable ease of reading for all readers,
with improved retention and comprehension.
dyslexia
ProparanoidPress has released the World’s 1st Ergonomic book. I know, you are asking how can a book be ergonomic? Does it fit the hand better? No. Well, just a bit, perhaps. But the way it is ergonomic is the way it reads… how it interacts with the eyes and the mind. That brings us to being heuristic. I know, you are asking what does heuristic even mean? The simple answer means it improves one’s ability to learn while doing. OK, then, so how does this new book manage to do all that?
It uses a new print technology, a method of displaying text called ErgoText by its inventor, ErgoDox LLC, a small start up in Oregon. I just happen to know the inventor and thus was quick to seek license to use the new technology for my next book. What’s really cool about from a publisher’s standpoint it is that is saves paper, which makes the book smaller, which means it DOES fit the hand a little better (I did say “a bit, perhaps”). What it really means though, is that the book costs about 20% less to print, which makes everyone happy, especially since heavy wood and paper products have to be shipped (with fuel prices sky high) up to ten times from forest to bookstore. But there is lot more than lower price to make consumers happy.
First, it is ergonomic in that it is easier to read for reasons which defy simple explanation. It even reads faster, because it is almost impossible to loose one’s place or misread a word unless there is a grave contextual error or misspelling. Yet for Editor’s of a book (or anything else using ErgoText), it is discovered that such error’s tend to jump off the page and thus there are fewer errors to be found in the final product.
Second, it is indeed heuristic, in that it converts textual material, which normally uses only the left-brain hemisphere inmost readers, into a form which is also seen as being graphical in nature by the mind, thus activating the right-brain hemisphere, as well. This means better comprehension and retention — as does the fact that there are fewer reading errors as described above. In fact, some uses can even activate other parts of the brain not normally used in either textual or graphical analysis, parts which stimulate episodic memory, which means a significant memory aid. Perfect for text books, manuals, and other serious texts. I’m so pleased with ErgoText that in the future, all ProparanoidPress books will be using it.
But perhaps the most amazing and unexpected thing is this: it seems to help readers who are Dyslexic or suffer other reading difficulties. I’ve only sold a handful of copies personally to users at Conspiracy Conference 11 last June, but as it happened, two of them were Dyslexic, and the reason they bought it was because they could instantly read it without struggling. I was shocked, as were they! It was as if scales had fallen from their eyes. So I next went out of my way to get some ErgoText material in front of several other Dyslexics I knew, and they said almost exactly the same thing.
In the process I learned that there are many forms of Dyslexia, each type causing a different viewing and comprehension experience roadblock. Some see letters jumbled (the most common). Some see the text quiver, shake, or move about. Some see funny visual effects which make letters and words unreadable except at vision center. And more. But thus far, of the 6 Dyslexics I’ve worked with, who have among them four of the various kinds of Dyslexia, ALL said it was dramatically better than regular text to read. So I contacted the folks at ErgoDox and, as result, they are currently offering a comparative reading challenge (remember the Pepsi Challenge?) to help quantify this phenomenon and determine what to do, next.
Go there and take the challenge!
It takes about 5 minutes to compare two paragraphs of material in each format for time it takes to read, ability to spot errors, and ability to find select text quickly. They want lots of people to take the test, because almost EVERYONE finds it easier to read, but especially want Dyslexics and persons with other reading issues to PLEASE take the test. Everyone who does take it should be sure to answer the anonymous questions about their experience. One does have the option of leaving an email address in which case they can receive a free downloadable print-your-own writing paper file of ErgoScript, which is the writing paper the firm offers based on the same technology. So even hand writing now becomes easier to read, etc.
I’d show you a sample of ErgoText right here, but I want to give you a reason (curiosity) to go to their Web site and take the challenge. Sorry if that seems like dirty pool, but its really important to learn if it really helps Dyslexics, et. al., or not, how much it helps, and what percentage of sufferers are helped. If enough good data is collected, it may justify a more formal scientific study which could result in further improvements for Dyslexics. Imagine if you didn’t know how to read at all, how much a loss of communication power that would represent. Dyslexic individuals are often just a notch away from that status, where any large block of text is difficult enough to read that they would just as soon pass as not, and go without the information.
Now imagine all the good stuff you’ve read in just the last 24 hours. That’s probably about as much as they would read in several years. Give them a break, and take the challenge, regardless of if you are Dyslexic, or not. And if you know someone who is Dyslexic, get them to read it by hook or by crook. Such a small thing to mean so much to so many. There are, after all, perhaps 50,000,000 Dyslexics in the U.S. alone. As a writer and publisher, I want to reach them, too.
Oh, yeah. The book? It’s called In Mindless Times.
A sci-fi time travel yarn determined not to bore you with the same old tired impossible time-loop plot twists. Not one single time traveler goes back in time to have sex and become their own father! However, there still is a lot of sex going on… and lots of plot twisting to go along with that trysting. Unlike many sci-fi works by other authors, I did a lot of research into the current state-of-the-art in actual time travel research. Discovered there is a lot of current (and well funded) research going on, and I think that effort made the book more plausible and realistic than most. That research is even summed up in the Appendix. How cool is that? A sci-fi book with an Appendix of facts. Who knows? Might start a trend; workable science fiction.
Want to learn more about time travel or the book? Listen to my interview on Truth Brigade Radio Show with Christie Czajkowski. There is dialog on other topics until about half an hour into the long show.
I promise it will be fun. So will be taking the challenge.
Related articles
- Writing with Dyslexia (sallyjenkins.wordpress.com)
- Dealing with Dyslexic Learners (socyberty.com)
- How to Help Dyslexia with Visual Learning Strategies (brighthub.com) Sort of confirms the whole graphical right-brain notion without stating it.









































There is a Mark of the Beast Implant with YOUR NAME on it
Jul 25
Posted by Author H. Michael Sweeney
This is an old topic that’s lost traction in the public eye, but in the background, the enemy continues to work ever closer to fulfilling prophecy about Mark of the Beast. Now, employees are being asked to implant themselves in order to get snacks, get through doors, and access workstations and photocopier.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.What you will learn reading this post:
Invasion of privacy tiny in size, massive in scope
Tracking implant quite similar in shape to a much larger one found in my own leg some 35 years ago. State of the art, today, are smaller, translucent, bond with and look like human tissue: invisible to a surgeon and to x-ray. MRI sees them as a blemish. Less sophisticated units without GPS/cellular/wifi capability can be as small as the period in this sentence.
Recent news stories, including a particularly scary one referenced in red text, herein, have forced me to draw upon years of research and dig out my old PowerPoint presentation, 666 Reasons for Smart Dust and RFID Technology, as presented as the keynote presentation at Conspiracycon 2010, in Santa Clara. Any definitive presentation must go back to the beginning, or the dots won’t quite usefully connect. This is going to impact YOU in YOUR LIFETIME. Actually, it already has, and you just don’t know it; the water temperature is slowly being raised on we Frogs, and it’s quite hot, already. Hopefully… we can somehow jump out before its too late.
Smart Dust and RFID tracking technology are quite related, but Smart Dust is not going to be a part of this presentation, except to say that it is nanotech capable of much more than RFID, but it is not an implant. While it is represents its own significant threat to social, financial, and physical security and well being, it is less useful than a tracking implant for the population at large, and cannot play the role of Mark of the Beast. Fortunately, it will not likely ever be used against anyone not deemed a high-priority national security risk. You know, like Will Smith, in Enemy of the State.
The less costly Digital Angel implant
RFID, however, is the very heart of the tracking bio implant, the most obscene version and infamous of which is Digital Angel. That’s the name of a CIA front central in pushing for implants, but also often used to describe their chip, itself as a product trade name. They also offer a wide variety of tracking systems which are non implant, such as wearable items like watches and ankle bracelets.
But we need start with a broader view on RFID to fully understand the greater threat this topic represents. Non implant (and seemingly harmless) versions of RFID are already used to track an endless array of products, and you are quite likely to bring them home every time you go shopping. In retail, it is mostly benign, but it becomes the bedrock of a useful personal tracking system.
What?
Mostly benign? Check this out, an edited and updated excerpt from my book, The Professional Paranoid: How to fight back when Investigated, Stalked, Harassed, or Targeted by any Agency, Organization, or Individual (third ed.) Excerpt begins…
Smart Dust, RFID, and the Mark of the Beast
i want you to consider the first letter of this sentence; the lack of capitalization is not a typo. I wanted to draw attention to the dot above the letter ‘i.’ There is a reason… there is an RFID invasion taking place, and some of the invaders can be just that small.
Though the Mark of the Beast is thought of as being the number 666, that is not quite the case. That is the number of the Beast himself (the Antichrist) in numerology evaluation of his name. The original words used in the original Greek texts of the New Testament can be translated to mean ‘insert’ as well as ‘mark.’ Thus there are growing numbers of people who think that some form of Digital Angel bio implant will be the actual marking device. This section will illustrate that likelihood and educate you on just how close to that day we may be.
This will make sense later: implants are the mark for the hands of peons, and marks on the forehead are the mark for meons.
What is Digital Angel? It is a firm which is known for a series of tracking products, including bio implants, all based on RFID technology. Simply put, it is a passive device which, when scanned with a low-energy RF signal, responds with a signal of its own, broadcasting a unique identification number or other data. Early versions of this are still commonly found in clunky removable/disposable merchandise security tags installed by retailers which can trigger alarms when shoplifted goods exit the store. In the modern version, the product manufacturer includes the chip which enables the same feature without the retailer needing to do anything but take delivery of the goods.
There is a whole emerging industry based on RFID, and it, in turn, impacts on almost all other industry sectors. The industry is driven at its heart by the military and intelligence community with the help of corporations who are part and parcel of the NWO elite, as defined by the makeup of their directors and other corporate leadership or ownership. What they want to do with RFID is mind boggling, as is what RFID is capable of in terms of invasion of privacy. To start, they want every single product manufactured and sold to have its own unique RFID tag, and are pitching it to manufacturers and retailers as the next evolution of bar code.
Similar chips in credit cards technically allow purchase without the need to remove the credit card from the wallet, though they currently require us to scan the card. But all that is really be needed is to specify which of several credit cards we might be carrying was desired to be used. That could be verbal, by touch screen, or smart phone application, which avoids producing the card. RFID is also being built into phones for comparison with credit cards nearby, to allow verbal telephone purchases to be made without the need to verbally confirm credit card details. The bio implant is ‘sold’ to us as a convenience to replace all of that (examples to follow).
That is the ‘convenience’ under which it will be sold to us in the retail world, and if a cash register can scan these chips, so can the device at the door looking for merchandise which had not yet been purchased. Why stop there? Anyone can put small and hidden scanners (with or without cameras) anywhere, and for any reason… such as at every doorway where some form of security or tracking feature is desired. By scanning RFID credit cards, the identity of everyone passing through is logged and time stamped without their knowledge or participation. Actually, any RFID tag on your person can do the same thing (it is being built into clothing), because your identity can be associated with its purchase. And that is just the beginning. Ergo, the national ID ‘Real ID‘ program is based on RFID, and eventually, the human body itself will be its on RFID ‘ID.’
Actual TIAO logo
But it gets worse. For any of this to work smoothly, somewhere, someone needs to catalog and keep all those transaction records and make them available for government’s needs. Enter the Total Information Awareness Office (TIAO), AKA the Terrorist Information Awareness Office. This was modeled after an expanded version of FINCEN (Financial Crimes Enforcement Network) capabilities (check this out); and was MILITARY led and very Intelligence community friendly Defense Advanced Research Projects Agency (DARPA) project. I’ve seen the original DOD call for papers and the final description of capabilities and intended uses for the TIAO, and it has little to do with targeting terrorists. Instead, it has to do with capturing records of EVERY transaction between EVERY citizen and business, as well as the passing of ANY citizen through ANY doorway in selected locations. Further, it will track vehicles past checkpoints and can log other kinds of interactions or transactions between people and each other or real world objects (i.e., machinery, vending machines.)
Everything in this image under Transactional Data, and all the little colored storage systems (the cloud), and Corporate Memory, comes largely from backdoor access to RFID-based data. The red Privacy and Security dotted line was added AFTER privacy concerns, to imply a search warrant would be employed (untrue). Intel data would include access to NSA’s massive global wire tap, as well as all of the other 16 spy agencies of the U.S., and those of friendly nations.
Update: TIAO ‘went away’ due to public protest and ‘too many questions,’ including “Why was the head to be a convicted criminal participant in Iran Contra, an ex Naval officer of significant credentials tied to CIA and the Pentagon, John Poindexter?” And yet, it did not actually go away. It has instead been quietly replaced with the OIA; the Office of Intelligence Analysis, another new super-secret spy agency operated out of Homeland Security. They, in turn, gently established ‘Fusion Centers.’
Fusion Centers are ‘sold to us‘ as a happy pill having nothing to with dark deeds, and as being established by cities and state governments in order to share information between partnering civic and federal agencies, local businesses and NGOs for improved security against terrorism and ‘other threats.’ In truth, they are hotbeds of social spies who operate external of the centers within those groups of partners on behalf of DHS and the intelligence agencies. It is often a source of organized gang stalking, and a collection point of ‘data’ about ‘other threats.’ We are the threats, and the data is obtained through backdoor access to the ‘data’ about us found in participant computers, including RFID transactions, security and traffic cams — and via gang stalking and the associated psychological profiling. It is a kind of fascist Brown Shirt group without the uniform, replaced with a smile and handshake… and big eyes and ears.
And worse still. If government decides it wants to know even more about you, a black van can drive by your home and scan it to collect the sum total of all information from all RFID tags (or Smart Dust) found within the home. They will quickly know EXACTLY what is in your home, where you got it, how you got it, and when. This gives field agents the ability to gain access to that kind of information in a very focused way instead of having to run tedious database searches which would necessarily include bureaucratic handling and, perhaps, the dreaded and feared need for a pesky warrant.
And, worst of all, the ultimate expression of RFID privacy abuse is to put one in the human body, with or without the target’s knowledge. The question is, how close are we to this nightmare, and what can we do about it? The answer is, we are frighteningly close, and in fact, it has already been happening for decades.
What can you do to defend against it?
Aside from sharing this post, not much. Be very vocal and protesting at every opportunity any discovered use of the technology. You might demand RFID tagged merchandise be detagged or the tag neutralized before you leave the store, but that would make you look crazy. However, organizing endless group protests can have an effect. Any firm that covertly uses it should be razed to the ground (sued into oblivion for violation of privacy). Any government office holder should be kicked out of office if they support the technology in any way, shape or form, or simply fail to oppose it. In my opinion, preparation for revolution should be made if these efforts fail, because that would be the only remaining recourse prior to full enslavement.
Back to the bible. In The Book of Revelations where the reference originates, there is also one more clue RFID will be the basis of the Mark of the Beast. One at a time, the Seven Angels open the Seven Seals to unleash seven deadly punishments upon the unfaithful on the earth. One of these states that those with the Mark of the Beast will suffer severe pain and many will perish from it. A subtle clue.
As it happens, there is one feature about RFID which must be told to make sense of this, and it suggests how to thwart the tech: if exposed to high energy radiation, RFID heats up incredibly and explodes. A burst of high energy radiation levels will literally destroy it… such as an intense solar CME blast (Coronal Mass Ejection – a high RF/EMF energy field). At this time, I cannot tell you how to generate such an energy and safely use and aim it, but it has been suggested by other experts than a ten second microwave oven exposure should be sufficient. Now if I just had a portable unit I could waltz through the retail Aisles with… set to ‘Burst’ mode… but you can bet there will be or already are laws written to make that illegal.
But there is something simpler which also defeats the technology. Metal shields the signals. Thus wrapping a National ID or an RFID equipped credit card or object (i.e., chipped hand) in aluminum foil defeats the device’s ability to communicate. When the revolution comes, if that is our future, there will be portable devices which anyone could build from easily obtained parts to detect or destroy RFID at will. I fear the day this is needed. I also say woe to those involved in the use of RFID should it come to that. End excerpted material.
There is one other thing you can do. The response time for reading a scanned RFID is very brief. There is a ‘failure’ in reading called ‘tag collision.’ When too many RFID tags of the same frequency (usually dictated by type of tag/use of tag) are present in a confined space, the scanner can fail to capture the data, or capture the wrong data. Therefore, if one were to collect dozens of RFID tags of various types and put them into a bag to carry along with them, it would effectively become a scanner blocker. Keep all your old canceled credit cards in the same wallet as your valid ones, sandwiching the new between the old, and pull them ALL out to select the one to use, holding them all in the same hand to swipe.
I also advise against Smart Appliances, and smart meters. RFID is at the heart of interaction with Smart Meters, which in turn is its own invasive privacy and stalking threat (widely experienced as a directed energy weapon). Worse, it is tied to mapping of the interior of your home; the floor layout, location of furnishings and other appliances and electronics, smart or otherwise. Programs are being developed to allow such mapping information to be available to manufacturers of smart devices and used to market to you based on use of not just their product, but all products. Naturally, all that can be accessed by government, as well… and hackers partnered with burglars.
I also suggest taking advantage of these resources as contingency against the worst:
How to war with the NWO; How to survive the NWO; and Localized defensive strategies.
The history of RFD tells all
It starts with Howard Hughes, though he was a victim, not an instigator. Most of us are familiar with his rise to being the richest man on Earth in his day, and his fall due to a mental condition which impacted his ability to interact with people, and life in general. The untold story is that once debilitated, CIA agents and Mormons (CIA likes to recruit from Mormans, and Masons, because such cults have secrets and know how to keep them through compartmentalization and other methods) became his ‘caregivers and managers.’ He trusted them, and they took advantage.
Once in control, his vast resources were diverted to CIA control and application. Hughes Shipbuilding built several spy vessels including the Glomar Explorer and companion vessel, both designed to retrieve sunken Soviet Subs. Hughes TWA aircraft and assets were diverted to form (over time) three different CIA ‘airlines,’ including the most recent, Evergreen Aviation, which wound up acquiring Hughes’ Spruce Goose for its museum. Hughes Tools, the financial cash cow of Howard’s meteoric rise, a maker of drilling systems for the oil industry, would eventually become Enron, and we know how that wound up vanishing billions of dollars into thin air. The remnants of Enron’s data processing center would be applied to CIA fronts engaged in porn (to profile user sexual preferences for possible blackmail application), web site hijacking (I was a victim of that, documented here), offshore gambling, and 4-1-9 scams (Nigerian money investment scams).
Then there were Hughes operations which would evolve to serve CIA’s efforts in Political Control Technology development and application. It starts with Hughes Aircraft’s electronics division, eventually become Hughes Electronics, which invented the RFID concept. These were originally used to identify and track cattle, marketed through Hughes Identification Devices, but also found their way into humans involved in early (late 1940s) non consensual CIA mind control projects and Atomic Energy Commission radiation experiments on civilians. I wound up with one in my leg, when as a child, when I was injected with a radioactive substance in Yakima, near the Hanford Energy Reservation.
From Hughes, the chip was migrated to Destron Fearing, and from there to our friend, Digital Angel. We will come back to them. More CIA fronts or partners duped into participation would be created in America and globally to market implants for humans. They do big business in ‘police state’ countries, often for the purpose of chipping persons in the criminal system. Of course, it is privately understood they are good for tracking anyone you wish to track, such as embarrassing political activists and whistleblowers.
LocatePLUS is a Homeland Security created and CIA infected front which pushes the implant in America and advertizes that it maintains 12 billion records covering 98% of the American Population. The DHS/CIA knows all about you and is making money selling you to anyone with the money. In America, the front markets to FBI, ATF, DEA, and 2000 law enforcement agencies, primarily non implant products such as ankle bracelets.
In Europe, the front Worldwide Information is a LocatePLUS spinoff doing much the same. Global reach far outstrips American consumption (there are a lot of fascists out there, in almost every government system): Universal Microchip in Italy, IDECHIP S.A. markets in Ecuador and Brazil, Solusat Medica in Mexico, Scientific Innovation and Integration (SII) in Korea, Taiwan, China, and Japan, Inforlexus Inc., for Malaysia and Indochina, Biometronix for Germany, Glezer Technology in Israel, and Cybertek in Puerto Rico. This list continues to grow; the Swedish firm Biohax International is behind the implant for snacks story.
The primary American front (a sister to LocatePLUS), Metro Risk Management Group, sold $13M worth of chips over 5 years to the Bonneville Power Administration (to track fish, officially). BPA is a Department of Energy firm which had in the same time frame been in the news because of high-tech spying operations having been detected taking place in their facilities… while BPA and Enron were significant others in the same bed. The U.S. Military contracted for $24M, while they sold $1M to private citizens wishing to chip their children or themselves. They sold $7M to the greater Intelligence community, and $73M for ‘internal use,’ which is to say, CIA, itself. Such orders are a combination of implants and scanner systems, both portable handhelds and installable units for security gates and doorways. A typical order might consist of hundreds of thousands of devices and a thousand scanners.
All this data represents 2005-2009. Sales are increasing over time, but increasingly hard to track for a variety of reasons, including corporate name changes, mergers, spinoffs, and other tactics often seen in CIA fronts trying to be a moving target. And the implant business is a target by activists and activist organizations worried about invasion of privacy and civil rights, to say nothing of some kind of New World Order nightmare ending with the Antichrist at Armegeddon. And, they are constantly being sued in court for a wide variety of reasons.
And this brings us back to Digital Angel, the key point in the bioimplant tracking food chain. As stated, a lot of business names and hanky-panky tactics are often employed by CIA fronts, as outlined in The Professional Paranoid, a privacy/security how to which, in covering that topic, helps readers to identify who is really causing the bumps in their night, should they be so unlucky (as was I). So let’s take a look at Digital Angel, again based on older ten-year research (I’m not going through that, again).
Let’s talk corporate names as clues: though most commonly known as Digital Angel (Florida), also DBA Verachip, they were formerly Applied Digital Solutions… which was formerly Applied Cellular Technology (because RFID tracking often relies on cell phone services)… which also used the DBA ACT Financial… formely Axiom Information Technology… formerly Axiom Computer Consultants… DBA Great Bay Acquisition Company (those all based in Wisconsin/Minnesota). Digital Angel divorced itself from Verachip (being sued out of business), but then Verachip merged with Steel Vault… which became PositiveID, which then in turn tried to acquire Digital Angel… which also operates Signature Communications in the U.K., where it might (conjecture based on company data and ties to CIA fronts) enjoy backdoor access to encrypted government radio communications, the assumption being that receiving units employ an RFID chip which, like the cell phone paradigm, authorizes descrambling of transmitted data, as well as authenticated identification of the sender and recipient. Finally, Digital Angel, also being sued and hounded, ran off to the U.K. where they now promote themselves as “a developer and publisher of consumer applications and mobile games designed for tablets, smartphones and other mobile devices, as well as a distributor of two-way communications equipment.” But they still push implants, and through Signature, the two-way communications gear.
Let’s talk facts as clues: Digital Angel does not make RFID. No. They merged with Destron Fearing, the actual imputus of modern RFID systems claiming to have invented RFID technology. No, that was Hughes Aircraft’s Electronic Division. Digital Angel at one point claimed to be founded in 1948. No, but Destron Fearing was founded in 1945, did the RFID for cattle thing in 1948. No one cited so far, actually makes RFID tags, the heart of the implant. No, that’s Raytheon, a military/CIA contractor… formerly known as Hughes Aircraft. That makes sense, since it is the U.S. Army which tracks all RFID tag assignments (unique tag number assigned to (whatever) user data). Meanwhile…
Let’s talk connected dots as clues: CIA’s HHMI (Howard Hughes Medical Institute) is steadily pushing for the use of RFID in both implant and non implant versions to hospitals (49 major facilities as of 2005, more every year) and the medical industry at large, and Hughes Satellite and Hughes Communications services RFID tracking systems via cellular/wifi. How do I know this? By temporarily working for both Hughes Satellite and a major cell phone carrier where I was able to verify specific cell phone traffic and routing of tracking data. The phone account was tied to an individual which shared an address with one of the above firms (how I found it). And that led to finding dozens of such phones for more firms. And even more looking at other fronts known to me outside of the RFID playing field. In fact, such details are part of my evolving insurance policy against ‘accidents.’
Let’s talk key people as clues: Another CIA front trait has to do with who is involved in the corporate structure. At ADS (old data) Dr. Richard Seelio was Director of Medical Applications. Really? He is a Bariatric Surgeon, so he knows how to suck fat out of your thighs, not exactly as advertised by his title (a typical front man). The Senior Vice President was, prior to installation, a small time lawyer (a cutout man). A look at the Board of Directors of almost many of the above firms variously will find persons of wealth and influence, persons with backgrounds or ties to military/intelligence (or both), and persons with membership in the nefarious NWO Round Table Groups, such as the Council on Foreign Relations, Trilateralists, and the Bilderbergers. This is a kind of corporate structure is a fingerprint that lets anyone track just who are the trackers.
The other shoe drops
As I wrote this, I was listening to radio, where Clyde Lewis more thoughtfully reviewed a greater enveloping matter on his Ground Zero show, things equally important to understand, and far more sinister. Listen to it, here. The short of it is that chipping people is not just about spying on them, it is about control. It will enable a complete rewrite of social, political, religious, and economic existence, and the script is already being followed step by step, RFID again at the core. You didn’t think ‘Global Warming’ was about weather, or that Transgender Issues were about rights, or that Terrorism was about political or religious ideologies, did you?
It is, all of it, in support of ‘a brave new world’ which the New World Order seeks to establish, a world where there are only three classes of people. While my friend Clyde did not use my labels for these classes, he did so describe: there will be Meons (a Club of Rome/Bilderberger label based on an ancient word for someone worthless, less than a peon – a ‘useless eater’ who will not likely survive the NWO on their own, and who will be made to ‘go away’ in time); Peons who will be usefully employed to run the system (government, business) for the elites; and the Elites, the 1% of the 1% who will rule.
Clyde explains how the Middle Class will be eliminated, divided between those willing to implant and deemed useful (peons), and those unwilling or deemed useless (meons), and the a host of new topics and proofs you have likely never heard of, and more. Naturally, the upper class will be peons, and the lower class, meons. Bio implants (part of Transhumanism) are key to all these plans. You had better understand all of this or you won’t be able to cope, and likely, will end up in the red list for population reduction.
Share this:
Posted in Abuse of Power, Conspiracy, Government, Health, military, Political Commentary, Political Control Technology, Religion, Science, Targeted Individuals, Technology
Leave a comment
Tags: bio implant, Central Intelligence Agency, CIA, DARPA, Department of Defense, Digital Angel, employees implanted for snacks, Homeland Security, Information Awareness Office, New World Order, NWO, personal privacy, personal security, radio frequency identification, RFID, sub-dermal implant, total information awareness office, tracking chip, transhumanism, Verachip