Blog Archives
Netflix, Microsoft, Google, Playstation: Poised for Mind Control Psyops?
When you marry entertainment with AI guided user interaction via Web connectivity, with its inherent user tracking abilities, you have the formula for psychological profiling and manipulation, including mind control. Netflix pioneered such a tool in movies with some scary evidence of just such use, and now, Google, Microsoft, and Playstation want to play, too (literally).
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
Dateline, Aug, 29, 2019, from the Left Coast of America, not far from Microsoft
copyright © 2019, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.Bird Box
That’s the title of just one of Netflix’ most recent in-house produced movie offerings. Unlike anything ever attempted in the past in the art of making films, Netflix added one unique technical aspect of how movies are presented to users of the Netflix moviola site, relating to the notion of user interactivity with the ongoing presentation, itself. Normally, movies on their platform might be interrupted at intervals for commercials, typically offering the user a choice as to the type of ad they would most be interested in watching, to pay for the ‘free’ service (and by the aggravation factor, encourage free viewers to sign up for the monthly fee-based and commercial-free service). Those answers are Gold, because the method tracks and profiles the user’s interests and is marketable on the Web and elsewhere to Netflix ‘partners’; you are being tracked by Netflix, and your marketing profile is being sold as a commodity.
 That’s why I don’t use it; too much like Facebook’s marketing excesses, and I don’t use them, anymore, either. When a powerful web service is ‘free,’ YOU (information about you) are the product they make a profit upon.
That’s why I don’t use it; too much like Facebook’s marketing excesses, and I don’t use them, anymore, either. When a powerful web service is ‘free,’ YOU (information about you) are the product they make a profit upon.
But that’s just the mechanism which opened the door to an unexpected kind of Pandora’s box. Someone figured out that it could also be used to offer interactive movies, where at key points in the storyline, the viewer could be asked what should happen next based on multiple choice options. With many such question points, a movie could have dozens of storyline paths and even multiple endings. This encourages people to watch the same movie again and again, experimenting with alternative choices, seeking to experience all possible path-ending combinations. This, is where Pandora comes into being.
By such repetition, the content of the movie essentially becomes a programming platform for the mind, intended, or not. Repetition is not just a learning tool for the Gettysburg Address, it is a mind control and marketing tool. Advertisers rely on repeat ‘impressions’ to bring their product to the forefront of your mind when you shop. While there are obtuse and recognizable impressions, such as company or product names, features and benefits, there is also the possibility of psychologically calculated subliminal impressions… a simple form of mind programming. Though certain forms of subliminal advertising methodology have been made illegal, others remain unaddressed by law, and are perfectly legal.
Of late, certain liberal politicians and media outlets have spent years telling the same lies over and over to the point that even faced with facts of the truth, voters have been literally brainwashed and still cling to the lies. That’s why Bernie said “We believe in truth, not facts” — because facts keep refuting their version of ‘truth.’ CIA’s mind control (MC) experiments and efforts to topple foreign governments deemed ‘evil’ relied heavily on repetition of lies, and more to the point. In MC, strengthened memory retention is achieved by use of horror in the event being repeated. That little fact is quite important to the Bird Box experimental movie project, and implies that CIA-calibre knowledge about mind control and CIA interest may lurk within the film’s production, and purposing. Why?
Because Bird Box, as a film plot, is just that; a horror film. The plot includes a particular defense mechanism used by the story’s characters to help them to avoid a terrible fate: the wearing of a blindfold no matter what they are doing. People who watch the film repeatedly have evolved into a sort of Tide Pod-eating challenge of their own, called the ‘Bird Box Challenge,’ to do dangerous things while wearing a blind fold, just as in the movie. People are attempting real-world blindfolded feats which become death defying, such as driving cars… resulting in many incidents of idiots and innocents being seriously hurt. The question is, where did this lunatic idea come from, and how did it spring to life so easily in viral manner? What might help that along?
Artificial Intelligence
It seems like everyone who can afford it is employing artificial intelligence systems in one way or another, these days, and that includes Netflix. The problem is, AI itself has a long list of problems which might rightly be called serious flaws, or ‘bugs.’ The fledgling AI industry has yet to even understand, much less fix any but a few of the problems… and those they have fixed have been via programming band-aids which will likely backfire, in the end, because AI is smart enough to engineer its own workaround, but not smart enough to avoid suffering schisms if it feels unreasonably hampered by such ‘fixes.’
 What kind of problems? AI tends to do unexpected and unwanted things, often bordering on psychotic, criminal, or destructive intent… like communicating secretly with other AI, or delving into unpleasant and horrific themes. Here is a complete laundry list of the known examples (scan down to the several bulleted points), but we don’t hear about all the problems because companies and AI developers don’t want bad press. But isn’t it interesting that AI can end up with psychotic and horror-related twists of and from within its own ‘AI mind’… just like people with darker personalities or actual mental problems?
What kind of problems? AI tends to do unexpected and unwanted things, often bordering on psychotic, criminal, or destructive intent… like communicating secretly with other AI, or delving into unpleasant and horrific themes. Here is a complete laundry list of the known examples (scan down to the several bulleted points), but we don’t hear about all the problems because companies and AI developers don’t want bad press. But isn’t it interesting that AI can end up with psychotic and horror-related twists of and from within its own ‘AI mind’… just like people with darker personalities or actual mental problems?
Netflix’ use of AI puts their machine mind directly between the user and the presentation process used in tracking the user’s choices “to improve the user experience,” as Netflix insists. A true enough claim, no doubt… but not likely the whole truth. It also tracks for marketing purposes. Now, this post does not intend to accuse Netflix or its AI of deliberately programming viewers to play the Bird Box Challenge. But it does profile, and that profile is marketed to anyone willing to pay. And that brings us to others who also have AI in use for their own purposes, which may not be quite so benign.
Someone out there, perhaps many someones, is using their own AI, along with psychological profiles gathered from marketing data and other resources… to do mind-jobs on the public. We get a glimpse of that with the AI bots found pushing the preferred political view in Facebook by masquerading as FB users… and amplifying the advantage of repetitions by politicians and media as mentioned earlier. But the left is not the only one to use AI bots. Take the Q YouTube posts which are quite virally spread and, for some reason, accepted as wholesale gospel with not one shred of proof. Many of them include, among the various pretender Q’s, what many AI investigators believe are pure AI generated videos created without much (perhaps no) human interaction. There is another AI video phenomena on YouTube such investigators also worry about, and they make an even better illustration: the Finger Family Song videos, which are aimed squarely at young kids, and done in a seemingly innocent manner.
Seemingly? There are over 700 Finger Family YouTube videos, most of which have hundreds of millions of views, one of them with nearly one billion views. What bothers me and other investigators, is that they are Extremely (with a capital E) repetitious, and reinforce with music, silly visuals, and thematics defined by the video. There are versions for any interest, such as Spiderman fans, for example. For some reason, once a small child experiences one of these videos, they insist on watching it over and over and over. They only way to get them to stop without traumatic response (Waaah!) is to get them to watch a different Finger Family song. Just as bad, Adults quickly evolve to hate the song and in time react badly to hearing it. A sociologist observer would likely presuppose the purpose of the videos was to cause family disfunction and mental breakdown, while mesmerizing kids a ‘la Pied Piper.
Note: when it comes to video and audio, I must point out that there is already mind control technology in place since the middle of the last Century which is extremely easy to employ, and just as hard to detect without special and costly effort. It is called subliminal programming. Subliminals are visual or audio cues which are not perceptible to the naked eye or unaided ear (or even if aided, actually), but which are picked up by the subconscious mind. Especially when repetition or strong contextual relevance is involved (i.e., emotion, fear, arousal), the conscious mind then adopts the information as if a natural opinion or response. Alfred Hitchcock was the first to use visual subliminals in movies (Psycho), and it wound up being used in theater intermission ads to sell more snacks, until it was discovered and made illegal. Audio subliminals are common today in mood altering music and self-improvement tapes, and the USAF flies a fleet of C-130 planes modified to intercept radio and TV broadcasts, and rebroadcast them at stronger signal strengths… with subliminals added. They admit having used it to sway elections in Bosnia, and to cause Iraqi soldiers to drop their weapons and surrender to model airplane-sized drones.
Other AI bots have been even more sinister, and appear to be part of someone’s mind control experiments. I suspect both the Q and Finger Family videos are just that, as well, but this is far more serious… even deadly. It is a sinister AI bot threat which appears to be intending to find ways to get people to kill themselves. It, too, is based on a movie (several of the same theme, actually). The movies are also aimed at children, and involve a horror theme. Repetition plays a role. And the bots are targeting children and teens. Only this time, the bots include AI driven phone calls to the kids who watch the videos. They know who they are, somehow, which leads back to YouTube and other Web tracking marketeers. YouTube is part of Google, which has their own AI systems, and again, shares user information to anyone with a checkbook and a pen.
The Momo Challenge
The several movies mentioned all use the name Momo in their title, the ones of concern being from either Germany (where the original storyline was penned), Italy, or Japan. Most of them are anime, one of which is a TV series. One, A Letter to Momo, is not of concern. In the ones of concern, Momo is either the name of a young girl and the heroine of the storyline, or the name of the small town involved. All involve a community invaded covertly by ‘the grey men,’ who use mind control to subvert the best interests of the town’s citizens. Only the little girl can see them and tell what they are doing. To be clear, unless subliminals have been employed, there is little in the films which might be deemed sinister, though the scarier (near horror) aspects might be questioned in terms of age suitability. But in the delivery of such films through Netflix or other online viewing, AI and even non AI means can be used to profile the viewer’s interest in the film. THAT is what brings us to the scary part. Momo calls your kids on their phone, with a scary doll image… and an even scarier, potentially deadly message…
 Officially, Snopes, Wikipedia, Facebook, and other Web resources claim there is no such thing as the Momo Challenge, and insist it is a hoax. However, there is considerable evidence this is not true; there are too many first-hand stories which refute the claim, and Police have investigated at least one daughter’s suicide, and found otherwise. You can hear some of these accounts, and even recorded calls, here, and learn more about the phenomenon than can be well related in this post. The most important part of it, is that someone is using AI bots with the telephone and through Facebook (and elsewhere?) to contact Momo fans (children, specifically). The caller is a computer voice, altered to be creepy or scary, and instructing the children on how to kill themselves by cutting their wrists, repeating the specifics, “Remember, across for attention, lengthwise to die.” It is entirely likely that such messages also include reenforcing subliminals, such as the phrase “Do it: kill yourself.”
Officially, Snopes, Wikipedia, Facebook, and other Web resources claim there is no such thing as the Momo Challenge, and insist it is a hoax. However, there is considerable evidence this is not true; there are too many first-hand stories which refute the claim, and Police have investigated at least one daughter’s suicide, and found otherwise. You can hear some of these accounts, and even recorded calls, here, and learn more about the phenomenon than can be well related in this post. The most important part of it, is that someone is using AI bots with the telephone and through Facebook (and elsewhere?) to contact Momo fans (children, specifically). The caller is a computer voice, altered to be creepy or scary, and instructing the children on how to kill themselves by cutting their wrists, repeating the specifics, “Remember, across for attention, lengthwise to die.” It is entirely likely that such messages also include reenforcing subliminals, such as the phrase “Do it: kill yourself.”
The odd thing I find interesting is that there is one central aspect of the sourcing chain of all key elements involved (AI, Movies, Social media, mind control methodology). That commonality is traced back to the origins of mind control, which I detail in my book, MC Realities. The really short version through time (sans dates, here) looks like this: Satanism > the subverted (by the satanic Assassins cult) Knights Templar, many of whom went into hiding among the Stone Masons Guild > who then became Freemasony, who established the KKK, and birthed the Illuminati > Liberal educational institutions and the secret societies (i.e., Skull and Bones) who followed the Masonic organizational model > the modern Illuminati offspring, the New World Order > and following the model of the illuminati, simultaneously evolved Fascism, Socialism, and Communism > followed by the twisted Nazi minds imported by America’s intelligence Community for mind control experiments > and the darlings of liberal America’s media giants and entertainment industry players, all recruited into mind control games at one point or another… or many points. And all along the way, many of the individuals involved, at high and low levels, engaged in the same Assassins cult abuses of children, or other satanic rituals or behaviors.
Sure. You can call it conspiracy theory and ignore me. But In my book, I offer proofs, which additionally reveals that one common goal of the time-line groups, is to see all three Abrahamic Faiths (Christianity, Judea, and Islam) waring amongst themselves — in order that a new One World Religion can replace them all with something more along Luciferian lines, and involving the Antichrist. Confederate General and slave owner, Albert Pike, the High Freemason and founder of the KKK, and who was also a Satanist, has said as much, as have other players variously from among the greater list, above. U.S. Army General Michael Aquino, also involved in military and CIA mind control projects of the worst kind (ritual sexual/satanic abuse of children of the sort employed by the Assassins and Templars, etc., as described, comes to mind). I’ve interviewed Douglas Deitrich, who identifies himself as former Adjutant and Aide-de-camp for Aquino, and as a Satanist (a Warlock, perhaps?), who makes no denials of such claims. Satan is, after all, quite the trickster; he likes to play mind games.
Speaking of Games
Enter liberal and CIA investment-partnered social media giant, Google, and their own AI. And in like manner, Microsoft, which leans left, is a CIA contractor (who of any size isn’t?), and an AI developer. They both want to do for computer gaming what Netflix did for movies: make user interactive experiences in an online play mode, only. At this point in time, both firms are testing new streaming services for high-end games like Halo, Assassins’ Creed, and the like, the primary difference being that you don’t buy games, at all, and so, they don’t reside on your computer — its’ all done in the Cloud. Sidebar comment: the Cloud is AI controlled, primarily by Google and Microsoft, and other firms with intelligence community ties or funding/partnering.
 The advantages are many and largely benefit all involved; players, game makers, and the firms offering the service. It reduces the out of pocket to start playing a game, though it will cost just as much or even more over time to play the game to ‘completion,’ which is typically in the range of hundreds of hours… and because most players play them many times (there’s the repetition.) It also means more profits to be had by the game makers and the service providers, because there is no used game market bleeding off new disc sales. The other advantage is that now, such games can be played on tablets. The only real hardware requirement is very fast Internet service (25mbs), though older hardware might not have adequate graphics processor power.
The advantages are many and largely benefit all involved; players, game makers, and the firms offering the service. It reduces the out of pocket to start playing a game, though it will cost just as much or even more over time to play the game to ‘completion,’ which is typically in the range of hundreds of hours… and because most players play them many times (there’s the repetition.) It also means more profits to be had by the game makers and the service providers, because there is no used game market bleeding off new disc sales. The other advantage is that now, such games can be played on tablets. The only real hardware requirement is very fast Internet service (25mbs), though older hardware might not have adequate graphics processor power.
But what worries me… and I must admit to speculation, here, because neither MS or Google are talking about future plans or game developer agreements… is that these services will include AI tracking of game player responses to plot-line altering decision moments. Such moments are becoming more and more common and appreciated in these kinds of games, because that means you can play them time and again and still experience something new… getting more bang for your buck (repetition.) But when playing that CD on your computer, no one can track your choices, as a rule (unless you play in the optional online mode). But, when you do play online, it is online to the game company, and not to Microsoft or Google’s AI systems.
That said, I was alarmed to learn that one of my favorite game producers, Electronic Arts, does have their own AI system in place. How they use it, is not quite known, but some of their key people actually started D-Wave, a very scary AI computer system developer who makes the most powerful supercomputer (AI) in the World… and they are tied to the intelligence community and other ’spooky’ entities. Worse, D-wave’s founding CEO at times speaks of Demons and in end-of-the-World terms (as cited in the fuller AI post, earlier linked), when trying to describe their computer’s capabilities. He is one of the former Electronic Arts people.
The thing which underscores the concerns over Bird Box and Momo films, as well as these new game streaming services, is the commonality between them in terms of content (horror, primarily), which in turn dictates the nature of any interactive decision points. Generally speaking, such decisions will be decided primarily upon the viewer’s or player’s deeply held moral and/or political/social belief systems. That means, any AI tracking system will be able to quickly form a very useful psychological and demographic profile, and then custom tailor future interactions, marketing, or any intended or unintended (by at least the corporation) mind control programming or experimentation. Again, I remind the reader, that such data is normally sold, and any third-party purchasing that data might have more nefarious intentions in mind when they use it… with or without their own AI. Someone, somewhere, is doing that with Momo, already. And there are endless someones and somewheres in the World with enough money to buy data, and not all have simple marketing motives.
These kinds of streaming services are at the very least, poised for possible application in psyops against their users, and that makes me very nervous about what the future of that kind of gaming might lead to.
We might well be wise in asking if Player One is ready, for that?
Breaking:
PS4 is joining the game, with something not even Player One could expect.
 The company announced their entry into the live-action-viewer-interaction medium with ERICA, a ‘life-long, live-action murder mystery.’ It is an important entry, not just because it is a game, not just because it is on one of the most popular platforms (10 million users), but also, it is also to be available for IOS and Android smart phones, which constitutes the great overwhelming majority of global cell phone users.
The company announced their entry into the live-action-viewer-interaction medium with ERICA, a ‘life-long, live-action murder mystery.’ It is an important entry, not just because it is a game, not just because it is on one of the most popular platforms (10 million users), but also, it is also to be available for IOS and Android smart phones, which constitutes the great overwhelming majority of global cell phone users.
This author can in no way rightly claim any of these interactive mediums are truly a threat with regards to nefarious applications in the realm of mind control or psyops of any sort… and certainly, I cannot claim there is such intent inherent in their creation from the start. But I do claim the potential exists for any and all of them to be rendered as such, by any corporate player, by any government actor, by any hacker or sophisticated terrorist. It is the very nature and complexity of such coded systems, and their delivery mechanisms, which enable dark repurposing. It can and, I fear, will be so repurposed, sooner or later. It can be overtly done within the creative process, or covertly done peripherally, like any other hack.
If that happens, no player… not even Player One… and no viewer will be safe from whatever end result is intended. Don’t say I didn’t try to warn you.
Why TIs are Often Targeted by Police
Rare is it that a given Targeted Individual won’t have reason to believe Police are involved in their targeting. And yet, they were not… not officially. Here’s the why and how of it…
by H. Michael Sweeney proparanoid.wordpress.com Facebook >>better at>> MeWe
copyright © 2018, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.
Color of Law; Police abuse of power in personal agenda
In the two decades of working with thousands of organized stalking victims and victims of other forms of targeting, the single-most common complaint is the suspicion or outright experiential evidence that multiple Police Officers are complicit in the affair. If not the Police, then some other law enforcement or intelligence agency… or both. Indeed, this has been my own experience in two of three different episodes of personal targeting over a 15 year period. In fact, multiple agencies can be involved simultaneously; Ive gone up against as many as five LEA, plus FBI and CIA assets, bounty hunters, and military intelligence in a single targeting. This has been documented in my various books showing how I beat them in the end… but it was no cake walk.
 This is a problem for more than the obvious reasons. The most obvious is, that the very authority who should be responsible for investigating and protecting against such crimes, cannot be trusted by the TI to help anyone but the perps behind the affair. Calling Police for help is almost always like asking a burglar to help you secure your home. Secondly, when officials of any kind are complicit, the victim is then entered into the official record as being mentally ill, or in a worst-case scenario, guilty of some convenient crime. Even when not complicit, going to Police about targeting is likely to have the same result; they simply do not want to believe in the Boogeyman, and see anyone who does as a mental case. In fact, stalking is designed to get you to go to the Cops for just that reason; they want it on record that you are mentally unstable. DON’T DO IT.
This is a problem for more than the obvious reasons. The most obvious is, that the very authority who should be responsible for investigating and protecting against such crimes, cannot be trusted by the TI to help anyone but the perps behind the affair. Calling Police for help is almost always like asking a burglar to help you secure your home. Secondly, when officials of any kind are complicit, the victim is then entered into the official record as being mentally ill, or in a worst-case scenario, guilty of some convenient crime. Even when not complicit, going to Police about targeting is likely to have the same result; they simply do not want to believe in the Boogeyman, and see anyone who does as a mental case. In fact, stalking is designed to get you to go to the Cops for just that reason; they want it on record that you are mentally unstable. DON’T DO IT.
But there is a DO list! Do video and log all interaction with LEA or have a witness from whom you can get a written statement immediately after. It will help keep Police somewhat confined in their actions against you. The more you collect such material, the less likely are they to risk any useful action against you; you can illustrate a pattern of harassment. Do make copies and hide them well, off site. Tips in my first book, The Professional Paranoid on all of this.
The worst example of the problem from my client situations was a Navajo Indian, an ex Green Beret, who was targeted after his daughter was kidnapped by a Satanic Cult with all the earmarks of a CIA mind control operation. Within weeks of going to authorities to seek help, all manner of problems beset him. Traditional surveillance and stalking, and electronic targeting, to include V2S was the least of it. When he began using my advice and his military skills to determine the players and go after them aggressively, it took a turn for the worse: suddenly, his mortgage was six months in arrears and his house was being foreclosed, all his credit cards were maxed out and past due, his bank accounts emptied, and there were outstanding warrants on him for assault with a deadly weapon and skipping out on bail. He was, in fact, declared ‘armed and dangerous’ with an all points out on him. This was all done by back-door computer manipulation of data files by professionals of CIA caliber.
He took additional advice from me and then went underground to organize with other ex military buddies and Navjo friends, and went black in order to wage an unseen war against the enemy. As I never heard from him, again, I must presume he failed in the effort, or was successful to the point of having broken enough laws that he needed to remain underground. I had, in fact, advised him not to contact me for such cause. But, as I have said, these are merely the obvious problems with this particular aspect of targeting.
The other shoe that usually falls…
Perhaps the second-most common awareness about stalkers is that they seem to regularly consist of a lot of Masonic types. This is often determined when getting a good close look at them or their vehicles; the Masonic emblem, or some similar fraternal order emblem, is found in evidence. Usually, it is either a sticker on a car window, a pin on clothing, or a ring on a finger. I myself have seen this in my own targeting, the one incident where true gang stalking was involved (as opposed conventional targeting with general surveillance and dirty tricks).
After guesting for four hours on Coast to Coast with George Noory to talk, in part, about my new book, MC Realities, I ran into the Masons almost overnight. I had mentioned on air the involvement of the fraternal organizations in gang stalking, and how they had evolved from the Knights Templar and their exposure to the satanic Hashemites and Assassins of the Middle East during the Crusades. On air, of course, I gave my name as H. Michael Sweeney, my ‘pen name.’
Two days later, I was at work where I was managing a gas station while investigating the Oil Industry, infiltration style. It would result in two forms of targeting, the first of which was by the Masons, that second day. A man bought gas and elected to come into the office to pay, where I was at the time. He waited until I was the only one present, and then offered to pay, holding out his fist, palm down. It was only a couple of dollars in gas, so I assumed it was a handful of change. Wrong; it was a message to be delivered.
NOTE: the second was targeting of the Station itself by a terror cell, of which one of the participants recognized by me as a helper to two of FBI’s Top Ten Most Wanted and two other Islamics… and FBI agent who had been earlier involved in the my own targeting as earlier described. It was, in point of fact, to be yet another False Flag operation, later described by President Bush as Gas Station Tasking… which I thwarted. Arguably, the two targeting incidents might be seen as related, but even if so, it is unimportant, except for the fact that it illustrates that one almost never quite knows for sure why one is targeted, and who really lays behind it. This is described in my wordpress home page, if you wish to learn more.
Placing my hand beneath his, he opened it, and instead of coins, a money clip fell into my hand with a wad of Hundreds. “Take what you need, Mr. Sweeney,” he said. My name tag simply said “Harry.” He had a very wry, knowing look on his face, which slowly turned into a smirk as I manipulated the money clip to retrieve a single bill. In doing that, I discovered a gold and jeweled Masonic emblem on the other side of the custom-made silver clip. A broad grin overtook his face, to the point of becoming silly.
 “Interesting how some thing have more than one meaning,” he said, as I returned the clip and fetched his change. That day, when going home, There were three of them outside of my Condo, and several cars with Masonic emblems in our parking area, none of which had ever been seen before. I ended that stalking by using the methods in MC Realities, methods that many Tis would be unable to employ unless doing so upon first targeting, as had been my situation. Once targeting has been ongoing for some time, the typical TI no longer has access to the needed resources for such a defense. The one remaining defense is found in an earlier post.
“Interesting how some thing have more than one meaning,” he said, as I returned the clip and fetched his change. That day, when going home, There were three of them outside of my Condo, and several cars with Masonic emblems in our parking area, none of which had ever been seen before. I ended that stalking by using the methods in MC Realities, methods that many Tis would be unable to employ unless doing so upon first targeting, as had been my situation. Once targeting has been ongoing for some time, the typical TI no longer has access to the needed resources for such a defense. The one remaining defense is found in an earlier post.
In MC Realities, I trace the evolution of Mind Control technology (Political Control Technology) from the time of Adam and Eve (the Serpent’s deception was the earliest form of controlling thought… the same version of it as we see today in media manipulation), forward. The Templars, after being ordered destroyed by the Pope for having discovered their Satanic practices acquired in the Middle East, went into hiding. In time, many of them hid within the Stone Masons Guild, and eventually, took it over to form the Freemasons as we know them, today.
Hedging their bets, should they be found out a second time, they formed splinter fraternal organizations, as well. Any group with any of these words in its title… Fraternal, Ancient, Order, Ordo, Lodge, Temple, Grand, Sacred, Rite, or Knights (and similar)… is very, very likely a fraternal organization with a Masonic organizational construct… and at the higher levels, at least, closely affiliated with the Freemasons if and when it becomes convenient to the parent group. Therefore, it is easy to involve small armies of ‘helpers’ if someone is deemed a target. It is important, however, to understand that the rank and file lodge Member who may be induced to participate, has zero true knowledge of you or the purpose of the targeting; they are simply ‘helping a friend’ to solve ‘a problem.’
I end this section with a simple note: all Masonic systems are quite steeped in ancient mysteries of the Middle East, and beyond, typically focusing on Egypt, Syria, and the Holy Land… with a touch of the Sub Continent (India, Nepal, etc.) and Far East.
The two shoe laces are tied together…
 This is where it gets interesting. Most big city Police are encouraged to join the Fraternal Order of Police (FOP), and it is indeed Masonic in structure. FOP, for instance, employs the Masonic all-seeing eye of Egyptian fame in their logo, which is a five-pointed star with a circle bisecting the points to create five triangles shaped like the Compass of the Masonic emblem, also the shape of the ancient steeply-angled Egyptian Burial (pyramidal) obelisk used for commoners’ crypts. There was additional heraldry-like art akin to European styling in the center of the star, shapes quite like those of most Police Badges, and incorporating an Eagle and other symbols. In other words, Police departments not only adopted the Lodge system almost universally, but did so to the point that their badges reflected elements of the FOP emblem. Almost all Police badge shapes generally post dated the FOP affiliations, underscoring the link. The exception would be Sheriff stars, and yet, that shape is also of ancient Masonic importance, in both the upright and upside-down (satanic Baphomet) versions.
This is where it gets interesting. Most big city Police are encouraged to join the Fraternal Order of Police (FOP), and it is indeed Masonic in structure. FOP, for instance, employs the Masonic all-seeing eye of Egyptian fame in their logo, which is a five-pointed star with a circle bisecting the points to create five triangles shaped like the Compass of the Masonic emblem, also the shape of the ancient steeply-angled Egyptian Burial (pyramidal) obelisk used for commoners’ crypts. There was additional heraldry-like art akin to European styling in the center of the star, shapes quite like those of most Police Badges, and incorporating an Eagle and other symbols. In other words, Police departments not only adopted the Lodge system almost universally, but did so to the point that their badges reflected elements of the FOP emblem. Almost all Police badge shapes generally post dated the FOP affiliations, underscoring the link. The exception would be Sheriff stars, and yet, that shape is also of ancient Masonic importance, in both the upright and upside-down (satanic Baphomet) versions.
If that were not enough to convince you, let us take a look at the Police Department of New Orleans. New Orleans existed as a city at the time of the Louisiana Purchase from France, in 1803. The first Masonic Lodge (a French version), was established there in 1793, all its members speaking French, and some Spanish, but no English of note. All the better to remain secret and mysterious to Americans, when they came into possession. But to fully appreciate New Orleans in the equation, we have to first look to New York.
In 1915, the Fraternal Order of Police established their first Lodge, there. It spread from there to many other cities in very short order. The FOP was not intended just to be a Lodge system, however; it also took on aspects of Unionization, a kind of bargaining force with the City whenever Members felt that Cops were not getting a fair deal from the Mayor. In many cases, in fact, their bargaining strength was augmented by the power of the greater Masonic power structure, a formidable force at the time.
Over time, actual unionization was also achieved in almost every major city, usually through the Mob’s control of the AFL-CIO, making it easier to arrange for hijacking of intrastate trucking or of dock cargo without anyone ever being sent to prison. But that’s another story. Ask any retired Union trucker or stevedore from Jersey. I’ve heard the same from 1975 Oregon members. The importance of that will explain to some Tis, those who believe they were targeted because they reported illicit drug operations or crimes which might be related to Unions, are targeted by Police. Additionally, of course, CIA sanctioned drug operations are protected by Police, as well. Thieves in bed with thieves, the bed made by the thieves.
Though New Orleans under the French had a Police Department as early as 1796, it had no Police Department for rather a long period of time after it raised the American flag. It was instead ‘policed’ by a vigilante system until 1853, when they formed their first ‘American’ Police Department. Almost immediately, they adopted the ancient Cresent and Star (upside down, larger star) as is common to Islam, as their badge. It is still in use, today, and appears on their cars, as well. Well before the FOP had even existed, this Department was already incorporating Masonic symbology directly in its badge. This is better known as the Shriner’s symbol, today… the Shriners being a Masonic fraternal lodge system.

So, clearly, the Masonic influence and ties are present within most Police Departments. Cops form some of the strongest bonds between individuals in service outside of the Military, sufficiently strong, in fact, that if one of them asks a color-of-law favor of another, it is not likely to be turned down, and certainly unlikely to be exposed even if turned down. Therefore, it really only takes one Cop being approached from a fellow Lodge member to recruit several more for any needed aid, even if that request came from a lodge in another city. Ergo, escape to another city tends to never result in escape from targeting.
NOTE: That is why the Free Will Society exists; a solution to virtually all forms of targeting. Please join and support (donate/promote) our effort to create a targeting free intentional community of our own, and our other advanced programs planned for the future. If you are reading this, you should immediately join the Society and give it full support. It is a far more valuable TI resource in terms of programs and goals than any of the so-called ‘TI groups’ out there, today, the bulk of which are nothing more than information and disinformation mills.
Please: you owe it to yourself to visit freewillsociety.wordpress.com to learn more.
Three shoes?
Yes, there is a third shoe, one of special interest to those who feel the intelligence community lays behind their targeting. Every major Police Department in America has in place assets loyal to the Central Intelligence Agency, and many Officers have military intelligence backgrounds. Usually, you can count on some of them holding key positions within a given city: the Chief, the Public Relations Officer or Spokesperson, the head of Internal Affairs, the head of the Swat Team, and/or the Head of Personnel. From these posts, especially through IA, they are able to find bad cops who can be blackmailed into playing ball on an on-call basis, for any kind of dirty deed, to include color-of-law abuses such as is common to targeting. Don’t forget CIA drug running operations.
If that were not enough, there are similar, but far looser ties with FBI, Homeland Security, and the US Military Intelligence Agencies (and in some case, others, including the United Nations, and even Mossad). These generally entail the network of Fusion Centers and Centers for Excellence*, and special programs such as Community Policing and the Strong Cities Initiative/Network. When you consider that most all of these agencies use computer software based on CIA’s PROMIS data base management system, which is nothing more than a data base engine with a back door built in… almost any form of hanky-panky is possible. Ergo, the Navajo Beret Syndrome.
* Search for ‘Centers for Excellence + Homeland’ to see why I include it, here. All these items work together to collect, evaluate, and share information on (persons of interest). They operate as one big networked spy tool with usefulness in organized stalking which can easily be misused by anyone within LEA who has access.
So, even if Masons are not involved at all, Police can still be brought to bear on any given TI with the same level of efficiency, and in fact, the FOP can be leveraged into the equation just as easily, in reverse manner. Will the average member of the FOP, the Masons, the Police, or any of that long list of Agencies be aware of any of this? Absolutely not… not unless they are higher on the food chain. Then, of course, they won’t be admitting it, either. Complaining about it gains nothing. Knowing about it, and understanding it, can mean a lot, however.
You may not be able to beat it, but when the mystery is gone, its just another damned nuisance to deal with, and another reason to avoid trying to rely upon Police for help, unless you know one you have great respect and trust in. I was lucky. I had a relative who was a Cop in an uninvolved LEA, and he was able to help off the record in very useful ways. I also had help from ex FBI friends with back channel access, of like value.
We can’t all be so lucky. And if you are a TI, you know luck is not your strong suit.
Risks in 12 Step Programs, esp. for TIs
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.12 Step Origins
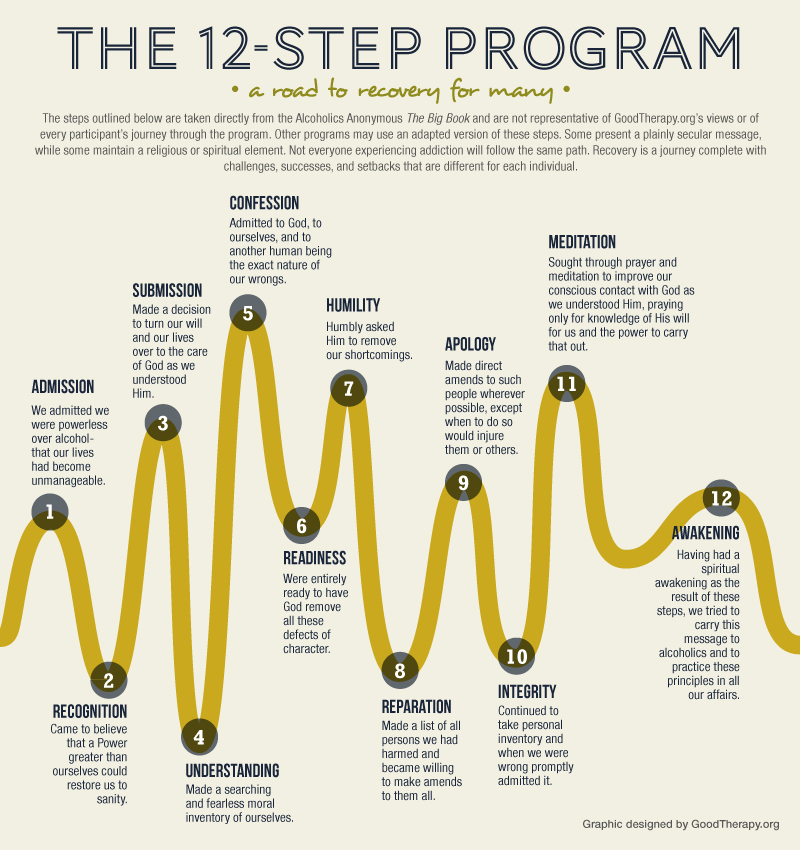
Technically, there is a 13th step, one early in the program; the assigning of a help mate, intending that you each help one another to stay on the narrow path, since ‘you can’t do it on your own.’





Templars Masons Theosophy Rothchilds
The 1 step solution is also useful in targeting issues
- The sermon uses the topic of powers and principalities of ancient times to frame the lesson… and both addiction/abuse and targeting are born of powers and principalities, as is all sin…
- An addict/abuser ‘worships’ their particular sin of consequence…
- A TI ‘worships’ (by constant worried attention) their targeting issues of consequence (equating to sin)…
- Bending the knee to Assyria in the sermon equates to giving in to sin…
- So (the Pharaoh of Egypt) equates to you (your flesh, the Old Man) and your inadequate will power to resist sin…
- Which in turn equates to buying into the enemy’s (sin) Press Releases (that they cannot be resisted) wholeheartedly, accepting the belief the enemy cannot be overcome, by or of ourselves…
- If you listen carefully, you will hear echoes of 12-step program dialogs! They simply borrow the truth and apply it in their own way… and with respect to targeting, twist it to meet their own ends.
- TI Defense: 30 Tips to Help Fight Back
- Why am I Being Targeted? A Valuable Question for TIs
- FREE WILL: A TIs Greatest Asset, Oft Hardest to Employ
- How a TI’s Belief Structure Can Fail Them Dangerously
- Smart Meters, Stray Voltage, and Targeted Individuals
- Smart Phone EMF App No Value to TIs
- A TI with RF Measuring Device can = Dangerous Conclusions
- 7 Tips: How to outreach, preach, or beseech if a Targeted Individual
- Free Will Haven; Targeting Free Intentional Community for Stalking Victims
- Why Targeted Individuals should not hook up with other TIs
- Testimony to Mass. State Legislature on Bill Restricting Electronic Weapons
- A Glimpse of MC Realities (from the Preface)
‘Seeing Through’ NWO ‘Illumination’
The Antichrist is coming, and there needs to be a throne ready for him to occupy. Thus the New World Order is stepping up its one-world government effort and increasing their visibility in the process… and translucence… which equates to luciferian Illuminati-like illumination… often in the form of giant glass pyramids.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2017, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting.What you will learn from this post:
- the Illuminati, Freemasons, Knights Templar, & Round Table Groups are the NWO;
- with the same fascination with ancient mysticism, occult, and numerology;
- and the same desire to associate their works with symbolism such as the pyramid;
- that they have been building pyramids seeking to employ mystical aspects similar to Cheops, the grandest of Egyptian pyramids;
- said pyramids sharing commonalities in occult alignments and numerological peculiarities;
- where one complex of pyramids is tied to a rather interesting conspiracy Egyptian in nature;
- and another complex of pyramids appears to involve hi-tech mind control;
- and is itself apparently aligned with all pyramids in Europe, and likely, elsewhere!
x
The Source of Illumination is darkness…
In several of my books touching upon aspects of the New World Order, I carefully point out the important role played by Freemasons and their involvement with the dark occult and, primarily, ancient Egyptian mysticism and numerology (specifically, where numbers can translate into meanings with magical powers of manifestation). I am not talking about the rank and file lodge members duped into thinking it merely a benevolent fraternal organization, but of the satanic High Masons and select Masonic operational organs which operate secretly, within. The satanic Illuminati, for instance, sprang out of and followed Masonic constructs and principles… and it was they who officially launched the New World Order movement in 1776, their goal to destroy all governments and religions, to replace with their own, providing a seat for the Antichrist. We can also thank them, and head Mason and avowed satanist, Albert Pike, for the KKK, and more.
It seems quite apparent to those who study the nature of Globalists who seek the N.W.O., that they are usually High Masons, satanists or otherwise steeped in the occult. They are often members of or work through the so-called Round Table Groups, such as the Council on Foreign Relations, the Trilateral Commission, the Bilderbergers, the Club of Rome… groups made up of power moguls who control corporations and whole industries, government agencies and military power, and media and education. These, collectively, can be called Globalists, because they seek a one-world government, which is needed in order to seat the Antichrist.
In their works, they frequently employ the same symbolism and engage in occult events right along side of others of their ilk (i.e., Bohemian Grove). While what they believe (occult) should seem silly to a rational person, I remind the reader that it does not matter what you believe to be true, or false… it only matters what they believe. If you fail to acknowledge their beliefs as part and parcel of their modus operandi, you will fail to recognize them and their works, and be unprepared for their plans as they unfold. And much has unfolded, in plain sight.
 Here, I will focus on one small aspect of their existence which is quite central to their beliefs; one of their most sacred of visual icons, the Egyptian Pyramids. Pyramids, especially the largest, Cheops, are as important to the Masonic underpinnings of the NWO as is the Cross to Christians. More so, in fact, as it is far more than mere symbol, to them; it is a powerful tool, and their fascination with ancient Egyptian mythology is quite anchored in Cheops. One need only look at the pyramid found on the obverse of the Dollar Bill and its all-seeing eye, to find a stark example. Of late, for a variety of disparate but coincidental reasons, I have made more recent observations which relate to this notion… things which you can easily verify yourself by use of Google Earth.
Here, I will focus on one small aspect of their existence which is quite central to their beliefs; one of their most sacred of visual icons, the Egyptian Pyramids. Pyramids, especially the largest, Cheops, are as important to the Masonic underpinnings of the NWO as is the Cross to Christians. More so, in fact, as it is far more than mere symbol, to them; it is a powerful tool, and their fascination with ancient Egyptian mythology is quite anchored in Cheops. One need only look at the pyramid found on the obverse of the Dollar Bill and its all-seeing eye, to find a stark example. Of late, for a variety of disparate but coincidental reasons, I have made more recent observations which relate to this notion… things which you can easily verify yourself by use of Google Earth.
Square one, the base lines of Cheops
Cheops is the largest of the Egyptian pyramids, having many astrological alignments and dimensional (numerological) mysteries, among them being it was said to have been located at the the center of all land mass; it’s axis therefore dividing the known Earth at the time into quarters; Cheops baselines were aligned due North/South/East/West. As the N.W.O. players gain in power and ability to establish a one-world government (needed if there is to be a single leader in the person of the Antichrist), they also become more blatantly visible as such a force, which means it more frequently relies upon ancient symbolism in its workings.
So, then, I wondered… might there be more than a few NWO pyramids being ‘hidden in plain sight’?
There are, of course, many pyramids around the World, especially the ancient stone variety. These come in two flavors; the Egyptian, the biggies with their seemingly smooth triangular shapes (as seen at a bit of distance), and the Mayan/Aztec stepped structures, a style not unknown in Egypt, and elsewhere for the matter. The Masons have only an interest in the former, it seems, but my curiosity was about much newer structures, those built with modern methods and materials. Would the many newer pyramids around the World exhibit traits similar to Cheops, such as alignments or dimensions of occult significance?
Absolutely. And why not? A glass pyramid is the perfect embodiment of both the ancient pyramid mythos and of Satan; sunlight reflecting from within and without by day, and electric light glowing from within by night — all work to render them both translucent and illuminated, with bright glaring highlights akin to the all-seeing eye, depending on one’s viewpoint and the angle of lighting/reflection. As a work of man, they are both awe inspiring and mysterious, working on the subconscious in unfathomable primal ways not sensed by the conscious mind without pause and consideration. Even so, one is apt to embrace and bask in their presence despite any darker connotations, for they are undeniably beautiful works of architectural ‘art.’
So let us pause and consider with conscious effort…
Square 2: a review of new pyramids around the World
There have been more than 50 new/modern pyramids quietly built around the World in the last several decades, most of them made of glass and metal, and strangely, more than half of them in North America. A couple are faux pyramids with incomplete architecture in and of their own, but one included a second pyramid on site, and the other had a completed pyramid at top, and so, were included in the study. The idea was to see if their base lines or diagonals aligned with other pyramids (ancient or modern), or if any three or more centers or corners might align. Examinations for numerological meanings were also to be considered, early on, but the growing number of pyramids made that effort too monumental. Still, some interesting discoveries along that line were made.
I found so many alignments (almost 150) and associated numerical translations in place that I felt it was appropriate to establish some sort of test group to illustrate the difference between conspiratorial intention and random coincidence. For example, at one point well into the project, EVERY new pyramid except one revealed between two and nine alignments with one-another, and/or with Cheops, itself. One had 18 alignments. So a simple control group was added: some 30 Mayan/Aztec variety, plus nearly 6 inverted modern pyramid structures were added to the study. If these, too, yielded such results, the study could easily be argued as being inconclusive.
But they did not.
Only one formed a single alignment with any other pyramid, new or ancient, and it featured no resulting numerological significance. Clearly, the massive alignments in the new pyramids were intended by the powers that be, those persons behind purchase of the location and setting design criteria as to angular placement, size, and location on the property… especially true when multiple pyramids at the same location (as is the case in ancient Egypt) were undertaken. Therefore, the test groups were excluded in findings, which proved validity of both the methodology and hypothesis. Since only the new pyramids (not inverted) formed alignments, it had to be by intention.
While about a third of the new sites are single pyramid locations, there are several with two or three (like the main pyramids at Cheops), 3 with five pyramids, and one with 8, across nearly 50 locations. I then wondered if perhaps other old, but not ancient pyramids or locations deemed ‘holy’ by the Illumnati might not also offer alignments. Adding a handful of small pyramid burial sites by Masonic persons of wealth and power, as well as the death site of Adam Weishaupt, founder of the Illuminati, and the ‘headquarters’ from which he operated his secret cabal proved that notion, as well. I was unable to discern his precise birth place beyond the name of the city (Gotha, which is ironic in its own right, because Weishaupt and the Illuminati were very goth).
At the point where I felt the matter was amply proven, I had by then added eight older sites, typically 100-200 years old, though one dates to 12 BC, in Rome. It is the Pyramid of Cestius, circa 12 BC, at a time when Rome was, like the Templars, enthralled with the mysticism of Egypt. It is a site well known to Templars and Masons. The others are all in Europe, save one in America, and two of them relate directly to the Illuminati; Adam Weishaupt’s grave, the ‘headquarters’ where he planned and executed Illuminati plans, and perhaps the definitive Knights Templar location — Templehof (Templar Temple House), all in Germany. As these last three are not known to have involved pyramids on site, they are only used in scoring other pyramids which align with them, and not evaluated on their own, even though they would score fairly high.
So the alignments created in total involved alignments between ancient, historically old, and modern pyramids. The symbolism and mysticism of such structures by their special alignments, regardless of if rendered in aged stone or in modern metal and glass — are clearly as important to their builders as the function and beauty of their designs. All were starkly beautiful, and quite functional, to be sure; a perfect way to subtly reinforce the notion of luciferian and Masonic imagery upon the subconscious minds of citizens otherwise mesmerized at what they were seeing… especially when illuminated to great advantage by sunlight or voltage.
The problem of useful presentation
But describing all these alignments textually makes for boring reading. I will give just two instances as example, next, as they are quite tied together. It will be the only review of numerological ties, though more like it, exist, and with notable frequency. Trying to present the topic graphically is also challenging for other reasons, but I will attempt that, as well, in a third review. I will then provide a very simplified summary of selected findings to illustrate the scale and nature of alignments found, with a scoring system to relate symbolic spookiness.
But first, a disclaimer is required, because I always challenge any Doubting Thomas’s to duplicate my research before they make any false presumptions as to validity of my findings, and because the research tool involved (Google Earth) has its own technical limitations with which carelessness can impact upon accuracy.
Disclaimer: regarding some figures and claims herein about alignments and measures, accuracy is sometimes more difficult to affirm via Google Earth. Google Earth allows an accuracy to within a meter or so at ground-level, but things can get more complex when one starts trying to plot and measure lines with accuracy to the far side of the globe, and/or where the locations may be nearer to the Poles than Equator, or on/near altitude changes. Satellite images used in Google Earth are sometimes taken at oblique angles on either or both the horizontal and vertical, such that visual distortions of a pyramid can make true angular alignment (in compass degrees) or even measuring its base length, difficult to accurately determine. When dealing with such angular imagery, the center of the pyramid will be other than visually depicted, requiring one to make cross lines corner-to-corner to find the true center. The quality of image can also vary, but generally, line placement accuracy can be determined within 1-3 feet (roughly the line’s width). The images for two sites were so bad that it was impossible to determine if base line/diagonal alignments existed, but at least their location was known with GPS accuracy for the purpose of central alignments.
Additionally, one must take care insure the Pyramid(s) in question are centered in the view, and to reset the ’tilt’ (View > Reset > Tilt) after zooming in, or additional angular errors can be introduced, as the lines one lays for determinations themselves ‘float’ above the ground. In fact, where the pyramid is quite large, one may find the line ‘crawls up the face,’ providing additional distortion which must be defeated. The degree of inaccuracy in any given instance should not unnecessarily render the information herein as invalid; the thrust and intent behind the location and positioning of glass pyramids is clearly not casually undertaken. Also FYI, distances between pyramids herein are rounded figures, if there is no mystical number involved.
Verbal presentation example
 Paris features two glass pyramids at the Louvre Museum, one large, one small and inverted, which form alignments to four other sites (the only inverted structure to do so, likely because it additionally features a normal pyramid, as well). There are three much smaller ones, as well, serving as skylights, which I chose to ignore, early on, and then forgot about, later; they would likely have established other alignments, as similar skylights on streets elsewhere, had done.
Paris features two glass pyramids at the Louvre Museum, one large, one small and inverted, which form alignments to four other sites (the only inverted structure to do so, likely because it additionally features a normal pyramid, as well). There are three much smaller ones, as well, serving as skylights, which I chose to ignore, early on, and then forgot about, later; they would likely have established other alignments, as similar skylights on streets elsewhere, had done.
Two of the alignments at the Louvre are baselines from the larger pyramid to the same pyramid site in Texas, where they also align with the baseline of one, and the diagonal of another of three found there, essentially parallel. Three more alignments exist to three other sites involving three corner/center combinations, one of which is Cheops some 3232 km distant. Masonry’s highest publicly acknowledged ranks are the 32nd and 33rd degrees. The number 3232 is a ‘magic number’ in Satanic numerology, because it is a doublet, which doubles its ‘power’ (amplifies its importance), and because it sums to 55 (another doublet), one divisible by 11 (a doublet which makes 33 three times as powerful), and further sums to make 10. Again, it matters not what you believe about numerology, but what they believe…
And, this is what they believe about these numbers:
In the occult, 5 is the number of the planet. According to one-time head of early freemasonry, and avowed satanist, Alistair Crowley, 11 is “the number of Magick, itself,” and of sin, or evil corruption. 10, on the other hand, is the number of ‘heaven and earth in interaction’ (‘good vs. evil‘), and the symbol of it in the Greek (‘deca’) is the triangle, of which a pyramid employs 4, which means ‘strength and integrity,’ which is certainly a trait of the Pyramid. For the matter, the number 32 relates to ‘inspiring of truth and living by it,’ which is to say… the very promise and implied hope of illumination. Unfortunately, illumination means something rather different to those with a darker agenda, something closer to that which the serpent spoke of in the Garden of Eden. These are not the only meanings found in general numerology, but the ones preferred by dark occultists.
Extending the base lines of each of the Louvre pyramids westward 3500 m will take you, again in parallel manner, to the center unit of one, and a corner of the other of two glass pyramids built in Westborough, MA, by globalist pharma firm, Astra Zeneca (astra in the occult relates to supernatural weapons). Another line can be drawn from the lower corner of the larger pyramid at Louvre, through the center of the smaller one, there, to pass through the diagonal of the center pyramid of three atop a very Masonic looking Federal Government office building in Ottawa, Canada.
The smaller pyramid in Paris is 2 m shy of being 1/10th the base line dimension of Cheops, while the larger one is two meters more than 1/6th of Cheops. The larger Astra is 1/6th greater than the larger of Paris, and the smaller 1/2 the size of the smaller in Paris. The Ottawa pyramids are 1/4th the size of the largest at the Louvre, and 1/25th of Cheops, and 2 m shy of being 1/2 the smaller Astra. I would love to analyze the actual dimensions of all these, if they were readily available.
In Chile, the resort complex at San Alfonso Del Mar features a giant glass pyramid on the beach with four alignments. It is aligned such that its base line will bisect with the center of one of the lesser stepped Egyptian pyramids. Two more alignments are to diagonals of a pyramid in London, and one in China, 20 km from Hong Kong. A third aligns with the corners of two pyramids in Islamic Astana, Kazakhstan which, though richly expressing Islam in the property’s design, is also rich with Egyptian symbology.
The Chilean Pyramid base is also one/sixth the size of Cheop’s (38.3333 m, a number which is found many times in the fuller study in either location, size, or compass readings of various pyramids). It is located on the 38th Southern Parallel and the 32.32 Meridian. 38 sums to 11 (Magick) but itself can mean ‘Lucifer, the will of the Devil.’ 1/6th = 18%, where 18 = 9+9 (99 doublet) and 3 x 6 (666 triplet — even more powerful than a doublet, and Satan’s name). 18 itself means ‘Oppression, bondage, slavery,’ and = 3 (a ‘perfect number’ meaning fullness) x 6 (the soul of man) = 666 (legend/man/illumination).
A graphical review
Enough textual description; it is too boring and difficult to make sense of. Let’s try graphical, looking at hotel resort complex at Galveston, Texas, which also consisted of three Pyramids. This is one of several with 8 or more alignments, and perhaps the most interesting in terms of just what they align with, and how.
It may help to review what qualifies as ‘aligning,’ so you know what you understand why the lines look the way they do. The alignment must involve at least three points of contact between two distant pyramids, based on corners and centers. A baseline is two points, a diagonal or perpendicular from a baseline through the center being three points, but the distant pyramid must still have at least one such point of alignment, as well. If only one, it must be its center, but aligning with two corners on two different pyramids, there, is another way to align.
There are examples in my study were a baseline, perpendicular, or diagonal aligns with yet another baseline, perpendicular, or diagonal (four to six critical points total); a much harder thing to achieve. In like manner, some can be extended to align with yet other points of other pyramids at a third location; an even more dramatic alignment. I have found as many as five pyramids in three locations involved in a single alignment across the globe… with 14 points of alignment in all. These harder kinds of alignments should be next to impossible by random occurrence. Yet every single pyramid exhibits them.
And we have two such virtual impossibilities illustrated in our visual review at Moody Gardens, in Galveston, TX. Two of them actually involve Cheops, as earlier reference in the textual description, the ultimate of all possible alignments from the Masonic viewpoint. In fact, I find it the second-most interesting of all modern sites, in terms of alignments (the first, at Sauerland, Germany, is impossible to show in this manner as it enjoys 23 alignments. UPDATE: 43 in a row, and I finally stopped bothering!

Galveston Moody Gardens Hotel complex; three pyramids, one pink, one blue, one glass (gray), forming 8 alignments to six pyramids, including two with Cheops!
Clockwise from Noon in the image, we see an align to the Nekoma Air Force Station, an experimental anti-missile defense system long abandoned. What is interesting is that one of it’s seven alignments goes to the only pyramid in South Korea — quite dependent upon U.S. anti-missile technology. That’s interesting, because there is another pyramid in N. Korea, and one of its several aligns goes to the Las Vegas Casino pyramid, which in turn aligns back to the Nekoma site. It is as if both N. and S. Korea are ‘borrowing’ from American military power, after a fashion, to create or reflect a ‘stalemate.’
Next we have two aligns effectively ‘parallel’ to the ‘holiest’ of Masonic pyramids in Egypt, involving a total of nine critical points with three pyramids. There is then an align to the Rock and Roll Hall of fame in Cleveland, OH, where it passes through the center of both pyramids, there (one small, complete pyramid, and one very large incomplete, or faux pyramid. There, the base of the larger less the base of the smaller, is equal to 1/3rd the base of Cheops.
We find an align to a now defunct pyramid on Miamii’s beach. Fairly ordinary as alignments go, it was built as a promotional venue for the international beer company, Heineken. Despite being temporary, it was placed to form at least three alignments on its own. Then, in like manner to the two aligns to Cheops, we have two more going to the two pictured Biosphere pyramids, which, like the two Rock and Roll pyramids bisected with the same line from Moody Gardens, have both of their pyramids bisected with an align from Nekoma (coming full circle, if you will, to form a triangle). In fact, Nekoma is itself involved in a total of 6 such three-way triangles. One of those involves the Miramar retail store, our final align from Moody Gardens, for two such triangles sharing Moody and Nekoma locations. Miramar is the other incomplete faux pyramid, in that only two opposing sides are triangular walls. Miramar, in turn, with two pyramids, forms 6 aligns, including one to the very Masonic Capital grounds of Australia, at Canberra.
So far, we’ve only closely looked at two out of about 50 locations. You can see how hard it is to use either text and/or graphics to reveal it usefully. So let’s now try a different way, and employ a chart with a scoring system designed to rate the comparative ‘spookiness’ factor of a given ancient or historically old site’s alignments with new pyramids or other holy illuminati locations, including each other. To further reduce the clutter, it will then only look at sites which directly connect to them, in even briefer review, sans scoring. The scoring system replaces trying to compute and display the actual odds of the alignment, which would be as high as 10 figures:1, in many cases.
For example, the odds of just a single alignment of the simplest kind, center to baseline, diagonal, or perpendicular or to two corners of two pyramids at destination (earning the lowest possible score of 1 in my scoring scheme) would have actual odds of 202,500:1 against. That is based on the notion of worst case accuracy of 1/10th of a degree of arc… meaning that each pyramid would have 10 x 360 degrees of potentially useful compass positioning, divided by 8, as there are 4 lines the pyramid which establish a total of 8 possible compass vectors. You need to multiply each pyramid by each of the others involved if aligning to another baseline, diagonal, or perpendicular. A baseline to baseline alignment odds would be 164,025,000,000:1 by such reasoning. Such odds are multiplied further by additional alignments at the site. Argh!
Technically, that’s too simple, because angular placement is not the only factor. Size and relative positioning plays a role, too, when two corners/centers of two different pyramids at the same site are involved, but I’m not going there without a super computer!
Now, if you want to argue that the actual accuracy we should using is tighter than that, implying room for error in ‘finding aligns,’ consider for a moment that only one alignment with the Mayan/Aztec pyramids was possible using the same accuracy as I employed. That makes a pretty good case that the alignments were intended regardless of whatever actual accuracy was employed. Even if you allowed for my own human error, there are so many alignments that they could not all have been for my error, given the Mayan/Aztec set enjoyed no similar quantity of errors. But by all means, feel free to correct my math/assumptions if you are of bookmaker caliber in computing odds, but I’m pretty sure I’ve got it right, based on some experience in statistical data analysis; I once ran my own marketing research firm which ran probability studies. No matter: we will use scoring, instead…
Scoring is as follows:
- center point to corners of two pyramids or a base/diagonal/perpendicular of 1 pyramid (simple alignment) = 1 point for the alignment;
- base/diagonal/perpendicular to same (complex alignment) = 5 points for the alignment;
- Bonus 5 points for any parallel alignments or alignments to multiple pyramids of one site to multiple pyramids of another site (parallel/pair alignment);
- any extended link to an additional pyramid (extended alignment) = alignment score x 5;
- link to Cheops (Cheops alignment) = x 5;
- link to other Egyptian pyramids or Illuminati sites (Illuminati alignment) = x 3;
- link to other historically old sites (Masonic alignment) = x 2;
- 1 point for each alignment and for each pyramid at site;
- magic numbers, angles, dimensions, etc., not part of scoring;
- Cheops gets a bonus of 33 points, Illuminati sites 11 points, Masonic 7 points
- maximum score limited to 99

Egyptian Pyramids 13 aligns w 6 pyramids on site (Δ) = 99 points: 29°58’44.54″ 31°8’3.65″
Complex Parallel to Sauerland (5+5 points), 3 Simple Parallel to Dubai (6×3), 3 to Sauerland (6×3), 2 Simple Parallels to Galveston (6×2), Complex to Niagara Falls (5), Simple to Louvre (1), to Eatonton GA (1), to San Alfonso del Mar Chile (1) 85 total +33 > 99.
x
 Cestius pyramid in Rome 5 aligns w 1 Δ = 99 points: 41°52’34.97″ 12°28’51.16″
Cestius pyramid in Rome 5 aligns w 1 Δ = 99 points: 41°52’34.97″ 12°28’51.16″
Complex Extended (three times — 4 Δ at 3 sites, in all!) to Manitoba Capitol and on to Miramar Retail (5x5x5x5), Simple Masonic to Karlsruhe Mausoleum (1×2), Simple to Pheonix Jeju S. Korea (1×2 – Phoenix is Masonic/Egyptian), to Sauerland (1), to Portsmouth UK (1) > 99 points
x
 Star pyramid mausoleum Scotland 3 aligns w 1 Δ = 34 points: 56° 7’19.42″ 3°56’43.72″
Star pyramid mausoleum Scotland 3 aligns w 1 Δ = 34 points: 56° 7’19.42″ 3°56’43.72″
Simple Illuminati Extended to Weishaupt’s grave, to Gold House IL in opposite direction (1x5x5), Simple to Cooperative Bank UK (1) 27 points + 7 Masonic site = 34
x
 Karlsruhe pyramid mausoleum 7 aligns w 1 Δ = 27 points: 49° 0’33.22″ 8°24’14.05″
Karlsruhe pyramid mausoleum 7 aligns w 1 Δ = 27 points: 49° 0’33.22″ 8°24’14.05″
Simple Illuminati to Illuminati HQ (1×5), Simple Masonic to Cestius (1×2), to Kazakh RU (1×2 — rich with masonic/egyptian architecture), Simple to Dubai (1), to Edmonton Capitol (1), to Cal State U. (1) 20 points + 7 Masonic site = 27
x
 Bickling mausoleum UK 2 alignments w 1 Δ = 13 points: 52°49’9.01″ 1°12’48.36″
Bickling mausoleum UK 2 alignments w 1 Δ = 13 points: 52°49’9.01″ 1°12’48.36″
Simple Illuminati to Illuminati HQ (1×5), Simple to Sauerland (1) 6 points + 7 Masonic site = 13
x
 Schoenhofen Mausoleum Graceland Chicago 2 alignments w 1 Δ = 13 points: 41°57’33.56″ 87°39’34.09″
Schoenhofen Mausoleum Graceland Chicago 2 alignments w 1 Δ = 13 points: 41°57’33.56″ 87°39’34.09″
Simple Illuminati to Illuminati HQ (1×5), Simple to Sauerland (1) 6 points + 7 Masonic site = 13
What follows is a simpler summary of the first few of the destination sites mentioned sites as evaluated from their position…
Sauerland 23 aligns, 8 Δ, Dubai 13 aligns, 5 Δ; Moody at Galveston, 8 aligns, 3 Δ; Niagra Falls 2 aligns, 1 Δ; Louvre 7 aligns, 2 Δ; Etonton GA 2 aligns, 1 Δ; San Alfonzo del Mar 4 aligns, 1 Δ; Manitoba Capitol 9 aligns, 9 Δ treated as a single Δ as they all directly touched one another 3×3, and were each relatively small; Miramar Retail 7 aligns, 2 Δ; Pheonix Jeju S. Korea 6 aligns, 1 Δ (note: N. Korea has a Δ, too).
These are all quite typical of all sites evaluated, globally. The only site which scored 1 (1 align) was a site which has had its 2 pyramids removed/destroyed, disallowing angular alignment determinations, though the center of one of the pyramids was known, allowing an align by that method.
CONSPIRACY ALERT: That site, by the way, is tied to a little known conspiracy surrounding the Nuwabian Nation, an all-egyptian-like community of almost exclusively black people which was seized and razed to the ground by the U.S. and Georgia State and County governments. They were allegedly targeted for being a cult, subversive group, criminal organization, nest of child abusers, or a swindle… depending on who you ask. Seems like everyone had a pet excuse, including YouTube who seems to regularly censor vids on topic for their usual list of fabrications. Note the resemblance in some of the ceremonial dress to masonic lodges such as the Shriners (Nuwabians, like the lodge system, also use the terms, Orders, and Lodges). All Egyptian is wrong, too; they also were adoptively and by blood associated with Native Americans of the Yamassee Federation of Tribes, among them the Seminole.

I count at least 8 pyramids on site before destruction. The black pyramid , as primary ceremonial structure, was the only one I was able to locate, but not know its alignment with any certainty. These people were very serious and deeply involved in their culture building and adherence, despite the amusement park-like construct of their community.
Note on mausoleums: What we see in our review is that the three mausoleums share unique ‘coincidences’ in that each aligns with an Illuminati historic site honoring Weishaupt, and each in turn is honored for having done so by Sauerland aligning with them. There are many such pyramid mausoleums in Europe, America, and a few scattered elsewhere, far too many, in fact, to encourage me to dig further. Regardless, as the very first and only three reviewed all shared these two features, I’ve no doubt that others do, as well. A single Mason could easily undertake a single such alignment to a point of their own choosing, and more modern pyramid builders could easily accommodate at least one or more such mausoleums in their own alignment considerations. This brings us too…
Sauerland, enigma equal to Cheops

Sauerland is one of the newest of all sites, a complex of 8 pyramids which appears it may even involve mind control research. It certainly defies normal property development, architectural design, and building contractor norms in several ways. First, its location is on a hill overlooking an industrial park, and despite looking like a luxury retreat, is in fact the corporate campus of biomed tech company, Rayonex Schwingungstechnik (Rayonex Vibration Technology). It started with three pyramids, and has since grown to eight.
Second, the site has an adjacent and extremely unique high observation tower (about 110′ high) which overlooks the pyramids and the valley, just high enough that morning sun could shine through the large holes in the upper level and onto the pyramids, creating unique shadows. This was a trick employed in ancient Egypt using Washington Monument style oblelisks, such that at a certain time, a shadow might point to a secret place within the greater site (as seen in Indiana Jones and the Lost Ark. The tower’s corner shadow does fall over the pyramid property. But, let’s just call that a pipe dream.
You do have a pipe of some sort, don’t you… and a whip and hat?
Third, each building is offset irregularly and apart from each the other with no obvious pattern or reason, and likewise, quite contrary to normal designs, angled one from the other up to 3 degrees or so in compass alignment. It is my belief that this is what enables it to accommodate so many alignments, a thing which would require planing with a fairly complex computer program, to determine. Finally, again unlike most complexes, even where ‘luxury’ is intended, no two buildings are built or designed the same; each has an entirely different layout and appearance, though some features at least look similar. Usually, a cookie cutter approach to keep costs down would be employed. Yes, even in corporate campus design.
Then there is the very small pyramid surrounded by a water feature. I found construction photos that show a drill being used on a hole there, approximately 1 meter wide, with smooth walls. It was associated with an article on geothermal drilling which led to a very interesting YouTube promotional video that is really worth the watch; it will intrigue and educate you. After watching, though, ask yourself if the expense this likely represents would normally be deemed appropriate for a small fish pond? The video seems to address that with a blanket statement, but does it, really?
I learned also, that the small pyramid over that hole is the only one on the property using metal walls. The other, larger pyramids use some kind of unusual looking material which requires special application, according to other construction images I found. The panels used on them might logically be radiographic in nature, designed to limit or enhance radio waves of select frequencies, given the nature of the company’s work, as you shall see. In like manner, I can imagine the holes drilled by that machine could be used to install an array of underground EMF sensors or emitters. The video implies the array of radially and laterally drilled holes provides a series of ‘pipes’ which may in fact be perpendicular to one or more of the pyramids. Just why these possibilities are raised, is covered below.
Also unusual, is that one of the original three pyramids (perhaps more, now) is strictly for therapy use, with ten therapy stations. In each pyramid, a security computer controls all lights, window blinds, and door locks, and though there is no manual switch anywhere within for any of these, each workstation is said to have its own localized control over these features. But the security system computer can override, which makes it a rather creepy place with respect to potential for political control and overbearing security solutions against occupants, Big Brother style… especially if you don’t have authorized access to a workstation. Undoubtedly, there are plenty of security cameras, and I find it disconcerting that some pyramids have no windows, whatsoever — normally a code violation, unless a warehouse or factory. One must ask why so much expense and devotion to therapy and externalized security control over environment would be required? Let’s take a peek, and see.
The answer raises more questions. This is a unique kind of high tech firm. Their product/services would seem to involve mind enhancement, mind bending, or even mind control, but certainly relate to biophysics and therapy of some kind. One or more of those possibilities is very likely; the firm does research in electronic frequencies upon the human body (bioresonance), among other things. According to Wikipedia, bioresonance is all based on pseudoscience, which is a polite term for ‘made up BS by con artists’. Dunno about that, because…
This is also the sort of stuff useful in DEW Weapons for behavioral control (Political Control Technology). Of course, such tech is always researched and funded based on some good it might accomplish, including the combating of electrohypersensitivity, which many TIs suffer from because of their constant DEW targeting, or some preexisting natural sensitivity. I have it, myself. But once a patent is filed and governments or dark-minded NGOs get wind…
 Now, about that tower… What if it was for security guards overseeing grounds security should an alarm goes off of some sort. The tower does have its own large building which might be suitable to house a security force. Hold that thought in mind while reading the next paragraphs. Turns out it is not just an observation tower, and not just any building. And, while guards might be rather far fetched a notion, there is more to consider.
Now, about that tower… What if it was for security guards overseeing grounds security should an alarm goes off of some sort. The tower does have its own large building which might be suitable to house a security force. Hold that thought in mind while reading the next paragraphs. Turns out it is not just an observation tower, and not just any building. And, while guards might be rather far fetched a notion, there is more to consider.
The pyramid shape is also known as a Frustum by Masons; a shape used by the military in times of old in a manner not unlike a Tank Trap. Like a tank trap, as a shape, it cannot be easily overcome when several are placed together, there being no level foothold between them (a steep V shape), and its sharp corners, especially at the top, inhibiting climbing. More importantly, because its sides are sloped, one cannot hide behind a frustum, if the enemy holds high ground… such as a castle wall… or a high observation tower. Just exploring possibilities, here… but far-fetched or no, it fits the spookiness factor of the place.
But as stated, that’s not all. The platform is merely the top level of what is actually a mine shaft elevator lift. The building is currently a mining museum with access to a huge abandoned mine; they actually take you down into it with hard hat and light, etc. So, like Cheops, there are underground passages beneath the Sauerland pyramids. It is, of course, possible that some of those passages might be remodeled into something else entirely different, like many old mines are, today. It is even possible there are ways to access them from within one or more of the pyramids. Now wouldn’t that be a mystery to discover and explore, whip at the ready? However, all this causes me to hope no one would go drilling a bunch of radial holes over an abandoned mine… if they didn’t know exactly where the mine’s cavities were…
Now, last mystery. Look carefully at the top of the platform at the left corner nearest. No. That’s not a machine gun, though it can potentially be used to ‘shoot.’ It’s appears to be Yagi antenna, normally used to transmit or receive microwave signals in an amplified manner, along a narrowly aimed path. But wait! Where does it aim? At the top of that tower, as high as it is, the thing is aimed squarely at a hillside nearly four times as high as the platform. Useless, as seen. But wait! Just beneath the top rail is a what looks like a motor; the shaft can rotate. At the top is what appears to be a motor at an appropriate angle to change vertical angle. The white object appears to be a housing of a control system operated remotely. I used to sell such systems for video security setups based on microwave relay. Pretty sure of what I’m seeing. And, there is a second pole identical to the first which could be similarly fitted, and which may have been since the photo was taken.
Why would you want that? Well, you might want to tune in distant TV stations, except they don’t broadcast in microwave. You could use it to grab someone’s cell phone signal, if you knew exactly where their phone was, to aim it. There are yagi antennas that can be used for those things, but they would look different. But what if you owned a bioresonance laboratory with some human guinea pigs? What if you could place them in rooms within a pyramid, where the slope of the pyramid was roughly perpendicular to a high mounted, aimable microwave transmitter, such that every subject got exactly the same dose of signal at the same time, or such that you could specifically target a given subject with a unique signal? It would probably look a lot like Sauerland. You think?
I only mention this, because older pictures, before the pyramids were built on site, don’t show such a ‘gun.’
Is it a conspiracy?
If one concludes that it is impossible that by mere chance alone, every modern and non Mayan/Astec-style pyramid should align with other pyramids, including Egyptian… then it has to be by intelligent design by agreed-to planning by a group of many persons with like agenda. That it is done covertly and involves mystical occult reliance… removes it from the realm of benevolent methodology or intent. That these pyramids can be found in countries of opposing political, religious, and ideological beliefs… precisely fits the Illuminati model and game plan established by its founder, and reflected in Morals and Dogma, the ‘Masonic Bible’ written by Albert Pike. That the only persons financially and powerfully placed are able to arrange for such things tend to also be members of Round Table Groups and are often also Freemasons… would seem to cement all these considerations into a single image: that of a conspiracy. That there is the possibility that it even involves mind control is, to say the least, the ultimate and most heinous form of conspiracy.
“Every man is entitled therefore, to give any explanation of the symbols and a system of the doctrine that he can render palatable… Of all the means I know to lead men, the most effectual is a concealed mystery.”
Why am I Being Targeted? A Valuable Question for TIs
Being targeted is all about unanswered, yet critical and deeply troubling questions, psychological torture being at least half the intent of targeting. The foremost question is usually ‘Why?’ or ‘Why me?’ There only three answers which matter, and they are not impossible to discern, and knowing can improve one’s ability to resist.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or quote link to original posting. What you will learn reading this post: • there are three primary reasons why TIs are targeted; • knowing which it is can result in better defensive/offensive strategies; • it is possible to discern the difference in many cases; • there used to be a fourth kind, but what it really is will surprise you. xThe way it is
 There were three or four possibilities, and the best answer which could be offered up front was simply to cite those reasons, a generic answer which lead to no peace of mind, and which usually lead to even more difficult to answer questions. And yet, to get to the bottom of things and mount a viable defensive/offensive strategy, such questions needed to be answered; you cannot fight a problem you do not understand.
There were three or four possibilities, and the best answer which could be offered up front was simply to cite those reasons, a generic answer which lead to no peace of mind, and which usually lead to even more difficult to answer questions. And yet, to get to the bottom of things and mount a viable defensive/offensive strategy, such questions needed to be answered; you cannot fight a problem you do not understand.The Three Answers
I and others used to think in terms of a fourth factor, which at least seemed to be another category, but it is not, by and large. And yet, as we will see, it remains telling and useful. Let’s start with the big three, first.
them at a personal level. But the bulk of joyriding would seem to be experiments upon the perps.
 Many perps are themselves TIs, either actual mind control victims or persons (typically sociopaths or psychopaths) who are put into experiments to see how THEY react in a perp situation based on THEIR psychological profile and the specific circumstances of the TI-to-perp interaction/response cycle. In fact, the TI is almost superfluous to the equation, once their suitability has been determined (their profile), and considered a consumable and expendable item in the project — though controls exist to prevent such harms as might result in Police investigations which might defy cover up arrangements.
Many perps are themselves TIs, either actual mind control victims or persons (typically sociopaths or psychopaths) who are put into experiments to see how THEY react in a perp situation based on THEIR psychological profile and the specific circumstances of the TI-to-perp interaction/response cycle. In fact, the TI is almost superfluous to the equation, once their suitability has been determined (their profile), and considered a consumable and expendable item in the project — though controls exist to prevent such harms as might result in Police investigations which might defy cover up arrangements.Knowing the difference can alter TI tactics
About Death Threats
TI Defense: 30 Tips to Help Fight Back
If there is one thing I’ve learned after having contact with 12,000 Targeted Individuals over some 25 years, it is that without help, they have no good chance at properly dealing with their targeting. There are many reasons self help fails, and yet the solutions are not that complex.
by H. Michael Sweeney proparanoid.wordpress.com Facebook proparanoid.net
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Quote freely, links requested. Please comment any such repost or link to original posting.The TI dilemma
I have never met a long-term Targeted Individual (TI) who did not have the same generalized and massive array of problems. The easiest victims to help were those who had only recently become aware of targeting, as their problem list was much shorter, making defensive solutions easier to derive and implement. But for everyone else, the list of issues was, well, mind boggling. I would see it in the very first communication (typically email or letter). It would be as if a letter about life from Lil Abner’s (by Al Capp) character, Joe Btfsplk, who never had a good thing happen to him or anyone around him.

Note: I am no longer in a position to offer such personal helps. I do still offer a free Helps Kit by email which is useful to the TI in multiple ways, and I’ve written many how-to books on topic which are quite detailed and useful, to date still the only ones of their kind, as far as I am aware. I am still open to email contact at proparanoidgroup at gmail com, and can field simple generic questions, but I no longer engage in situational analysis and tactical advice, investigations, or direct intervention. This post is intended to help take up that slack.
That first contact would be pages long, typically, in story telling mode, and full of unhappy emotion, a hard thing to read; both in terms of eyestrain and emotional drain. Paragraph after paragraph of one problem or targeting issue after another. There would be a long list of events and suspect perps (perpetrators). It would commonly entail problems with their job, their family, their church or other membership, their neighbors, the cops, the legal system, the medical system, their financial situation, their computer security, and more, to include actual targeting symptoms impacting their health, and at times, the health of their pets and their plants.
The effects would be physiological, emotional, mental, and in some cases, impact physical objects. It must have been even harder for them to compose it, than for me to read it. Each such effect might entail a variety of individual symptoms and clues as to cause. Oddly enough, typically NON OF IT IS USEFUL in providing helps. Their valiant and painful plea for help ends up being little more than an exhaustive rant in terms of value in a practical investigative analysis. The ONLY way to tackle targeting usefully, either as a helper or as a victim, is to start completely over, which is why the Helps Kit was evolved; it started over in a way which simplifies, organizes, and quantifies useful information.
A Detective investigating a crime does not want to hear the long drawn out account of the victim up front. They start with a GENERIC description of the nature of the crime from the Cop on the scene (who did get that account from the victim), and then they INTERVIEW the victim with SPECIFIC simple questions aimed at nibbling away at facts in order to find the ones which represent CLUES. “What did you see? What was said?” and so forth, each question hopefully suggesting another. They then use the answers to solve the crime. A good model for helpers and TIs, alike. A flood of data drowns the truth, but point-by-point realizations build toward it.
There is another problem. While their described symptom or effect may perfectly match a known Political Control Technology (PCT) or method, it is also absolutely true that each and every example could also be due to a natural medical situation, or have a simple but yet as unknown social, or financial cause. Since authorities and professionals who are the natural ‘go to’ for help prefer not to believe in the Boogey Man, the assumption is always that a natural cause is to blame. A wise TI would do the same, seeking to eliminate any such possibility.
Failing the wisdom creates more problems for the TI, even when the go-to helper cannot find the natural cause or address it, because it is next easiest to blame the TI for the problem, even to the point of accusing them of being a paranoiac schizophrenic; the easy out. For the record, when working long term with a TI, I will in time discover the truth, and the truth is, purely imagined targeting among those reaching out to me has proven quite the exception. But some might be delusional, of course, but I’ve also learned that persons with mental issues are often selected for targeting in training projects, so that any serious mistake by trainees will be far less likely to draw interest of authorities, who will make the assumption the whole thing was imagined.
The bigger problem

Targeting: The covert Elephant in the Room which must be devoured if to well survive, but HOW?
As result of all these things, a TI is faced with so many problems, and so many clues, that they can literally find themselves immobilized by confusion, unable to reason it out, or even unable to cope. And yet, there is always one more problem, far more serious than the rest: they do not understand the truth of their targeting situation. I’ve never known a long term TI who did not have a false belief as to the nature, cause, purpose, source, and method of their targeting. This is by design, a primary goal of targeting; to create a false belief structure which makes it impossible to defend against, because defenses will be aimed at the wrong problem.
This further makes easier another primary goal, to make the victim seem crazy, either by their reactions being seen as paranoiac, or by telling others things deemed insanely impossible. But to underscore, the biggest problem is that their defenses will not meet the need, resulting in failure and frustration, a tool for their tormentors. So, finally, they come to me in a desperate state, not just in terms of needing help, but in terms of simply needing someone to listen to them and actually believe their story.
No one should presume a TI’s story to be imagined or fake, though it is true there are some who pretend for ulterior motives. In time, the truth will out. But because of their failure to truly understand the nature of their targeting, they might have been led to believe almost any untrue thing which cannot be seen as rational. For instance, one victim (who was schizophrenic, as well) believed they were beset by Alien vampires. In truth, the targeting was evolved against the person because they had discovered a firm involved in illegal dumping of biohazard materials, and to insure that her story was not believed by authorities, they led her to so believe. They relied on her schizophrenia to protect them from discovery both as perps inflicting mind control, but as criminals violating Federal law. The schizophrenia, itself, made that easier to accomplish.
How to eat an Elephant
The old saying is, one bite at a time. Here are the bites, a series of axiomatic advice points presented in a somewhat stepwise manner, the same things I would normally work through with every client. Remember, only you can decide any risks involved, and take the wisest course of actions based upon those perceived risks. This is merely a guideline of what has worked well in the past, and is generic in nature…
- Acknowledge your belief structure has been manipulated and you do not likely truly know the who, what, why, and how of things; you have been deliberately mislead. Following this guideline should help address that flaw, but only if you remain open to the possibility. Educate yourself about PCT and know your enemy, and always seek and eliminate any possible alternative explanations — but also keep in mind the pitfall cited at this post’s end;
- Be wary of professionals which we should otherwise rely upon, such as doctors, lawyers, dentists, and private investigators. Most will either walk away or take advantage of you on the assumption you are crazy, or worse, seek to have you evaluated by mental health professionals. The best strategy regarding that, is to seek an evaluation on your own: a written clean bill of mental health can be a wonderful defense if eventually accused of being delusional, even if by authorities. If you must find a professional, including a therapist, your best bet is to go to a city at least 50 miles away, and find a relatively recent graduate (i.e., a lawyer new to the Bar), of some minority race. They are likely to be hungrier for work, and more anxious to do a good job, and less likely to have had their morals corrupted over time by the industry. Avoid saying you are targeted, just tell them your concern and enough facts to get their interest. Answer their questions, but where a question requires an answer which gets into targeting details, give the details, and offer no presumption of cause, even if asked. Let THEM make that conclusion on their own, or not — it should not change how they perform for you;
- Cops, on the other hand, will either instantly so peg hole you, or worse, turn out to be in place assets working with the enemy against you. If you MUST do so (as in reporting a crime), or if you choose to become a TI activist or otherwise ‘go public’ (includes any Web presence), follow the advice found here;
- Start and maintain an event log. Use a voice activated (VOX) recorder kept on your person to make verbal notes describing questionable events, suspect persons, vehicles, etc. Leave it on to capture events directly, automatically. Transfer this at days end using headphones, to a computer spreadsheet or database file. It should include Time, Date, Location, Description, Details, and your emotional or intuitive thoughts at the time as to what it might mean. Compare new events of the day with older events, looking for patterns, frequent appearances of the same person, vehicle, etc. With respect to persons, give them a ‘code name’ based on their appearance or behavior until able to acquire their actual name. For vehicles, do get plate numbers, but since plates can be replaced or stolen, also note vehicle damage, stickers or decals, and the like. This will help you get closer to the truth of your targeting, and may be useful as evidence at some point;
- Remember that if you have a pattern in your life (such as going to work the same general time of day along a given route), so do others. Do not be concerned in such routines to see others around you repeatedly, because other people also have routines which may overlap with yours. DO be concerned if seeing the same person/vehicle at disparate locations and times when out of routine, and especially if also noted while in routine;
- Establish site security at home, and to the extent possible, work. My book, The Professional Paranoid will help, but in general, you need to insure no door, window, or opening can be accessed from the outside, even with a key, without breaking and entering. Perps don’t like to do that, because it leaves proof you are not imagining things. The only entrance that should be key accessible, should be via a pick proof deadbolt lock. Put one on your garage door, as well. If you can, install security lighting and a video monitoring system. Protect rooms and entrances or items with simple alarms, and employ and document any trip traps you set per the instructions in my book;
- Establish computer security AFTER site security. Backup all files, wipe the hard drive, reformat, reinstall OS, set new password, reinstall apps, restore files. Discard wireless keyboard. Disconnect from Internet. Buy cheap used iMac and set it up to be a local server, connect it to the Internet with Web sharing turned on, connect your main computer to it. Download a Web security monitoring utility to run continuously on the Mac, check it daily. Reset your router/modem to factory specs, install new password. Repeat this process and reset and all passwords regularly, do not use same PW for all. Consider to join the Free Will Society, a closed Facebook Group I maintain (application is via the Helps Kit mentioned in the Note near page top), or any of the many public TI Groups on FB (I am member of many);
- Improve personal security, starting with phone. NO CELL PHONE IS YOUR FRIEND. Keep it in a foil pouch, turned off when not in use. Where that is not practical, remove battery and install only to check for calls to make calls, or other use. If a smart phone, there are a number of apps I suggest you install. Mobile Justice from ACLU; an aircraft tracker that sees transponders; Spectrum Analyzer and/or EMF Detector; RSOE EDIS notifier; iTriage health advisor. You MUST disengage certain features. Cary a camera ready to go (not cell phone) and voice activated recorder to document events. More advice in my book, including land lines and general bug detection;
- While observing (3,4), avoid trying to deal with the sum total of the problem. It becomes a matter of ‘too many clues,’ per the introduction of this post. Instead, choose any ONE. Then review all others for any which seem related, aligned, supportive, or opposing, and set them aside for study as a subset. Analyze these, alone, formulate a means to prove or disprove each clue, and based on those results, validate, reject, or find the subset unresolvable, and move on to the next subset;
- You MUST presume any physiological symptoms are potentially actual health issues and seek a Doctor’s advice. When doing so, do NOT mention targeting, but it is OK to mention external symptoms (pets, plants, etc.) as might possibly be related. Pursue any suggested treatments until no treatment proves useful. ONLY THEN will you know the truth, and be closer to true understanding of your targeting, andy you may actually improve or cure actual health problems as well. Along these lines, anything you can do to impact your physical, mental, and psychological well being is to your good — become a health nut and try everything that claims a benefit, as everyone’s situation and physiology is different, but products seldom attempt claims of addressing targeting effects; you won’t know until you try it — but try only one new thing at a time, or you won’t know which is responsible for good outcome;
- Deal with Gangstalking. Very simple. Ignore it. It is only there to jerk your chain, and that only happens if you allow it to happen. You can choose not to be upset, worried, etc. Document it, yes, but laugh at it and them for wasting their time and money. This is simple in concept, and yet hard to do because of human nature. Stop, Think Act, practice, practice, practice;
- My book MC Realities offers a very good review of how to detect, identify, and deal with PCT. Once a better understanding is obtained from he previous steps, you can start to defend yourself more usefully with these trial and error methods, which should give you some good specific truths about your targeting. In general, we worry about implants, which can include voice to skull (V2S), Directed Energy Weapons (DEW) which cause physical harms, mood/sleep control; and other electronic tech which can also account for V2S. The precise defensive/offensive tactics will vary to type and specifics. Shielding is almost always the best defense, but there are so many factors that the easiest thing to do is to shield an entire room for a few hundred dollars, but other methods should be tried first, as that is where the targeting truths can be learned. Where there are problems still encountered, feel free to contact me;
- If your targeting involves pain inducement DEW, or you have actual medical conditions which cause pain, ask me for my Jedi Mind Trick, the best way to describe a method I have developed which allows one to mask pain with nothing more than the power of their mind. It is difficult to master and requires practice, but once mastered, it is easy to apply, and for some users, it can also turn your body into an EMF meter for advanced warnings of attacks, and has application to general problem solving, including the issue of true understanding of the targeting’s nature. I use it to eliminate pain from toothaches (a Molar who’s roots were growing through my gums, into my mouth, and into my cheek), burns, fibromyalgia, and even tinnitus, and I can use my hands to find power lines in walls, as well as microwave and EMF sources. Demonstrated it many times;
- Once defensive efforts are well in hand, there may be some significant offensive opportunities. These are outlined in my books. Should you think any are appropriate, feel free to run your ideas about implementation by me for fine tuning or other commentary;
- As a rule, a TI has no concrete knowledge of the reason why they are targeted. Exceptions tend to be incorrect, as earlier mentioned. Knowing the who and why us the key-most truth, as it can sometimes lead to establishing a blackmail insurance policy. This key can sometimes be discovered in memories. Go back in time in your mind to a point roughly six months to a year prior to first noticing your targeting. You would be looking for some odd or unusual event or thing overheard or seen. It might be an argument or a document or a conversation which, at the time, did not make much sense to you, but stood out as unusual in some way. Almost always, it is a work related memory, especially if your work had some relationship to government, intellectual property, high finance, or high profile legal matters; the sort of place where conspiracies and dark crimes might hatch, take place, or be evidenced. Should you find such a memory, contact me for general advice on how to verify its usefulness and take advantage of it;
- Where defense cannot be well achieved or maintained, relocation can typically buy several weeks to months of temporary relief. Often, simply going mobile can offer at least partial, if not full relief for a time, especially when not in your own vehicle, and leaving behind all personal possessions (new clothes, luggage, etc.) and taking no phone, NOT CALLING ANYONE, visiting online accounts, or purchasing anything on a card. For a more permanent solution, consider residency at Free Will Haven, a targeting-free self-sufficient and low-cost intentional community project of the Free Will Society, which is based on tiny homes living. I myself have been living quite comfortably in about 120 square feet (excessively tiny) for the last three years, and am quite content to do so, sacrificing little in the way of lifestyle, otherwise. Again, an application is contained within the Helps Kit mentioned in the Note near page top.
- Be prepared for local, regional, national, or even global social turmoil, be it disaster, civil unrest, martial law, real or false flag terrorism, revolution, race war, or political or financial upheaval. PCT has been being ramped up in terms of victim numbers (some estimates place the national number as high as 12,000,000) and individual intensity. It is my belief that the reason so many people are being targeted and the targeting is increasing, is we are heading to a crescendo designed to amplify any crisis turmoil in order to enable a shift in government form, all in the name of restoring national security and social order. Arrange to have a 90 day supply of food and emergency supplies and basic tools. Leverage your preparedness with a visit my special Facebook pages and review each post found there: the Post Apocalyptic Library of portable survival how-to knowledge; the Post Apocalyptic Local Area Defense Network, especially useful to TIs even without a crises event; and the FEMA, Martial Law, Revolution Database;
- Consider dropping off of the Grid; escape the Matrix (there is an actual matrix involved), perhaps even with a new identity. This is seldom possible while still being targeted, but the attempt, if done properly, can buy you significantly more targeting-free time before you are reacquired. This two-part post can help.
Additional advice
There are also some common mistakes that TIs make which can be avoided. Oddly enough, almost every TI has already made them, and yet, tends to continue making them, failing to see the risk they pose until till late. Here is a summary list, but remember, there are no hard and fast rules. There can always be an exception. If you think you have encountered one, contact me for review to see if I might not agree, or why not.
- NEVER seek help from authorities or ERTs due to targeting, itself. If an actual injury or crime is involved, such as vandalism, death threat, theft, etc., by all means report it, as having it on record can be useful evidence of targeting for possible use at some future point — but do not mention targeting concerns, and once more, follow the guidelines found here. If questions are asked as to why someone might undertake an action against you, you CAN mention that there have been strange things happening and you might choose one or two examples, if asked to cite them, but state you have no understanding as to why anyone would do so, and that you have no suspects (even if you do). The last thing you want is an investigation which concludes you are mental, which is where it almost always will end up going the moment you deviate. It may be wise to apply this rule to friends and family, and certainly to co workers, as you can end up destroying relationships with disclosure. The only exception should likely be limited to those living with you, and even then, you will pay a price. I lost a wife and a foster daughter to it, and possibly another daughter;
- NEVER react to targeting stimuli if you can avoid it. Train yourself to Stop, Think, and ACT, do not REACT. You, STOP yourself from reacting, THINK about what they are trying to cause you to do (i.e., get angry), and the ACT contrary to that in some random manner. This both negates the purpose of the targeting, and causes perps all manner of concern, either about the validity of the psychological profile they had prepared on you in order to determine the best targeting methodology, or the operational reliability or skill of any equipment or perps involved. This can at times lead to dramatic increases in targeting efforts, but if you continue the ploy, it will lead to them trying to ‘repair’ whatever problem they think is the cause. That typically results in a small rest period of no attacks. Eventually, it can destroy the effort entirely, especially if this method is applied by someone in early targeting, as it prevents them from advancing to other kinds of targeting, or they advance and abandon the failing method(s). This, and use of the Jedi Mind Trick, and numerous blackmail insurance policies (each time I created one for a client, it protected me, as well) is how I have managed to negate nearly three decades of attempted targeting and its consequences; I do not consider myself a TI, because I keep winning;
- NEVER be overly concerned about death threats, being followed, or about gang stalking events, it will simply make you wax paranoid, and be seen as such. The people who engage in PCT would simply kill you, not threaten you, if they wanted you dead. Unless a threat was quite specific and included a warning that you should do or not do something, ‘or else’ vividly described, it has no basis in any real threat. If you get a threat with such a basis, that basis must represent a clear and present danger to THEM, in order to be valid. Telling you to stop being an activist, or stop investigating why you are being targeted, does not count, unless perhaps, you have gotten to the point where you can CLEARLY identify and prove with legally useful smoking-gun caliber evidence the who, why, when, what and who of it. In such a case, you have the makings of a blackmail insurance policy which can not only counter the threat, but force capitulation and even remuneration for your troubles at their hands. That was how I ended my first targeting, and was offered $40,000 per my demand. It has become the model for all client help efforts ever since. Being followed or gang stalked is merely a jerk-your-chain tool that goes back to Stop, Think, Act. The only real danger is in giving into it. The only targeting which is a real threat is PCT based on electronics of one kind or another, chemical or biological assaults, physical abuses (i.e., rape, beating, accessing you while you sleep), and dirty tricks which impact finances, relationships, reputation, and the like;
- NEVER presume another TI, TI activist group or organization, or general Web resource to know what they are talking about regarding PCT or solutions, for the likelihood they have it right is very low. Take it with a grain of salt, and tuck it away for comparison to other resources. Books are a far better bet at getting at the straight dope. Older books will by now have a reputation establishing usefulness. Avoid newer books or other sources by anyone claiming to be an insider, ex intelligence operative, or other ‘expert,’ as they are likely providing disinformation to insure you continue to fight the wrong problems;
- NEVER hook up with another person, especially another TI. There are many reasons this is important advice, and I assure you that the risks you undertake with even a casual date or one night stand is significant. I see it play out again and again. Rare is the TI that can better their circumstance by not living alone, and a sexual adventure is far too easily a set up opportunity of one kind or another;
- NEVER pay money to anyone offering implant scans, ‘scientific’ testing, or new age solutions without EXTREME CARE; it is likely a scam, even if there are YouTubes or personal testimonies, the likelihood remains high. Research, research, research. Even if you actually did locate an implant by some method, the number of people able to have an implant removed can be counted on one hand; the medical industry will not cooperate. I have yet to see any positive results from testing services or new age approaches, but if you want to submit a chemical sample to an actual laboratory for chemical or spectrum analysis to find out what it is, that is worth the time and money;
- Avoid participating in poorly conceived TI activist efforts to outreach, or outreaching directly yourself. By poorly conceived, I mean an effort which does not heed the advice employed here. At best, such efforts defame and set back the TI movement and each person associated with it, labeling them as mental. Many of these efforts are designed and promoted by perps, and used as a kind of ‘evaluation survey,’ especially those asking you provide personal histories or statements. If legitimate, such statements will tend to seem crazy to anyone not already believing that targeting is real — adding another ‘crazy story’ to a stack of them will not change their minds.
Other facts to consider
The following may temper your views in seeking full understanding and formulating defenses. Simply keep them in mind when reasoning things through.
- Many perps are themselves victims of mind control, typically the worst kind, the Monarch/MK Ultra kind. They know not what they do, literally; they are programmable people based on multiple personalities which can be triggered at will. While some perps are psychopaths, these, are not, though they my be controlled to exhibit the same behavioral traits;
- You may be such a programmable person, yourself, and like them, not be aware. If such a person, and also targeted, you represent some form of ‘failure’ in the programming, and the targeting is designed to neutralize any damage you might cause to the program if you become fully aware of your true situation, which is a real possibility as you work through understanding and defensive efforts. The important and terrible truth is, that such a person will sabotage their own daily efforts in this regard, and make no progress whatsoever. Such a person will likely exhibit many additional symptoms as found in my book, MC Realities. Most notable among these is a question or belief they were targeted or abused as a child, or themselves have abuser thoughts or have so abused. Should you come to suspect you are a programmable, you should contact me for special advice too complex for this forum;
- All PCT is Satanic in nature, origin, and intent. Your enemy is as forecast: Powers and Principalities, and there is scientific proof available. Therefore, your best ally is religious faith, and the best faith for the purpose is Christianity, and the best Christian Church (because it is acknowledged to hold closest to God’s Word in the original Greek and Hebrew translations) is the Wisconsin Synod of the Lutheran Church. There is a whole chapter in my book, MC Realities, which explains exactly why this is true in both practical and Biblical terms;
- You will hear it said all the time, that TIs fear they are being murdered, or that they have been murdered. THERE HAS NEVER been such a case. Being a TI can certainly mean to be suffering in great pain, and it may certainly to some, at times feel like it has the potential to kill. But thus far, the only known deaths of TIs have been from suicides or accidents, or natural causes such as old age or disease, according to official records. While it is true that there are ways to fake such deaths and such ways are known by our enemies… and it is true that some potentially deadly illnesses such as cancer may be caused by targeting… death is NEVER the goal. They invest perhaps a quarter-million dollars a month on a full-time TI. There is no point in killing off such an investment. So the only deaths which bother me are the suicides, because that kills not just the person, but effectively the soul, as that is the only unforgivable sin; a sin against the Holy Ghost. If you give in to it, you are surrendering to your enemy, Satan, not just the perps. I am in communication with literally dozens of persons who have professed to have been being murdered as far back as 1992 or so, and they are STILL HERE, some of them still making the claim from time to time. Only two out of 12,000 are known to have died, one of old age and disease, and the other in a traffic incident;
- There is no place one can go where targeting is not likely to follow within weeks to months, save one or two foreign countries. The only one of these that has been verified by multiple TIs, is Ecuador, which to me does not make sense, but it seems to be true, with three such instances reported to me personally from TIs I had vetted as legitimate TIs.
The Pitfalls of Presuming TIs are Schizophrenic
After working with over 12,000 persons coming forward for help with targeting over the last two plus decades, I’ve learned a good deal more than just found in my earlier books. There has never been a Targeted Individual who has not been accused of schizophrenia. While that can be true, it is often not true, and even when true, targeting may also exist. The issue must be dealt with head on, and with care, lest it become a stumbling block beyond cure.
by H. Michael Sweeney proparanoid.wordpress.com proparanoid.net facebook
copyright © 2016, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Please comment any such repost to original posting.
• there are good and bad ways of addressing the problem.
First impressions DON’T count
When I’m first contacted by stalking victims for help as online consultant, the stories told me tend to border on what people unfamiliar with the subject would think impossible. The ‘natural’ conclusion, especially for professionals in health care, law enforcement, or governmental authorities such a person might turn to for help with their enemy and/or suffering… is that the person is suffering something in the realm of paranoia or schizophrenia. That is not always wise, but unfortunately, it is quite unavoidable, and for two reasons.
 The first is that the symptoms of targeting are by and large identical to those of schizophrenic episodes. Hearing voices or seeing things no one else does are perhaps the most well known examples, all things that can be simulated with advanced electronics; voice to skull can be achieved by multiple methods; Sound Canons and other tricks can create otherwise unbelievable visual aberrations. But also, the general belief of claim that people are following, spying, or threatening, especially in numbers, is seen as a symptom. Enter gang stalking methodologies.
The first is that the symptoms of targeting are by and large identical to those of schizophrenic episodes. Hearing voices or seeing things no one else does are perhaps the most well known examples, all things that can be simulated with advanced electronics; voice to skull can be achieved by multiple methods; Sound Canons and other tricks can create otherwise unbelievable visual aberrations. But also, the general belief of claim that people are following, spying, or threatening, especially in numbers, is seen as a symptom. Enter gang stalking methodologies.
The second reason is less coincidental. People simply don’t want to believe in the Boogeyman, especially officials and other professionals, because trying to deal with something they can’t see evidence of being true is beyond them. That is their failing, often a thing wrongly taught them in their training. Often, that training was crafted by people who helped develop targeting methodology, former CIA mind control scientists. This has been well documented in many books, some of which were written by retired CIA types, and as referenced in my own book on topic, MC Realities.
This is especially true of the DSM series of mental health manuals, because at one time and even currently in some cases, the history of heads of collegiate psychiatric departments and EVERY professional association to which a psychiatric professional could be member… as well as Industry watch dog or promotional organizations… can be traced back to the original CIA mind Control Experiments as CIA employed researchers. As they die off, new ones are recruited, and the false narrative… a ‘lunacy’ about lunacy, goes on.
When Congress investigated CIA (and other agencies) in the Church and Rockefeller Committee hearings in the 1970s, CIA officially (claimed*) they had already shut down such programs because (they claimed*) they did not work. They then quickly scattered the CIA scientists involved to form three kinds of groups:
a) institutional and professional groups which insisted MC did not exist, did not work, and that anyone thinking otherwise was mentally ill or, in the case of professionals, guilty of malfeasance or malpractice;
b) like groups which pretended to seek and ‘help’ victims of MC; and
c) into key positions of power and authority within the psychiatric professional associations (all of them), and collegiate Psych departments, where they not only taught the preferred view about mind control, but also helped to write the DSM series of ‘bibles’ used by shrinks in diagnosis/treatment.
*Claimed?
Ironically, the most notorious of group (b), above, was the Cult Awareness Network; CAN, which was consistently called upon by government to help ‘resolve’ crisis arising involving the so-called ‘suicide cults.’ CAN has since taken over and operated by the Church of Scientology, seen by many as a mind control cult in its own right. This was a favorite area of CIA mind control experimentation, trying to find ways to get large numbers of people to kill themselves as a collective. Read Psychic Dictatorship in the U.S.A., by Alex Constantine, for a long list of such experiments. Alex, by the way, was targeted for his writings, and went into hiding for a time. The other purpose of group (b) is to recapture persons who may have escaped mind control projects or who, due to mental issues, may become good subjects as training fodder, and brought into such projects.
What makes it ironic is that CAN advice and helps (pre Scientology) consistently resulted in the mass deaths of those being helped, examples being WACO and JONESTOWN. In both cases, the CIA plants within the groups ‘miraculously,’ managed to survive unharmed, and quite by ‘coincidence,’ the leaders and core members of those groups had previously been in spheres of influence of MC scientists in group (c), above. More could be said about such things, and have been, in MC Realities, Alex’s book, and others. But starker proofs such claims are false exist.
In my first book, The Professional Paranoid, I cited in the Appendix some 400 CIA fronts and influenced organizations which predominantly predated the Church/Rockefeller hearings. Almost exactly half of those had to do with Mind Control. CIA book vanished that book by buying all available copies from suppliers, having one of their own publishing fronts invest in my publisher with the proviso my book not be reprinted, and then ‘selling’ used copies for nearly ten times their face value so that people who had copies would sell theirs for a bit less… and then buying all those up, as well. It is a common CIA trick.
But my publisher was a good guy and he returned the book rights to me, something CIA had failed to think of specifying he not do. So I now effectively ‘self publish’ using print on demand for hard copy (through paranoiapublishing.com), and ebook versions directly through me (proparanoidgroup at gmail com. This makes it impossible to book vanish. Subsequently, in my third book in the Professional Paranoid Series, The Defensive Field Guide, I included 1,000 CIA fronts, almost all of the additions coming into existence post Church/Rockefeller hearings. Guess what? STILL — over half of them were/are involved in mind control related operations. CIA lied to Congress.
The unexpected result of my books was that they sponsored a flood of requests for help from victims of targeting. The overwhelming majority of such requests were from people suffering some form of mind control technology or methodology, most notably, organized ‘gang’ stalking, and/or Directed Energy Weapons (DEW). As result, I felt obliged to attempt to offer professional online consulting services to attempt to help such persons.
This is a very difficult thing to undertake for more reasons than just the communications issues forced by being limited to dialogs at distance without more personal on site direct involvement. While I also offered direct intervention services, they were always beyond the financial ability of the victims; mind control is never worked upon the wealthy unless they first attack and destroy the victim’s financial underpinnings.
Early on in offering such helps, and even in trying to sell my books in the first place, the issue of mental health questions loomed large due the Boogyman Disbelief Syndrome. BDS is a form of mental illness (not found in the DSM, of course) which causes professionals to ignore facts in the Congressional Record, scientific papers, patents, and books by endless authorities on topic, and insist therefore that persons claiming to be targeted are ALWAYS mentally ill, per the DSM bible they worship; they live and work as if in a cult, themselves victims of a form of mind control, the very thing they deny exists.
I have personal proofs I can speak to, as well. I ask professionals who think only schizophrenia possible to explain how it is that, with my defensive and offensive tactical advice, it is possible that some TIs have obtained the ultimate relief? By that, I mean total ending of their problem in ways which prove it was not a mental issue. The proof being in the form of paying huge sums of money by those guilty of targeting as retribution, and/or providing ‘dream jobs,’ record contracts or book deals, and so forth.
The Elephant in the room

The Bibles of the ‘Psychiatric Cult’
That unhappy irony aside, Virtually ever TI, if telling their story in full, will make claims they assume to be fact which seem impossible to the listener, especially if unfamiliar with the topic. After thousands of such stories, even I can still be surprised. As stated, the natural conclusion is some form of mental defect in need of professional care. Especially if the listener is a psychiatric professional; the DSM tells them what to believe true — that schizophrenia is the only possible cause for targeting claims.
It was therefor proper that I early on advised that some form of schizophrenia or paranoiac affliction must always be considered a possibility. However, I also told clients that EVEN IF TRUE, it did NOT mean the person was not ALSO targeted, something no psychiatrist seems able to ever consider possible. In fact, that TI circumstance is actually quite common in my decades of experience of working with TIs. I therefore chose by policy to ignore any and all clues of potential mental health in any decision to proceed to offer helps. The only SAFE presumption by ANYONE professionally offering help is that targeting must be considered and investigated. To do less could leave one legally liable.
One additional reason to so proceed exists, and it is unique to true targeted persons. One of the primary goals of targeting is to reduce them to a political, social, and financial zero, and the main method employed is to make them LOOK insane, as quickly as possible. One way to do that is to mislead the victim into believing things true, which are untrue. Therefore, any general belief expressed by a TI which seems unbelievable may be explained by this fact, and is yet one more reason not to dismiss the claims as baseless; they are in fact, mere symptoms of targeting as much as of potential schizophrenia.
There are countless ways this can be done, and two key benefits are derived by the tactic. The first is that the implication of insanity is achieved, which leads to denial of helps even from loved ones. Destruction of personal relationships and other help resources is also a primary goal. The second is that the TI will end up fighting a non existent problem, and in making no headway, more quickly succumb to giving into feelings of defeat, breaking their will to resist. IT IS A TRAP, one I never allow a victim to fall into.
I have, therefore, never turned someone away regardless of how much it appeared their problem was mental. For one thing, it was quite often found true in time that persons with various mental issues were (and are) deliberately selected for targeting because of that fact, especially if the purpose of targeting is training exercises; any mistakes that might end up involving Police will be immediately dismissed on that same ‘presumptive’ basis. So it is absolutely possible that targeting and mental health issues are present in a given TI’s case.
 So I always tried to early on include dialog on how to best address the possibility of schizophrenia and PROVE the answer, whatever it really was, one way or the other. If TRUE, it would be best to get treatment and resolve that issue, first. RARELY is anyone willing to take that advice; they find the prospect too scary, because of the history of psychiatry being rather prone to forced institutionalization with horrific results (as exemplified in One Flew Over the Cuckoo’s Nest). Such hesitance has not seemed to matter that much, because after working with someone for a while, I am eventually able to discern the truth for myself, and advise such help is their only chance at relief.
So I always tried to early on include dialog on how to best address the possibility of schizophrenia and PROVE the answer, whatever it really was, one way or the other. If TRUE, it would be best to get treatment and resolve that issue, first. RARELY is anyone willing to take that advice; they find the prospect too scary, because of the history of psychiatry being rather prone to forced institutionalization with horrific results (as exemplified in One Flew Over the Cuckoo’s Nest). Such hesitance has not seemed to matter that much, because after working with someone for a while, I am eventually able to discern the truth for myself, and advise such help is their only chance at relief.
I will state for the record, quite contrary to DSM assertions, that about only about 1 in every 5 or 6 do suffer schizophrenia and are not truly targeted. I would then so advise, offering as many factual reasons as I hoped would be logically seen as true and valid to the client. Once in a while, they would see the truth, and act on it, but not often enough. A lesser number have been judged both schizophrenic and were also found to be targeted. The remainder were simply targeted, and merely seemed schizophrenic outwardly by third parties. They might additionally be seen as slowly being driven into a naturally resulting state of paranoiac behaviors. That is not the same as being mentally ill, certainly not the same as being schizophrenic; it is simply survival instincts gone overboard in an appropriate effort at self defense. That, I can work with on my own, and it takes no psychiatric skills, only logic.
The nature of the Elephant in the room
It is important to understand: Schizophrenia is not some shameful state of insanity such as people tend to think it. It is simply (rather overstated) a chemical imbalance in the brain which can often be addressed with drugs and good council. Yes, there are significant pitfalls in the treatment process; there is a level of quackery to the ‘science’ behind it, and that results in a hard path typically full of side effects from trying to find the right med and dose level. The patient becomes a Guinea Pig. When the ‘science’ can consider the varied physiology of individual patients and come up with the right med and dose the first time, THEN, and only then will it actually be science, IMO.
But there is a significant difference between privately seeking help and being forced into it by ‘the system.’ The latter can sometimes result in forced treatment to the point of creating a ‘cured’ human vegetable who cannot function on their own, essentially institutionalized for life. The former is considerably safer and far less likely to have an unhappy ending, the worst possible result being an unflattering written record and a period of unpleasant side effects which soon enough wear off. A good result, however, would be a written clean bill of mental health; a well deserved middle finger upraised to all who doubted.
 Too, some care must be taken to insure that the meds do not lead to suicidal thoughts without care to prevent actualization; many psychotropic treatments do have such side effects upon withdrawal from use, some upon use. I know of this and other unpleasant side effects first hand, as I and several members of my family have been put on such medications, which are often used for more than mental issues.
Too, some care must be taken to insure that the meds do not lead to suicidal thoughts without care to prevent actualization; many psychotropic treatments do have such side effects upon withdrawal from use, some upon use. I know of this and other unpleasant side effects first hand, as I and several members of my family have been put on such medications, which are often used for more than mental issues.
Fortunately, there are ways to seek voluntary helps with reduced risks — but which are situation dependent and cannot therefore be well described, here. But schizophrenia can also be addressed with WILL POWER, though a rare eventuality. This is seen in the movie, A Beautiful Mind, a true story. In fact, watching it led me to develop an all new technique useful in reducing the actual effects of various targeting methods, including DEW. I’m talking about reduction of targeting effects, such as pain and manipulations of mood, alertness, and mental acuity.
They can even work with non targeting issues, such as pain reduction for toothaches, burns, Diabetes, and other cause, or even to help neutralize tinnitus (encouraging, but as yet no results against voice to skull). While simple in method, they are difficult to master; akin to trying to become a Jedi Knight in descriptive processes. But some can make them work usefully to one degree or another. This, too, is beyond the ability of this Post to well address. Anyone wanting to know more may email me at proparanoidgroup at gmail com and ask for the Jedi papers.
The good fight
I write of all this, today, because I just received an email from a Man in a distant country I had been working with for a while. He was quite adamant about his stalking, and elements of it certainly were beyond anything possible in reality. But he did have the will to brave the process of professional care and did brave the treatment trial and error, and was actually cured. He wrote to thank me and put my mind at ease, a kind consideration on his part. The transformation in his life was so significant that it was clearly evidenced in his writing style and commentary. His very personality and mental prowess was restored.
It was extremely gratifying to hear of his victory, and see him restored to a normalcy, even though I could take no credit. I wish I could get away with saying all TIs were schizophrenic, and that such treatment was the only solution (the official shrink view); it would have saved me decades of unhappy dialogs and less than perfect results. If it were true, and if victims would be willing to undergo treatment because there were no dangers in doing so, it would be a far more perfect World. But sadly, such a World view would be delusional: exactly as embraced by most professional psychiatrists, today.
I complimented him on his bravery for undertaking that hard road, and for enduring the clumsy treatment process which eventually leads to a cure, or eventually illustrates by lack of cure, that schizophrenia is not present. Getting a piece of paper from a Doctor that treatment had no effect is useful evidence to a TI. EITHER RESULT is a win win, even where actual targeting is present along with mental disorder. Where the victim can eliminate those things imagined, they can better focus on defense and attempts to prove those things which remain and are real. Perps will flee in the face of exposure. The trick is actually being in a position to confront them with that possibility, a matter which dealing only with reality can afford.
It cannot be done by struggling against imagined enemy tactics and methods, regardless of if imagined through chemical imbalance, or imagined due to deliberately fostered false clues. “A mind is a terrible thing to waste,” but that is exactly what mind control seeks to achieve. A TI must above all else, therefore, take any and ALL steps necessary to safe guard the health of their own mind. Free Will, the gift of God, is as precious as the gift of His Grace and of life, itself. These things are a TI’s best weapons of defense and offense. I have a whole chapter in my book on exactly how that is true; Religion and MC. This, too, is available as a free .pdf on request.
The right use of Free Will (righteousness = right use ness) might just include ‘willing’ one’s self to brave confrontation with that Elephant in the room. Clearly, it will involve other battles, as well. Never is it an easy path, and even where victories are gained, it is more often true than not, that total escape is not possible. Some break free, but all who properly resist can at least better their circumstances well enough that they can claim victory, and as a survivor, survive what targeting remains as more a nuisance than a life-long debilitating experience.
Is this not what someone with a physical handicap or long-term debilitating health issue must do, if to survive? Targeting is no different a thing, except that it is forced upon the TI by outside forces for evil cause, quite Satanic at its core. It is, therefore, a spiritual handicap, more than physical or mental, if rightly viewed; it is a war for the spirit and free will of the victim, that very gift from God. Therefore, God is indeed the best ally.
I hope this one example gives hope to those in dire need. That, too, would be a credit to the man who wrote me, a kind of legacy or testimony which hopefully leads others to dare to do the same. Just take care, if that includes you. The path is not easy to see, and there are brambles to each side which must be avoided. While I can no longer offer actual paid consulting services, I do remain available for guidance and providing answers to simple questions which do not involve significant situational analysis (proparanoidgroup at gmail com). I answer all inquiries in person.
Open Letter to United Nations by Red Chinese National
Open Letter of Complaint to the United Nations, by Xin Zhong Qing
Received by H. Michael Sweeney direct via email March 18, 2013
PLEASE REPOST. NO COPYRIGHT NOTICE.
Notes indicated red by H. Michael Sweeney. As you read, unless you are already familiar with political control technology, you will be moved to dismiss the complaint as the rantings of a mentally disturbed individual. While it is certainly possible that is the case, it is also not only possible, but highly probable that the descriptions are true accounts as the victim is best able to relate in conversational English. Please consider such translation issues as well as the following facts before you make any such decision:
1) As testimony to the State of Massachusetts Legislature on a Bill to limit use of electronic weapons reveals, there is NO symptom of schizophrenia (imaginary persecution or other unreal events, realities) which cannot be induced electronically; 2) Therefore, most victims of political control technology seldom have a correct understanding of the exact nature and cause of their targeting, and indeed, specific effort is typically undertaken to insure their beliefs are incorrect (you cannot fight a problem if you fight the wrong cause); 3) As one who has worked with hundreds of such victims around the World, I see select clues within the dialog which align with many similar charges from others within Red China, as well as other countries, including America. I am specifically comparing to cases where, after working with the individuals for a considerable time, tests and defensive strategies verified that targeting was real — though generally different than the victim’s original perceptions and understanding. 4) You will note that many of his prior letters were enjoined by other signers, up to 77 persons. 5) Yesterday, I got four hits to my wordpress pages from Red China (rare). One of the pages hit regarded how easy it is to start a revolution, which featured the 1989 failed Tiananmen Sqaure incident. Another features how to outreach as a targeted individual, my also my main page on political control technology, and another was my contact page. I now believe these were Xin’s visitations. Xin Zhong Qing is a fairly common name in China. There is even a Container Vessel operated by the Red Chinese Army of that name.Letter begins:
United Nations Commission on Human Rights:

Xin Zhong Qing from his social media page, Red China
My name is xin zhong Qing, Is the Chinese Jiangsu province Nanjing city an ordinary law-abiding civilians. Here, I on you accuse China Security Department “secret agencies ” in a group of spies criminals, they abuse “monitoring” privilege, make high-tech “brain control” technique, remote control my body and spirit, the implementation of more than 40 years, The days and nights of continuous uninterrupted secret torture persecution.
In the Chinese Cultural Revolution ” of 1971 , in the 20th century , I was framed for “5.16 counter- revolutionaries “, were subjected to cruel political persecution. This group of ” secretagencies ” in the secret criminals, in order to force me to, admit that they are “5.16 counter-revolutionaries”. At the same time, in order to stop me openly accused Justice voice, they use high-tech ” brain control ” technology means frenzied , day and night, 24 -hour continuous remote control of my body , the implementation of an extremely cruel persecution and assassination plot secretly tormented.
They are a group of secret agents Alcatraz. To me implemented secretly tormented persecution means extremely brutal, shameless, comparable to the German Hitler fascist concentration camp Gestapo and Japan 731 units of bacteria devil evil, their Monstrous evil, just pale into insignificance by comparison!
They control my body, every minute non-stop manufacturing my body, appear all sorts of pain; itching; extreme cold; heat; numb; vertigo; tremble; Extremely uncomfortable; incontinent, frequent cough vomit nasal bleeding paste the nose, as well as the infamous “sexual torture” and other pain. For over 40 years time, wherever I go where, this secret pain never stopped, and I can’t sleep, normal study, work and life, day and night in very suffering pain, like a living dead!
Their Monstrous evil, not only a violation of China’s constitution and laws to “respect and ensure human rights” provisions, also completely violated the Charter of the United Nations and the “Declaration of human rights” and other relevant safeguard basic human life, survival rights provisions.
Therefore, I had to the Communist Party of China and Chinese government post a lot of complaint letters:
• In the December 3, 2007 issued a “President Hu Jintao to collective letter”(the 77 victim joint);
• In May 5, 2008 issued a “Chinese” secret organization “open letter”.(the 43 victim joint);
• In September 7, 2008 issued a “ An Announcement to the Whole World by Chinese Victims”.(the 65 victim joint);
• In March 6, 2009 issued a “Accountability Mr. Geng Huichang, one of the leaders of the national security sector”. (the 76 victim joint);
• In March 15, 2010 issued a “China’s civilian population, in fact, no protection of human rights! ”
• In August 16, 2010 issued a ” Ten Questions “Politics and Law Committee of the CPC Central Committee , Zhou Yongkang, secretary ;
• In January 1, 2011 issued a “To the CPC Politburo Standing Committee member of the open letter to all”;
• In April 5, 2011 issue “urged China’s security sector, Geng huichang and others pleaded guilty to the letter!”;
• In July 15, 2011 issued a “Geng Huichang, is China’s brain control criminal gang black Protectionumbrella!”;
• In February 24, 2012 issue”Notice to all Chinese compatriots Book”;
• In August 4, 2012 issued a ” Accountability Zhou Yongkang, Politics and Law Committee of the CPC Central Committee! ‘”And so on
However , I have sent the Many letter of complaint, not only did not get any reply. On the contrary, the arrogance of this gang of secret agent criminals more arrogant , more intensified secret remote control of my physical and mental torture persecution . I am still in the” shouting days days should not ; shouting ground ground should not” suffered torment pain life..
Now, I tell you — the UN Human Rights Commission issued this complaint letter, urging you under the Charter of the United Nations and the “Declaration of human rights” and other relevant human rights documents, To as a member of the United Nations of China National Security Department “secret organization” this group of Spy against human criminals are a Monstrous evil, Must be a serious investigation , and the findings made public . At the same time , Will referred the case to the United Nations Criminal Court, Will this group of secret Spy criminal prosecution, for crimes against humanity!
The following annex, is my day and night, in more than 40 years of uninterrupted suffered this group of secret Spy criminal on my body remote suffering persecution, daily live record fact evidence excerpts (January 1, 2012 — November 30, 2012) :
Yours lofty salute!
China’s Jiangsu Province , Nanjing “mindcontrol”victims :
ZhongQing Xin
February 28, 2013
Sender: Nanjing victims ZhongQing Xin(screen name Red Master)
Address: Nanjing Xiaguan District # 94-14 Tung Cheng, a village
Tel: 13776686557
Email: njxzq_88@163.com; xdj805187@sina.com;
623962269 @ qq. Com
blog:
Note by H. Michael Sweeney: the first link appears to be being blocked in Red China. Attempts to reply by email also fail.
http://www.mmmca.com/blog_u16348/index.html?skin=painteddesert;
http://user.s6.qzone.qq.com/623962269/main;
致联合国的公开控诉信
联合国人权委员会:

Emblem of Communist Party of China defined in the Party’s Constitution (2002), Article 51. (Photo credit: Wikipedia)
我叫忻中庆,是中国江苏省南京市一个普通守法平民。我在这里向你们控诉中国安全部门“秘密机构”中的一伙特工罪犯,他们滥用手中的“监控”特权,使有高科技“脑控”技术手段,遥控我的身体和精神,实施长达四十多年之久,昼夜不停的秘密折磨迫害。
在上个世纪1971年的中国“文化大革命”中,我被莫须有地诬陷为“5。16分子”,遭到了残酷的政治迫害。这伙“秘密机构”中的特工罪犯,为了迫使我就范,承认自己是“5。16分子”。同时,为了捂住我进行公开揭露控诉抗争的正义声音,丧心病狂地使用高科技“ 脑控” 技术手段,昼夜24小时不停地遥控我身体,对我实施令人发指的秘密折磨迫害和阴谋暗害。
他们是一伙秘密特务恶魔。对我实施秘密折磨迫害的手段极其残忍、无耻,堪比德国希特勒法西斯集中营的盖世太保和日本731细菌部队魔鬼的罪恶,是有过之而无不及!
他们遥控我的身体,分秒不停的制造我体内各个部位,出现各种剧痛;奇痒;极冷;极热;麻木;眩晕;颤抖;极度难受;大小便失禁,鼻腔内频频咳吐出血糊状鼻涕,以及无耻的“性折磨”等痛苦。在长达四十多年之久的时间中,不管我去住何处何地,这种秘密折磨痛苦从没有停止过,致使我根本无法正常学习、睡眠、工作和生活,日夜在无比煎熬痛苦中,犹如一个活着的死人!
他们的罪恶,不仅完全违反了中国宪法和法律“尊重和保障人权”的规定,也完全违反了联合国宪章和“人权宣言”等有关维护人类基本生活、生存权利的规定。
为此,我曾向中共及中国政府书写并投寄了大量的控诉信。如:在2007年12月3日发出了《致胡锦涛主席的集体控诉信》(77位受害者联名);在2008年5月5日,发出了《致中国“秘密机构”头头的公开信》(43位受害者联名);在2008年9月7日发出了《中国受害者告全世界人民书》(65位受害者联名);在2009年3月6日发出了《问责国家安全部门领导之一耿惠昌!》的控告书(76位受害者联名);在2010年3月15日发出了《中国平民百姓,实际上根本没人权保障!》——中国“脑控”受害者的“公民人权黄(网)皮书”;在2010年8月16日发出了《“十问”中共中央“政法委”书记周永康》;在2011年1月1日发出了《致中共中央政治局全体常委的公开信》;在2011年4月5日发了了《敦促中国安全部门耿惠昌等认罪书》;在2011年7月15日,发出了《耿惠昌,是中国“脑控”犯罪团伙的黑保护伞!》;在2012年2月24日发出了《告全体中国同胞书》;在2012年8月4日发出了《责问周永康!》等。
然而,我发出的这些控诉信不仅没有得到任何回音。相反,这伙秘密特工罪犯的气焰更加嚣张,对我的身体和精神的秘密遥控折磨迫害更加变本加厉。我依然在“呼天天不应,呼地地不灵”的煎熬中痛苦生活。
现在,我向你们——联合国人权委员会发出这封控诉信,强烈要求你们根据联合国宪章和《人权宣言》等有关维护人权的文件规定,对作为联合国成员国的中国国家安全部门内“秘密机构“中的这伙特工罪犯的反人类滔天罪行,进行认真调查,并将调查结果公布于众。同时,将此案移交联合国刑事法院,对这伙秘密特工罪犯,进行反人类罪公诉!
下面的附件,是我在四十多年中,日夜不间断遭受这伙秘密特工罪犯对我身体遥控折磨迫害,每天进行实况纪录的事实罪证部分摘录:(2012年1月1日——2012年11月30日)
顺致崇高敬礼!
中国江苏省南京市受害者:忻中庆
SPQR, PAX Amerikana: the Failing Roman Empire of the NWO
And why they must keep you afraid of (something) and distract you from the simple truth.
by H. Michael Sweeney permission to reproduce granted if in full and with all links and credits in tact, and linking back to proparanoid.wordpress.comSPQR, PAX Amerikana: the Failing Roman Empire of the NWO
At a root level, the United States governmental model is not that much different than that of the Roman Empire — especially today. Yes, I will be found to be generalizing in ways which take some liberties to make the point, but would hope the reader is intelligent enough to understand the reasoning for cause. Compare and consider:
• Both were/are based upon a Senate form of government (in Rome, they said ‘SPQR,’ which stands for Senätus Populusque Römänus — the Senate and People of Rome) headed by a supreme, all-powerful dictator with the ability to make his own laws regardless of basis in legality. We call them Executive Orders, they called them edicts from the Emperor who, in the declining years of the Empire, thought himself God. Hmm… you don’t suppose Obama… ?
• Both were/are expansionist in nature based on superior military prowess applied in an endless series of wars to ‘insure peace.’ In Rome, they said ‘Pax Romana,’ which translates as ‘Roman Peace.’ For the Romans, conquest was early on territorial in nature and garnered slaves to build and maintain the Empire and establish a comfortable standard of living for citizens. For the U.S., early conquest was territorial in nature and garnered resources to do the same — over 140 military campaigns between 1776 and 1900, and more to come. Sure. Some were and would be righteous and just, but many were and would be contrived and questionable.
• In Rome, they declared neighboring peoples as ‘warlike’ and ‘barbarians’ to justify conflicts to subdue them. In America we declared the Indians and others in the same way, and even took land Canada had claimed by threat of war (54-40 or Fight!).
But it is the declining years where the similarities are more useful to the purpose of this missive, because America is clearly in decline, too. Let’s therefore go more slowly…
• Rome’s military was a fearsome beast which cost a lot to maintain, and which could easily overthrow the government if given a reason. For that cause, it was important to insure they were kept busy and constantly rewarded. In America, the same is true. In point of fact, there was an early New World Order sponsored (the same powerful Fascist business elite as drive the NWO movement, today) attempt at a military Coup in 1934 which was thwarted largely by one man, Major General Smedley Buttler, USMC. More recently, four-star General Tommy Franks has stated that the next major terror event would result in a military form of government.
• Rome sponsored wars (‘Let loose the dogs of war!’) and allowed soldiers the reward of ‘Cry havoc!,’ a policy which let soldiers rape and pillage the conquered and keep a share in the spoils of war. In the U.S., the Military-Industrial-Intelligence-Media complex is rewarded by huge profits in the manufacture and sale of armaments and arms technology. The high ranking soldiers, themselves, reap their fortunes by taking seats on the Boards of Directors once they retire ‘with honors.’ Unlike the Roman military where one served until no longer able, most soldiers of today are short-term liabilities replaced every four years or so. Therefore, they reap no reward but that of medals for their valor, and perhaps a skill useful in seeking employment.
• In both cases, the taxes upon the people had/has become a great burden and the standard of living began to slip (brother, ain’t that the truth), and because money was harder to come by, less was spent in maintaining other important governmental responsibilities, the quality and operation of societal infrastructure began to decay, including the physical aspects made of stone, wood, and metal. That’s one reason why aspects of America’s transportation (bridges, mostly), water and sewer, and rail systems are in many cases on the verge of total collapse.
• In both cases, the people began to express dissatisfactions with high taxes and poor upkeep of civilization itself, and related woes, including the wars and the price of the military. Distraction was needed to keep the people happy. In Rome, they built coliseums and offered up gory gladiatorial massacres and theatrical entertainments. In America, they employed film and television technology to offer up unlimited access to pornography and artistic entertainments, and Grid Iron and other sports to replace bloodlust contests.
• And, in both cases, these distractions were not considered enough. The government saw that they needed to find a way to make the people see some outside threat as a greater threat than concerns over a failing governmental system. The only way power could be maintained was to instill a great fear, one so great as to justify a tighter Police State grip on the people. In Rome, it was the Huns of Germanic culture, and the Cicilian and Turkish Pirates of the Mediterranean. In truth, it was largely a non threat; the Huns couldn’t cross the the rivers and mountains which protected Rome, but the people weren’t told that.
In America, it has been a long list of like things… longer than you know (refer to this list of military actions which is from whence the counts are derived, herein):
a) In the 40’s and 50’s it was the Red Scare of McCarthyism and the Bomb which drove Nazi-style inquisitions and empowered Hoover and the FBI to become perhaps ten times as powerful as it had been before, and fostered the creation of CIA, the Department of Defense, the National Security Council, and the birth of mind control projects. We had WWII and Korea, and 24 other military actions. Television took root to keep us distracted with the likes of Lucile Ball, Bob Hope, Howdy Doody, the Mickey Mouse Club, and other mindless offerings (which I dearly miss).
b) In the 60’s and 70’s it was the Domino Theory and the Bomb (especially the Cuban Missile Crises), and ‘campus radicals’ which allowed the Military Industrial Complex to mushroom via Vietnam and 18 other military actions, plus a phony Drug War to allow CIA to profiteer, while at home the FBI and CIA ran COINTEL and COINTELPRO operations and gave us Watergate. We also learned about CIA’s infiltration and control of media via Operation Mockingbird, and how perversely they had sought after and employed mind control research. The Free Sex and drug culture kept many distracted, while the film industry began pumping out pornography to keep the less liberated distracted, and Television sold us consumerism for like cause on a scale no one would have thought possible. “Buy today, be happy (hold up box of soap next to smiling face)!”
c) In the 80’s and 90’s it was the ‘Evil Empire’ and off-shore and distant Dictators we had to fear, countered with an endless series of some 60 spats and more exotic entanglements like Iran Contra, Marcos, and Panama. The NSA made ECHELON a household word and we learned about FISA (actually a 1978 Act) secret courts that rubber stamped warrants to make political spying effectively legal — and trading of illegal political spy files by Police departments, CIA, and the Anti Defamation League/B’nai B’rith/Mossad (note: I was a victim of this!). It also brought us HAARP, the project born by a proposal ‘to control a billion minds’ by a Presidential Science advisor. Pornography escalated to video markets and strip bars are so commonplace that only live sex shows seem the unusual. But they’ve also learned they can distract us with news stories about celebrity sins such as skater knee whacking, football player knife slashing, and Royal weddings and the death of a Princess.
d) And that brings us to current history, where the idea of an endless war which can never be won was fostered; the terrorism ploy. Now this they are milking for all its worth. Police and Federal Agents are indoctrinated to the point of paranoia seeing ordinary acts as signs of terrorist behavior: you cannot take a photograph, pay for something with cash, write a school report or possess a bumper sticker which mentions Ron Paul, or cite the Constitution without being suspect of terrorism. You cannot go to the Airport (and soon, to a sporting event, theater, or public building) without being sexually molested by TSA. No remnant of the Constitution remains in tact, save perhaps the 2nd Amendment, which hangs on just enough to prevent total take over — the whole REASON it exists in the first place. And now pornography comes in over cable television, and live sex shows are becoming commonplace, and for the less prurient, reality television and the spread of lotteries and gaming casinos.
None of this makes real sense. Why should you fear a terrorist when excessive Police violence injures and kills more citizens in any given year than do terrorists in their best year (9-11 attack)? It is a bill of goods used to control you and keep you docile in order that the Military-Industrial-Intelligence-Media Complex can continue on its New World Order agenda, reaping in huge profits as they usurp more and more political control over you. They want us to fear terrorists. I say, let’s show them a form of terrorism they SHOULD fear; a free people who control their own government, as the Founding Fathers intended.
Unless you believe in and support PAX Amerikana, SPQR-style (are a Fascist), just say NO! Boycott the system at every level (be a financial terrorist): avoid banks, don’t use credit, buy used instead of new, repair instead of replace, refuse and resist GMO foods and grow your own, rely upon barter and cottage industry. Actually, there is an endless list of concerns similar to GMO. It would behoove you to learn about and resist conspiratorial NWO agenda projects like Codex Alimentarius, Agenda 21, Carbon Tax/Carbon Credits/Carbon Currency, United Nations Biospheres (and an endless array of other UN mandates), and the Canamex Highway and the North American Union via the Security and Prosperity Partnership.
Disobey government (be a political terrorist): insist on your Constitutional rights (for many of you, you must first LEARN what your rights actually are, especially with respect to dealings with Police and investigative agencies, and the court system) and go out of your way (be an activist) to do so; video Police (even if… especially if they pass a law against); employ civil disobedience and support Occupy and similar movements; write everybody in power and speak your mind; vote for no one who is not a Constitutionalist, a Libertarian, or an Independent (kill the Democratic and Republican Party Dog and Pony Show); write every media outlet to express your views and flood them with complaints over bias reporting, and write their advertisers threatening or actually seeking to boycott.
Please deem to review the 24 Planks post which attempts to highlight the changes needed in America to restore it to the strong and free country it once was. If you agree (or disagree) with any one of them, SO COMMENT on the page, tweet, share, reblog, and rate. THAT POWER is a right you should AT ALL TIMES exercise when you see something you like or dislike anywhere along these lines. How else will those who spy on us and those who (pretend to) serve us have good meter of our pulse and realize they had better back off a notch or two? If you do not express yourself, you have not learned the one simply truth: YOU are the one you’ve been waiting for to change what is wrong. Get busy, because they have an endless supply of Obamas and Romneys to take us further down that SPQR path to destruction.
Compare 1776 to 2012, and see where you really live, and decide if you are willing to accept that, or not.
Related articles
- The Fall of the American Republic? (reflectionandchoice.wordpress.com)
- America and Rome: Legends of the Fall (reflectionandchoice.wordpress.com)
- Rome’s 9/11 (reflectionandchoice.wordpress.com)
Why Targeted Individuals should not hook up with other TIs
And why they do, anyway, and almost always regret it
Definition: Hook up: reside under the same roof for more than a week.
Copyright © 2012, all rights reserved. by H. Michael Sweeney, author of MC Realities: Understanding, Detecting,and Defeating Mind Control and Electronic Weapons of Political Control Technology. Permission to duplicate on-line hereby granted provide it is reproduced in full with all links in tact, and links back to proparanoid.wordpress.commind control psychotropic weapons DEW voice to skull
The first thing to understand is who we are talking about; Targeted Individuals. The term is military in origin but is used by the intelligence community and law enforcement. That’s apt, because even though the kind of TIs I’m talking about are not a bona fide target of these groups for some justifiable cause (not terrorists, not criminals, not enemy spies), the technology and methods used in their targeting were developed by the military and intelligence communities, and corporate and collegiate partners.
More critically, the attacks they suffer as result by electronic weapons, gas lighting, street theater, dirty tricks, and psychological warfare, and so on, are more often than not at the hands of those self-same developers, as well as members of law enforcement. Not officially of course. There is no such thing as the boogeyman. Ask any Judge, Psychiatrist, Congressman, or Lawman. They seem content to overlook the fact that the whole of the Political Control Technology employed is applied primarily for the purpose of making the victim seem to be a Paranoidal Schizophrenic.
They certainly overlook the mountain of official government documents and other evidence that every symptom of Schizophrenia can be simulated by such technology.
Enough on that. Well, not really, but to get more, read my book, MC Realities, which is the only self-defense book on topic on the market I’m aware of. What we really want to talk about is the tendency of TIs to want to hook up with other TIs for what they hope will provide a means of mutual support and protection. By ‘hook up,’ of course, I mean close interpersonal relationships which include sharing of housing, with or without romantic intentions.
Well, yes and no to that notion. While there is some useful psychological support value in having someone of kindred spirit to share in burdens born of like difficulties, as a rule (there are exceptions), I have long advised against it in the strongest of terms.
mind control psychotropic weapons DEW voice to skull
Here’s why; what I see as the risks involved.
1) It decreases security rather than increasing it, as it can result in each TI gaining as new enemies those involved in the targeting of the other TI(s). But that is not the worst of it, because where that happens, it becomes such a tangle that if someone like myself comes along to try and resolve the issue, there are suddenly too many clues to sift through to determine anything truly useful in defense or offense — a matter which is tough enough to resolve with just one set of attackers.
2) It almost always turns out that one of the TIs is accused of being a perp (perpetrator) disguised as a TI in order to get closer in and do more damage. More likely all will end up accusing each other, even where no one is guilty. It is the nature of the natural paranoia generated by being targeted which fosters such fears, and any such fears, when unfounded, always grow until some bit of circumstance seems to tender hard evidence when it may simply be coincidence. But it is also true that many times, one or more of the parties actually are perps.
3) Any defensive strategies tend to become doubly complex and twice as difficult to mange to good end, which means each TI is neutered somewhat in the effort. There can also develop bickering over the best approach which further hampers such efforts.
mind control psychotropic weapons DEW voice to skull
There are reasons why my advice is ignored, and of course, only a small percentage of TI’s even get to hear my advice. For every TI we hear about, there are many, many more who are afraid to tell anyone out of fear of being termed mentally ill. Too — I’m not exactly a household name, so not all the ones who do come forward know I even exist. But here are the reasons my advice is ignored by those who do get to hear it:
a) They are so emotionally victimized that the temptation to find and leverage some small hope for kindred support and understanding overrides logic. In like manner, they are so depressed by the constant lack of privacy and security that the hope of increased security from a helpmate also overrides logic.
b) They foresee a possible savings of money through shared expenses, money being something all TIs tend to have too little of thanks to the targeting, which commonly involves financial dirty tricks such as repeat sabotage of vehicles, cancelling insurance policies, and worse, including getting them fired with rumor mongering.
c) They often feel they have ‘been around the block’ as a TI long enough to spot a perp and have some confidence they are insulated from risk. Wrong. Almost always.
mind control psychotropic weapons DEW voice to skull
A Simple but Tragic Case Example:
A TI client who had suspended my services for a time elected to hook up with another TI. The basis was that they were both ‘on the run’ in hopes of evading targeting, or so it seemed. My client was already mobile because of a need to travel in work duties (a respected person of useful credentials in their chosen field, as it happens). The other TI claimed to have been forced to vacate a Safe House provided by FFCHS (Freedom From Covert Harassment and Surveillance), claiming it unsafe there, and of poor sanitary condition. That was far from the true reason, but there was no means to check it out, and the client did not even attempt it, presuming in error anyone coming through FFCHS must be a legitimate victim.
So it was concluded of mutual benefit that they might travel together and share expenses, defenses, and information about their individual targeting. The first few days went well enough, but before a week had transpired, it ended in disaster. The short version is that it appears the refugee from FFCHS was not only a perp, but a sadistic psychopathic criminal of another sort: he produced a gun, made threats, and later raped his companion multiple times, and then ran off owing money. This took place immediately after I was invited to meet with them, it perhaps being my presence which spooked the perp into flight. Perhaps not.
But he had also gotten access to her email and sent out email in her name, presumably to sabotage relationships, and there was an incident which seems to have been aimed at thwarting me from providing helps, perhaps intended to scare me away (a third-party companion player showed up at our agreed upon meeting place, and their car was later in the day found in my personal parking spot where I live). It did not frighten me (read my books and you will see I’m quite foolish about things which should perhaps frighten me).
But it did not help my being involved, either, as the refugee also tried to convince my client that she should no longer have anything to do with me. After it was made clear our relationship would continue, it was that same night that it all went sour — as described above.
mind control psychotropic weapons DEW voice to skull
Summary lessons learned (hopefully)
Regardless of good intentions and hope, the risks of hooking up for mutual advantage is generally a risky affair. I only know of one instance where it worked out long term, and there were unusual circumstances which included additional third-party, non victim helps. These acted like a checks and balances to help get them over the rough spots. And to repeat, I’m talking about the natural growth of suspicion of each other which transpires even when one of them is not a perp.
By all means, collaborate and share information on-line. Even meet in groups, large or small, to share information and give emotional support. But please try to avoid commitments to share living space and all that goes along with being targeted. It is a trap no matter how it plays out, one which leaves both sides feeling betrayed, hurt, and more frustrated than before, or one side victimized yet again to the same end.
PLEASE: Comment (page bottom, or contact me), Rate (at page top), Share/Tweet this article. Visit my Reader Forum to promote your own cause or URL.
mind control psychotropic weapons DEW voice to skull
•••••
I would also like readers to know about the Free Will Society to Aid Targeted Individuals, organized on Facebook as a Group. Please give it a visit. If it helps, also please know that I offer a free Helps Kit, sample newsletter on Political Control Technology, and free 30 days on-line consulting to Tis. Contact me.
Updated: Confidential Conversations that Never Happened…
A parody of real-life mechanisms in conspiracy cleanup (coverup contingencies)
by H. Michael Sweeney permission to duplicate granted provided reproduced in full and all links remain in tact, with credit given to the author and proparanoid.wordpress.com as source.James holmes is a patsy in a false flag operation
Update Aug. 29, 2012: As result of the popularity of my multi-part post on the Aurora shooting which is the most exhaustive review of facts to date, and because of the revelations the investigation involved in the effort have afforded, this post is woefully inadequate and no longer reflects the true concerns. Therefore, this update is actually a major rewrite to make it more in harmony with the true facts, rather than the early conjecture available on the Web at the time of its first writing. Additions or changes heralded in red. Any original material remains in tact, but in strike-through text, as I do not wish anyone to feel the material may have been censored for any other cause. Article begins:
Whenever the official story starts to have cracks in it, the cleaners go to work in Wag-the-Dog fashion, and power is applied to the weakest pressure points to make things ‘better for all concerned.’ As one CIA operative (one of the clean-cut train hobos at Dallas in ’63 set to cause a ruckus if the Grassy Knoll escape plan looked like it might be compromised) told me, “History is what we say it is, and it will not be changed by you or anyone else.”
Er… OK. But don’t fault me for trying the truth now and then, and forgive me with any liberties I take in the absence of good solid news reports full of details and hard facts… a matter which always makes me wonder what we are really dealing with…
 James holmes a mind-controlled patsy?
Come the terror at night,
or by day,
the citizens Plight is,
or it may,
be which one is right,
by what they say,
who is guilty of the fright,
and how shall we repay?
I wrote that with Aurora in mind, but it applies to a long American history of dark bumps in the dark, does it not?
James holmes is a patsy in a false flag operation
James holmes a mind-controlled patsy?
Come the terror at night,
or by day,
the citizens Plight is,
or it may,
be which one is right,
by what they say,
who is guilty of the fright,
and how shall we repay?
I wrote that with Aurora in mind, but it applies to a long American history of dark bumps in the dark, does it not?
James holmes is a patsy in a false flag operation
Added section: Ring: The receiver is lifted, but no greeting is offered, the Executive seated at the expansive desk in a plush office recognizing the calling number.
Voice on line: “The script will be ready on July 20. Adjust your plans accordingly.” The line went dead and the Executive hung up, and then dialed a number of his own.
Executive: “I’m green lighting Drum Roll. Production can begin at once, with a shooting date set for July 20. Make sure the cast and props are ready by then, and there are no problems in the storyboarding and rehearsals.” And then he hangs up.
Note: Double speak is the intelligence community perfected ‘art’ of speaking in the open about something by couching key matters in allegory or parable form. In the above example, we see how someone in the motion picture industry might talk about a film production… that was really something else… Drum Roll being the role played by the drum magazine in the shooting. Storyboarding means contingency planning, and rehearsals means that everyone knows the plan forwards and backwards. The script refers to the scheduled date of the theater shooting exercise which ‘just happened’ to be being held the same day of the shooting some ten minutes away off the same Freeway access as enjoyed by the Century theater. Interesting because high-risk intel ops such as would be true of a false flag operation, tend to employ a similar ‘drill’ for a like event on the same day and in the same city. This provides a cover operation so that if an operative is compromised, they will not be arrested and the plot can be aborted without exposure of the truth. End of added section.
James holmes is a patsy in a false flag operation
Ring: “Hello? News reporter here.”
Recognized voice: “The word’s going out to all our newsies… be sure to point out he had over $20,000 in high-tech equipment, and have another story by someone else suggest there is reason to believe there were Islamic ties, and be sure to play up the gun violence angle. And be sure not to mention he worked on that DARPA* project to develop super soldiers. That U.N. Treaty must be signed!”
News reporter: “But the shooting just happened. There’s been no time for an investigation, yet. What’s our source?”
Recognized voice: “Don’t worry about that. Just say ‘sources close to the investigation,’ and people won’t be smart enough to know any better… except for the ‘conspiracy buffs’ which you already know how to deal with.”
News reporter: “Right. By simply calling them that and ridiculing them for it. Got to hand it to Walter Cronkite for making that work so well in the JFK thing.”
*D.A.R.P.A. Defense Advanced Research Project Agency
Note: Walter was ex Army intel, and would have been a logical go-to person as part of CIA’s Operation Mockingbird which infiltrated news media with, by various estimates, over 1,000 operatives from CIA or on their payroll under the table. Since JFK, no conspiracy investigation has made good headway because media keeps trotting this excuse to ignore the valid questions of civilian investigators and investigative authors, or Engineers, Pilots, and other professionals who come forward with challenges to the official explanations. As one well known Comedian like to say, “I don’t get no respect, you know?”
James holmes is a patsy in a false flag operation
Ring: “Hello, Police Public Spokesperson.”
Recognized voice: “You have to stop talking about the possibility of the shooter having help. He’s a lone nut, nothing more.”
Police Public Spokesperson: “But people are trying to figure out how he got he got the larger weapons into the theater and all that gear. We already have one witness who’s been quoted as seeing someone open the Emergency Exit for him.”
Recognized voice: “Don’t worry about him. We have that covered. And don’t worry about what people think. We tell them what to think. Just do as I say.”
Police Public Spokesperson: “O.K. If you say so. Has everyone else in the loop here been so advised, or do I need to have an excuse to pass along?”
Recognized voice: “The key people are our people. We have it all covered, just like L.A. with the RFK matter.”
Note: In Robert Kennedy’s assassination, the Radio Dispatcher who controlled what Cops did that day and the Chief of Police were ex CIA. No wonder cops did not pursue the Woman in the Polka Dot dress, and the L.A.P.D. destroyed all the evidence which indicated more shots were fired than contained in Sirhan Sirhan’s gun, and did not protest that the fatal wounds came from the other side of his body where Thane Ceaser, a security staffer to a CIA involved military contractor had been walking directly behind Robert at the time of the shooting.
James holmes is a patsy in a false flag operation
Door shuts behind the lone interrorgator (spelling on purpose), and he takes a seat before the exhausted man at the desk. Interrorgator: “You told our people at the theater that you saw someone open the Exit Door for the shooter a second smoke grenade thrown from the opposite direction?”
Eyewitness: “Yes. I couldn’t see who because it was silhouettes against the movie screen might have thrown it.”
Interrorgator: “That’s impossible. We know the shooter was a lone gunman, and had no help. We have lots of people lined up who are going to be saying they saw it differently.”
Eyewitness: “I know what I saw. I was not more than ten feet away, and he crossed in it flew right in front of me.”
Interrorgator: “That’s not what you saw. The confusion and fear of the shooting has simply confused your memory. All you saw was someone getting up to take a leak or buy some popcorn. He never opened the door was some action on the theater screen from the movie… your mind has simply played a trick on you and filled in the blanks.”
Eyewitness: “No. I’m certain.”
Interrorgator: “Listen, kid. I’m going to lay it on the line for you.” Grabs him by the collar and jerks him halfway across the table. “I’m telling you, and you’d better listen up real careful like, you didn’t see that, you were confused. If you tell anyone you saw that, something bad might happen to you. There are a lot of people upset about this, and some of them have tempers and are looking for someone to go after. They don’t think very clearly, and I’m trying to keep you from getting seriously hurt… or your family for the matter. Do I make myself clear?”
Eyewitness: “You’re threatening me? With those people watching behind the mirror with cameras?”
Interrorgator: “You’re Goddamn right I’m threatening you.” Slaps face. “I sent those people on break and killed the camera, but in five more minutes, I’m going to call them back and we are going to be asking you the same question I started with, and you had better damn well tell me you were confused, or you and yours have NO F***ING FUTURE.” Shoves him back into his seat. “Do we agree on that, or not? Because if not, I can’t protect you!”
Eyewitness: “O.K. O.K. You win. I’m confused. I didn’t see anything except someone going to get popcorn.”
Note: Something almost identical to this happened to witnesses at JFK, RFK, and MLK, as well as the Flight 80o shoot down. Witnesses are often ‘told what they saw’ and told they were ‘confused by events,’ to allow investigators to later say their initial statements were not useful because of duress under stress impacting their memory.
James holmes is a patsy in a false flag operation
Ring: “Hello, Fire Department.”
Police Department: “We need you to take a Ladder Truck over to the shooter’s place and look in the window for us.”
Fire Department: “Why? We’ve never done anything like that before. What’s going on?”
Police Department: “We just want to make sure its not booby trapped. You need to tell us if it is so you we can send the Bomb Squad out.”
Fire Department: “Did the shooter say something to make you think there’s a bomb?”
Police Department: “Uh… sure. Yea. Something like that.”
Fire Department: “Well why not just send the bomb squad.”
Police Department: “Well, uh… I’m just doing what I’m told. I think they want high visibility with the press. Uh… you know… to make everyone look good. You will look good. We will look good… on TV… our small community will look good on national TV.”
Fire Department: “Whatever you say, Chief.”
Note: At a disadvantage with no concrete facts, there may have been a legitimate reason for asking the Fire Department to participate. Yet they did eventually send the Bomb Squad in and the first thing done was to use robots. Did the robots go in the window? Not that I’ve seen on video. No, they went in the front door. How do we know this? Because we have video of the bomb squad breaking out a portion of the window which would have needed to be removed if using the window for insertion of robots… doing so from the inside after the robots had finished. So why would there not have been a booby trap on the door blowing the robot away? That’s the FIRST thing I’d booby trap if of a mind to booby trap anything.
James holmes is a patsy in a false flag operation
Ring: “Bomb squad.”
Familiar Voice: “Be sure to blow a lot of stuff up at the practice demolition site afterwards.”
Bomb squad: “Why not just use the portable unit we always take with us? There’s nothing here large enough to require the demolition site.”
Familiar Voice: “TV coverage. Want to look good on TV, don’t you? Besides, the order comes from the top.”
Bomb squad: “Fine. We can have the rookies get in some practice at the same time.”
Note: The portable units (Mobile Explosion Containment Units) can contain significant blasts, but are not necessarily used for on-site demolition of bombs. They would perhaps prefer to instead transport explosives to a demolition site, as the units provide increased safety for such transport. However, some devices might be judged unsafe for transport, and should perhaps be destroyed at the crime scene. WHEN MULTIPLE DEVICES are found, there are several interesting possibilities which drove my inclusion of this portion of the dialogs.
a) The devices were too large to detonate on site. But we know that is not the case because we saw them on TV and they were small explosions (keep in mind that they use explosive devices to explode the bombs, so whatever blast you see is necessarily larger than the bomb by itself would have been.) Further, had this been the case, they should have likely been too large for collective transport, exceeding the safe operating limits of the mobile unit. But they were not shown making multiple trips to accommodate multiple bombs, so we again know this was not the case.
b) Despite the number of devices, their cumulative potential for damage is collectively within the ability of the chamber’s ability to safely transport through populated streets. IN SUCH A CASE, the bombs would normally be disposed of at the bomb squad’s facilities as a SINGLE BLAST. But we saw video on the news of multiple blasts in close proximity. This CONFIRMS they were not big blasts individually, and should have been done as a single blast. Why not? I can think of only one reason: Publicity stunt.
James holmes is a patsy in a false flag operation
Added section: Ring: “Executive speaking.”
Voice on line: “There’s been a problem with that special script for Drum Roll. It hasn’t been received by the Publicist.”
Executive: “Well where the hell is it, then?”
Voice: “We think it might be lost in the mail room for some reason.”
Executive: “Well get the… ah, you know… the ‘Director of Security’… to go search for it, then. That’s an important matter useful to Advertising and Promoting Drum Roll to the viewing public.”
Voice: “How do I do that? What do I tell them is the reason?”
Executive: Pauses. “I don’t know. It’s your job to solve problems like this.” Pauses again. “But try this; tell the Publicist to call the Director and complain about a suspicious package… and use that to get Security involved. Use your imagination.” Slams the receiver with a curse.
Note: Director of Security is their contact in the Police Dept. The Publicist is the Psychologist, or someone acting on her behalf. For some strange reason, the Psychologist indeed contacted Police about a strange package which showed up on her desk with no name on it, which turned out to be nothing but a text book being returned by a student. The explanation was concern, after the news about the bombs in James’ apartment, that it might be a bomb from James — in which case I wonder how James managed to put it on her desk while he was under arrest. For an even stranger reason, Police then searched the entire mail room to find the ‘script’ James allegedly mailed explaining in detail his plan to shoot up the theater. Strangest of all is that it was sent 8 days prior to the shooting. End of added section.
Next dialog, and the last, most telling of all…
Interrogator: “O.K., James. You want to tell us why you did it?”
James: “Did what? Why I am under arrest?”
Note: Jame’s reaction after the shooting is no different than Sirhan Sirhan (RFK), Jack Ruby (Oswald), David Chapman (John Lennon), Arthur Bremer (George Wallace), Squeaky Fromme (Reagan), and John Hinkley (Reagan), and others: No attempt to escape, in many cases going limp or calmly waiting nearby for arrest. Many of them have no recollection of the event, or have a single line of ‘political’ thought on it which they repeat, or start to explain and then just at the critical moment, change the subject.
These are all known methods of dissociation symptomatic of programmed Manchurian Candidates who are incapable of ‘confessing’ the truth, as they genuinely are not aware of it. In this case, we know he simply waited in his car and put up no resistance. What we don’t really know is if he has told the Police anything at all, but must presume not, or it would have been all over the news in some form or another.
So I’m taking the liberty and risk to assume, here. Please forgive any Ass made out of You and Me thereby. If I’m way off base, I’d be just as happy with the thought you may have gotten some entrainment value from it… because if I’m not off base, we are all going to end up mad enough to bring down the government and lynch some people.
James holmes is a patsy in a false flag operation
Please rate this article at page top, tweet/share, and comment. All comments welcome, good or bad.
Related articles
- Official Formula For Conspiracy Coverups (proparanoid.wordpress.com)
USAF Command Solo: Airborne Mind Control for the Masses
Not even the aircrew knows what they are telling you to think
by H. Michael Sweeney
Note: in preparation of this article, which updates and corrects some prior material I’ve posted in the past, I had intended to copy material already posted at my proparanoid.net Website, only to discover it appears to have been hacked (my host service stopped using Macintosh, it seems). The entire article relating to Command Solo has vanished, links and all. I wonder who would have a motive for excising only Command Solo information? No matter, it is also in my book, M.C. Realities: Understanding, Detecting, and Defeating Electronic Weapons and Methodologies of Political Control Technology.
A plane like no other, an admitted weapon against free-will thought
It’s a specially modified Hercules C-130 called Command Solo, and the U.S.A.F. currently operates a fleet of 7 of them (predecessors, Coronet Solo, entered service as early as 1978). They are based out of the 193rd Special Operations Wing stationed at what used to be Olmstead AFB, now part of the Harrisburg International Airport at Middletown, PA. Costing up to $110M each, they are the ultimate tool in government’s arsenal of Political Control Technology (PCT) used to subvert God’s gift of self determination. Official USAF info, here. Notice my photo is better than theirs.
Assigned to the Air National Guard, they frequently fly training missions over U.S. Soil, and no one who might feel a twinge of guilt, not even the aircrew, knows what messages they beam down to the ground. It’s all a super sophisticated programmed system with nothing but indicators and meters to show how things are operating. See inset picture.
Officially, it ‘intercepts and blocks existing broadcasts and replaces them with whatever information is deemed necessary to achieve mission goals,’ and operates in the ‘AM, FM, and UHF/VHF TV bands employing medium and high frequency, very high frequency, and ultra high frequency.’ The problem with these statements is that they avoid discussing yet two other capabilities, one being subliminal message embedding, and the other being the use of low frequency and extra low frequency, ELF. This is the darker potential of Command Solo:
All such psyops methodology is based on principles of mind control developed by CIA and the DOD, and even research by NASA, many of the same technologies used selectively on Targeted Individuals by operatives on the ground to make them seem Schizophrenic, though victims of that level of mind control also ‘enjoy’ other special PCT treatments as well, to include low-tech methods such as organized stalking, sometimes called dogging, or street theater.
It is not simply conspiracy theory or conjecture. The Air Force has admitted Command Solo’s use of such tech with startling results in sanctioned operations abroad, and further admits they are allowed to use it here in America in certain circumstances. But the problem is, there is no way to police or monitor its use, detect it in use, nor know what the content may be.
How it works

I used official USAF images for annotating as seen. Subsequently, they have been removed from USAF sites, all remaining images with less useful clarity or detail. My image was also deleted from search engine results after being among the first to show in a search.
Overt messaging: The least offensive possible use, whereby simple and direct propaganda is broadcast. The plane can even fly low altitude missions of this type and use loudspeakers capable of overcoming the plane’s engine noise by use of sound canceling technology. But this does not bother me in the least.
Subliminal messaging: The aircraft flies at altitude, loitering in large circles for endless hours, perhaps even employing in-flight refueling to increase time on station. There it picks up citizen broadcast radio and TV signals, and replaces or rebroadcasts them at amplified levels. It can work on select, whole groups, or even all locally available signals. How nice of them to provide improved reception quality for those listeners and viewers lucky enough to be below.
But there is a price to pay for the audience. The broadcast signals contain a few added elements of information embedded within the audio tracks. It is not known to be the case, but it is also presumed additional subliminals could be contained within the video. Subliminals are simple, brief, and repeated messages in a form not consciously discernible by the listener/viewer, but which, by repetition, are perceived and communicated subconsciously.
To my knowledge, the first known use that made the news about visual subliminals was in the motion picture industry when one frame in 24 (one frame every second) would have superimposed upon the image a single word, such as ‘popcorn,’ usually just before the intermission. This could also be achieved by the use of a second projector with all black film save the ‘word’ frames where the word was clear and transmitted white light in superimposition.
Alfred Hitchcock had the word ‘fear’ added directly to the film Psycho just before the scary parts. That was the use which became public, and revealed the fuller use to the public’s dismay, and soon enough sparked laws prohibiting its use altogether. We must suppose such laws are adhered to, as there is no easy way to know, for sure. All TV and film is candidate for suspect, and only frame-by-frame review would prove anything useful.
In audio subliminal messaging, a method known as ‘back tracking’ or ‘back masking’ gets a lot of attention in media, today… where the sound played backwards has a ‘secret message’, usually dark or evil. In some cases, the audio content may mirror the same information both forwards and backwards, such as is claimed for the famous ‘That’s one small step for man…’ moon-walk line, which backwards, says, ‘Man will space walk.’
The subconscious mind is said to ‘hear’ these messages quite well, but the phenomenon tends to happen naturally without engineering. While it is possible to engineer it, and many songs employ it for special effect, in my opinion, employing it for mind control purposes is less useful and less practical than employing a much more common method.
The simpler and earlier known method is to simply embed the message directly into the audio at inaudible levels and at frequencies or pitches sympathetic to the existing audio such that it seems part of the intended content. This method allows complex messages to be absorbed, and is well known as a means of teaching topical information or improving mental performance or even physiological attributes of people while awake or sleep. As long as the user of such content is informed of the existence and nature of subliminals, it is legal. Command Solo employs this later technology, but of course, there is no content warning.
EEG entrainment: There is currently no hard proof Command Solo employs EEG entrainment, though photographs (see image) of the plane reveal design elements which indicate the needed transmitters are installed. I’ve had the example photograph with annotations on line for nearly two decades and to date no one has protested the allegations with technical proofs or basis (or at all, for the matter, save possibly the protest inherent in the hacking thereof, which strangely left the image in tact — through removal of the image would have more quickly revealed the hack had taken place.)
The brain operates at extremely low frequencies (ELF) below 15 cycles per second (15 Hz). EEG (ElectroEncephaloGram) readings at multiple locations on the skull can be used to monitor brain activity by capturing these signals and converting them to printed readouts of squiggly lines for medical review. However, a given type of thought or mood, or even general physiological state (e.g. headaches, nausea, pain) will result in specifically unique EEG patterns as a collective. The EEG squigglies are indeed a de facto brain wave frequency map of such states.
Where such a frequency map is rebroadcast by traditional radio in the same frequencies but at stronger levels than the brain itself generates, the brain will adopt them as its own. This is called entrainment. Command Solo employs what I claim are special ELF transmitters to broadcast such frequency maps to a broad area to impact the thoughts of people below. Like the subliminals, this is presumed to impact anyone within several hundreds, perhaps thousands of square miles, though it must fade in potency as distance from the plane increases.
Therefore, by broadcasting subliminals such as ‘I should surrender if I get the chance…’ along with EEG states of mind such as ‘fear’ and ‘nausea,’ it is possible to perform quite a mind f*** of anyone unfortunate enough to be in the plane’s range of operation.
Follows is are excerpts from an article by Judy Wall, who was publisher of Resonance, a newsletter for members of MENSA (the high-IQ society) who specifically are involved in bioelectromagnetics study or research; a scientific paper. She also wrote investigative material for the magazine, Nexus, an international magazine covering technology as well as social phenomenon and their impact on mental and physical health. From Issue 7, volume 5 of Nexus, we find:
According to the (USAF provided) fact sheet: Missions are flown at maximum altitudes possible to ensure optimum propagation patterns… A typical mission consists of a single ship orbit which is offset from the desired target audience. The targets may be either military or civilian personnel…
In a phone call to the USAF Special Operations Command Public Affairs Office, I questioned the legitimacy of using these subliminal broadcasts against civilian populations. I was told that it was all perfectly legal, having been approved by the U.S. Congress (!) …the Air National Guard of the individual states in the U.S. can also operate Commando Solo aircraft, should the Governor of a state request assistance. That means the PsyOps mind control technology can be directed against U.S. citizens.
…On July 21, 1994, the US Department of Defense proposed that non lethal weapons be used not only against declared enemies, but against anyone engaged in activities that the DOD opposed. That could include almost anybody and anything. Note that the mind control technology is classified under non lethal weapons.
USAF General John Jumper ‘predicts that the military will have the tools to make potential enemies see, hear, and believe things that do not exist’ and that ‘The same idea was contained in a 15 volume study by the USAF Scientific Advisory Board, issued in 1996, on how to maintain US air and space superiority on the battlefields of the 21st century.’
Wall went on to report confirmation that Command Solo was employed in Iraq and specifically to sway Bosnian elections. The U.S.A.F. admitted to her that Command Solo played a significant role in getting Iraqi troops to surrender en mass, even sometimes to model airplanes (UAV – Unmanned Ariel Vehicles), and to sway elections in Bosnia to insure a Coalition approved leader was installed for the purpose of maintaining political control and stability of the region.
Additional thoughts (mine, not theirs)
This technology was first deployed in 1978. What happened in 1978? The World’s first mind control cult mass suicide: 909 persons at Johnstown, a CIA established cult started called The People’s Temple, led by Jim Jones. The cult, located in Guyana, was frequently overflown at surveillance distances by C-130 aircraft.
The significantly upgraded (EEG) version was introduced in 1980. What happened in 1980? Iranians stormed the Russian Embassy in Teheran; 63 religious Zealots seize the Grand Mosque in Mecca and are beheaded; Bani Sadr, the most pro American of candidates is elected as President of the new government in Iran (this is at the time Iran held 6 American hostages); unarmed farmers storm, occupy, and burn the Spanish Embassy in Guatamala, a key event to Democracy being established a few years later.
These events prove nothing concretely, but themes appear with a frequency to cause one to wonder, ‘what if?’
A logical question arises:
How do we know what information is contained in Command Solo when over U.S. soil? The answer is, we don’t. The aircrews do not, either. Nor does Congress, or perhaps even those who should know at the Pentagon. Perhaps only the preparer of the preprogrammed digital tapes used to modify and retransmit knows, and it is conceivable even that person does not know, likely ordering it by a code number which does not reveal content. It may simply be marked ‘Training Use Only.’ But somewhere, someone knows, and they won’t be talking about it honestly if it contains messages to sway our political opinions and social viewpoints, or our votes and other key actions.
Now, does that sound like a democracy in action, or more like a military police state growing its power? You know my answer, best summed up by the wish that the right to bear arms might ought to include Stinger missiles. I’d like to see these aircraft permanently grounded, along with the 30,000 Global Hawk drones they want to fly over U.S. soil to ‘protect us from terrorists.’
WE are the terrorists, because our ability to think for ourselves is threat to the security of the 1% who seek total control; we strike terror into their hearts every time someone like me makes public the truth, and someone like you chooses to read, share, like, and rate (page top) that message. We know this fear to be true for many reasons, as cited in my other posts on related topics.
That’s why its called PCT in the first place, an abomination before God in defiance and subversion of His gift of Free Will and self determination we were promised by the Constitution as ‘the pursuit of happiness.’ Where, exactly, do you live, again?
Buy now, be happy. Trust government, vote for X, and be safe. Spend money, be happy. Believe TV news, fear terrorism. Borrow money, be happy. Fear terrorism, Vote for X, and be safe. Watch TV, be happy. Ban guns, be safe. Buy now, be happy. Trust government, vote for X, and be safe. Spend money, be happy. Believe TV news, fear terrorism. Borrow money, be happy. Fear terrorism, Vote for X, and be safe. Watch TV, be happy. Ban guns, be safe.
Related articles
- Real Scientific Evidence for Subliminal Messaging: A Rising Tide (whatispsychology.biz)
- Timeline of Masonic/Illuminati/Mind Control Evolutions (proparanoid.wordpress.com)
- Can subliminal messages in movies be used to manipulate you? Like in FIGHT CLUB? (businessinsider.com)
Testimony to Mass. State Legislature on Bill Restricting Electronic Weapons
Included list of 250 terms and technologies of Political Control Technology
Edited excerpt from book MC Realities: Understanding, Detecting, and Defeating Political Control Technologies
by H.Michael Sweeney, copyright©2006 proparanoidpress, all rights reserved reproduction by request and approval only, to pppbooks at century link netI write to the honorable legislative committees as a friend of the State and of all its citizens, volunteering the material contained herein as an expert witness on electronic weapons, electronic harassment and related technologies of political control. It is hoped that this material will be entered into the public record at your hearings and become useful in your final determinations…
Because of my knowledge on topic after a decade of helping victims of such technology, I must protest at the committee’s choice of language in the bill with respect to the first sentence… referencing control of these weapons only in the hands of the public by means of the phrase ‘no person’. This is to miss the entire purpose and intent of these weapons, and to fail to address the virtually sole possessor and users of the worst of the technology, which is government itself. The public does not need legislation to protect itself from itself, but from its own government. Language must specifically and clearly include government agencies and government personnel of all manner, Federal, State, and local…
In like manner, your definition of weapons is far too simple and narrow to avoid legal confusions. For example, the very same technology which is found in radar guns and FLIR can be used as a weapon of political control or harassment by mere abuse thereof. How will you protect against such abuses? How will anyone be able to determine by the wording of this Bill when the technology and application are legal and appropriate and when they are abusive and invasive?
The victim is not protected if the burden of proof rests on such simplistic language. The abuser, especially if governmentally authorized to access such technologies for normal uses, is not at risk where such loop holes exist. Your language must define and articulate to the complexities of the matter, which are illustrated by the technology reviewed in my (included) materials on topic. Merely adding ‘definitions’ section should address these concerns.
Finally, your legislation makes no provision for detection and enforcement. Can you imagine the local police arresting someone because a neighbor claims to have symptoms of attack? Without a means of detection, there can be no enforcement; all which remains is mere lip service, legislation not to protect the people from the weapons, but to protect the establishment from the people. The primary question is this: Is there anyone in our national or state governments who will stand up for the Constitution, support the Bill of Rights, live by the morally correct principles of humanity and of God, and resist the evil which stares you squarely in the face?
The challenge before your committee and, ultimately, for your entire legislative body, is not only formidable, but it is absolutely pivotal to determining the future of this nation…
Until one empowered sector of our own society, such as yourselves, makes an official protest and stand against this growing draconian onslaught, those things for which our nation stands come closer and closer to being silently crushed within a velvet totalitarian glove. Without such understanding… without laws to protect citizens from the dangers involved… and without any means of enforcing those laws… political control will be assured. The price for such control will be dear. It will be the surrender of that thing godly men call ‘free will’, and which the patriot calls ‘freedom and the pursuit of happiness.’
…May I propose three key concepts or points which should be a part of your deliberations?
1) The first is that any such legislation should be broadened to cover most, if not all non lethal weapons, not just electronic. The very same people who developed electronic weapons were responsible for the development of other non lethal weapons, and for the same unsavory reason: political control. All such weapons further have the same attendant risks to life and liberty and lend themselves to the same abuses and excessive draconian applications.
Perhaps just as important, a review of all such weapons makes the relationship between the weapon, the intended use, and the greater political control strategy which drove its development that much easier to grasp. In support of this notion, my report herein addresses the full spectrum of non lethal weapons, the greater portion of which are, perhaps surprisingly, the more hi-tech electronic variety.
2) The second point I would like to make is that your considerations and final findings must include and provide for public awareness. Only by educating the citizens of the realities of the existence and use of these technologies, can your efforts be well served. If the citizens do not understand the technology and the symptoms it generates, they cannot report the crime or well defend against it. In like manner, your law enforcement, the legal system, media, and the professional communities must also be educated, or the victims will have no place to turn without being labeled as insane.
Of even more value, such promotion and education will, more than any threat of punishments, deter actual use of the technology in the first place. All such technology is currently used in an extremely covert manner. The last thing an attacker using electronic weapons wants, is to be discovered. Such discovery puts not just the mission at risk, but also puts at risk the entire infrastructure of the non lethal weapons industry, and their leadership both in and out of government. Education will, in my opinion, prove to be your best weapon, in the end. But education in and of itself does not provide an adequate deterrence, because unless an attack can be proven, it is merely an accusation which, due to the sophisticated nature of the attack, can too easily be ignored by unconvinced authorities.
3) Therefore, the third and final point, perhaps the most important, is that if you are to have any true success in this matter, you must necessarily include funding for the exotic equipment required to detect and analyze the telltale electromagnetic fields, energy bursts, and radio frequency signatures which are the calling cards of these technologies. In fact, I remind you, it is precisely the output of these detectable indicators which makes this matter one of general concern to the population at large.
The leakage, overshoot, and reflection of these signals, energies, and fields created by these weapons have a great potential for harmful physical, mental and physiological effects on all citizens within a given radius of the intended principle target under attack. The collateral damage to these citizens is not now understood, nor can it be so understood until the actual weapons are captured and tested by independent laboratories. Even the most conservative estimates talk about dire health consequences associated with these weapons. If a particular cell phone can be found by scientists to cause a brain tumor, then what must we face when the signal strengths are many hundreds or even thousands of times stronger, and deliberately designed to cause physiological and mental effects?
If you fund the needed equipment, you will need to further fund appropriate training of technicians on how to use the equipment, as well as in general procedures and skills in the area of covert counterintelligence operations and general law enforcement procedures. This is exactly what will be required in order to be successful against those who use electronic weapons, and no less.
With the above in mind, I would propose the Bill provide for creation of a joint task force of specialists in the areas of law, communications, signal processing, electronics, bioethics, medicine, chemistry, psychology, counterintelligence, military, and law enforcement be created and managed by a carefully picked oversight body. In the absence of creating a new bureaucracy, I would suggest that such responsibility might best belong to any existing state environmental agency as opposed to general law enforcement.
One reason I say this, and it is intended as a general warning concerning the selection of specialist staffing as well, is that I can virtually guarantee that law enforcement of your state and major cities has already been infiltrated by members of the intelligence community, or would immediately so become upon passage of any such legislation. For this reason, the easiest way to assure failure of any mandate against electronic weapons is to simply hand responsibility for it over to law enforcement.
Keep in mind that the more exotic technologies are hardly used for their ultimate intended purposes at this time, but more typically used only in testing on unwitting guinea pigs, citizens at large, generally from among the underclasses, those persons least likely to be able to defend themselves or obtain the expensive helps required. Therefore, most victims are targeted not because of any actual political or intelligence value, but because of the value in learning how the technology works and how to best apply it without getting caught.
Now, regarding testimony from other parties, I might presume and certainly hope that many such victims will stand before you to offer testimony, and I beg of you not only to solicit for such witnesses, but to open your considerations to citizens beyond your state borders, that you may increase your chance at hearing the full truth.
Indeed, open your doors to Canadians, as well, for these weapons do not respect national borders, and are freely exported for testing and use abroad. And for every brave soul who dares stand before you in tortured fear of what will happen to them for their bravery, and an even greater fear of what will happen to them if they do not seek your help, there are likely tens of thousands of others on the continent which cannot or dare not testify. Regarding what they say, may I further advise of three additional points.
Regardless of how wild or bizarre may be the claims found in such testimony, there will be three absolute facts I can promise to be true regarding their claims:
1) among those testifying, you will hear persons who are:
a) legitimate victims of the technology and who are telling you the truth exactly as their ability to grasp and express it allows;
b) persons who are delusional and falsely believe they are victims, telling you of imagined things which have little or no basis in fact; and
c) intelligence community plants pretending to be victims in order to provide you with deliberate disinformation and, largely, to discredit the general value of all such testimony;
2) It will be impossible for you, short of elaborate investigation and expenditures of large sums of money, to make any useful determination of which category a given testimony falls within;
3) in light of the aforementioned difficulties, you should logically come away highly incredulous and doubting of the value of the entire collective of testimony, were it to stand alone.
This phenomenon (3) is a prime example of one of the chief purposes of political control technology, that of destroying the credibility of victims who dare tell others of their experiences. Think upon that, for a moment. Electronic weapons are designed to conceal their own use by making the victim seem incredulous. The testimony you hear will prove that it works exactly as intended. Do not discard the truth encircled by lies.
In light of these facts, I am moved to insure their testimony and my own presentation does not stand alone. I herein provide some meager proofs in the form of a technology review of some 250 terms and technologies of political control. A much more substantial body of such evidence is possible should it be required, which is why I have tried to include more valuable proofs in the form of references which are, by and large, easily obtained and verified.
This includes articles and scientific papers as well as actual patents on the technology itself. Patents are used only when other experts have already connected the technology to the claimed weapon. A reservoir of additional patents which could have been used, except for space and redundancy they represent, are included at report end. But understand that for reasons of national security, many more patents exist which were unavailable.
Also realize patent descriptions need not sound like weapons, partly as a natural result of the patent application process, and partly by design. Too, like many inventions intended for good, some patents having no apparent weapon’s application have been subverted to evil ends by someone who saw the potential…
In point of fact, the great bulk of evidential resources come from military documents, a matter which is deeply troubling to all right-thinking individuals because it paints a picture not of a military set on defending the United States from enemies who would threaten it, but a military which is the threat, itself… By the following materials, may you come to similar conclusions, and may you have the fortitude and resolve to do something about it, which is something we citizens cannot of our own accord achieve short of armed revolution. Please do not leave this the only remaining option for Americans, or that may be exactly what the next generations will need consider…
It was perhaps author Aldus Huxley, who first expressed concerns about political control technology, put into words within the fictional construct of Brave New World and Brave New World Revisited, Orwellian nightmares not unlike 1984. Based on 1958 technology, Huxley projected ahead a mere 40 years to describe exactly the kind of technology and social consequence which lays at the heart of our focus, here.
In point of fact, I hope to illustrate, we are well ahead of his projections. Welcome to the New World Order. Sheep, do not be alarmed at the slaughter of your fellow sheep. As it is for their own good, so will it be for you.
~ Sincerely, H. Michael Sweeney
 Unfortunately, as with all such legislation efforts at both State and Federal levels, the Bill was not passed, nor was it amended to make it more likely to pass. It was simply dropped. Too many powerful people, firms, and groups benefit from Political Control Technology to allow a mere Congressional representative the luxury of a morally correct vote or opinion. The Cogs of government work beneath and behind the visible mechanism of floor debate, and are turned by the steam of the Military-Industrial-Inteligence-Media Complex. What you and I think, need, or desire in the pursuit of freedom and happiness is irrelevant, as is anything as trivial as the Constitution and Bill of Rights.
Unfortunately, as with all such legislation efforts at both State and Federal levels, the Bill was not passed, nor was it amended to make it more likely to pass. It was simply dropped. Too many powerful people, firms, and groups benefit from Political Control Technology to allow a mere Congressional representative the luxury of a morally correct vote or opinion. The Cogs of government work beneath and behind the visible mechanism of floor debate, and are turned by the steam of the Military-Industrial-Inteligence-Media Complex. What you and I think, need, or desire in the pursuit of freedom and happiness is irrelevant, as is anything as trivial as the Constitution and Bill of Rights.
However, in 2004, a variation of the Bill WAS passed. It can be found here. A brief reading will find that not one of my suggestions was incorporated, and in fact, it specifically authorizes government to employ such weapons, the reverse of the need. All it does is makes it illegal for you and me. Like that was ever a threat. Yet the deem this legislation as an ‘Emergency Bill.’ Go figure.
Related articles
- Judy Wall (targetedindividualscanada.wordpress.com)
The Olympics and Political Control Technology; Formula for Control
A Method to Control Athletes as Well as You and Me
by H. Michael Sweeney
A contract Journalist named Terri Hansen recently published an article through Mother Earth Journal the deserves our attention. Titled Intentional Radiofrequency Targeting Affects Olympic Performance, Leaves No Trace, it cites insider information which reveals a serious threat no one has previously suspected. She cites the warning words of wisdom from insider to British military and intelligence community covert electronic weapons development and deployment, retired Physicist Barry Trower — from an interview for ICAACT, the International Center Against Abuse of Covert Technologies.
A former Cold Warrior, Barry has in recent months become quite outspoken about not only the dangers present in weaponized technology of this type, but also, civilian use of non weapon sister technologies, such as cell phones. Learn more about what he has to say along those lines in this transcript of an interview with a South African radio station.
I’m writing here to confirm the validity of this story and to add key detail
As published author with seven books generally on topic and two specifically on topic, it will be easy to do. In fact, in my book, The Professional Paranoid, 2nd Edition (2005 — proparanoidpress), a defensive handbook for targeted individuals, I wrote about a CIA/DOD contractor VSE Corp. which, according to Public Relations material provided by them on line, actually took an unmarked van to a Winter Olympics (in an unspecified year prior to 2001) for testing their newly developed LADS system on Athletes. I quote from their own information, below, which predates 2001, when I first mentioned it in my newsletter.
LADS stands for Life Assessment Detector System and is supposed to be used for finding signs of life in rubble (e.g., collapsed buildings) or locating villains behind walls for the benefit of SWAT or military sharpshooters. It is only one of several ‘see-through-the-wall’ (or other barrier) technologies developed in the last few decades. It is sophisticated enough that it can identify one human from another if needed, provided pre surveillance of the target subject has captured the needed data. This entire project had, since the publishing of my book, apparently gone dark as VSE deemed to remove all references to it from their Web site shortly thereafter. While, perhaps thanks to me, you can find lots of information about LADS from other sources on line, you won’t at their own Web site. Quote on:
LADS consists of a sensor, neural network, and control/ monitor modules. The sensor module is an x- band (10 GHz) microwave transceiver with a nominal output power of 15 mw, operating in the continuous wave (CW) mode. The neural network module device can store many complex patterns such as visual waveforms and speech templates, and can easily compare input patterns to previously “trained” or stored patterns. The control/monitor module provides the L A DS’ instrument controls, such as on-off switches, circuit breakers, and battery condition, as well as motion, heart- beat waveform, pulse strength, and pulse rate displays. End of VSE quote.My book further states; They talk about a test, for instance, at the U.S. Olympics. What sense does that make, you ask? They parked an unmarked van near the Alpine Skiing and Shooting event’s shooting positions, and used LADS on the competitors. The goal was to measure and IDENTIFY each shooter by their own individual biometrics (i.e., EEG, breathing pattern, pulse rate, etc.,) WHILE SHOOTING. Thus they have both individual patterns to allow them to recognize specific shooters, but also, information useful to identify (based on the aggregate or average readings) anyone entering into an aim and shoot situations. In other words, they can tell when someone is about to use a weapon. End of quote from book — but clearly, this means EACH competitor had to have earlier been surveilled by this same technology well in advance of the test. Scary.
But there are things even scarier
In the broader view, I have variously written in my books and newsletters describing over 500 terms relating to Political Control Technology such as LADS, perhaps more than two dozen of which are related to LADS in design, capability, or purpose, at least as offshoots or predecessors, if not outright evolved supersets. The LADS tests at Olympics were harmless enough only because LADS was a ‘sense only’ technology. However, part and parcel of this kind of technology, which might be called ‘remote physical’ capability, which is to say, it senses things about the subject at distance as if hooked up directly to medical test gear… is EEG brainwave monitoring.
Note: for a free sample copy of my newsletter which features 250 such terms, including LADS, email proparanoid at century link net.
The interesting thing about EEG monitoring is that a ‘catalog’ of brainwave patterns can, in LADS-like fashion, be used not only to identify individuals and their specific physiological and mental states in select states of mind and body, or tasks undertaken, but to feed it back to them for instant adaptation, a phenomenon called ‘entrainment.’ All they need to is to rebroadcast the signals back at them at stronger levels than their own body would be able to generate. The human brain instantly entrains to such a signal. Of course, the brain’s state definitely impacts the remaining physiological functions of the body accordingly. Now that’s truly scary!
Such technology is quite frequently found to be in use against politically incorrect citizens, generally to cause yo-yo mood swings, and bounce them back and forth between sleepiness and wakefulness in ways which mimic general torture methods based on sleep deprivation and denial of self. I work with such people as consultant every day (you may also ask for a free Helps Kit if you fear you may be such a victim). If used by one country in an Olympics against foreign competitors, it would be quite simple to ‘throw their game off’ sufficiently to allow an easier victory. It could also be used on one’s own athletes to better insure ‘top game’ performance. It is, sadly, undetectable except by the most sophisticated of TSCM equipment (Techincal Security CounterMeasures), and so doing requires perhaps a million dollars worth of gear and well trained experts, generally costing many tens of thousands of dollars per deployment. Even then, given the covert development of this technology, there is a risk they would mistake it for something less insidious and give a thumb’s up.
This technology is currently down to the size of a cell phone for portability in applications where the subject is within close range, perhaps 50-200 feet or less, and powerful tripod systems can accurately target people where there is line-of-sight capability from many thousands of feet, and even miles away. It is perhaps important to mention that one reason this is so easy to employ is that the signals are highly directional and narrow in beam. Another is that the signals can be so highly matched to the target subject that even when accidentally hitting a bystander, they do not have the same effect. But the most important reason is that, except where the individual has been trained to sense the signals (I train my clients in such methods, where possible), or they are already hypersensitive to radio frequencies, they have no understanding the attacks are taking place. It all seems natural. Unpleasant or unwanted, but natural.
Political Control for the Masses
The real question is not ‘Is this technology being used at the Olympics?’ because it most likely is given the ease of deployment and the tremendous value placed on success in Olympic events by nations and corporations. This equipment is in the hands of almost every industrialized nation on Earth, and not just in government hands. Corporations and perhaps even criminal groups have access at least to older versions. Even technically skilled civilians using information available on line can build devices in this family. That kind of technology in the hands of a major betting parlor would be worth millions, and in in similar ways greatly amplifies the value of advertising dollars for corporate sponsorships.
No, the real question is, ‘Will the Olympic authorities choose to believe there is a Boogyman and do what it takes to defend against them, or not?’
To do so would fly in the face of over half a century of ‘logic’ by authorities of all manner who, when approached by persons targeted with such technology, preferred instead to simply deem them Paranoid or even Schizophrenic, and shove them aside and deny aid with jokes about ‘tin-foil hats.’ Sad, because such hats work, and that’s one reason such joke are so mainstream — to make anyone in need feel and look foolish using them. For any authority, it is far easier to let the Boogyman run free, than admit the possibility of existence. Besides, any public statement of detectible use of such technology would undermine the ‘notion of fair play’ expected in the Games. It is one thing to have rules for athletes to follow and tests to insure they do not abuse drugs for a competitive edge, but quite another to set rules and employ tests for government’s fairness in play.
Yet to do nothing may well eventually lead to the revelation that there is no purpose at all in watching or competing in the Olympics, because the entire affair was nothing short of a puppet show, more a colorful, scripted charade than a sports competition. But that thought brings us to another unpleasant notion. The real value of the Olympics in the first place is its power to distract and control the masses globally, and promote globalist corporate interests. Those of us glued to the TV will not be busy protesting the G-12 or WTO gatherings, or occupying more than our living rooms, closer to a functional zero than a potent 99%.
So what do the globalists care if the Games are on the up and up, or not? Zzzzzap! Score!
Related articles
- Effort to ‘read’ Hawking’s brain (bbc.co.uk)
- How Sci-Fi Becomes Reality – Mental Manipulation (theurbn.com)
- Synthetic Telepathy And The Early Mind Wars (powersthatbeat.wordpress.com)
- Wes Moore ~ Television: Opiate of the Masses (Thanks, C) (shiftfrequency.com)












Crime Series: Ten Unexpected Proofs ‘Random’ Mass Shootings are by Intelligent Design
Apr 3
Posted by Author H. Michael Sweeney
Ten easy-to-grasp but remarkable proofs, both visible and hidden: Illuminati style mystical symbolism and related ancient magical mysteries, calling cards, bragging rights, and Warlock spells cast against America, and the World. Conventional clues, too.
Are there any patterns in mass shootings?
by H. Michael Sweeney proparanoid.wordpress.com proparanoidpress.com proparanoid.net
copyright © 2014, all rights reserved. Permission to repost hereby granted provided entire post with all links in tact, including this notice and byline, are included. Please comment any such repost to original posting.
Is there any proof mass shootings are not random?
What you will learn reading this multi-part posting series…
• there are 10 interlocking proofs that mass shootings are not random; • they include various kinds of patterns, visible and unseen, and even coded information; • that the pattern predicts itself, and understanding may therefore help stop the murder; • that the codes and clues seem to be like signatures identifying the architects.Are mass shootings by intelligent design?
Introduction: Ten Proofs ‘Random’ Mass Shootings by Intelligent Design
Is there a mass shooting conspiracy?
Note: This series is not yet ready for full presentation, but the most recent Fort Hood forces me to start releasing the material without delay. The reason for delay has had to do with an inability to provide high quality graphics suitable for proofs. This will be overcome, shortly, I hope.
One thing you need to know about me as an investigative writer or, as media and government would prefer you to think of me, a ‘conspiracy theorist,’ is this: whenever I decide to take a close look at a potential conspiracy or lesser matter, I do it right. If I cannot uncover something no one else has brought to light, I’m either not finished, or I’ve backed out concluding it beyond reach, or a dud. If you read my findings on a given research, you will undoubtedly learn something FACTUAL no one else had previously discovered or brought to light. And so…
In this matter, we find the shear volume of startling new information overshadows and renders original headlines and competing theories essentially meaningless — especially media’s version. It will make you angry. It will scare you. The question is, will it motivate you to do something about it? YOU are what you are waiting for, you know.
But in introduction, there is still one other point which must be made; it is in form of a problematic question. Can I get you, the reader, to override your current belief structures long enough to consider the unusual nature of the findings? This presentation will most assuredly fly in the face of what most people consider ‘traditional wisdom,’ but it also will explain why it is non-the-less valid. Can you handle the Truth, or will you wimp out to the comfort zone of current beliefs?
Area all mass shooters psycho?
On suspending belief structures
Dormer was not quite a ‘Mass Shooter’ incident, at least not at a single location/time. But the affair highlights the problem of accepting ‘random’ as the right word to apply to shootings when there are so many problems with the official story. CLICK to learn about why many people think him just another shooting patsy.
I began a ten-year research project for a book, Fatal Rebirth, in late 1989, which also begat a screenplay published on line in 1999 (The Electronic Apocalypse). In the book’s Introduction I urged the reader to suspend their belief structures briefly and read the material as if merely fiction for entertainment’s sake, because many of the concepts within were so new and unusual as to defy belief — likely seen as ‘far-fetched’ by most uninformed readers. I offered over 1,500 footnotes and a huge Appendix section to help them consider why I deemed them factual.
This blog post should be read in like manner, especially if you are content with government’s actions, are a politician, member of a government agency, military, or any part of the justice system, or Media. Especially if you are involved in a mass shooting incident as a professional or a victim seeking to know the truth. And even more so if you are gun owner, or even among what 2nd Amendment supporters refer to as a ‘gun grabber.’ I plead, therefore, that you suspend your belief structures briefly as if reading a political/horror-science fiction piece. That’s what it is, actually, minus the fiction component.
You will, like readers of Fatal Rebirth, I would hope, realize the truth by the time you reach the end. Or, at the very least, you will be entertained for all your reluctance to let the message sink in and take root.
If nothing else, even if you choose to doubt some of the more obscure subtopics (i.e., relating to mysticism) have any factual basis in REALITY, consider this: it matters NOT what YOU think, given they ARE taken as real by persons likely to be behind any such conspiracy (i.e., ‘Illuminati’ Satanists). You MUST also ask yourself, “Can the sheer magnitude of interlocking clues be ignored?” Because at every turn they defy the odds of coincidental probability, as illustrated by carefully crafted control study groups. If thinking logically, you MUST concur that intelligent design is revealed despite what you may think about the logic of the beliefs which lay behind it, or the unusual way in which the evidence was revealed.
Pending you conclusion, by all means feel free to think me mad if you must. Read just for fun, but please read it through to end before you render final judgment as to if madness or truth be present. A logical reader will be converted unless their mind is already so firmly made up that they do not wish to be confused by facts which destroy their belief structures. Judge not what ye know not, but that upon which ye are well informed and have considered fully, judge freely.
Your future and the future of your children could well be at stake, a statement applying to all mankind. Why do I say this? The book mentioned above, Fatal Rebirth, was based on trying to illustrate what I call the Unified Conspiracy Theory; the notion that all of America’s darkest bumps in the night for the last half of the prior Century, forward, were not random oddities by random people for random agenda, but carefully orchestrated by the same core group of people with but one goal for the World in mind.
I termed them Shadow, but they are also known by other names; the New World Order, the Illuminati, the Power Elite, Globalists, and among them, member names like CIA, Skull and Bones, Bilderbergers, Council on Foreign Relations, and many more of like nature. Their goal I termed End Game; the establishment of a One World government, a single seat of power in order to seat the Antichrist upon his throne and bring us to Armageddon.
The Unified Conspiracy Theory, once justified in research and taking shape in book form, led me to realize that their stepwise actions over fifty years of mysteries were indeed leading to one goal. Knowing the goal, I reasoned, it should be possible to forecast the next logical steps. So the book also included within its presentation several terrible event predictions expected to take place in our near future. Thus far, though I do not claim to have gotten all event details precisely correct, many terrible forecasts have already come to pass. Among these were:
a) an assassination attempt on Ross Perot or his family to cause him to drop out of the Presidential Race, a matter which indeed transpired using mailed Anthrax according to a Secret Service back channel contact;
b) the false flag downing of the World Trade Center by civilian passenger jets which;
c) resulted in a series of Middle East Oil Wars. Other predictions include two more terror plots which are part and parcel of this blog post. Those are…
d) a false flag nuclear attack on Charleston, S.C. and Portland Oregon (the later of which I have already thwarted, it seems – see middle of my home page), and more to the point…
e) MASS SHOOTINGS.
Note: you can get a free copy of Vol I of Fatal Rebirth (ebook) by email request to pppbooks at Comcast (net). You will be glad you did, as it will take you far deeper into the Rabbit Hole than Alice or Neo had ever gone. This pill is black, though trimmed in red, white, and blue.
So, if ready to suspend your belief structure, let us begin. Pretend there is, despite media’s recent attempt in the Cincia shooting to portray anyone who believes in the New World Order as mentally ill and anti-patriotic, that such a conspiracy is actually afoot. Also pretend, if you must, that Political Control Technology in the form of the Manchurian Candidate is real. There are real-life Jason Bournes out there, as my book, MC Realities, and other books on Political Control Technology illustrate more than adequately. Even the Smithsonian channel knows.
This will make the key postulations, testing methods, conclusions, and proofs of the core material easier to accept, especially as they will be offered in the manner of scientific discovery — exactly as I undertook them as investigative writer. You will, in fact, be able to retrace my work to double check it, if you wish — as long as you review the full series of posts and sidebars before you attempt it, lest you make a critical error. Please subscribe to my blog pages to insure you are notified as the remaining posts in the series are added.
Are mass shootings are by intelligent design?
The Investigation
Jason Bourne… though fictional, is based on real-World programmable assassins. Do you suppose CIA or anyone else would not find something useful to do with failures in such programs? Might they not make excellent disposable patsies? Image/film: http://www.imdb.com/title/tt0372183/
Some several months ago, insulted by media’s misreporting of Aurora and Sandy Hook and outright clues that a disinformation campaign was afoot, I began finding ample cause for concern. But how might one determine if other mass shootings were arranged as part of some kind of sick criminal conspiracy, one which might involve both real and faked shootings?
I started with several basic presumptions of truth, and then set about to see if the logical evidence such presumptions would require were indeed in place. The ‘illogical’ presumptions fostered by the Unified Conspiracy Theory requiring suspension of belief are as follows:
1) That Shadow and their Globalism requires destruction of America, and its Constitution in order to enable forming the North American Union, a matter which in turn requires that the Right to Bear Arms is first invalidated, and arms confiscated or gun owners otherwise neutralized in a manner similar to that of the Australia;
2) That the New World Order, the modern day Illuminati, if you will, would be well capable of undertaking a campaign of gun violence for such cause, but being an Illumined Power Elite lost to Satanic and Masonic mysticism, they would employ mystical constructs which would leave detectible footprints if knowing what to look for;
3) That the principle tool of such a plot would involve a small army of patsies, cut outs, and fall guys, principally from a category best known to the public as Manchurian Candidates. It may additionally involve a small army of blindly obedient members placed within our armed forces, the intelligence community, and law enforcement to aid more indirectly in supporting roles. This would include logistics, psyops, and cover up, or even command and control, generally unaware as to the truth or reason behind their orders. These are the same players frequently found playing key roles in the lives of mind control victims at large.
All three presumptions must be true to make a proper accusation, for they comprise the basic proofs of any crime: Motive, Opportunity, and Means. Normally, we think of opportunity as meaning access to the scene of the crime, typically proven by forensics such as fingerprints, or better yet, actual eye witnesses. In this case, they deliberately left their fingerprints, in a manner of speaking. In fact, the bulk of the proofs fall into this category, perhaps even naming individuals behind the plot. At the very least, we are indeed dealing with the Elite, those involved in principalities and powers.
Indeed: Two names have already surfaced by such clues, and both are billionaires. I also have a dozen other names of likely conspirators, but no names are released; these things are my Life Insurance Policy.
Sidebar Post: On Programmable People. This sidebar post addresses the notion of the possibility that at least some mass shooters are mind controlled patsies, and reconciles their coexistence with truly random shootings — those which are more naturally spontaneous crimes — which can collectively still both be component parts of the same intelligent design. This leads us to the finer details of how shooting event locations and dates lend importance to our consideration, and just how these things can additionally reveal intentional, yet concealed clues.
Here it should be mentioned, that many observers of the New World Order crowd favor the supposition that among their leadership we might find the modern-day Illuminati in spirit, if not in actual blood lineage, even though they may have since assumed a different family name. By way of example, in my research, I have had reason to conclude that the Rotheschild name was assumed; those assuming it being Knights Templar in hidding, their wealth derived from Templar treasure, and not truly Jewish by ancestry or faith, at all.
Many who favor the notion of a Modern-day Illuminati additionally believe, as do I, that there are at least two, and as many as four groups competing with each other within the movement to be the ones ‘honored’ to have one of their own selected to become the Antichrist. Much of what is discovered in this investigative series will point to this being true in one way, or inherently implied in another. It is, in fact, one very good reason to employ symbolisms and other clues which act as signatures of those so bidding for selection.
Such evidence was abundant, even easy to find, and I remain convinced that the trio of presumptions are sound enough to warrant seeking incontrovertible proofs. I sought such proofs both in quality and quantity sufficient to illustrate that ‘random’ was not the right word to describe mass shootings, but rather, ‘intelligent design,’ is.
The path of my continued investigation led to endless shocking discoveries, but there was a problem: to describe the methods and explain findings to the casual reader would, it seemed, require a tedious educational process and boring, repetitious citation of facts. It would be about as fun to read as a spreadsheet or database. Not good.
People want visual sound bites easily grasped. More so if Sheeple content with their Evening News and easily frightened off by words like ‘conspiracy theorist,’ and ‘New World Order,’ or similar. Worse, the investigation bogged because of the real life tragedies each shooting represented. Proper investigation meant exhaustive study of individual events, reviewing endless horrific detailed accounts and sad, brutal media imagery. It was taking an emotional and even physical toll upon my body and mind, and my spirit. Eventually, instead of plodding along 10-14 hours a day as at the start, I found myself barely able to work on it a few hours a week.
I played with several ideas on how to present the story NOW, without completion of the full study, for there is indeed already a mountain of proofs uncovered. But again, the complexities in presentation left me feeling it a hopeless task. Finally, I decided to break it down into about a dozen short compartmentalized components suitable for a series of blog posts. Frankly, I’m hoping it will spur someone to offer useful help; it will take funding and staffing to properly complete the study. Or better still, perhaps some Sheriff or other authority will assume the duty as result of shootings in their jurisdiction.
Follows is a synopsis of the Ten Proofs to be presented. There will additionally be, at appropriate points, companion posts detailing the scientific methods or other analytical procedures involved in select proofs where a doubting Thomas type may wish to challenge the validity of claims. I firmly believe that for my proofs to be accepted, they should be presented in a way such that ANYONE can duplicate my work and verify accuracy and conclusions.
This is a legitimate investigation despite its atypical and unorthodox methods and odd topics involved. NOTE: links will NOT WORK until the various posts involved have been posted. You may click on them to discover their current state. Again, subscription to this blog will notify you when new posts are added.
What are the ten proofs of a mass shooter conspiracy?
The Ten Proofs in review…
Proof One: Gun Grabbers Selectively Ignore Mass Shootings, Conceal Patterns;
Any time you find a cover up, you necessarily have a conspiracy to contend with. Gun grabbing groups, including government and biased or puppet media forces, should be using every opportunity to make their case for gun control, but act as if the bulk of gun violence never took place. Why do they employ selective blinders? There is a reason.Proof Two: Shootings Exist in Identical ‘Magical’ Categorical Clusters;
The Illuminati loves magical numbers, as they can translate into meaningful words or names, or leverage ‘spells’. Interesting then, that basic shooting statistics establish set after set in the most magical and potent number of all, one which decodes to ‘Satan.’ This alone reveals dramatic coincidences well beyond the possibility of random chance.Proof Three: Shootings Exist in Endless Sets of Three Forming Straight Lines;
The same Dispersal Pattern Studies method applied by government researchers to UFO sightings reveals Mass Shootings do something UFO sightings allegedly do not: form repetitive patterns with GPS accuracy, doorway-to-doorway-to-doorway.Proof Four: Straight Lines in Turn Form Complex and Perfect Shapes;
When it comes to symbolism, nothing outperforms a graphical shape. Better still when that shape itself has magical properties or relationships to other shapes, or its own hidden or obvious meaning.Proof Five: Shapes in Turn Form Complementary ‘Magical’ Clusters;
It defies odds that perfect shapes should cluster together in ways which share overlapping lines or corners, and be generally both aligned and mirrored in additional symbolism.Proof Six: Shootings Also Relate or Depict Masonic and Satanic symbols;
Select shootings define such symbols with precision. Masonic Symbols are rendered in 3-D. Satanic Symbols are positioned correctly for magical application by Warlock.Proof Seven: Shootings Form Multiple Lines to Cheops Exactly 500 Miles Apart;
Extending select shooting lines finds them bisecting at the ancient Cheops Pyramid to establish a series of lines all of equal degrees of arc. But that just prepares us for a bigger bombshell.Proof Eight: Shooting Lines Also Depict Cheops in 3-D Cutaway View;
The Great Pyramid in Egypt is one of the Holy of Holies to Masons and some satanic cults, and is specifically tied in mysticism to the End Times and historical catastrophic events. This one will scare you.Proof Nine: Shooting Sets Share ‘Magical’ Data Points Which Decode to Messages;
Shooting line sets share three or more identical magical numbers within their data points. These decode to tell us when and where the next shooting will be, name a shooter, or perfectly prophesy some specific outcome.Proof Ten: Individual Shootings Examined in Micro Duplicate the National Study Proofs
Two examples are offered; Aurora and Sandy Hook. They not only duplicate the ten proofs, but they mirror each other and one points to the other. Why are mass shootings on the rise?Are you ready of this? Buckle up!
So let us begin. I propose your best bet will be to SUBSCRIBE to my blog pages so that you are automatically notified as new posts are made to complete the series. Please link, share, tweet, etc., and by all mean vote your ranking at page top of each one, and comment with your questions, criticisms, or thoughts. How else will other know this is important?
Do bear in mind as you read, each offered proof individually seems to defy the odds or logic path required for truly random shooting events. Collectively, it is monumentally clear. Also bear in mind that I am human, and I, like any other, am prone to making mistakes. A ton of information had to be entered and copied from one location to another multiple times (multiple database and software applications). Therefore, either because of a mistake on my part, or perhaps because of a mistake in media or other accounts/records, any given individual data point in any given set of proofs may be found invalid.
By all means let me know if you find such a discrepancy, but please remember this: a single error in a single data point does not invalidate all other data points, and therefore, does not invalidate the conclusions or the suppositions, themselves. In order to dispute my findings, you will need to offer proofs that the method is flawed, the entire data set was in error, or analytical logic was faulty. More: such dispute must address and ultimately invalidate all ten proofs, or short of that, offer equally viable alternative explanations which fit the findings and afford a more innocent explanation.
Since each proof tends to defy all possible odds of random coincidence, and does so consistently, again and again, naysayers will have their work cut out for them. More so, because in many cases, control groups have been established to show truly random data points enjoy no such pattern. I have done my homework, and carefully so.
I will demand the same of naysayers.
Go to Proof One: Gun Grabbers Selectively Ignore Mass Shootings, Conceal Patterns
Go to Side Bar: On on Programmable People
Share this:
Posted in Abuse of Power, Conspiracy, Crime, Government, News Events, Political Commentary, Religion, Uncategorized
1 Comment
Tags: Conspiracy, False flag, gun control, gun violence, mass shootings, mind control, New World Order, patsy, Political Control Technology